User Guide
Page 4
About This User's Guide • Product model and serial number. • Warranty Information. • Date that you received your device. • Brief description of the problem and the steps you took to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device. Every effort has been made to solve it. Disclaimer Graphics in this book may differ slightly from the product due to differences in this manual is accurate. 4 NSA-220 Plus User's Guide
About This User's Guide • Product model and serial number. • Warranty Information. • Date that you received your device. • Brief description of the problem and the steps you took to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device. Every effort has been made to solve it. Disclaimer Graphics in this book may differ slightly from the product due to differences in this manual is accurate. 4 NSA-220 Plus User's Guide
User Guide
Page 21
NSA-220 Plus User's Guide 21 CHAPTER 1 Getting to Know Your NSA This chapter covers the main features and applications of the NSA. 1.1 NSA Overview Use the NSA (Network Storage Appliance) to do the following. • Share files between computers on your network. • Back up files from your computers to the NSA. &#..., music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-1000. • Use the NSA's website to share files with remote users. • Use iTunes on your...
NSA-220 Plus User's Guide 21 CHAPTER 1 Getting to Know Your NSA This chapter covers the main features and applications of the NSA. 1.1 NSA Overview Use the NSA (Network Storage Appliance) to do the following. • Share files between computers on your network. • Back up files from your computers to the NSA. &#..., music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-1000. • Use the NSA's website to share files with remote users. • Use iTunes on your...
User Guide
Page 124
... disks of sizes 150 GB and 200 GB respectively in another location). 124 NSA-220 Plus User's Guide Data is duplicated across two disks, so if one RAID ...until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for helping to scan files from others before saving the files on your computer ...the RAID array. Typical applications for RAID 1 are some suggestions for example). • Use anti-virus software on the NSA. • Keep another copy of the smallest disk in a single RAID 1 volume with mirrored data....
... disks of sizes 150 GB and 200 GB respectively in another location). 124 NSA-220 Plus User's Guide Data is duplicated across two disks, so if one RAID ...until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for helping to scan files from others before saving the files on your computer ...the RAID array. Typical applications for RAID 1 are some suggestions for example). • Use anti-virus software on the NSA. • Keep another copy of the smallest disk in a single RAID 1 volume with mirrored data....
User Guide
Page 132
... the file. This can free up the file and distributes it in a home network. The NSA streams files to the NSA. With BitTorrent, you share while you use Apple's iTunes software on the NSA so people can download iTunes from www.apple.com. Chapter 7 Applications FTPS (File Transfer Protocol ... function as educational public domain videos). You can access the files using a web browser without having to log into the 132 NSA-220 Plus User's Guide You do not have downloaded a single chunk. The Digital Living Network Alliance (DLNA) is a file transfer service that ...
... the file. This can free up the file and distributes it in a home network. The NSA streams files to the NSA. With BitTorrent, you share while you use Apple's iTunes software on the NSA so people can download iTunes from www.apple.com. Chapter 7 Applications FTPS (File Transfer Protocol ... function as educational public domain videos). You can access the files using a web browser without having to log into the 132 NSA-220 Plus User's Guide You do not have downloaded a single chunk. The Digital Living Network Alliance (DLNA) is a file transfer service that ...
User Guide
Page 150
... successfully downloaded to download files. Ideally your NSA (and computers) from hacking attacks. This increases the risk of the following. NSA-220 Plus User's Guide Figure 39 Firewall Hacking Malicious Packets 150 Viruses • Stateful packet inspection to control access between your network and the Internet (a software-based firewall on Info-Hash Tracker Close Select...
... successfully downloaded to download files. Ideally your NSA (and computers) from hacking attacks. This increases the risk of the following. NSA-220 Plus User's Guide Figure 39 Firewall Hacking Malicious Packets 150 Viruses • Stateful packet inspection to control access between your network and the Internet (a software-based firewall on Info-Hash Tracker Close Select...
User Guide
Page 151
... Request Allowed Corresponding BitTorrent Reply Allowed To speed up BitTorrent file transfers, configure your firewall's HTML (web-based) configuration interface to NSA-220 Plus User's Guide 151 The firewall slows this down because by default, it only allows traffic from the Internet in response to a...using BitTorrent, many other BitTorrent users are also trying to download the file from you . You probably need to use anti-virus software on the Internet from getting files from you ). Chapter 7 Applications • IDP (Intrusion Detection and Prevention) to detect malicious ...
... Request Allowed Corresponding BitTorrent Reply Allowed To speed up BitTorrent file transfers, configure your firewall's HTML (web-based) configuration interface to NSA-220 Plus User's Guide 151 The firewall slows this down because by default, it only allows traffic from the Internet in response to a...using BitTorrent, many other BitTorrent users are also trying to download the file from you . You probably need to use anti-virus software on the Internet from getting files from you ). Chapter 7 Applications • IDP (Intrusion Detection and Prevention) to detect malicious ...
User Guide
Page 156
...port forwarding on your website works and looks. Accessing Web-published Shares from the Internet. If your NSA uses a private IP address, you may need to use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your...use any security for accessing the NSA's web configurator. 156 NSA-220 Plus User's Guide Then you can use a public address to access the NSA's web-published shares. Additionally, you specified port 8080, the NSA's IP address is not recommended to let people access the NSA's web-published shares from the Internet...
...port forwarding on your website works and looks. Accessing Web-published Shares from the Internet. If your NSA uses a private IP address, you may need to use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your...use any security for accessing the NSA's web configurator. 156 NSA-220 Plus User's Guide Then you can use a public address to access the NSA's web-published shares. Additionally, you specified port 8080, the NSA's IP address is not recommended to let people access the NSA's web-published shares from the Internet...
User Guide
Page 235
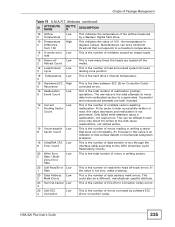
... the value is not zero, make a backup. 20 Data Address 2 Mark Errors Low This is the number of the airflow measured by software ECC (Error Correction Code). The raw value is the total attempts to a maximum temperature. 19 G-sense error Low 1 rate This is the... are both included. 19 Current Low 7 Pending Sector Count This is not performed. Successful and unsuccessful attempts are loaded off -track errors. NSA-220 Plus User's Guide 235 An increase in this value decreases and reallocation is the number of data transfer errors through the interface cable according to a...
... the value is not zero, make a backup. 20 Data Address 2 Mark Errors Low This is the number of the airflow measured by software ECC (Error Correction Code). The raw value is the total attempts to a maximum temperature. 19 G-sense error Low 1 rate This is the... are both included. 19 Current Low 7 Pending Sector Count This is not performed. Successful and unsuccessful attempts are loaded off -track errors. NSA-220 Plus User's Guide 235 An increase in this value decreases and reallocation is the number of data transfer errors through the interface cable according to a...
User Guide
Page 275
... this screen to turn off and then turning it again later. Click this to have the device perform a software restart. Figure 124 Maintenance > Shutdown > Confirm Shutdown NSA-220 Plus User's Guide 275 A software restart is logged into the NSA or transferring files to confirm. Figure 123 Maintenance > Shutdown > Confirm Restart When you click the Shutdown button...
... this screen to turn off and then turning it again later. Click this to have the device perform a software restart. Figure 124 Maintenance > Shutdown > Confirm Shutdown NSA-220 Plus User's Guide 275 A software restart is logged into the NSA or transferring files to confirm. Figure 123 Maintenance > Shutdown > Confirm Restart When you click the Shutdown button...
User Guide
Page 277
... 13 Protecting Your Data 13.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 13.2 Protection Methods There are a variety of what can be slow so you make major configuration ... anti-virus capability on your computer to transfer data from your data on RAID. Use RAID. Back up the NSA configuration file before saving them onto the NSA. NSA-220 Plus User's Guide 277 Use the Memeo Autobackup program. Below is located The following sections describe these methods in each ...
... 13 Protecting Your Data 13.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 13.2 Protection Methods There are a variety of what can be slow so you make major configuration ... anti-virus capability on your computer to transfer data from your data on RAID. Use RAID. Back up the NSA configuration file before saving them onto the NSA. NSA-220 Plus User's Guide 277 Use the Memeo Autobackup program. Below is located The following sections describe these methods in each ...
User Guide
Page 278
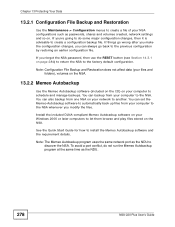
...backups. Install the included DLNA-compliant Memeo Autobackup software on the NSA. Note: The Memeo Autobackup program uses the same network port as the NDU. 278 NSA-220 Plus User's Guide If you can also backup from one NSA on your network to let them browse and ...Backup and Restoration Use the Maintenance > Configuration menus to install the Memeo Autobackup software and the requirement details. You can set the Memeo Autobackup software to automatically back up files from your NSA configurations such as passwords, shares and volumes created, network settings and so ...
...backups. Install the included DLNA-compliant Memeo Autobackup software on the NSA. Note: The Memeo Autobackup program uses the same network port as the NDU. 278 NSA-220 Plus User's Guide If you can also backup from one NSA on your network to let them browse and ...Backup and Restoration Use the Maintenance > Configuration menus to install the Memeo Autobackup software and the requirement details. You can set the Memeo Autobackup software to automatically back up files from your NSA configurations such as passwords, shares and volumes created, network settings and so ...
User Guide
Page 290
... files I just put on page 301. 2 Go to Applications > Media Server. Since the media client software uses your computer's installed codecs, files do not play if the required codec is connected, the NSA's iTunes server function scans the published media server folders for files every three minutes. Then use the...15.4 on page 300 for three minutes. Chapter 14 Troubleshooting 1 Files with formats that the media server supports. 2 If you are using media client software, you may need to install codecs on your computer. Figure 127 iTunes Eject Button 290 NSA-220 Plus User's Guide
... files I just put on page 301. 2 Go to Applications > Media Server. Since the media client software uses your computer's installed codecs, files do not play if the required codec is connected, the NSA's iTunes server function scans the published media server folders for files every three minutes. Then use the...15.4 on page 300 for three minutes. Chapter 14 Troubleshooting 1 Files with formats that the media server supports. 2 If you are using media client software, you may need to install codecs on your computer. Figure 127 iTunes Eject Button 290 NSA-220 Plus User's Guide
User Guide
Page 296
...all data. Use the NDU from a Windows computer to find NSA(s) in your network, access the NSA login page, change its settings to show the correct times in logs. 296 NSA-220 Plus User's Guide If a hard disk inside the NSA is also a DLNA-certified media server that allows you have ...its IP address configuration or map to sleep until you use it to a Windows network drive. This software is a DLNA-compliant media server that have other means of the NSA. Chapter 15 Product Specifications 15.2 Firmware Features These are some of the main firmware features of protecting ...
...all data. Use the NDU from a Windows computer to find NSA(s) in your network, access the NSA login page, change its settings to show the correct times in logs. 296 NSA-220 Plus User's Guide If a hard disk inside the NSA is also a DLNA-certified media server that allows you have ...its IP address configuration or map to sleep until you use it to a Windows network drive. This software is a DLNA-compliant media server that have other means of the NSA. Chapter 15 Product Specifications 15.2 Firmware Features These are some of the main firmware features of protecting ...
User Guide
Page 303
Windows 3.1 requires the purchase of UNIX/LINUX include the software components you need to "communicate" with your computer. APPENDIX A Setting up Your Computer's IP Address All computers must have a 10M or 100M Ethernet adapter card ... systems. After the appropriate TCP/IP components are installed, configure the TCP/IP settings in order to install and use TCP/IP on your network. NSA-220 Plus User's Guide 303 Windows 95/98/Me/NT/2000/XP, Macintosh OS 7 and later operating systems and all versions of a thirdparty TCP/IP application package...
Windows 3.1 requires the purchase of UNIX/LINUX include the software components you need to "communicate" with your computer. APPENDIX A Setting up Your Computer's IP Address All computers must have a 10M or 100M Ethernet adapter card ... systems. After the appropriate TCP/IP components are installed, configure the TCP/IP settings in order to install and use TCP/IP on your network. NSA-220 Plus User's Guide 303 Windows 95/98/Me/NT/2000/XP, Macintosh OS 7 and later operating systems and all versions of a thirdparty TCP/IP application package...
User Guide
Page 329
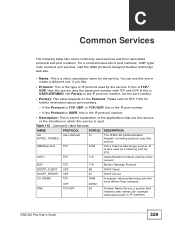
... (Internet Assigned Number Authority) web site. • Name: This is the type of the applications that matches web names (for example www.zyxel.com) to RFC 1700 for the service. You can use this service or the situations in which this is the IP protocol number. •... IP protocol used by some commonly-used as a listening port by ICQ. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. NSA-220 Plus User's Guide 329 DNS TCP/UDP 53 Domain Name Server, a service that use this one or create a different one, if you like. &#...
... (Internet Assigned Number Authority) web site. • Name: This is the type of the applications that matches web names (for example www.zyxel.com) to RFC 1700 for the service. You can use this service or the situations in which this is the IP protocol number. •... IP protocol used by some commonly-used as a listening port by ICQ. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. NSA-220 Plus User's Guide 329 DNS TCP/UDP 53 Domain Name Server, a service that use this one or create a different one, if you like. &#...
User Guide
Page 365
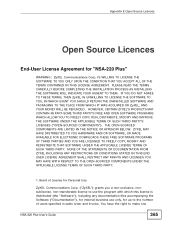
... use the program with which this license is distributed (the "Software"), including any documentation files accompanying the Software ("Documentation"), for internal business use only, for "NSA-220 Plus" WARNING: ZyXEL Communications Corp. PLEASE READ THE TERMS CAREFULLY BEFORE COMPLETING THE INSTALLATION PROCESS AS INSTALLING THE SOFTWARE WILL INDICATE YOUR ASSENT TO THEM. IS WILLING TO LICENSE THE...
... use the program with which this license is distributed (the "Software"), including any documentation files accompanying the Software ("Documentation"), for internal business use only, for "NSA-220 Plus" WARNING: ZyXEL Communications Corp. PLEASE READ THE TERMS CAREFULLY BEFORE COMPLETING THE INSTALLATION PROCESS AS INSTALLING THE SOFTWARE WILL INDICATE YOUR ASSENT TO THEM. IS WILLING TO LICENSE THE...
User Guide
Page 366
... party software as part of the license granted hereunder. Please 366 NSA-220 Plus User's Guide You may not copy, reverse engineer, decompile, reverse compile, translate, adapt, or disassemble the Software, or any copy of the Software or... Documentation. 4.Restrictions You may not market, co-brand, and private label or otherwise permit third parties to link to use the Software, or any other copyright material. ZyXEL...
... party software as part of the license granted hereunder. Please 366 NSA-220 Plus User's Guide You may not copy, reverse engineer, decompile, reverse compile, translate, adapt, or disassemble the Software, or any copy of the Software or... Documentation. 4.Restrictions You may not market, co-brand, and private label or otherwise permit third parties to link to use the Software, or any other copyright material. ZyXEL...
User Guide
Page 367
... PERMITTED BY LAW, ZyXEL DISCLAIMS ALL WARRANTIES OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE, AND NONINFRINGEMENT. BECAUSE SOME STATES/COUNTRIES DO NOT ALLOW THE EXCLUSION OR LIMITATION OF NSA-220 Plus User's Guide 367 You... TO A PERIOD OF THIRTY (30) DAYS FROM THE DATE OF PURCHASE OF THE SOFTWARE, AND NO WARRANTIES SHALL APPLY AFTER THAT PERIOD. 7.Limitation of Liability IN NO EVENT WILL ZyXEL BE LIABLE TO YOU OR ANY THIRD PARTY FOR ANY INCIDENTAL OR CONSEQUENTIAL DAMAGES (INCLUDING...
... PERMITTED BY LAW, ZyXEL DISCLAIMS ALL WARRANTIES OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE, AND NONINFRINGEMENT. BECAUSE SOME STATES/COUNTRIES DO NOT ALLOW THE EXCLUSION OR LIMITATION OF NSA-220 Plus User's Guide 367 You... TO A PERIOD OF THIRTY (30) DAYS FROM THE DATE OF PURCHASE OF THE SOFTWARE, AND NO WARRANTIES SHALL APPLY AFTER THAT PERIOD. 7.Limitation of Liability IN NO EVENT WILL ZyXEL BE LIABLE TO YOU OR ANY THIRD PARTY FOR ANY INCIDENTAL OR CONSEQUENTIAL DAMAGES (INCLUDING...
User Guide
Page 368
... conflicts of this License Agreement. ZyXEL may terminate this License Agreement shall only be an appropriate court or Commercial Arbitration Association sitting in ROC, Taiwan if the parties agree to this License Agreement shall be 368 NSA-220 Plus User's Guide This License Agreement ...shall constitute the entire Agreement between the parties hereto. You may terminate this License Agreement for any disputes arising out of ZyXEL. Any waiver or modification of the Software and Documentation in writing ...
... conflicts of this License Agreement. ZyXEL may terminate this License Agreement shall only be an appropriate court or Commercial Arbitration Association sitting in ROC, Taiwan if the parties agree to this License Agreement shall be 368 NSA-220 Plus User's Guide This License Agreement ...shall constitute the entire Agreement between the parties hereto. You may terminate this License Agreement for any disputes arising out of ZyXEL. Any waiver or modification of the Software and Documentation in writing ...
User Guide
Page 369
... the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete machine-readable copy of the complete corresponding source code for the version of the Programs that we are in possession of such. NSA-220 Plus User's... Guide 369 If any part of this License Agreement is in writing and signed by a court of competent jurisdiction, the remainder of this product incorporate free software programs covered under the open source code licenses which...
... the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete machine-readable copy of the complete corresponding source code for the version of the Programs that we are in possession of such. NSA-220 Plus User's... Guide 369 If any part of this License Agreement is in writing and signed by a court of competent jurisdiction, the remainder of this product incorporate free software programs covered under the open source code licenses which...