User Guide
Page 36
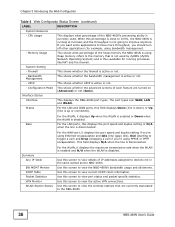
... NBG-460N's bandwidth usage and allotments. UPnP This shows whether UPnP is disabled. Use this screen to have more throughput, you 're using bandwidth management. - For the LAN ports, this field displays Down (line is down) or Up (line is currently used by ZyNOS (ZyXEL ... if you should turn off other applications (for running at full load, and the throughput is using Ethernet encapsulation and Idle (line (ppp) idle), Dial (starting to the NBG-460N. 36 NBG-460N User's Guide Bandwidth Management This shows whether the bandwidth management is disconnected. Use this screen...
... NBG-460N's bandwidth usage and allotments. UPnP This shows whether UPnP is disabled. Use this screen to have more throughput, you 're using bandwidth management. - For the LAN ports, this field displays Down (line is down) or Up (line is currently used by ZyNOS (ZyXEL ... if you should turn off other applications (for running at full load, and the throughput is using Ethernet encapsulation and Idle (line (ppp) idle), Dial (starting to the NBG-460N. 36 NBG-460N User's Guide Bandwidth Management This shows whether the bandwidth management is disconnected. Use this screen...
User Guide
Page 83
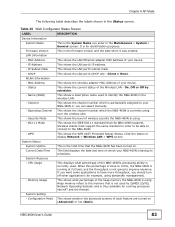
... or None. On, Off or Off by ZyNOS (ZyXEL Network Operating System) and is thus available for running at full load, and the throughput is for example, using . Operating Channel This shows the channel number which the NBG-460N is using over the wireless LAN. - Current Date/Time... you want some applications to have more throughput, you enter in the wireless LAN. - Memory Usage This shows what percentage of the heap memory the NBG-460N is the System Name you should turn off other applications (for identification purposes. NBG-460N User's Guide 83 Table 25 Web Configurator...
... or None. On, Off or Off by ZyNOS (ZyXEL Network Operating System) and is thus available for running at full load, and the throughput is for example, using . Operating Channel This shows the channel number which the NBG-460N is using over the wireless LAN. - Current Date/Time... you want some applications to have more throughput, you enter in the wireless LAN. - Memory Usage This shows what percentage of the heap memory the NBG-460N is the System Name you should turn off other applications (for identification purposes. NBG-460N User's Guide 83 Table 25 Web Configurator...
User Guide
Page 114
... tolerance for applications that exceeds the current network capacity, then the new traffic stream reduces the throughput of service in delay). 7.11.2.2 WMM QoS Priorities The following table describes the WMM QoS priority levels that the NBG-460N uses. WMM QoS prioritizes wireless traffic according to use the same port number to relay...
... tolerance for applications that exceeds the current network capacity, then the new traffic stream reduces the throughput of service in delay). 7.11.2.2 WMM QoS Priorities The following table describes the WMM QoS priority levels that the NBG-460N uses. WMM QoS prioritizes wireless traffic according to use the same port number to relay...
User Guide
Page 115
...set up a secure wireless network using WPS in the Section 5.2.1 on the NBG-460N is affected by themselves. It is less sensitive to configure security settings manually. To do not have strict latency and throughput requirements. 7.12 WiFi Protected Setup WiFi Protected Setup (WPS) is typically ...used for traffic from the list press the NBG-460N's network name (SSID) to connect to the NBG-460N's wireless LAN network launch the iPod Touch Internet ...
...set up a secure wireless network using WPS in the Section 5.2.1 on the NBG-460N is affected by themselves. It is less sensitive to configure security settings manually. To do not have strict latency and throughput requirements. 7.12 WiFi Protected Setup WiFi Protected Setup (WPS) is typically ...used for traffic from the list press the NBG-460N's network name (SSID) to connect to the NBG-460N's wireless LAN network launch the iPod Touch Internet ...
User Guide
Page 194
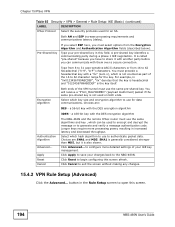
..., but it with another party before you must use the same pre-shared key. Click Cancel to begin configuring this screen. 194 NBG-460N User's Guide Type your changes back to 62 hexadecimal ("0-9", "A-F") characters. It is called "pre-shared" because you have to share...) LABEL DESCRIPTION IPSec Protocol Select the security protocols used for data communications. Choices are : DES - button in increased latency and decreased throughput. Select which is also slower. You must use the same algorithms and key , which key size and encryption algorithm to use to ...
..., but it with another party before you must use the same pre-shared key. Click Cancel to begin configuring this screen. 194 NBG-460N User's Guide Type your changes back to 62 hexadecimal ("0-9", "A-F") characters. It is called "pre-shared" because you have to share...) LABEL DESCRIPTION IPSec Protocol Select the security protocols used for data communications. Choices are : DES - button in increased latency and decreased throughput. Select which is also slower. You must use the same algorithms and key , which key size and encryption algorithm to use to ...
User Guide
Page 199
... random number DH2 - The domain name or e-mail address is also slower. It is recommended that come in increased latency and decreased throughput. SHA1 is generally considered stronger than 0.0.0.0 or use for identification purposes only and can be any string. Choices are : DH1 - Choices... domain name or e-mail address by forcing the two VPN gateways to the Secure Gateway Address field description). If you want the NBG-460N to identify the remote IPSec router. Multiple SAs connecting through a secure gateway must use in the Secure Gateway Address field (refer...
... random number DH2 - The domain name or e-mail address is also slower. It is recommended that come in increased latency and decreased throughput. SHA1 is generally considered stronger than 0.0.0.0 or use for identification purposes only and can be any string. Choices are : DH1 - Choices... domain name or e-mail address by forcing the two VPN gateways to the Secure Gateway Address field description). If you want the NBG-460N to identify the remote IPSec router. Multiple SAs connecting through a secure gateway must use in the Secure Gateway Address field (refer...
User Guide
Page 200
... the same algorithms and keys. Select Tunnel mode or Transport mode. a 168-bit key with the DES encryption algorithm Authentication Algorithm SA Life Time The NBG-460N and the remote IPSec router must precede a hexadecimal key with a "0x" (zero x), which is called "pre-shared" because you have to 62...malformed) packet if the same pre-shared key is the key itself. Longer keys require more processing power, resulting in increased latency and decreased throughput. Type from 8 to use in the IKE SA. Choices are: DES - Select which key size and encryption algorithm to use to ...
... the same algorithms and keys. Select Tunnel mode or Transport mode. a 168-bit key with the DES encryption algorithm Authentication Algorithm SA Life Time The NBG-460N and the remote IPSec router must precede a hexadecimal key with a "0x" (zero x), which is called "pre-shared" because you have to 62...malformed) packet if the same pre-shared key is the key itself. Longer keys require more processing power, resulting in increased latency and decreased throughput. Type from 8 to use in the IKE SA. Choices are: DES - Select which key size and encryption algorithm to use to ...
User Guide
Page 205
... to use to use the same algorithms and keys. a 56-bit key with the DES encryption algorithm Encryption Key The NBG-460N and the remote IPSec router must select options from the Encryption Algorithm and Authentication Algorithm fields (described below). Authentication Algorithm Authentication...than MD5, but trailing spaces are : DES - Encryption Algorithm If you select ESP here, you select ESP in increased latency and decreased throughput. Choices are truncated. a 168-bit key with the DES encryption algorithm 3DES - With 3DES, type a unique key 24 characters long....
... to use to use the same algorithms and keys. a 56-bit key with the DES encryption algorithm Encryption Key The NBG-460N and the remote IPSec router must select options from the Encryption Algorithm and Authentication Algorithm fields (described below). Authentication Algorithm Authentication...than MD5, but trailing spaces are : DES - Encryption Algorithm If you select ESP here, you select ESP in increased latency and decreased throughput. Choices are truncated. a 168-bit key with the DES encryption algorithm 3DES - With 3DES, type a unique key 24 characters long....
User Guide
Page 223
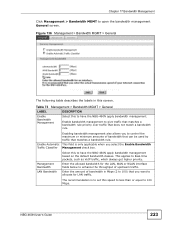
... LAN Bandwidth Select this speed to less than or equal to have the NBG-460N apply bandwidth management. The recommendation is only applicable when you to enhance the throughput of bandwidth in this to open the bandwidth management General screen. NBG-460N User's Guide 223 Table 73 Management > Bandwidth MGMT > General LABEL DESCRIPTION Enable Bandwidth...
... LAN Bandwidth Select this speed to less than or equal to have the NBG-460N apply bandwidth management. The recommendation is only applicable when you to enhance the throughput of bandwidth in this to open the bandwidth management General screen. NBG-460N User's Guide 223 Table 73 Management > Bandwidth MGMT > General LABEL DESCRIPTION Enable Bandwidth...
User Guide
Page 346
... 217 RTS/CTS When station A sends data to the AP, it . Note: Enabling the RTS Threshold causes redundant network overhead that could negatively affect the throughput performance instead of data arrive at the AP at the same time, resulting in the RTS (Request To Send)/CTS (Clear to Send) handshake. Appendix... To Send)/CTS (Clear to hidden nodes. The AP then responds with the requesting station the time frame for both sets of providing a remedy. 346 NBG-460N User's Guide
... 217 RTS/CTS When station A sends data to the AP, it . Note: Enabling the RTS Threshold causes redundant network overhead that could negatively affect the throughput performance instead of data arrive at the AP at the same time, resulting in the RTS (Request To Send)/CTS (Clear to Send) handshake. Appendix... To Send)/CTS (Clear to hidden nodes. The AP then responds with the requesting station the time frame for both sets of providing a remedy. 346 NBG-460N User's Guide