Security Target
Page 4
... 66 6.2 Security Assurance Requirements 66 6.3 Security Requirements Rationale 67 6.3.1 Tracing ...67 6.3.2 Justification of Traceability 69 6.3.3 Dependency Analysis 75 6.3.4 Security Assurance Requirements Rationale 77 7 TOE Summary Specification 78 7.1 Audit Function ...78 7.2 Identification and Authentication Function 80 Copyright (c) 2011...
... 66 6.2 Security Assurance Requirements 66 6.3 Security Requirements Rationale 67 6.3.1 Tracing ...67 6.3.2 Justification of Traceability 69 6.3.3 Dependency Analysis 75 6.3.4 Security Assurance Requirements Rationale 77 7 TOE Summary Specification 78 7.1 Audit Function ...78 7.2 Identification and Authentication Function 80 Copyright (c) 2011...
Security Target
Page 6
...of Administrative Roles...18 Table 7 : Definition of User Data ...24 Table 8 : Definition of TSF Data ...25 Table 9 : Specific Terms Related to This ST 25 Table 10 : Rationale for Security Objectives 40 Table 11 : List of Auditable Events ...48 Table 12...Roles Allowed to Override Default Values 62 Table 28 : List of TSF Data ...63 Table 29 : List of Specification of Management Functions 64 Table 30 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2 67 Table 31 : Relationship between ...Table 35 : Unlocking Administrators for Each User Role 81 Copyright (c) 2011 RICOH COMPANY, LTD.
...of Administrative Roles...18 Table 7 : Definition of User Data ...24 Table 8 : Definition of TSF Data ...25 Table 9 : Specific Terms Related to This ST 25 Table 10 : Rationale for Security Objectives 40 Table 11 : List of Auditable Events ...48 Table 12...Roles Allowed to Override Default Values 62 Table 28 : List of TSF Data ...63 Table 29 : List of Specification of Management Functions 64 Table 30 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2 67 Table 31 : Relationship between ...Table 35 : Unlocking Administrators for Each User Role 81 Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 25
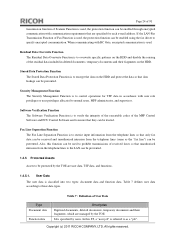
...encrypt the data on the HDD and protect the data so that data leakage can be prevented. 1.4.5 Protected Assets Assets to overwrite specific patterns on the HDD. Software Verification Function The Software Verification Function is to verify the integrity of the executable codes of the ... to specify encrypted communication. Also, this ST, a "user job" is classified into two types: document data and function data. Copyright (c) 2011 RICOH COMPANY, LTD. Page 24 of 91 transmission function of Scanner Function is used . Table 7 : Definition of User Data Type Document data Function data...
...encrypt the data on the HDD and protect the data so that data leakage can be prevented. 1.4.5 Protected Assets Assets to overwrite specific patterns on the HDD. Software Verification Function The Software Verification Function is to verify the integrity of the executable codes of the ... to specify encrypted communication. Also, this ST, a "user job" is classified into two types: document data and function data. Copyright (c) 2011 RICOH COMPANY, LTD. Page 24 of 91 transmission function of Scanner Function is used . Table 7 : Definition of User Data Type Document data Function data...
Security Target
Page 26
... stored in the TOE. The TOE identifies users by users without viewing permissions. Copyright (c) 2011 RICOH COMPANY, LTD. Type Protected data Confidential data Table 8 : Definition of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to these data types. A password associated with each normal user, MFP administrator...
... stored in the TOE. The TOE identifies users by users without viewing permissions. Copyright (c) 2011 RICOH COMPANY, LTD. Type Protected data Confidential data Table 8 : Definition of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to these data types. A password associated with each normal user, MFP administrator...
Security Target
Page 46
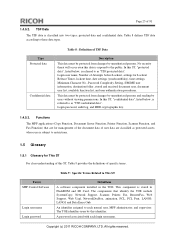
... provides for the management functions in FMT: a) Definition of functionality. Rationale: Quite often, a TOE is supposed to perform specific checks and process data received on one external interface before such (processed) data are allowed to be considered for the functionality to... received over defined external interfaces before it is forbidden unless explicitly allowed by an authorized administrative role. Examples Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. The family FPT_FDI_EXP has been defined to require TSF controlled processing of unprocessed data between ...
... provides for the management functions in FMT: a) Definition of functionality. Rationale: Quite often, a TOE is supposed to perform specific checks and process data received on one external interface before such (processed) data are allowed to be considered for the functionality to... received over defined external interfaces before it is forbidden unless explicitly allowed by an authorized administrative role. Examples Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. The family FPT_FDI_EXP has been defined to require TSF controlled processing of unprocessed data between ...
Security Target
Page 47
... between different external interfaces is to address this . FPT_FDI_EXP.1 Restricted forwarding of data to external interfaces Hierarchical to: No other systems that require a specific work flow for a number of products, it has been viewed as a single component that allows specifying the property to disallow direct forwarding and require...using administrative control instead of both user data and TSF data, and it in either the FDP or the FPT class. Copyright (c) 2011 RICOH COMPANY, LTD. The Common Criteria defines attribute-based control of the existing families in the FPT class.
... between different external interfaces is to address this . FPT_FDI_EXP.1 Restricted forwarding of data to external interfaces Hierarchical to: No other systems that require a specific work flow for a number of products, it has been viewed as a single component that allows specifying the property to disallow direct forwarding and require...using administrative control instead of both user data and TSF data, and it in either the FDP or the FPT class. Copyright (c) 2011 RICOH COMPANY, LTD. The Common Criteria defines attribute-based control of the existing families in the FPT class.
Security Target
Page 49
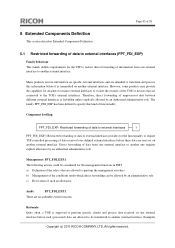
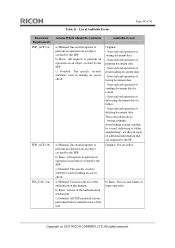
...document data. - Those described above, "storing, printing, downloading, faxing, sending by e-mail, delivering to folder. - c) Detailed: The specific security attributes used in making an access check. Start and end operation of storing document data. - Start and end operation of delivering document data... an access check. b) Basic: All use of the authentication mechanism; Start and end operation of login operation Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. Table 11 : List of Auditable Events Page 48 of 91 Functional Requirements FDP_ACF.1(a) FDP_ACF.1(b) ...
...document data. - Those described above, "storing, printing, downloading, faxing, sending by e-mail, delivering to folder. - c) Detailed: The specific security attributes used in making an access check. Start and end operation of storing document data. - Start and end operation of delivering document data... an access check. b) Basic: All use of the authentication mechanism; Start and end operation of login operation Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. Table 11 : List of Auditable Events Page 48 of 91 Functional Requirements FDP_ACF.1(a) FDP_ACF.1(b) ...
Security Target
Page 61
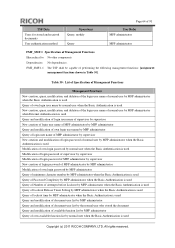
... MFP administrator who owns the applicable login user name Supervisor None No operation permitted None Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(a) The TSF shall enforce the [assignment: document access control SFP] to restrict...
... MFP administrator who owns the applicable login user name Supervisor None No operation permitted None Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(a) The TSF shall enforce the [assignment: document access control SFP] to restrict...
Security Target
Page 62
... Normal user who owns the applicable login user name MFP administrator MFP administrator Applicable normal user None None Copyright (c) 2011 RICOH COMPANY, LTD. Document user list [when document data attribute is (+DSR)] Document user list [when document data attribute is... 27]. All rights reserved. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(b)The TSF shall enforce the [assignment: TOE function access control SFP] to restrict the ability to [selection: query...
... Normal user who owns the applicable login user name MFP administrator MFP administrator Applicable normal user None None Copyright (c) 2011 RICOH COMPANY, LTD. Document user list [when document data attribute is (+DSR)] Document user list [when document data attribute is... 27]. All rights reserved. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Function FMT_MSA.1.1(b)The TSF shall enforce the [assignment: TOE function access control SFP] to restrict the ability to [selection: query...
Security Target
Page 63
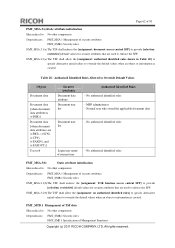
...: restrictive] default values for security attributes that are used to enforce the SFP. Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of normal user Authorised Identified Roles - No authorised identified roles - All rights reserved. Dependencies: FMT_MSA.1 Management of security... job Security Attributes Document data attribute Document user list Document user list Login user name of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD. MFP administrator - FMT_MTD.1 Management of TSF data Hierarchical to: No other components. Page 62 of 91...
...: restrictive] default values for security attributes that are used to enforce the SFP. Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of normal user Authorised Identified Roles - No authorised identified roles - All rights reserved. Dependencies: FMT_MSA.1 Management of security... job Security Attributes Document data attribute Document user list Document user list Login user name of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD. MFP administrator - FMT_MTD.1 Management of TSF data Hierarchical to: No other components. Page 62 of 91...
Security Target
Page 65
... MFP administrator Query of performing the following management functions: [assignment: management functions shown in Table 30]. Table 30 : List of Specification of Management Functions Management Functions New creation, query, modification, and deletion of the login user name of normal user by MFP administrator... when the Basic Authentication is used Query of lockout time by MFP administrator when the Basic Authentication is used Copyright (c) 2011 RICOH COMPANY, LTD. Page 64 of 91 TSF Data Users for stored and received documents User authentication method Operations Query, modify Query...
... MFP administrator Query of performing the following management functions: [assignment: management functions shown in Table 30]. Table 30 : List of Specification of Management Functions Management Functions New creation, query, modification, and deletion of the login user name of normal user by MFP administrator... when the Basic Authentication is used Query of lockout time by MFP administrator when the Basic Authentication is used Copyright (c) 2011 RICOH COMPANY, LTD. Page 64 of 91 TSF Data Users for stored and received documents User authentication method Operations Query, modify Query...
Security Target
Page 67
... line]. 6.1.7 Class FTA: TOE access FTA_SSL.3 TSF-initiated termination Hierarchical to : No other components. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. FTP_ITC.1.3 The TSF shall initiate communication via the trusted channel for [assignment: communication via...to initiate communication via the LAN]. 6.2 Security Assurance Requirements The evaluation assurance level of the TOE. Dependencies: FMT_SMF.1 Specification of components defined in evaluation assurance level 3 (EAL3). Dependencies: No dependencies. FTP_ITC.1.1 The TSF shall provide a ...
... line]. 6.1.7 Class FTA: TOE access FTA_SSL.3 TSF-initiated termination Hierarchical to : No other components. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. FTP_ITC.1.3 The TSF shall initiate communication via the trusted channel for [assignment: communication via...to initiate communication via the LAN]. 6.2 Security Assurance Requirements The evaluation assurance level of the TOE. Dependencies: FMT_SMF.1 Specification of components defined in evaluation assurance level 3 (EAL3). Dependencies: No dependencies. FTP_ITC.1.1 The TSF shall provide a ...
Security Target
Page 68
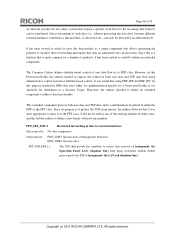
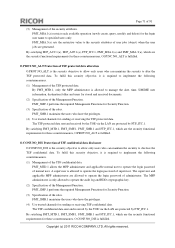
...Table 32 shows the relationship between the TOE security functional requirements and TOE security objectives. Copyright (c) 2011 RICOH COMPANY, LTD. Page 67 of 91 Table 31 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2) Assurance ....2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance Components Security architecture description Functional specification with complete summary Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification...
...Table 32 shows the relationship between the TOE security functional requirements and TOE security objectives. Copyright (c) 2011 RICOH COMPANY, LTD. Page 67 of 91 Table 31 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2) Assurance ....2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance Components Security architecture description Functional specification with complete summary Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification...
Security Target
Page 72
...maintain the security to disclose the TSF confidential data. The supervisor and applicable MFP administrator are generated. Copyright (c) 2011 RICOH COMPANY, LTD. O.PROT.NO_ALT Protection of administrator. FMT_MSA.3(a) sets the restrictive value to the security attributes of user jobs... and FTP_ITC.1, which are protected by the TOE via the LAN are the security functional requirements for Security Function. (3) Specification of TSF confidential data disclosure O.CONF.NO_DIS is only allowed to operate the login password of the Management Function. A ...
...maintain the security to disclose the TSF confidential data. The supervisor and applicable MFP administrator are generated. Copyright (c) 2011 RICOH COMPANY, LTD. O.PROT.NO_ALT Protection of administrator. FMT_MSA.3(a) sets the restrictive value to the security attributes of user jobs... and FTP_ITC.1, which are protected by the TOE via the LAN are the security functional requirements for Security Function. (3) Specification of TSF confidential data disclosure O.CONF.NO_DIS is only allowed to operate the login password of the Management Function. A ...
Security Target
Page 73
... the persons by FTP_ITC.1. FIA_UID.2 identifies the person who have the privileges. (4) Use trusted channels for Security Function. (3) Specification of the roles. All rights reserved. The supervisor and applicable MFP administrator are allowed to the protected assets of the users ... identification and authentication. FIA_ATD.1 and FIA_USB.1 manage the access procedures to operate the login password of administrator. Copyright (c) 2011 RICOH COMPANY, LTD. The MFP administrator is allowed to operate the login password of supervisor. By satisfying FMT_MTD.1, FMT_SMF.1, FMT_SMR.1 ...
... the persons by FTP_ITC.1. FIA_UID.2 identifies the person who have the privileges. (4) Use trusted channels for Security Function. (3) Specification of the roles. All rights reserved. The supervisor and applicable MFP administrator are allowed to the protected assets of the users ... identification and authentication. FIA_ATD.1 and FIA_USB.1 manage the access procedures to operate the login password of administrator. Copyright (c) 2011 RICOH COMPANY, LTD. The MFP administrator is allowed to operate the login password of supervisor. By satisfying FMT_MTD.1, FMT_SMF.1, FMT_SMR.1 ...
Security Target
Page 76
...FMT_MTD.1 allows the MFP administrator to be stored in the HDD, and decrypts the data to manage the cryptographic keys. (4) Specification of the roles. FMT_SMF.1 performs the required Management Functions for the communication between the TOE and RC Gate are the security ... FIA_UID.1 FAU_GEN.1 FAU_STG.1 FAU_GEN.1 FAU_SAR.1 FCS_COP.1 Dependencies Not Satisfied in ST None None None None None None FCS_CKM.4 Copyright (c) 2011 RICOH COMPANY, LTD. Table 3334 : Results of Dependency Analysis of 91 (1) Generate appropriate cryptographic keys. All rights reserved. FCS_COP.1 encrypts the ...
...FMT_MTD.1 allows the MFP administrator to be stored in the HDD, and decrypts the data to manage the cryptographic keys. (4) Specification of the roles. FMT_SMF.1 performs the required Management Functions for the communication between the TOE and RC Gate are the security ... FIA_UID.1 FAU_GEN.1 FAU_STG.1 FAU_GEN.1 FAU_SAR.1 FCS_COP.1 Dependencies Not Satisfied in ST None None None None None None FCS_CKM.4 Copyright (c) 2011 RICOH COMPANY, LTD. Table 3334 : Results of Dependency Analysis of 91 (1) Generate appropriate cryptographic keys. All rights reserved. FCS_COP.1 encrypts the ...
Security Target
Page 79
...events shown in the audit log files to audit (audit log review). Page 78 of 91 7 TOE Summary Specification This section describes the TOE summary specification for the audit log are derived from RC Gate communication interface Table 30 Record of Management Function Date settings (year.../month/day), time settings (hour/minute) Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. The recorded audit log can be ...
...events shown in the audit log files to audit (audit log review). Page 78 of 91 7 TOE Summary Specification This section describes the TOE summary specification for the audit log are derived from RC Gate communication interface Table 30 Record of Management Function Date settings (year.../month/day), time settings (hour/minute) Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. The recorded audit log can be ...
Security Target
Page 86
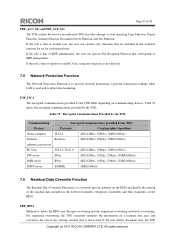
...is that of 91 FDP_ACC.1(b) and FDP_ACF.1(b) The TOE verifies the role for each normal user. FDP_RIP.1 Methods to overwrite specific patterns on the HDD. For sequential overwriting, the TOE constantly monitors the information on communicating devices. If the role is ... Function, Scanner Function, Document Server Function, and Fax Function. If the user deletes document data, the TOE Copyright (c) 2011 RICOH COMPANY, LTD. Table 39 : Encrypted Communications Provided by the TOE Communicating Encrypted communications provided by the TOE Devices Protocols Cryptographic Algorithms...
...is that of 91 FDP_ACC.1(b) and FDP_ACF.1(b) The TOE verifies the role for each normal user. FDP_RIP.1 Methods to overwrite specific patterns on the HDD. For sequential overwriting, the TOE constantly monitors the information on communicating devices. If the role is ... Function, Scanner Function, Document Server Function, and Fax Function. If the user deletes document data, the TOE Copyright (c) 2011 RICOH COMPANY, LTD. Table 39 : Encrypted Communications Provided by the TOE Communicating Encrypted communications provided by the TOE Devices Protocols Cryptographic Algorithms...