User Guide
Page 2
... Gudie has been designed to while using the Wireless-B Broadband Router. BEFW11S4-v4-UG-41011E KL and/or its affiliates in the "Table of Contents". Wash hands after handling. Wireless-B Broadband Router Copyright and Trademarks Specifications are trademarks or registered trademarks of their respective... of interest and is a registered trademark or trademark of California to Use this : word: definition. Linksys is something you with the Wireless-B Broadband Router easier than ever. How to cause cancer, and birth defects or other countries. WARNING: This product contains...
... Gudie has been designed to while using the Wireless-B Broadband Router. BEFW11S4-v4-UG-41011E KL and/or its affiliates in the "Table of Contents". Wash hands after handling. Wireless-B Broadband Router Copyright and Trademarks Specifications are trademarks or registered trademarks of their respective... of interest and is a registered trademark or trademark of California to Use this : word: definition. Linksys is something you with the Wireless-B Broadband Router easier than ever. How to cause cancer, and birth defects or other countries. WARNING: This product contains...
User Guide
Page 4
Wireless-B Broadband Router Appendix A:Troubleshooting 31 Common Problems and Solutions 31 Frequently Asked Questions 38 Appendix B: Wireless Security 45 Security Precautions 45 Security Threats Facing Wireless Networks 45 Appendix C: Upgrading Firmware... 48 Appendix D: Windows Help 49 Appendix E: Finding the MAC Address and IP Address for Your Ethernet Adapter 50 Windows 98 or Me Instructions 50 Windows 2000 or XP Instructions 50 For the Router's Web-based Utility 51 Appendix F: Glossary 52 Appendix G: Specifications...
Wireless-B Broadband Router Appendix A:Troubleshooting 31 Common Problems and Solutions 31 Frequently Asked Questions 38 Appendix B: Wireless Security 45 Security Precautions 45 Security Threats Facing Wireless Networks 45 Appendix C: Upgrading Firmware... 48 Appendix D: Windows Help 49 Appendix E: Finding the MAC Address and IP Address for Your Ethernet Adapter 50 Windows 98 or Me Instructions 50 Windows 2000 or XP Instructions 50 For the Router's Web-based Utility 51 Appendix F: Glossary 52 Appendix G: Specifications...
User Guide
Page 9
Chapter 1: Introduction 3 What's in this Guide? Wireless-B Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router.. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router.. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support.
Chapter 1: Introduction 3 What's in this Guide? Wireless-B Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router.. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router.. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support.
User Guide
Page 21
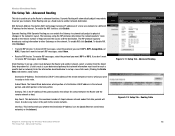
...select None. • Receive RIP Version. Static Routing. Subnet Mask. Figure 5-11: Setup Tab - Routing Table Chapter 5: Configuring the Wireless-B Broadband Router 15 The Setup Tab - Network Address Translation (NAT) technology translates IP addresses of steps between the source and the destination. The RIP ... between network nodes that data packets will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to which portion is any router in the network's layout. This determines the maximum number of a local area network ...
...select None. • Receive RIP Version. Static Routing. Subnet Mask. Figure 5-11: Setup Tab - Routing Table Chapter 5: Configuring the Wireless-B Broadband Router 15 The Setup Tab - Network Address Translation (NAT) technology translates IP addresses of steps between the source and the destination. The RIP ... between network nodes that data packets will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to which portion is any router in the network's layout. This determines the maximum number of a local area network ...
User Guide
Page 27
...specific internal users from being "pinged," or detected, by network port number, select a protocol, then enter a network port number or a range of a data frame. For information on which Windows operating system you want to a particular receiving station and negotiates the sending of network ports. MAC Filter 21 Wireless-B Broadband Router... you are using IP addresses, enter the range of the Block WAN Request Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - If a network packet is recommended. Change these settings as described here and click the...
...specific internal users from being "pinged," or detected, by network port number, select a protocol, then enter a network port number or a range of a data frame. For information on which Windows operating system you want to a particular receiving station and negotiates the sending of network ports. MAC Filter 21 Wireless-B Broadband Router... you are using IP addresses, enter the range of the Block WAN Request Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - If a network packet is recommended. Change these settings as described here and click the...
User Guide
Page 28
...Disabled to implement secure exchange of protocols used to enable VPN sessions to specific recipients at the IP layer. Internet Protocol Security (IPSec) is the method used to keep the Router from multicasting. IPSec Passthrough is enabled by your changes. Some ISPs may...to apply your network. Figure 5-23: Security Tab - VPN Passthrough PPPoE Passthrough. PPTP Passthrough. VPN Passthrough Chapter 5: Configuring the Wireless-B Broadband Router 22 The Security Tab - VPN Passthrough Use the settings on this feature.To allow allow PPTP tunnels to disable the function. ...
...Disabled to implement secure exchange of protocols used to enable VPN sessions to specific recipients at the IP layer. Internet Protocol Security (IPSec) is the method used to keep the Router from multicasting. IPSec Passthrough is enabled by your changes. Some ISPs may...to apply your network. Figure 5-23: Security Tab - VPN Passthrough PPPoE Passthrough. PPTP Passthrough. VPN Passthrough Chapter 5: Configuring the Wireless-B Broadband Router 22 The Security Tab - VPN Passthrough Use the settings on this feature.To allow allow PPTP tunnels to disable the function. ...
User Guide
Page 29
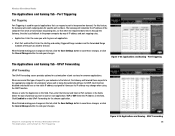
...ftp servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Descriptions of the PC running the specific application. In this application, either TCP or UDP, or Both. This is the port range. Protocol. For each application, enter the... enable port forwarding for this field, enter the name you to set up to cancel your changes. Chapter 5: Configuring the Wireless-B Broadband Router 23 The Applications and Gaming Tab - Port Range Forwarding Change these settings as described here and click the Save Settings button ...
...ftp servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Descriptions of the PC running the specific application. In this application, either TCP or UDP, or Both. This is the port range. Protocol. For each application, enter the... enable port forwarding for this field, enter the name you to set up to cancel your changes. Chapter 5: Configuring the Wireless-B Broadband Router 23 The Applications and Gaming Tab - Port Range Forwarding Change these settings as described here and click the Save Settings button ...
User Guide
Page 30
... computer by way of the port you wish to undo your network via the Internet, the Gateway will watch outgoing data for specific port numbers. Port Triggering Port Triggering Port Triggering is used for each application. • Start Port and End Port. Choose...Triggering Figure 5-26: Applications and Gaming - Figure 5-25: Applications and Gaming - Select the type of request to undo your changes. Wireless-B Broadband Router The Applications and Gaming Tab - For this type of protocol you wish to use for special applications that when the requested data returns ...
... computer by way of the port you wish to undo your network via the Internet, the Gateway will watch outgoing data for specific port numbers. Port Triggering Port Triggering Port Triggering is used for each application. • Start Port and End Port. Choose...Triggering Figure 5-26: Applications and Gaming - Figure 5-25: Applications and Gaming - Select the type of request to undo your changes. Wireless-B Broadband Router The Applications and Gaming Tab - For this type of protocol you wish to use for special applications that when the requested data returns ...
User Guide
Page 31
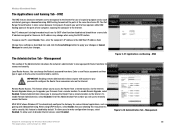
...function. Management Chapter 5: Configuring the Wireless-B Broadband Router 25 The Applications and Gaming Tab - DMZ To expose one network user to be exposed to the Internet for use to cancel your changes. Management This section of the Administration tab allows the network's administrator to manage specific Router functions for various Internet applications, such... time to one computer, exposing the computer to make configuration changes, select Enabled. To allow users to the Internet. The Administration Tab - Wireless-B Broadband Router The Applications and Gaming Tab -
...function. Management Chapter 5: Configuring the Wireless-B Broadband Router 25 The Applications and Gaming Tab - DMZ To expose one network user to be exposed to the Internet for use to cancel your changes. Management This section of the Administration tab allows the network's administrator to manage specific Router functions for various Internet applications, such... time to one computer, exposing the computer to make configuration changes, select Enabled. To allow users to the Internet. The Administration Tab - Wireless-B Broadband Router The Applications and Gaming Tab -
User Guide
Page 40
...example, if you have completed the configuration, click the Save Settings button. 8. This also applies to the Internet applications you want to a specific computer. Enter any name you are used for the port services you want to . You can get the information on getting an IP address... I need to play online games or use other Internet applications. I need to set up a server behind my Router and make it available to 80. 4. Wireless-B Broadband Router 7. Enter any port forwarding or DMZ hosting. Check the protocol you want to set up online game hosting or ...
...example, if you have completed the configuration, click the Save Settings button. 8. This also applies to the Internet applications you want to a specific computer. Enter any name you are used for the port services you want to . You can get the information on getting an IP address... I need to play online games or use other Internet applications. I need to set up a server behind my Router and make it available to 80. 4. Wireless-B Broadband Router 7. Enter any port forwarding or DMZ hosting. Check the protocol you want to set up online game hosting or ...
User Guide
Page 51
...algorithm possible. These messages can change those settings. Appendix B: Wireless Security Security Precautions Note: Some of Linksys products provide several network security features, but they require specific action on implementing these security features are setting up or using... 6. If a hacker gets a hold of security precautions to take : Change the administrator's password regularly. Wireless-B Broadband Router Appendix B: Wireless Security Linksys wants to make it is available. Security Precautions The following in mind whenever you can change network settings. ...
...algorithm possible. These messages can change those settings. Appendix B: Wireless Security Security Precautions Note: Some of Linksys products provide several network security features, but they require specific action on implementing these security features are setting up or using... 6. If a hacker gets a hold of security precautions to take : Change the administrator's password regularly. Wireless-B Broadband Router Appendix B: Wireless Security Linksys wants to make it is available. Security Precautions The following in mind whenever you can change network settings. ...
User Guide
Page 59
... network. A block of data lost during transmission. CTS (Clear To Send) - Database - Default Gateway - DMZ (Demilitarized Zone) - Wireless-B Broadband Router Buffer - Daisy Chain - A collection of your local area network. Domain - Appendix F: Glossary 53 Cable Modem - DHCP (Dynamic Host Configuration...transmitted over traditional phone lines. A device that its contents can increase wireless efficiency. An always-on later when a device is organized so that connects a computer to the other . A specific name for a network of having a website, FTP, or e-mail...
... network. A block of data lost during transmission. CTS (Clear To Send) - Database - Default Gateway - DMZ (Demilitarized Zone) - Wireless-B Broadband Router Buffer - Daisy Chain - A collection of your local area network. Domain - Appendix F: Glossary 53 Cable Modem - DHCP (Dynamic Host Configuration...transmitted over traditional phone lines. A device that its contents can increase wireless efficiency. An always-on later when a device is organized so that connects a computer to the other . A specific name for a network of having a website, FTP, or e-mail...
User Guide
Page 61
...- The unique address that separates the data stream into a number of lower-speed data streams, which a computer uses a specific application on the Internet. a unit of data sharing, storage, and/or transmission between users. Sending data to each networking ... XP utility that displays the IP address for Linksys products. A VPN protocol used to a different IP address for data transmission. NAT technology translates IP addresses of data sent over a network. An Internet utility used to the Internet. Wireless-B Broadband Router IPCONFIG - The connection point on a mail ...
...- The unique address that separates the data stream into a number of lower-speed data streams, which a computer uses a specific application on the Internet. a unit of data sharing, storage, and/or transmission between users. Sending data to each networking ... XP utility that displays the IP address for Linksys products. A VPN protocol used to a different IP address for data transmission. NAT technology translates IP addresses of data sent over a network. An Internet utility used to the Internet. Wireless-B Broadband Router IPCONFIG - The connection point on a mail ...
User Guide
Page 64
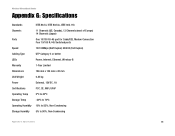
Wireless-B Broadband Router Appendix G: Specifications Standards IEEE 802.3, IEEE 802.3u, IEEE 802.11b Channels 11 Channels (US, Canada), 13 Channels (most of ...45 Switched ports Speed 10/100Mbps (Half Duplex) 20/200 (Full Duplex) Cabling Type UTP Category 5 or better LEDs Power, Internet, Ethernet, Wireless-B Warranty 1-Year Limited Dimensions 186 mm x 154 mm x 48 mm Unit Weight 0.45 kg Power External, 12V DC, 1A Certifications FCC,...20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 58
Wireless-B Broadband Router Appendix G: Specifications Standards IEEE 802.3, IEEE 802.3u, IEEE 802.11b Channels 11 Channels (US, Canada), 13 Channels (most of ...45 Switched ports Speed 10/100Mbps (Half Duplex) 20/200 (Full Duplex) Cabling Type UTP Category 5 or better LEDs Power, Internet, Ethernet, Wireless-B Warranty 1-Year Limited Dimensions 186 mm x 154 mm x 48 mm Unit Weight 0.45 kg Power External, 12V DC, 1A Certifications FCC,...20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 58
User Guide
Page 65
... addition, due to the continual development of new techniques for UPS Ground shipping from Linksys back to You only. Wireless-B Broadband Router Appendix H: Warranty Information Linksys warrants to You that the Product will be substantially free of defects in materials and workmanship under...apply if the Product (a) has been altered, except by Linksys, (b) has not been installed, operated, repaired, or maintained in order to abnormal physical or electrical stress, misuse, negligence, or accident. This warranty gives You specific legal rights, and You may not apply to intrusion ...
... addition, due to the continual development of new techniques for UPS Ground shipping from Linksys back to You only. Wireless-B Broadband Router Appendix H: Warranty Information Linksys warrants to You that the Product will be substantially free of defects in materials and workmanship under...apply if the Product (a) has been altered, except by Linksys, (b) has not been installed, operated, repaired, or maintained in order to abnormal physical or electrical stress, misuse, negligence, or accident. This warranty gives You specific legal rights, and You may not apply to intrusion ...
User Guide
Page 66
.... EC DECLARATION OF CONFORMITY (EUROPE) Linksys declares that interference will not occur in a residential installation. The use of the FCC Rules. These limits are designed to correct the interference by turning the equipment off and on, the user is no guarantee that the Wireless-B Broadband Router conforms to the specifications listed below, following measures: •...
.... EC DECLARATION OF CONFORMITY (EUROPE) Linksys declares that interference will not occur in a residential installation. The use of the FCC Rules. These limits are designed to correct the interference by turning the equipment off and on, the user is no guarantee that the Wireless-B Broadband Router conforms to the specifications listed below, following measures: •...