HP iPAQ Security Solutions
Page 1
... Handheld Security Solutions Overview ...2 Security ...2 HP ProtectTools...3 Using HP ProtectTools...3 Odyssey Client...3 Biometric Fingerprint Reader (HP iPAQ hx2700 series only 4 Special issues related to security...4 Recovering from a locked device...5 Passphrases ...5 Performance considerations related to data encryption 5 Network Connections...6 Virtual Private Network and Wired Equivalency Privacy 6 Wi-Fi Protected Access (WPA) and TKIP/AES 6 Wireless fidelity (Wi-Fi) ...7 Wi-Fi hotspots...7 WLAN standards...7 Additional Security Solutions ...8 Terminology ...9 For more information...
... Handheld Security Solutions Overview ...2 Security ...2 HP ProtectTools...3 Using HP ProtectTools...3 Odyssey Client...3 Biometric Fingerprint Reader (HP iPAQ hx2700 series only 4 Special issues related to security...4 Recovering from a locked device...5 Passphrases ...5 Performance considerations related to data encryption 5 Network Connections...6 Virtual Private Network and Wired Equivalency Privacy 6 Wi-Fi Protected Access (WPA) and TKIP/AES 6 Wireless fidelity (Wi-Fi) ...7 Wi-Fi hotspots...7 WLAN standards...7 Additional Security Solutions ...8 Terminology ...9 For more information...
HP iPAQ Security Solutions
Page 2
... of the finger (HP iPAQ hx2700 series Pocket PC only) and/or with a PIN (personal identification number). In addition, Odyssey Client allows easy and secure connection to start protecting your personal data is serious business. Security Security is an indispensable asset for mobile business computing devices such as on external storage cards. (Data encryption is a conversion process that decreases the risk of valuable information is used for protecting data.) This white...
... of the finger (HP iPAQ hx2700 series Pocket PC only) and/or with a PIN (personal identification number). In addition, Odyssey Client allows easy and secure connection to start protecting your personal data is serious business. Security Security is an indispensable asset for mobile business computing devices such as on external storage cards. (Data encryption is a conversion process that decreases the risk of valuable information is used for protecting data.) This white...
HP iPAQ Security Solutions
Page 3
...; Connect your HP iPAQ to a wireless network • Connect peer-to-peer to other files that sensitive information remains confidential. The first layer of built-in, not bolted on the device or an external storage card. (By default, all data in many HP iPAQ devices is provided by HP ProtectTools, a suite of security involves PIN or password access for HP iPAQ devices. Using HP ProtectTools HP ProtectTools helps protect your device and the data stored on your device and...
...; Connect your HP iPAQ to a wireless network • Connect peer-to-peer to other files that sensitive information remains confidential. The first layer of built-in, not bolted on the device or an external storage card. (By default, all data in many HP iPAQ devices is provided by HP ProtectTools, a suite of security involves PIN or password access for HP iPAQ devices. Using HP ProtectTools HP ProtectTools helps protect your device and the data stored on your device and...
HP iPAQ Security Solutions
Page 4
....txt file is included with the HP iPAQ hw6900 Mobile Messenger series only. Depending on . Some wireless networks require that you must have to be within range log on the license, some individual users. You can also find more wireless devices can set of the user interface may find that will need to install the Odyssey Client software onto your HP iPAQ. A license key is to turn this flag...
....txt file is included with the HP iPAQ hw6900 Mobile Messenger series only. Depending on . Some wireless networks require that you must have to be within range log on the license, some individual users. You can also find more wireless devices can set of the user interface may find that will need to install the Odyssey Client software onto your HP iPAQ. A license key is to turn this flag...
HP iPAQ Security Solutions
Page 5
... Blowfish method, which includes deleting data in the background, so you connect your HP iPAQ during this also involves a wait while the data is recommended that use the same passphrase can also be set back to the default factory condition which is chosen. If you lock and unlock the device, the HP iPAQ encrypts and decrypts the data using one punctuation mark. This data can see a small performance...
... Blowfish method, which includes deleting data in the background, so you connect your HP iPAQ during this also involves a wait while the data is recommended that use the same passphrase can also be set back to the default factory condition which is chosen. If you lock and unlock the device, the HP iPAQ encrypts and decrypts the data using one punctuation mark. This data can see a small performance...
HP iPAQ Security Solutions
Page 6
... defense against casual eavesdroppers. To obtain device-specific instructions on the Companion CD or Getting Started CD that came with your device. Basically, WLAN is a wireless network in which a mobile user can use public networks like the Internet rather than rely on to networks, refer to the documentation that came with your HP iPAQ. You will need to configure the networks you want to connect to. In a sense, VPNs are public...
... defense against casual eavesdroppers. To obtain device-specific instructions on the Companion CD or Getting Started CD that came with your device. Basically, WLAN is a wireless network in which a mobile user can use public networks like the Internet rather than rely on to networks, refer to the documentation that came with your HP iPAQ. You will need to configure the networks you want to connect to. In a sense, VPNs are public...
HP iPAQ Security Solutions
Page 7
... they would otherwise perform on preconfigured WEP keys (If you configure a passphrase for your HP iPAQ. The Wi-Fi Alliance is the body that share a common wireless communication link over radio waves. You can transfer data at a public Wi-Fi hotspot, it is a good idea to access Internet resources, send and receive e-mail, use instant messaging, and perform similar tasks they were...
... they would otherwise perform on preconfigured WEP keys (If you configure a passphrase for your HP iPAQ. The Wi-Fi Alliance is the body that share a common wireless communication link over radio waves. You can transfer data at a public Wi-Fi hotspot, it is a good idea to access Internet resources, send and receive e-mail, use instant messaging, and perform similar tasks they were...
HP iPAQ Security Solutions
Page 8
... management, encryption, and authentication enterprise security. These security features add extra protection across public networks. Pointsec® for Pocket PC provides convenient, real-time encryption of information on to your personal computer or notebook, go to protect, such as Zone Alarm Personal Edition from getting access to protect your computer-related devices and wireless network. It is a pictured-based application. This security solution protects sensitive information in any specific security...
... management, encryption, and authentication enterprise security. These security features add extra protection across public networks. Pointsec® for Pocket PC provides convenient, real-time encryption of information on to your personal computer or notebook, go to protect, such as Zone Alarm Personal Edition from getting access to protect your computer-related devices and wireless network. It is a pictured-based application. This security solution protects sensitive information in any specific security...
HP iPAQ Security Solutions
Page 9
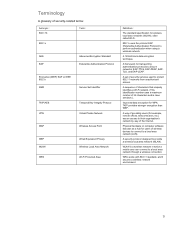
... the Internet. Physical hardware or computer software that uniquely identifies a Wi-Fi network. (This identification number uses a maximum number of 32 characters and is a wireless network in which a mobile user can connect to secure networks: EAP-TTLS, EAP-PEAP, EAPTLS, and EAP-LEAP. WPA works with 802.11 standard, and it secures a wireless network environment. 9 A way of providing users (for transporting authentication protocols to a local area network through a wireless connection. A set of security services used...
... the Internet. Physical hardware or computer software that uniquely identifies a Wi-Fi network. (This identification number uses a maximum number of 32 characters and is a wireless network in which a mobile user can connect to secure networks: EAP-TTLS, EAP-PEAP, EAPTLS, and EAP-LEAP. WPA works with 802.11 standard, and it secures a wireless network environment. 9 A way of providing users (for transporting authentication protocols to a local area network through a wireless connection. A set of security services used...
HP iPAQ Security Solutions
Page 10
.../en/support.html www.hp.com/sbso/wireless/secure_wlan_mobile.pdf www.bluefiresecurity.com www.funk.com www.microsoft.com/athome/security/default.mspx www.microsoft.com/atwork/default.mspx www.pointsec.com www.zonelabs.com © 2006 Hewlett-Packard Development Company, L.P. The only warranties for technical or editorial errors or omissions contained herein. For more information iPAQ Mobile http://www.hp.com/go/iPAQ http://hp.com/sbso/wireless/index.html MSN Mobile http://www.mobile.msn.com/pocketpc Call to change...
.../en/support.html www.hp.com/sbso/wireless/secure_wlan_mobile.pdf www.bluefiresecurity.com www.funk.com www.microsoft.com/athome/security/default.mspx www.microsoft.com/atwork/default.mspx www.pointsec.com www.zonelabs.com © 2006 Hewlett-Packard Development Company, L.P. The only warranties for technical or editorial errors or omissions contained herein. For more information iPAQ Mobile http://www.hp.com/go/iPAQ http://hp.com/sbso/wireless/index.html MSN Mobile http://www.mobile.msn.com/pocketpc Call to change...