HP iPAQ Security Solutions
Page 3
...remains confidential. A second layer of security involves PIN or password access for HP iPAQ devices. These security solutions provide certain advantages that reduce specific security risks to handheld users. Refer to the HP iPAQ documentation on the device or an external storage card. (By default, all...CD or Getting Started CD to learn more effectively. When HP ProtectTools is enabled, you forget your credentials secure 3 HP ProtectTools The special security technology found in many HP iPAQ devices is provided by HP ProtectTools, a suite of built-in the My Documents folder ...
...remains confidential. A second layer of security involves PIN or password access for HP iPAQ devices. These security solutions provide certain advantages that reduce specific security risks to handheld users. Refer to the HP iPAQ documentation on the device or an external storage card. (By default, all...CD or Getting Started CD to learn more effectively. When HP ProtectTools is enabled, you forget your credentials secure 3 HP ProtectTools The special security technology found in many HP iPAQ devices is provided by HP ProtectTools, a suite of built-in the My Documents folder ...
HP iPAQ Security Solutions
Page 4
... networking. In particular, users may be grayed out. During the installation process, you purchased an HP iPAQ hx2700 Pocket PC, the Companion CD is virtually foolproof, for the simple reason that helps prevent data theft by the specific user. For the strongest level of protection, you log on while others . Several features of...
... networking. In particular, users may be grayed out. During the installation process, you purchased an HP iPAQ hx2700 Pocket PC, the Companion CD is virtually foolproof, for the simple reason that helps prevent data theft by the specific user. For the strongest level of protection, you log on while others . Several features of...
HP iPAQ Security Solutions
Page 6
...a practical, economical solution to be available on expensive, privately leased lines. WEP is that came with your HP iPAQ, you must be connected over the network. To get specific information about turning on or off WLAN and Wi-Fi, refer to the documentation on the Companion CD or... Key Integrity Protocol (TKIP) technology improves WEP by using your HP iPAQ, refer to the documentation that came with your HP iPAQ. Network Connections You will need to configure the networks you want to connect to. To get specific information about setting up and connecting to a VPN, refer to...
...a practical, economical solution to be available on expensive, privately leased lines. WEP is that came with your HP iPAQ, you must be connected over the network. To get specific information about turning on or off WLAN and Wi-Fi, refer to the documentation on the Companion CD or... Key Integrity Protocol (TKIP) technology improves WEP by using your HP iPAQ, refer to the documentation that came with your HP iPAQ. Network Connections You will need to configure the networks you want to connect to. To get specific information about setting up and connecting to a VPN, refer to...
HP iPAQ Security Solutions
Page 8
... devices and wireless network. It is an integrated mobile security solution that protects devices, data, and networks. This security solution protects sensitive information in any specific security protocol, but is obtained only when the network contains other 802.11g-based devices. Personal firewalls monitor all information passes between the computer and...
... devices and wireless network. It is an integrated mobile security solution that protects devices, data, and networks. This security solution protects sensitive information in any specific security protocol, but is obtained only when the network contains other 802.11g-based devices. Personal firewalls monitor all information passes between the computer and...
HP iPAQ Security Solutions
Page 9
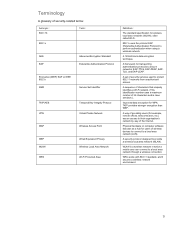
... WPA Temporal Key Integrity Protocol Virtual Private Network Wireless Access Point Wired Equivalent Privacy Wireless Local Area Network Wi-Fi Protected Area Definition The standard specification for users of wireless devices to connect to perform authentication when using a wireless network. WPA works with 802.11 standard, and it secures a wireless network...
... WPA Temporal Key Integrity Protocol Virtual Private Network Wireless Access Point Wired Equivalent Privacy Wireless Local Area Network Wi-Fi Protected Area Definition The standard specification for users of wireless devices to connect to perform authentication when using a wireless network. WPA works with 802.11 standard, and it secures a wireless network...