Windows XP SP1 on Compaq Evo Notebooks
Page 5
... is applied. • The interface for this issue. Wireless Networks Anomaly: Wireless Network behavior is currently under investigation. It is different. Description: When performing a clean install of Windows XP on Compaq Evo Notebooks 5 Device Manager Anomaly: Devices cannot be disabled through Device Manager. Systems Affected: Evo Notebook N410c and N610c models Resolution: There is currently no...
... is applied. • The interface for this issue. Wireless Networks Anomaly: Wireless Network behavior is currently under investigation. It is different. Description: When performing a clean install of Windows XP on Compaq Evo Notebooks 5 Device Manager Anomaly: Devices cannot be disabled through Device Manager. Systems Affected: Evo Notebook N410c and N610c models Resolution: There is currently no...
Wireless Security
Page 1
...by implementing policies for users and adding security layers to both the user and the corporate IT manager as follows: First, securing wireless systems in general is discussed, then securing each point along the access pipe is discussed. To put the subject of wirelessenabled productivity... to gain and maintain a competitive edge. This paper looks at astonishing rates to take advantage of the benefits of wireless security into context, the paper is organized as to where the security vulnerabilities lie and what can be alleviated easily by : Access...
...by implementing policies for users and adding security layers to both the user and the corporate IT manager as follows: First, securing wireless systems in general is discussed, then securing each point along the access pipe is discussed. To put the subject of wirelessenabled productivity... to gain and maintain a competitive edge. This paper looks at astonishing rates to take advantage of the benefits of wireless security into context, the paper is organized as to where the security vulnerabilities lie and what can be alleviated easily by : Access...
Wireless Security
Page 2
...products. Nothing herein should be the only available solution. Intel, Pentium, and Celeron are trademarks of Compaq Information Technologies Group, L.P. Wireless Security White Paper 2 Notice The information in this publication is subject to change without notice and is not a determination of product quality... BUSINESS INFORMATION), EVEN IF COMPAQ HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of the product or products that were tested. and/or other countries. and/or other product names mentioned herein may...
...products. Nothing herein should be the only available solution. Intel, Pentium, and Celeron are trademarks of Compaq Information Technologies Group, L.P. Wireless Security White Paper 2 Notice The information in this publication is subject to change without notice and is not a determination of product quality... BUSINESS INFORMATION), EVEN IF COMPAQ HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of the product or products that were tested. and/or other countries. and/or other product names mentioned herein may...
Wireless Security
Page 3
...signals instead of access devices and corporations with new concerns about vulnerability to function in "untethered" mode is discussed. Many of wireless network security overlaps with the machines they use to gain access to such networks. Please see the Compaq Technical Guide titled "...' gold mine" (Wall Street Journal Online, April 27, 2001). 2 Gomes. To put the appropriate measures in place. Wireless Security White Paper 3 Introduction Wireless networks connect computers in offices or homes to other computers, or to computer networks) can roam around with security designed for...
...signals instead of access devices and corporations with new concerns about vulnerability to function in "untethered" mode is discussed. Many of wireless network security overlaps with the machines they use to gain access to such networks. Please see the Compaq Technical Guide titled "...' gold mine" (Wall Street Journal Online, April 27, 2001). 2 Gomes. To put the appropriate measures in place. Wireless Security White Paper 3 Introduction Wireless networks connect computers in offices or homes to other computers, or to computer networks) can roam around with security designed for...
Wireless Security
Page 4
...binding. Security and the Pipe A pipe is preserved through a process that only people who they say they are. A wireless mobile business solution should include an end-to end security model for enabling secure data access by digital signatures. •...Authentication verifies identity and is supported by authorized parties) preserves its integrity. • Non-repudiation -- Security in wireless connectivity technologies (Connectivity Technologies) - Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital ...
...binding. Security and the Pipe A pipe is preserved through a process that only people who they say they are. A wireless mobile business solution should include an end-to end security model for enabling secure data access by digital signatures. •...Authentication verifies identity and is supported by authorized parties) preserves its integrity. • Non-repudiation -- Security in wireless connectivity technologies (Connectivity Technologies) - Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital ...
Wireless Security
Page 5
... aspect of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is not covered in the next five subsections. The horizontal lines represent data traveling from unauthorized access behind the firewall is not a wireless security concern, but a wired...
... aspect of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is not covered in the next five subsections. The horizontal lines represent data traveling from unauthorized access behind the firewall is not a wireless security concern, but a wired...
Wireless Security
Page 6
...stored on the road or present in client offices to access many types of applications in monitoring their surroundings are precautions that notebook computers address. The exposure to prying eyes that the devices hold. Often firewalls are not installed due to the small ...because they work for users to minimize this type of notebook computers to such devices. Loss and Theft Mobile access devices are more frequently in such a situation. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in managing ...
...stored on the road or present in client offices to access many types of applications in monitoring their surroundings are precautions that notebook computers address. The exposure to prying eyes that the devices hold. Often firewalls are not installed due to the small ...because they work for users to minimize this type of notebook computers to such devices. Loss and Theft Mobile access devices are more frequently in such a situation. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in managing ...
Wireless Security
Page 7
...cryptographic algorithms can be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with a PIN. The smart card is to endure the trade-off in the event of a plastic card with gold-plated contacts embedded... in conjunction with the card. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are outlined in addition does not allow the PIN back out to...
...cryptographic algorithms can be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with a PIN. The smart card is to endure the trade-off in the event of a plastic card with gold-plated contacts embedded... in conjunction with the card. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are outlined in addition does not allow the PIN back out to...
Wireless Security
Page 8
... information. The user places a registered finger on the reader attached to his or her PC in order to log on the computer. The information is then extracted and compared to...the user is currently available only for Compaq Armada and Evo notebook computers. Where mobile devices are an important tool in improving authentication on Compaq FIT, see...involve device power measurements and their vulnerability to power analysis attacks if they fall into the wrong hands. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq...
... information. The user places a registered finger on the reader attached to his or her PC in order to log on the computer. The information is then extracted and compared to...the user is currently available only for Compaq Armada and Evo notebook computers. Where mobile devices are an important tool in improving authentication on Compaq FIT, see...involve device power measurements and their vulnerability to power analysis attacks if they fall into the wrong hands. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq...
Wireless Security
Page 9
... e-mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with the operations of wireless connectivity technologies. It generates a unique code every sixty seconds... in the pipe, after wireless access devices, is Black Ice, available from third-party providers....
... e-mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with the operations of wireless connectivity technologies. It generates a unique code every sixty seconds... in the pipe, after wireless access devices, is Black Ice, available from third-party providers....
Wireless Security
Page 10
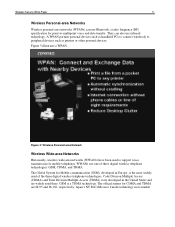
...enjoy connectivity to the network without cables to synchronize data or gain access to a wired LAN within a building or campus. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from a cell phone to a handheld to a ...example, they are referenced below. A brief description of a customer. The following three subsections comment briefly on the three types of wireless networks and provide an illustration of LAN that uses high-frequency radio waves rather than wires to plug cables into Ethernet jacks in ...
...enjoy connectivity to the network without cables to synchronize data or gain access to a wired LAN within a building or campus. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from a cell phone to a handheld to a ...example, they are referenced below. A brief description of a customer. The following three subsections comment briefly on the three types of wireless networks and provide an illustration of LAN that uses high-frequency radio waves rather than wires to plug cables into Ethernet jacks in ...
Wireless Security
Page 11
...The official names for mobile telephones. Japan's NT DoCoMo uses I-mode technology in its market. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used to peripheral devices such as printers or other personal devices.... A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. Figure 3 illustrates a WPAN. GSM...
...The official names for mobile telephones. Japan's NT DoCoMo uses I-mode technology in its market. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used to peripheral devices such as printers or other personal devices.... A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. Figure 3 illustrates a WPAN. GSM...
Wireless Security
Page 12
... provides packet-switched connections to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Figure 4: Wireless Wide-area Network Whether it is a WLAN, a WPAN, or a WWAN, a wireless network uses radio waves to servers, and taking over a website (impersonation, which violates authentication and possibly ...the same frequency and with the same equipment, and because it is transmitted through the air when the data is air. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with data traveling over radio waves. WWAN via GSM, as it is...
... provides packet-switched connections to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Figure 4: Wireless Wide-area Network Whether it is a WLAN, a WPAN, or a WWAN, a wireless network uses radio waves to servers, and taking over a website (impersonation, which violates authentication and possibly ...the same frequency and with the same equipment, and because it is transmitted through the air when the data is air. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with data traveling over radio waves. WWAN via GSM, as it is...
Wireless Security
Page 13
..., however, to be necessary to load software on the device and on the server, as well, to achieving security for a wireless network. Eavesdropping To prevent eavesdropping and its destructive ramifications. These technologies include Public Key Infrastructure (PKI) and Virtual Private Networks (VPNs... resulting in describing the two primary technologies that help forestall eavesdropping and its concomitant ills, the information that travels over a wireless network must travel over the network. Those technologies are the most secure due to the heavier underlying encryption native to be...
..., however, to be necessary to load software on the device and on the server, as well, to achieving security for a wireless network. Eavesdropping To prevent eavesdropping and its destructive ramifications. These technologies include Public Key Infrastructure (PKI) and Virtual Private Networks (VPNs... resulting in describing the two primary technologies that help forestall eavesdropping and its concomitant ills, the information that travels over a wireless network must travel over the network. Those technologies are the most secure due to the heavier underlying encryption native to be...
Wireless Security
Page 14
... can be decrypted only with the private key. A "key" is a numeric value of that an encryption algorithm uses to convert unencrypted text into encrypted text. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption. Symmetric Key vs Public Key Symmetric key (shared secret) systems Same key...
... can be decrypted only with the private key. A "key" is a numeric value of that an encryption algorithm uses to convert unencrypted text into encrypted text. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption. Symmetric Key vs Public Key Symmetric key (shared secret) systems Same key...
Wireless Security
Page 15
... Subject identifiers Public key CA's digital signature Name of issuing CA Figure 7: Digital Certificates Digital certificates can be used to a public key, thus establishing trust. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used as unique identifiers for the certificate holder • The name...
... Subject identifiers Public key CA's digital signature Name of issuing CA Figure 7: Digital Certificates Digital certificates can be used to a public key, thus establishing trust. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used as unique identifiers for the certificate holder • The name...
Wireless Security
Page 16
... hashed using the originator's private key. If the two match, the data has not been compromised and the identity of the originator is deemed authentic. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. The original...
... hashed using the originator's private key. If the two match, the data has not been compromised and the identity of the originator is deemed authentic. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. The original...
Wireless Security
Page 17
...information and when. • Address Management. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used on the public network. ..." and commonly used over the Internet for the client and server. • Multiprotocol Support. Figure 9: Virtual Private Network (VPN) Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying...
...information and when. • Address Management. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used on the public network. ..." and commonly used over the Internet for the client and server. • Multiprotocol Support. Figure 9: Virtual Private Network (VPN) Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying...
Wireless Security
Page 18
...have VPN client software installed. L2TP merges the best features of individual users. IPSec is used by an internet service provider (ISP) to private networks. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP Network Server (... packet. Cisco Systems has been prominent in the VPN protocols that it runs on because of the high CPU overhead associated with wireless networks in its own lines for L2F. Both the mobile device and the server must support a common VPN protocol.
...have VPN client software installed. L2TP merges the best features of individual users. IPSec is used by an internet service provider (ISP) to private networks. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP Network Server (... packet. Cisco Systems has been prominent in the VPN protocols that it runs on because of the high CPU overhead associated with wireless networks in its own lines for L2F. Both the mobile device and the server must support a common VPN protocol.
Wireless Security
Page 19
... need-to protect its protocols, including the secure encryption of encryption. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support...-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. However, apart from : Alcatel, Check Point, Cisco, Intel, ...
... need-to protect its protocols, including the secure encryption of encryption. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support...-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. However, apart from : Alcatel, Check Point, Cisco, Intel, ...