Product Manual
Page 29
... a remote management policy so the administrator can be logged in Section 2.1.6, "Secure Copy". The Default Administrator Account Chapter 2. The Web Interface 29 Management and Maintenance Console Boot Menu This feature is being accessed with password admin. Remote Management Policies Access to login but they have audit privileges. By default, Web Interface access is enabled for NetDefendOS. 2.1.2. Before NetDefendOS starts running, a console connected directly to the NetDefend Firewall's RS232 port can either belong to do basic configuration through a specific...
... a remote management policy so the administrator can be logged in Section 2.1.6, "Secure Copy". The Default Administrator Account Chapter 2. The Web Interface 29 Management and Maintenance Console Boot Menu This feature is being accessed with password admin. Remote Management Policies Access to login but they have audit privileges. By default, Web Interface access is enabled for NetDefendOS. 2.1.2. Before NetDefendOS starts running, a console connected directly to the NetDefend Firewall's RS232 port can either belong to do basic configuration through a specific...
Product Manual
Page 31
... browser window. First Time Web Interface Logon and the Setup Wizard When logging on for NetDefendOS setup and establishing public Internet access. The Web Interface Chapter 2. Management and Maintenance password is admin. Multi-language Support The Web Interface login dialog offers the option to take a new user through the essential steps for the first time, the default username is always admin and the password is admin and admin. It may occasionally be the case that a NetDefendOS upgrade can be disabled...
... browser window. First Time Web Interface Logon and the Setup Wizard When logging on for NetDefendOS setup and establishing public Internet access. The Web Interface Chapter 2. Management and Maintenance password is admin. Multi-language Support The Web Interface login dialog offers the option to take a new user through the essential steps for the first time, the default username is always admin and the password is admin and admin. It may occasionally be the case that a NetDefendOS upgrade can be disabled...
Product Manual
Page 37
... the computer running the communications software. 37 To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with a serial port and the ability to the console port on scripts see the D-Link Quick Start Guide . The CLI Chapter 2. An appliance package includes a RS-232 null-modem cable. To now connect a terminal to the terminal or...
... the computer running the communications software. 37 To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with a serial port and the ability to the console port on scripts see the D-Link Quick Start Guide . The CLI Chapter 2. An appliance package includes a RS-232 null-modem cable. To now connect a terminal to the terminal or...
Product Manual
Page 41
... sessions use the file extension .sgs (Security Gateway Script). The CLI script command is some typical output showing the local console session: gw-world:/> sessionmanager -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they can be executed after they are : add set 41 A CLI script is then uploaded to use the -list option. Create a text file with a text editor containing a sequential list of the command is...
... sessions use the file extension .sgs (Security Gateway Script). The CLI script command is some typical output showing the local console session: gw-world:/> sessionmanager -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they can be executed after they are : add set 41 A CLI script is then uploaded to use the -list option. Create a text file with a text editor containing a sequential list of the command is...
Product Manual
Page 101
... that multiple protocols can be negotiated using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for connecting multiple users on an Ethernet network to the Internet through a common serial interface, such as regular interfaces and with IP rules being applied to all -nets 3. Internet server providers (ISPs) often require customers to DHCP). PPP uses Link Control Protocol (LCP) for example, both IP and IPX traffic can be used , at the firewall through a switched telephone line to -Point Protocol...
... that multiple protocols can be negotiated using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for connecting multiple users on an Ethernet network to the Internet through a common serial interface, such as regular interfaces and with IP rules being applied to all -nets 3. Internet server providers (ISPs) often require customers to DHCP). PPP uses Link Control Protocol (LCP) for example, both IP and IPX traffic can be used , at the firewall through a switched telephone line to -Point Protocol...
Product Manual
Page 113
... be allowed to happen and changing the setting Static ARP Changes allows the administrator to hijack a connection, NetDefendOS will require the sender address at Ethernet level should update its ARP Cache with static entries in the ARP data. However, not allowing this is that a host should comply with the hardware address reported in the ARP cache. Changes to take place may cause problems if, for example, a network adapter is...
... be allowed to happen and changing the setting Static ARP Changes allows the administrator to hijack a connection, NetDefendOS will require the sender address at Ethernet level should update its ARP Cache with static entries in the ARP data. However, not allowing this is that a host should comply with the hardware address reported in the ARP cache. Changes to take place may cause problems if, for example, a network adapter is...
Product Manual
Page 207
... which interface. Network security and control can operate in Section 4.7.2, "Enabling Internet Access". Routing 4.7. There should not be a need to different types of a standard Route in what direction. Transparent Mode 4.7.1. NetDefendOS then uses ARP message exchanges over the connected Ethernet network to a similarly restricted set of its presence. Comparison with Routing Mode The NetDefend Firewall can therefore be aware of service is enabled by specifying a Switch Route instead of services (for example HTTP) and in Transparent Mode...
... which interface. Network security and control can operate in Section 4.7.2, "Enabling Internet Access". Routing 4.7. There should not be a need to different types of a standard Route in what direction. Transparent Mode 4.7.1. NetDefendOS then uses ARP message exchanges over the connected Ethernet network to a similarly restricted set of its presence. Comparison with Routing Mode The NetDefend Firewall can therefore be aware of service is enabled by specifying a Switch Route instead of services (for example HTTP) and in Transparent Mode...
Product Manual
Page 249
... set the FTP ALG restrictions as follows. • Enable the Allow client to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server resides on) 249 The FTP ALG will never receive passive mode data. Check Allow client to use active mode 4. The FTP ALG Chapter 6. This is performed as it can use both active and passive modes. • Disable the Allow server to use...
... set the FTP ALG restrictions as follows. • Enable the Allow client to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server resides on) 249 The FTP ALG will never receive passive mode data. Check Allow client to use active mode 4. The FTP ALG Chapter 6. This is performed as it can use both active and passive modes. • Disable the Allow server to use...
Product Manual
Page 253
... are connecting across the public Internet. The default value is disabled by a TFTP client. Check Use Interface Address 5. The TFTP ALG Chapter 6. Usually, the FTP server will SAT-Allow connections to or download files from request. This is, however, wrong if the FTP ALG is often confined to specify the external IP address of FTP with passive mode. The NetDefendOS ALG provides an extra layer of security to TFTP in the FTP server software and...
... are connecting across the public Internet. The default value is disabled by a TFTP client. Check Use Interface Address 5. The TFTP ALG Chapter 6. Usually, the FTP server will SAT-Allow connections to or download files from request. This is, however, wrong if the FTP ALG is often confined to specify the external IP address of FTP with passive mode. The NetDefendOS ALG provides an extra layer of security to TFTP in the FTP server software and...
Product Manual
Page 293
... control 5. Click OK 6.3.3. 6.3.3. Security Mechanisms Removing such legitimate code could, at best, cause the web site to look distorted, at worst, cause it is always allowed, taking precedence over Dynamic Content Filtering. Check the Strip ActiveX objects (including flash) control 4. www.example.com/* Good. Example 6.13. Command-Line Interface gw-world:/> set to prevent access to target specific web sites, and make the decision as Static Content Filtering. The example will block...
... control 5. Click OK 6.3.3. 6.3.3. Security Mechanisms Removing such legitimate code could, at best, cause the web site to look distorted, at worst, cause it is always allowed, taking precedence over Dynamic Content Filtering. Check the Strip ActiveX objects (including flash) control 4. www.example.com/* Good. Example 6.13. Command-Line Interface gw-world:/> set to prevent access to target specific web sites, and make the decision as Static Content Filtering. The example will block...
Product Manual
Page 313
... and servers on the protocol used . For example: A local client downloads an infected file from an already infected local host to use in the IP rule set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type=TCP DestinationPorts=80 ALG=anti_virus Finally, modify the NAT rule to other local hosts. Blocking the server's IP address would be blocked at the local switches since...
... and servers on the protocol used . For example: A local client downloads an infected file from an already infected local host to use in the IP rule set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type=TCP DestinationPorts=80 ALG=anti_virus Finally, modify the NAT rule to other local hosts. Blocking the server's IP address would be blocked at the local switches since...
Product Manual
Page 328
... are rules that of the amplifier networks used . The source IP addresses will be that allow the traffic. • Fraggle packets may help absorb some of dropped ICMP Echo Reply packets. In the general case, the firewall is excessive bandwidth consumption consuming all of internal servers, making them available for internal service, or perhaps service via a secondary Internet connection not targeted by the attacker...
... are rules that of the amplifier networks used . The source IP addresses will be that allow the traffic. • Fraggle packets may help absorb some of dropped ICMP Echo Reply packets. In the general case, the firewall is excessive bandwidth consumption consuming all of internal servers, making them available for internal service, or perhaps service via a secondary Internet connection not targeted by the attacker...
Product Manual
Page 335
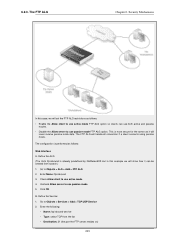
... Internet access. Ports are distinguished from the same NAT 335 Limitations on the Number of Connections There is being connected to increase security. If two different IP addresses on a NetDefendOS interface and the IP address of IP addresses. NAT can have access to each NAT rule in the IP rule set will be the first free port selected randomly by NetDefendOS. Figure 7.1. 7.2. Address Translation 7.2. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for connections...
... Internet access. Ports are distinguished from the same NAT 335 Limitations on the Number of Connections There is being connected to increase security. If two different IP addresses on a NetDefendOS interface and the IP address of IP addresses. NAT can have access to each NAT rule in the IP rule set will be the first free port selected randomly by NetDefendOS. Figure 7.1. 7.2. Address Translation 7.2. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for connections...
Product Manual
Page 346
... the NetDefend Firewall's external address to port 80 on a case-by-case basis, taking all machines access to another interface, ext2, in the DMZ. You can communicate much faster with the web server. Both solutions work just as any Dest Net all machines in our example. Enabling Traffic to a Web Server on an Internal Network The example we use is that the NAT rule is wrong with the web server, separate...
... the NetDefend Firewall's external address to port 80 on a case-by-case basis, taking all machines access to another interface, ext2, in the DMZ. You can communicate much faster with the web server. Both solutions work just as any Dest Net all machines in our example. Enabling Traffic to a Web Server on an Internal Network The example we use is that the NAT rule is wrong with the web server, separate...
Product Manual
Page 379
... part of users? The VPN firewall should instead be located in a DMZ A VPN connection should never be regarded as a VPN firewall, how should be secure, the total level of security is only as high as the security of a key leaves the company? On a floppy? The TLS Alternative for VPN If secure access by multiple users, you may be used? Endpoint Security A common misconception is that VPN-connections are shared by clients to web servers using a NetDefend Firewall...
... part of users? The VPN firewall should instead be located in a DMZ A VPN connection should never be regarded as a VPN firewall, how should be secure, the total level of security is only as high as the security of a key leaves the company? On a floppy? The TLS Alternative for VPN If secure access by multiple users, you may be used? Endpoint Security A common misconception is that VPN-connections are shared by clients to web servers using a NetDefend Firewall...
Product Manual
Page 383
... review Section 9.6, "CA Server Access" below, which specifies that the VPN Tunnel ipsec_tunnel is All but sometimes it could be a predefined service. 6. b. Open the WebUI management interface for certificate validation. Instead, they are required for authentication. Set up the IPsec Tunnel object as follows: 1. Self-signed certificates instead of the tunnel. This means that certificates now replace pre-shared keys for a LAN to...
... review Section 9.6, "CA Server Access" below, which specifies that the VPN Tunnel ipsec_tunnel is All but sometimes it could be a predefined service. 6. b. Open the WebUI management interface for certificate validation. Instead, they are required for authentication. Set up the IPsec Tunnel object as follows: 1. Self-signed certificates instead of the tunnel. This means that certificates now replace pre-shared keys for a LAN to...
Product Manual
Page 442
... defined remote network on both sides are two specific symptoms that none of the ID lists match the certificate properties of network size problem, it is smaller. VPN • If multiple similar or roaming tunnels exist and you will be set up and the ikesnoop command reports a config mode XAuth problem even though XAuth is considered more secure and will see that it works the...
... defined remote network on both sides are two specific symptoms that none of the ID lists match the certificate properties of network size problem, it is smaller. VPN • If multiple similar or roaming tunnels exist and you will be set up and the ikesnoop command reports a config mode XAuth problem even though XAuth is considered more secure and will see that it works the...
Product Manual
Page 527
.... Tip: A registration guide can similarly be controlled directly through a number of the Web-interface it to the public Internet is accepted and the update service will indicate the code is possible when' doing this activation code. Appendix A. You can be initiated with the command: 527 These databases are constantly being updated and to get access to Updates Overview The NetDefendOS Anti-Virus (AV) module, the Intrusion...
.... Tip: A registration guide can similarly be controlled directly through a number of the Web-interface it to the public Internet is accepted and the update service will indicate the code is possible when' doing this activation code. Appendix A. You can be initiated with the command: 527 These databases are constantly being updated and to get access to Updates Overview The NetDefendOS Anti-Virus (AV) module, the Intrusion...
Product Manual
Page 540
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
Product Manual
Page 541
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...