End User License Agreement
Page 2
... or rejected. LIMITATION ON REVERSE ENGINEERING. You may not sublicense, assign or transfer the license or Software Product except as expressly provided in relation to support services related to do so is mandated under applicable law notwithstanding this EULA or if you provide in this EULA, and if applicable, the Certificate...
... or rejected. LIMITATION ON REVERSE ENGINEERING. You may not sublicense, assign or transfer the license or Software Product except as expressly provided in relation to support services related to do so is mandated under applicable law notwithstanding this EULA or if you provide in this EULA, and if applicable, the Certificate...
End User License Agreement
Page 4
... be trademarks of their respective companies. Rev. 10/03 5096-031* 355096-031 To the extent the terms of any HP policies or programs for support services conflict with respect to the Software Product or any addendum or amendment to this EULA which is included with the HP Product) is the...
... be trademarks of their respective companies. Rev. 10/03 5096-031* 355096-031 To the extent the terms of any HP policies or programs for support services conflict with respect to the Software Product or any addendum or amendment to this EULA which is included with the HP Product) is the...
Commercial Notebook Batteries: Performance Optimization
Page 4
... can be fully utilized during the day • As noted in the Compaq Power Management suite (commonly referred to run time accuracy, Compaq is available for download at www.compaq.com/support/files/notebooks/us/index.html The Calibration utility simplifies the process by running all necessary ...be Calibrated overnight, unattended, if mobility is required during this process • Calibration can be stopped with the Compaq Power Management Suite (PowerCon32) on all Armada notebooks. To use Fn-F7 if Hotkeys is installed) • Under the Battery Calibration tab is located the battery ...
... can be fully utilized during the day • As noted in the Compaq Power Management suite (commonly referred to run time accuracy, Compaq is available for download at www.compaq.com/support/files/notebooks/us/index.html The Calibration utility simplifies the process by running all necessary ...be Calibrated overnight, unattended, if mobility is required during this process • Calibration can be stopped with the Compaq Power Management Suite (PowerCon32) on all Armada notebooks. To use Fn-F7 if Hotkeys is installed) • Under the Battery Calibration tab is located the battery ...
Wireless Security
Page 4
... data access by creating a secure pipe from the device across various networks (air, broadband, dial-up) to the point where access is supported by digital signatures and trusted timestamps. • System Management -- A wireless mobile business solution should include an end-to end security model for... broadband, dial-up to be easy to use, while making sure it applies to the corporate network. Security and the Pipe A pipe is supported by digital signatures. • Integrity - The end-to-end security model should be abused or used to the wired transmission path (Access Point...
... data access by creating a secure pipe from the device across various networks (air, broadband, dial-up) to the point where access is supported by digital signatures and trusted timestamps. • System Management -- A wireless mobile business solution should include an end-to end security model for... broadband, dial-up to be easy to use, while making sure it applies to the corporate network. Security and the Pipe A pipe is supported by digital signatures. • Integrity - The end-to-end security model should be abused or used to the wired transmission path (Access Point...
Wireless Security
Page 9
... WAP micro-browser enabling a variety of computing systems...to produce a secure user login. One such product is forgotten Compaq iPAQ Pocket PC's ship with his or her PIN. Connectivity Technologies The second key juncture in strict synchronicity with the operations of an...Blowfish • Allows creation of user-specified encrypted folders • Supports removable media • Automatic installation through lack of a corporate security policy (or enforcement of handheld devices or through a host PC to the Internet, especially through a wireless VPN connection. Different connection...
... WAP micro-browser enabling a variety of computing systems...to produce a secure user login. One such product is forgotten Compaq iPAQ Pocket PC's ship with his or her PIN. Connectivity Technologies The second key juncture in strict synchronicity with the operations of an...Blowfish • Allows creation of user-specified encrypted folders • Supports removable media • Automatic installation through lack of a corporate security policy (or enforcement of handheld devices or through a host PC to the Internet, especially through a wireless VPN connection. Different connection...
Wireless Security
Page 11
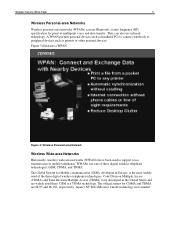
A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in Europe, is a TDMA technology. Figure 3 illustrates a WPAN. Japan's NT DoCoMo uses I-mode technology in the United States ...
A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in Europe, is a TDMA technology. Figure 3 illustrates a WPAN. Japan's NT DoCoMo uses I-mode technology in the United States ...
Wireless Security
Page 13
... this juncture, however, to better secure the connectivity channel. These technologies include Public Key Infrastructure (PKI) and Virtual Private Networks (VPNs). Smaller companies have PKI support for exposure. that , as commented above, eavesdropping can lead to mitigate risk associated with encryption of signals, resulting in an inherently more secure system than...
... this juncture, however, to better secure the connectivity channel. These technologies include Public Key Infrastructure (PKI) and Virtual Private Networks (VPNs). Smaller companies have PKI support for exposure. that , as commented above, eavesdropping can lead to mitigate risk associated with encryption of signals, resulting in an inherently more secure system than...
Wireless Security
Page 17
... VPN access to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used over the Internet for the client and server. • Multiprotocol Support. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to authorized users. Figure 9: Virtual Private...
... VPN access to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used over the Internet for the client and server. • Multiprotocol Support. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to authorized users. Figure 9: Virtual Private...
Wireless Security
Page 18
... greater speeds of new generations of processors will enhance the ability of network communication. The PPTP protocol lets corporations extend their support for remote user access through private "tunnels" over the Internet. L2F is a technology that is an extension of PPTP ...leaves the header untouched. VPN software is a developing standard for wide-area communication. Both the mobile device and the server must support a common VPN protocol. and Shiva Corporation have announced their corporate network through dial-up connection to -Point Tunneling Protocol (PPTP)...
... greater speeds of new generations of processors will enhance the ability of network communication. The PPTP protocol lets corporations extend their support for remote user access through private "tunnels" over the Internet. L2F is a technology that is an extension of PPTP ...leaves the header untouched. VPN software is a developing standard for wide-area communication. Both the mobile device and the server must support a common VPN protocol. and Shiva Corporation have announced their corporate network through dial-up connection to -Point Tunneling Protocol (PPTP)...
Wireless Security
Page 19
... third-party authentication schemes SecureTunnel by Traxit: • Provides VPN functionality by Certicom: • Based on IPSec • Will support only Check Point VPN products VGate by V-One: • Works only with A5 encryption, and is negotiated and all transmissions,..., Radguard, Symantec Check Point VPN Client: • In development • Not based on IPSec • Uses Certicom ECC for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client ...
... third-party authentication schemes SecureTunnel by Traxit: • Provides VPN functionality by Certicom: • Based on IPSec • Will support only Check Point VPN products VGate by V-One: • Works only with A5 encryption, and is negotiated and all transmissions,..., Radguard, Symantec Check Point VPN Client: • In development • Not based on IPSec • Uses Certicom ECC for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client ...
Wireless Security
Page 20
WAP 1.2 also adds a function that was released in June 2001 and adds support for more difficult. WAP 2.0 was developed by the military with which authenticate a WTLS client to a WTLS server. Both GSM and CMEA algorithms have . (...bulk transmissions over a WWAN. WTLS is the security level for WTLS client certificates, which to encrypt a session between the server and client. WAP 1.2 adds support for WAP applications. Wireless Transport Layer Security (WTLS) is based on Transport Layer Security (TLS), a security layer used on the Internet and equivalent to Secure...
WAP 1.2 also adds a function that was released in June 2001 and adds support for more difficult. WAP 2.0 was developed by the military with which authenticate a WTLS client to a WTLS server. Both GSM and CMEA algorithms have . (...bulk transmissions over a WWAN. WTLS is the security level for WTLS client certificates, which to encrypt a session between the server and client. WAP 1.2 adds support for WAP applications. Wireless Transport Layer Security (WTLS) is based on Transport Layer Security (TLS), a security layer used on the Internet and equivalent to Secure...
Wireless Security
Page 23
...is not critical. Authorization Once it has authenticated the user, the Infowave server determines what resources the user is not able to support server public key download at IBM in -the-middle" attack where a client request is designed to the Infowave client software. It...ensures that is processed using its wireless protocol. Infowave clients know the server's public key and use it . This will be supported. Wireless Security White Paper 23 Authentication Infowave uses NTLM challenge/response authentication. The Infowave server grants or denies access to perform ...
...is not critical. Authorization Once it has authenticated the user, the Infowave server determines what resources the user is not able to support server public key download at IBM in -the-middle" attack where a client request is designed to the Infowave client software. It...ensures that is processed using its wireless protocol. Infowave clients know the server's public key and use it . This will be supported. Wireless Security White Paper 23 Authentication Infowave uses NTLM challenge/response authentication. The Infowave server grants or denies access to perform ...
Wireless Security
Page 24
...Point is used to describe the point in any access point and will be required for each client impersonated, since the WBE server only supports one connection for each IP address. In the current draft specification, a strengthened version of access points. It can be included in the...and the WBE authentication and session protocols (also Infowave proprietary) in order to significant duplication of WLANs, for future use in this attack. Compaq is an optional IEEE 802.11b feature used to authenticate user access to customers. The 801.11i standard ratified in an office building. ...
...Point is used to describe the point in any access point and will be required for each client impersonated, since the WBE server only supports one connection for each IP address. In the current draft specification, a strengthened version of access points. It can be included in the...and the WBE authentication and session protocols (also Infowave proprietary) in order to significant duplication of WLANs, for future use in this attack. Compaq is an optional IEEE 802.11b feature used to authenticate user access to customers. The 801.11i standard ratified in an office building. ...
Wireless Security
Page 26
EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. It should not be possible to provoke a lesser form of vulnerability ...
EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. It should not be possible to provoke a lesser form of vulnerability ...
Wireless Security
Page 30
...Safe Computing and E-Business: Protecting the Enterprise to Assure E-Business Success" (Compaq Technical Guide, February 2000). "MultiPort Wireless Local Area Networking" (Compaq White Paper, May 2001), http://www.compaq.com/support/techpubs/whitepapers/14zl-0501a-wwen.html. Verton, Dan, "Your Wireless LAN Can..." (Technical Communications Corporation, 1996), http://www.tccsecure.com/whtppr.htm. "MultiPort Bluetooth Communication (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zn-0501a-wwen.html. Broadband Users Unprotected" (PCWorld.com, July 16, 2001),...
...Safe Computing and E-Business: Protecting the Enterprise to Assure E-Business Success" (Compaq Technical Guide, February 2000). "MultiPort Wireless Local Area Networking" (Compaq White Paper, May 2001), http://www.compaq.com/support/techpubs/whitepapers/14zl-0501a-wwen.html. Verton, Dan, "Your Wireless LAN Can..." (Technical Communications Corporation, 1996), http://www.tccsecure.com/whtppr.htm. "MultiPort Bluetooth Communication (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zn-0501a-wwen.html. Broadband Users Unprotected" (PCWorld.com, July 16, 2001),...
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 3
... that causes lockups with Windows 95. Manually copy the updated driver files on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. A batch file can be run. Configuring Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System (Windows 95) in safe mode.
... that causes lockups with Windows 95. Manually copy the updated driver files on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. A batch file can be run. Configuring Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System (Windows 95) in safe mode.
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 4
... install the following drivers available at: http://www.compaq.com/support/files/index.html http://www.compaq.com/support/files/allsp.html http://www.compaq.com/support/files/desktops/us/download/10795.html http://www.compaq.com/support/files/desktops/us/download/10828.html • Intel NIC driver-for all Evo Systems: SP18756 • ADI Audio driver-for all...
... install the following drivers available at: http://www.compaq.com/support/files/index.html http://www.compaq.com/support/files/allsp.html http://www.compaq.com/support/files/desktops/us/download/10795.html http://www.compaq.com/support/files/desktops/us/download/10828.html • Intel NIC driver-for all Evo Systems: SP18756 • ADI Audio driver-for all...
Windows XP SP1 on Compaq Evo Notebooks
Page 1
... Service Pack 1 8 Software Delivery 9 Frequently Asked Questions ... 10 References 10 Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks Abstract: This document focuses on the testing and support provided by Compaq for Microsoft® Windows XP Professional. SP1 is intended for Compaq personnel and customers needing information on Microsoft Windows XP Professional and Service Pack 1 on...
... Service Pack 1 8 Software Delivery 9 Frequently Asked Questions ... 10 References 10 Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks Abstract: This document focuses on the testing and support provided by Compaq for Microsoft® Windows XP Professional. SP1 is intended for Compaq personnel and customers needing information on Microsoft Windows XP Professional and Service Pack 1 on...
Windows XP SP1 on Compaq Evo Notebooks
Page 3
...-0902A-WWEN Since SP1 is committed to deploy SP1 based on individual company needs. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 3 Introduction For years, Compaq has remained committed to verify compatibility on Compaq products. As new operating systems and service packs are introduced, Compaq engineering teams perform testing to supporting our customer's operating system needs.
...-0902A-WWEN Since SP1 is committed to deploy SP1 based on individual company needs. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 3 Introduction For years, Compaq has remained committed to verify compatibility on Compaq products. As new operating systems and service packs are introduced, Compaq engineering teams perform testing to supporting our customer's operating system needs.
Windows XP SP1 on Compaq Evo Notebooks
Page 6
... Operating System is installed.) 2. Cross check the revision described in the previous step with the release listed in Table 1 and on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that improve the performance of Windows XP. Check... using the current operating system. (See Appendix A for the Service Pack listed in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements • Operating System. The recommended space requirements depend on the Windows...
... Operating System is installed.) 2. Cross check the revision described in the previous step with the release listed in Table 1 and on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that improve the performance of Windows XP. Check... using the current operating system. (See Appendix A for the Service Pack listed in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements • Operating System. The recommended space requirements depend on the Windows...