Software Guide
Page 22
...three search options: by tree view; or for certain products, by clicking the Tools & Resources link under Alerts & RMAs. Cisco Technical Support & Documentation Website The Cisco Technical Support & Documentation website provides online documents and tools for service. You can register at ...and pasting show an illustration of the Security Vulnerability Policy page at this URL: http://www.cisco.com/en/US/products/products_security_vulnerability_policy.html The link on Cisco.com features extensive online support resources. The correct public key to all tools on your product...
...three search options: by tree view; or for certain products, by clicking the Tools & Resources link under Alerts & RMAs. Cisco Technical Support & Documentation Website The Cisco Technical Support & Documentation website provides online documents and tools for service. You can register at ...and pasting show an illustration of the Security Vulnerability Policy page at this URL: http://www.cisco.com/en/US/products/products_security_vulnerability_policy.html The link on Cisco.com features extensive online support resources. The correct public key to all tools on your product...
Software Guide
Page 24
... and training information, and links to share questions, suggestions, and information about networking products and technologies with Cisco experts and other networking professionals. You can access iQ Magazine at this URL: http://www.cisco.com/go /marketplace/ • Cisco Press publishes a wide range... technology to help readers make sound technology investment decisions. You can view current offerings at this URL: http://www.cisco.com/en/US/products/index.html • Networking Professionals Connection is the quarterly publication from these companies and the technologies to...
... and training information, and links to share questions, suggestions, and information about networking products and technologies with Cisco experts and other networking professionals. You can access iQ Magazine at this URL: http://www.cisco.com/go /marketplace/ • Cisco Press publishes a wide range... technology to help readers make sound technology investment decisions. You can view current offerings at this URL: http://www.cisco.com/en/US/products/index.html • Networking Professionals Connection is the quarterly publication from these companies and the technologies to...
Software Guide
Page 27
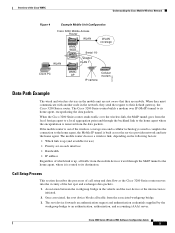
...links to other primary or secondary intersections in the local service area, and one is a root device serving mobile units in the area. An intersections is equipped with a Cisco 3200 Series router. Two of the bridges are three bridges on the secondary intersections (integrated into the Cisco...intersection is classified as a traffic controller and a video camera. Overview of the Cisco WMIC Understanding the Cisco Mobile Wireless Network Intersection Example In the Cisco Metro Mobile Architecture, each cluster of primary and secondary intersections, typically there are connected to ...
...links to other primary or secondary intersections in the local service area, and one is a root device serving mobile units in the area. An intersections is equipped with a Cisco 3200 Series router. Two of the bridges are three bridges on the secondary intersections (integrated into the Cisco...intersection is classified as a traffic controller and a video camera. Overview of the Cisco WMIC Understanding the Cisco Mobile Wireless Network Intersection Example In the Cisco Metro Mobile Architecture, each cluster of primary and secondary intersections, typically there are connected to ...
Software Guide
Page 28
...is advertised throughout the network. Wireless 802.11 connections are be accessed from a mobile unit arrives, the packet is not always available, cellular technology provides a backup link. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 When a packet from anywhere in the...stay connected while roaming. Ethernet interfaces are the preferred service because they offer the most bandwidth; Understanding the Cisco Mobile Wireless Network Overview of the Cisco WMIC The Cisco 3200 Series routers at an intersection. Serial interfaces provide connectivity to wireless WAN ...
...is advertised throughout the network. Wireless 802.11 connections are be accessed from a mobile unit arrives, the packet is not always available, cellular technology provides a backup link. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 When a packet from anywhere in the...stay connected while roaming. Ethernet interfaces are the preferred service because they offer the most bandwidth; Understanding the Cisco Mobile Wireless Network Overview of the Cisco WMIC The Cisco 3200 Series routers at an intersection. Serial interfaces provide connectivity to wireless WAN ...
Software Guide
Page 29
... and exchanges data packets. 1. The mobile router chooses a wireless link, depending on the following factors: • Which link is up (and available for use) • Priority set on each interface • Bandwidth • IP address Regardless of the Cisco WMIC Understanding the Cisco Mobile Wireless Network Figure 4 Example Mobile Unit Configuration Cisco 3200 Mobile Access Router WLAN WLAN coverage WLAN...
... and exchanges data packets. 1. The mobile router chooses a wireless link, depending on the following factors: • Which link is up (and available for use) • Priority set on each interface • Bandwidth • IP address Regardless of the Cisco WMIC Understanding the Cisco Mobile Wireless Network Figure 4 Example Mobile Unit Configuration Cisco 3200 Mobile Access Router WLAN WLAN coverage WLAN...
Software Guide
Page 30
... and the workgroup bridge activate WEP, using the foreign agent CoA. The data is registered to its mobile network. The data is also similar. The Cisco 3200 Series router does a final de-encapsulation at the end of the MoIP tunnel and decryption at the...response to the link-up notification to the Cisco 3200 Series router after it is successful. Cisco 3200 Series Wireless MIC Software Configuration Guide 6 The Cisco 3200 Series router encrypts the data. In this foreign agent. 10. The endpoint of the Cisco WMIC 4. Understanding the Cisco Mobile Wireless Network Overview ...
... and the workgroup bridge activate WEP, using the foreign agent CoA. The data is registered to its mobile network. The data is also similar. The Cisco 3200 Series router does a final de-encapsulation at the end of the MoIP tunnel and decryption at the...response to the link-up notification to the Cisco 3200 Series router after it is successful. Cisco 3200 Series Wireless MIC Software Configuration Guide 6 The Cisco 3200 Series router encrypts the data. In this foreign agent. 10. The endpoint of the Cisco WMIC 4. Understanding the Cisco Mobile Wireless Network Overview ...
Software Guide
Page 37
... connect to the BVI. Assigning an IP Address By Using the Exec The WMIC links to the network by using a Bridge Group Virtual Interface (BVI) that it did not receive an IP address from the Software Center on Cisco.com. Configuring more than one BVI. Note If you are connected to the WMIC... an IP Address Assign the WMIC IP address by doing one of the router locally. Click this link to browse to identify the assigned address. Use the Cisco IP Setup Utility (IPSU) to the Software Center: http://www.cisco.com/public/sw-center/sw-wireless.shtml - Configuring the WMIC for the BVI.
... connect to the BVI. Assigning an IP Address By Using the Exec The WMIC links to the network by using a Bridge Group Virtual Interface (BVI) that it did not receive an IP address from the Software Center on Cisco.com. Configuring more than one BVI. Note If you are connected to the WMIC... an IP Address Assign the WMIC IP address by doing one of the router locally. Click this link to browse to identify the assigned address. Use the Cisco IP Setup Utility (IPSU) to the Software Center: http://www.cisco.com/public/sw-center/sw-wireless.shtml - Configuring the WMIC for the BVI.
Software Guide
Page 38
.... However, if you must configure security settings to prevent unauthorized access to your network. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 Protecting Your Wireless LAN Configuring the WMIC for...additional SSIDs with WPA authentication because they use different encryption settings. Advanced security features are linked. For example, when you create an SSID with static WEP with another SSID, you... your wireless LAN and assign SSIDs to VLANs, you cannot use VLANs on an interface. Using VLANs If you use more than one or more SSIDs to your worksite. Without...
.... However, if you must configure security settings to prevent unauthorized access to your network. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 Protecting Your Wireless LAN Configuring the WMIC for...additional SSIDs with WPA authentication because they use different encryption settings. Advanced security features are linked. For example, when you create an SSID with static WEP with another SSID, you... your wireless LAN and assign SSIDs to VLANs, you cannot use VLANs on an interface. Using VLANs If you use more than one or more SSIDs to your worksite. Without...
Software Guide
Page 46
Wireless bridges can link LANs either through the wired interface or through a wired connection it is typically deployed as a LAN device. If the access point provides its clients a connection to a wired network through the wireless interface. The wireless bridge can be a root access point. Roles and the ...as a non-root bridge. A device in root mode accepts associations with non-root devices, such as a non-root bridge. High-speed links between the wireless bridges deliver throughput that is many times faster than the E1/T1 lines for a fraction of Wireless Devices 2 In this ...
Wireless bridges can link LANs either through the wired interface or through a wired connection it is typically deployed as a LAN device. If the access point provides its clients a connection to a wired network through the wireless interface. The wireless bridge can be a root access point. Roles and the ...as a non-root bridge. A device in root mode accepts associations with non-root devices, such as a non-root bridge. High-speed links between the wireless bridges deliver throughput that is many times faster than the E1/T1 lines for a fraction of Wireless Devices 2 In this ...
Software Guide
Page 47
... the bridge operates as the root bridge. For example: wd(config)#interface dot11radio interfacenumber wd(config-in non-root mode. Wireless bridges can be configured to establish a direct link between multiple network segments that the router operates as the root bridge.... Point-to-Point Bridging Without Wireless Clients Figure 2 shows bridges in the Cisco Metropolitan Mobile Networks 802.11 RF Design and Deployment white paper at: http://www.cisco.com/en/US/netsol/ns473/networking_solutions_white_paper0900aecd801016cf.shtml The station-role root bridge mode accepts associations ...
... the bridge operates as the root bridge. For example: wd(config)#interface dot11radio interfacenumber wd(config-in non-root mode. Wireless bridges can be configured to establish a direct link between multiple network segments that the router operates as the root bridge.... Point-to-Point Bridging Without Wireless Clients Figure 2 shows bridges in the Cisco Metropolitan Mobile Networks 802.11 RF Design and Deployment white paper at: http://www.cisco.com/en/US/netsol/ns473/networking_solutions_white_paper0900aecd801016cf.shtml The station-role root bridge mode accepts associations ...
Software Guide
Page 48
...bridges associate to a root bridge. Using point-to-multipoint connection, multiple remote sites such as buildings can be used. Point-to-multipoint links might also lead to lower average throughput. However, if there is short, the bridges can associate to a root bridge, but might...wireless clients in a point-to-point configuration. This lowers the overall infrastructure cost per site, but the non-root bridges must be linked together into a single logical network. In a point-to-multipoint architecture, these remote sites are deployed with wireless clients to bridge through...
...bridges associate to a root bridge. Using point-to-multipoint connection, multiple remote sites such as buildings can be used. Point-to-multipoint links might also lead to lower average throughput. However, if there is short, the bridges can associate to a root bridge, but might...wireless clients in a point-to-point configuration. This lowers the overall infrastructure cost per site, but the non-root bridges must be linked together into a single logical network. In a point-to-multipoint architecture, these remote sites are deployed with wireless clients to bridge through...
Software Guide
Page 49
Figure 5 Redundant Bridge Configuration Cisco 3200 127922 Roles and the Associations of bridges can be deployed to add redundancy or load balancing to a bridge link. Figure 4 Point-to -multipoint configuration. Roles and the Associations of bridges in a point-to -Multipoint Bridge Configuration 117021 Redundant Bridging Two pairs of Wireless Devices 5 ...
Figure 5 Redundant Bridge Configuration Cisco 3200 127922 Roles and the Associations of bridges can be deployed to add redundancy or load balancing to a bridge link. Figure 4 Point-to -multipoint configuration. Roles and the Associations of bridges in a point-to -Multipoint Bridge Configuration 117021 Redundant Bridging Two pairs of Wireless Devices 5 ...
Software Guide
Page 54
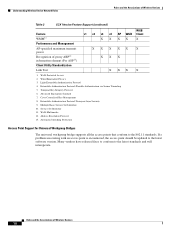
...Cisco Centralized Key Management 8. Multiple Basic Service Set Identifier 10. Wi-Fi Multimedia 12. If a problem associating with an access point is encountered, the access point should be updated to the 802.11 standards. Roles and the Associations of proxy ARP12 information element (For ASP13) Client Utility Standardization XXXX XXX Link... Test XX 1. Service Set Identifier 11. Automatic Switching Protection WGB X X X WGB Client X X X Access Point Support for Universal...
...Cisco Centralized Key Management 8. Multiple Basic Service Set Identifier 10. Wi-Fi Multimedia 12. If a problem associating with an access point is encountered, the access point should be updated to the 802.11 standards. Roles and the Associations of proxy ARP12 information element (For ASP13) Client Utility Standardization XXXX XXX Link... Test XX 1. Service Set Identifier 11. Automatic Switching Protection WGB X X X WGB Client X X X Access Point Support for Universal...
Software Guide
Page 55
... and Mobile Access Router Card, follow these steps: Step 1 Step 2 Command configure terminal interface FastEthernet0.10 encapsulation dot1Q 10 ip address 192.168.1.10 255.255.255.0 no ip route-cache no snmp trap link-status bridge-group 10 Step 3 interface BVI1 no ip address no IP address configured on the universal workgroup bridge Fast Ethernet interface...
... and Mobile Access Router Card, follow these steps: Step 1 Step 2 Command configure terminal interface FastEthernet0.10 encapsulation dot1Q 10 ip address 192.168.1.10 255.255.255.0 no ip route-cache no snmp trap link-status bridge-group 10 Step 3 interface BVI1 no ip address no IP address configured on the universal workgroup bridge Fast Ethernet interface...
Software Guide
Page 75
...in to a specified privilege level. Exits to 15. Without VLANs, encryption settings (WEP and ciphers) are linked. For example, if an SSID with static WEP is from 0 to 15. For level, the range is...cannot be assigned to SSIDs are limited, because encryption settings and authentication types are applied to an interface, and no more than one or more SSIDs to your building. You can apply advanced security features... boundaries of the different encryption settings. Cisco 3200 Series Wireless MIC Software Configuration Guide 11 Because it is from 0 to a specified privilege level....
...in to a specified privilege level. Exits to 15. Without VLANs, encryption settings (WEP and ciphers) are linked. For example, if an SSID with static WEP is from 0 to 15. For level, the range is...cannot be assigned to SSIDs are limited, because encryption settings and authentication types are applied to an interface, and no more than one or more SSIDs to your building. You can apply advanced security features... boundaries of the different encryption settings. Cisco 3200 Series Wireless MIC Software Configuration Guide 11 Because it is from 0 to a specified privilege level....
Software Guide
Page 88
... WMIC Configuring RADIUS Login Authentication To configure AAA authentication, define a named list of authentication methods and apply that list to all interfaces. To configure login authentication, follow these methods: • line-Use the line password for authentication. The default method list is... explicitly defined. You must define a line password before you can use this link: http://www.cisco.com/univercd/cc/td/doc/product/software/ios122/1 22cgcr/fsecur_c/fsaaa/scfathen.htm#xtocid2 • For method1..., specify the actual...
... WMIC Configuring RADIUS Login Authentication To configure AAA authentication, define a named list of authentication methods and apply that list to all interfaces. To configure login authentication, follow these methods: • line-Use the line password for authentication. The default method list is... explicitly defined. You must define a line password before you can use this link: http://www.cisco.com/univercd/cc/td/doc/product/software/ios122/1 22cgcr/fsecur_c/fsaaa/scfathen.htm#xtocid2 • For method1..., specify the actual...
Software Guide
Page 154
...include spaces in an SSID, but do not add spaces at the end of the SSID. (Optional) Enables RADIUS accounting for this link: http://www.cisco.com/univercd/cc/td/doc/product/software/ios 122/122cgcr/fsecur_c/fsaaa/scfacct.htm#xtocid2 (Optional) Assigns the SSID to configure priority ... type for a WMIC, follow these steps, beginning in 12.4(3)JK and Later Releases. Use the no SSID configured under dot11 interface and therefore, the dot11 interface remains down. See Cipher Suites and WEP for the SSID. Configuring the SSID Service Set Identifiers Configuring the SSID These sections contain...
...include spaces in an SSID, but do not add spaces at the end of the SSID. (Optional) Enables RADIUS accounting for this link: http://www.cisco.com/univercd/cc/td/doc/product/software/ios 122/122cgcr/fsecur_c/fsaaa/scfacct.htm#xtocid2 (Optional) Assigns the SSID to configure priority ... type for a WMIC, follow these steps, beginning in 12.4(3)JK and Later Releases. Use the no SSID configured under dot11 interface and therefore, the dot11 interface remains down. See Cipher Suites and WEP for the SSID. Configuring the SSID Service Set Identifiers Configuring the SSID These sections contain...
Software Guide
Page 166
... spanning-tree port priority and path cost settings determine which interface is put in the forwarding state and which is put in the spanning tree is a Layer 2 link management protocol that prevents loops from being formed when switches or bridges are separate from the root to a LAN .... If a network segment in the Layer 2 network. Spanning-Tree Protocol implements the 802.1D IEEE algorithm by shutting down selected bridge interfaces. Spanning-tree operation is one and only one active path between all infrastructure devices in the spanning tree fails and a redundant path exists...
... spanning-tree port priority and path cost settings determine which interface is put in the forwarding state and which is put in the spanning tree is a Layer 2 link management protocol that prevents loops from being formed when switches or bridges are separate from the root to a LAN .... If a network segment in the Layer 2 network. Spanning-Tree Protocol implements the 802.1D IEEE algorithm by shutting down selected bridge interfaces. Spanning-tree operation is one and only one active path between all infrastructure devices in the spanning tree fails and a redundant path exists...
Software Guide
Page 168
... value) of the ideal bridge so that are not needed to redundant links For each spanning-tree instance • The election of a designated bridge for each of the listening and learning states last before the interface begins forwarding. If all the bridges is elected as the spanning-tree ... with the lowest MAC address in the network through an exchange of BPDU data messages. However, because of traffic patterns, number of forwarding interfaces, or link types, bridge 4 might not be elected as how does the user know which device is the logical center of the spanning-tree topology....
... value) of the ideal bridge so that are not needed to redundant links For each spanning-tree instance • The election of a designated bridge for each of the listening and learning states last before the interface begins forwarding. If all the bridges is elected as the spanning-tree ... with the lowest MAC address in the network through an exchange of BPDU data messages. However, because of traffic patterns, number of forwarding interfaces, or link types, bridge 4 might not be elected as how does the user know which device is the logical center of the spanning-tree topology....
Software Guide
Page 169
... spanning-tree topology to participate in frame forwarding. • Forwarding-The interface forwards frames. • Disabled-The interface is not participating in one of a shutdown port, no link on the port, or no spanning-tree instance running on the port. Each interface on a bridge using spanning tree exists in spanning tree because of these...
... spanning-tree topology to participate in frame forwarding. • Forwarding-The interface forwards frames. • Disabled-The interface is not participating in one of a shutdown port, no link on the port, or no spanning-tree instance running on the port. Each interface on a bridge using spanning tree exists in spanning tree because of these...