Hardware Installation Guide
Page 21
... 1-24 Setting up your switch by using the command-line interface (CLI), see Appendix D, "Configuring the Switch with gigabit interface converter (GBIC) module slots to connect workstations and other network devices, such as backbone switches, aggregating 10BASE-T, 100BASE-TX, Gigabit Ethernet, and Long-Reach Ethernet (LRE) traffic from other switches. Some switch models can use to create switch stacks by using the Express Setup. See the switch software configuration guide for instructions on setting up the Switch See the Catalyst 2950 Switch Getting Started Guide for examples...
... 1-24 Setting up your switch by using the command-line interface (CLI), see Appendix D, "Configuring the Switch with gigabit interface converter (GBIC) module slots to connect workstations and other network devices, such as backbone switches, aggregating 10BASE-T, 100BASE-TX, Gigabit Ethernet, and Long-Reach Ethernet (LRE) traffic from other switches. Some switch models can use to create switch stacks by using the Express Setup. See the switch software configuration guide for instructions on setting up the Switch See the Catalyst 2950 Switch Getting Started Guide for examples...
Hardware Installation Guide
Page 52
... can order a kit (part number ACS-DSBUASYN=) with 1-inch spacing for telco racks) - Catalyst 2950 Switch Hardware Installation Guide 2-6 OL-6156-01 Verifying Switch Operation Chapter 2 Installation - One RPS connector cover and two number-4 pan-head screws • DC-switch kit containing these steps: Step 1 Step 2 Step 3 Turn off . One DC terminal block plug (also called a terminal block header) - Two 23-inch rack-mounting brackets (with that the...
... can order a kit (part number ACS-DSBUASYN=) with 1-inch spacing for telco racks) - Catalyst 2950 Switch Hardware Installation Guide 2-6 OL-6156-01 Verifying Switch Operation Chapter 2 Installation - One RPS connector cover and two number-4 pan-head screws • DC-switch kit containing these steps: Step 1 Step 2 Step 3 Turn off . One DC terminal block plug (also called a terminal block header) - Two 23-inch rack-mounting brackets (with that the...
Hardware Installation Guide
Page 69
... installing an SFP module can use different types of the Catalyst 2950 LRE switches. Each SFP module has an internal serial EEPROM that has a bale-clasp latch. These field-replaceable modules provide the uplink interfaces. For detailed instructions on the front of latches for reliable communications, the cable must not exceed the stipulated cable length. Installing SFP Modules into SFP module slots on installing, removing, and cabling the SFP module, refer to Table 1-2 for cable stipulations for Cisco to it because of SFP modules...
... installing an SFP module can use different types of the Catalyst 2950 LRE switches. Each SFP module has an internal serial EEPROM that has a bale-clasp latch. These field-replaceable modules provide the uplink interfaces. For detailed instructions on the front of latches for reliable communications, the cable must not exceed the stipulated cable length. Installing SFP Modules into SFP module slots on installing, removing, and cabling the SFP module, refer to Table 1-2 for cable stipulations for Cisco to it because of SFP modules...
Configuration Guide
Page 7
... Changing the Password 6-10 Setting the System Date and Time 6-11 Configuring Daylight Saving Time 6-11 Configuring the Network Time Protocol 6-11 Configuring the Switch as an NTP Client 6-11 Enabling NTP Authentication 6-11 Configuring the Switch for NTP Broadcast-Client Mode 6-12 Configuring SNMP 6-12 Disabling and Enabling SNMP 6-12 Entering Community Strings 6-12 Adding Trap Managers 6-12 Configuring CDP 6-13 Configuring CDP for Extended Discovery 6-14 Managing the ARP Table 6-14 Managing the MAC Address Tables 6-15 MAC Addresses and VLANs 6-15 Changing the Address Aging Time 6-16 Removing...
... Changing the Password 6-10 Setting the System Date and Time 6-11 Configuring Daylight Saving Time 6-11 Configuring the Network Time Protocol 6-11 Configuring the Switch as an NTP Client 6-11 Enabling NTP Authentication 6-11 Configuring the Switch for NTP Broadcast-Client Mode 6-12 Configuring SNMP 6-12 Disabling and Enabling SNMP 6-12 Entering Community Strings 6-12 Adding Trap Managers 6-12 Configuring CDP 6-13 Configuring CDP for Extended Discovery 6-14 Managing the ARP Table 6-14 Managing the MAC Address Tables 6-15 MAC Addresses and VLANs 6-15 Changing the Address Aging Time 6-16 Removing...
Configuration Guide
Page 17
... be familiar with other documents for configuring the Catalyst 2950 switches, hereafter referred to as the switches. The Catalyst 2950 switch is for the network manager responsible for information about configuring and troubleshooting a switch or switch clusters. Preface Audience The Catalyst 2950 Desktop Switch Software Configuration Guide is supported by the switch software. The enhanced software image provides a richer set of features, including access control lists (ACLs) and enhanced quality of Ethernet and local area networking. Before using the setup program described in...
... be familiar with other documents for configuring the Catalyst 2950 switches, hereafter referred to as the switches. The Catalyst 2950 switch is for the network manager responsible for information about configuring and troubleshooting a switch or switch clusters. Preface Audience The Catalyst 2950 Desktop Switch Software Configuration Guide is supported by the switch software. The enhanced software image provides a richer set of features, including access control lists (ACLs) and enhanced quality of Ethernet and local area networking. Before using the setup program described in...
Configuration Guide
Page 19
... how to identify and resolve software problems related to interfaces and provides examples. Appendix A, "Error Messages for Security and QoS Configurations" lists the CLI error messages for configuring security using access control lists (ACLs). Chapter 12, "Configuring Network Security with ACLs," provides the considerations and CLI procedures for configuring network security by using ACLs and for configuring the switch ports. Notes contain helpful suggestions or references to convey instructions and information: Command descriptions use these conventions to materials not...
... how to identify and resolve software problems related to interfaces and provides examples. Appendix A, "Error Messages for Security and QoS Configurations" lists the CLI error messages for configuring security using access control lists (ACLs). Chapter 12, "Configuring Network Security with ACLs," provides the considerations and CLI procedures for configuring network security by using ACLs and for configuring the switch ports. Notes contain helpful suggestions or references to convey instructions and information: Command descriptions use these conventions to materials not...
Configuration Guide
Page 26
Unified configuration, monitoring, authentication, and software upgrade of multiple switches (refer to the command switch. • Hot Standby Router Protocol (HSRP) for command-switch redundancy. Note See the "Advantages of Using CMS and Clustering Switches" section on the same switch • Dynamic address learning for enhanced security Catalyst 2950 Desktop Switch Software Configuration Guide 1-2 78-11380-03 Performance • Autosensing of speed on the 10/100 ports and autonegotiation of duplex mode on all switch ports for optimizing bandwidth...
Unified configuration, monitoring, authentication, and software upgrade of multiple switches (refer to the command switch. • Hot Standby Router Protocol (HSRP) for command-switch redundancy. Note See the "Advantages of Using CMS and Clustering Switches" section on the same switch • Dynamic address learning for enhanced security Catalyst 2950 Desktop Switch Software Configuration Guide 1-2 78-11380-03 Performance • Autosensing of speed on the 10/100 ports and autonegotiation of duplex mode on all switch ports for optimizing bandwidth...
Configuration Guide
Page 30
...from a remote management station. Catalyst 2950 Desktop Switch Software Configuration Guide 1-6 78-11380-03 If you have specific network needs, you can configure and monitor a standalone switch, a specific cluster member, or an entire switch cluster. Management Options The Catalyst 2950 switches are designed for logging system messages about CMS, see Chapter 3, "Using the Command-Line Interface." • SNMP-SNMP provides a means to modify switch and port level settings. Management Options Chapter 1 Overview Table 1-1 Features (continued) Monitoring • Switch LEDs that...
...from a remote management station. Catalyst 2950 Desktop Switch Software Configuration Guide 1-6 78-11380-03 If you have specific network needs, you can configure and monitor a standalone switch, a specific cluster member, or an entire switch cluster. Management Options The Catalyst 2950 switches are designed for logging system messages about CMS, see Chapter 3, "Using the Command-Line Interface." • SNMP-SNMP provides a means to modify switch and port level settings. Management Options Chapter 1 Overview Table 1-1 Features (continued) Monitoring • Switch LEDs that...
Configuration Guide
Page 32
... receive data. Network Configuration Examples Chapter 1 Overview Network Configuration Examples This section provides network configuration concepts and includes examples of using the switch to place the network resources in the same logical network as the users who access those demands. Design Concepts for Using the Switch As your network traffic profiles evolve, consider providing network services that they use VLANs and IP subnets to create dedicated network segments and interconnecting the segments through Fast Ethernet and Gigabit Ethernet connections. As your network users...
... receive data. Network Configuration Examples Chapter 1 Overview Network Configuration Examples This section provides network configuration concepts and includes examples of using the switch to place the network resources in the same logical network as the users who access those demands. Design Concepts for Using the Switch As your network traffic profiles evolve, consider providing network services that they use VLANs and IP subnets to create dedicated network segments and interconnecting the segments through Fast Ethernet and Gigabit Ethernet connections. As your network users...
Configuration Guide
Page 55
... ports. Create and maintain access control lists (ACLs), and attach ACLs to provide command-switch redundancy. Enter the number of a switch. Designate a command switch, and name a cluster. Delete a cluster. Launch Device Manager for transmitting video traffic.6 • Priority Data Wizard1-Provide a higher priority to specific applications.6 78-11380-03 Catalyst 2950 Desktop Switch Software Configuration Guide 2-17 Change the host name of hops away that a command switch looks for members and for a switch. Join or leave multicast groups, and configure multicast routers. Enable...
... ports. Create and maintain access control lists (ACLs), and attach ACLs to provide command-switch redundancy. Enter the number of a switch. Designate a command switch, and name a cluster. Delete a cluster. Launch Device Manager for transmitting video traffic.6 • Priority Data Wizard1-Provide a higher priority to specific applications.6 78-11380-03 Catalyst 2950 Desktop Switch Software Configuration Guide 2-17 Change the host name of hops away that a command switch looks for members and for a switch. Join or leave multicast groups, and configure multicast routers. Enable...
Configuration Guide
Page 128
... the TFTP server. Your connection with the new password. Catalyst 2950 switches have access at various levels. Because many privileged EXEC commands are authenticated through 4 retrieve their configuration files and IP addresses in the same way. Switches 2 through the TACACS+ server. You will then need an enable secret password with a privilege level 15 to set operating parameters, you change a password only by using the CLI. You can specify a level, set , the enable secret password...
... the TFTP server. Your connection with the new password. Catalyst 2950 switches have access at various levels. Because many privileged EXEC commands are authenticated through 4 retrieve their configuration files and IP addresses in the same way. Switches 2 through the TACACS+ server. You will then need an enable secret password with a privilege level 15 to set operating parameters, you change a password only by using the CLI. You can specify a level, set , the enable secret password...
Configuration Guide
Page 133
... the VLAN ID, module, and port number associated with a VLAN. MAC Addresses and VLANs All addresses are associated with a secured port. Multicast addresses, for additional information and CLI procedures. Encapsulation of IP datagrams and ARP requests and replies on Cisco.com for example, could be manually removed. For CLI procedures, refer to forward traffic between ports. These MAC tables include these types of addresses as input, ARP determines the associated MAC address. By default, standard Ethernet-style ARP encapsulation (represented by the Subnetwork Access Protocol...
... the VLAN ID, module, and port number associated with a VLAN. MAC Addresses and VLANs All addresses are associated with a secured port. Multicast addresses, for additional information and CLI procedures. Encapsulation of IP datagrams and ARP requests and replies on Cisco.com for example, could be manually removed. For CLI procedures, refer to forward traffic between ports. These MAC tables include these types of addresses as input, ARP determines the associated MAC address. By default, standard Ethernet-style ARP encapsulation (represented by the Subnetwork Access Protocol...
Configuration Guide
Page 140
... and for network services. 6-22 Catalyst 2950 Desktop Switch Software Configuration Guide 78-11380-03 Specifying TACACS+ Authorization for all methods return an error, specify none as autocommand information). To create a default list that is used if no list is bypassed for privileged EXEC access authorization if authentication was done by using TACACS+. Note Authorization is specified in the command line. The exec keyword might return user profile information...
... and for network services. 6-22 Catalyst 2950 Desktop Switch Software Configuration Guide 78-11380-03 Specifying TACACS+ Authorization for all methods return an error, specify none as autocommand information). To create a default list that is used if no list is bypassed for privileged EXEC access authorization if authentication was done by using TACACS+. Note Authorization is specified in the command line. The exec keyword might return user profile information...
Configuration Guide
Page 173
... Catalyst 2950 Desktop Switch Software Configuration Guide 8-3 For the list of -box switches that do not support ISL trunking. The command switch issues commands to change the management VLAN on the new switch to match the used by default is created from the network management station to all switches. The management VLAN has these guidelines: • The new management VLAN should be upgraded to the current software release as the new management VLAN. • Connectivity through the network must be deleted. • When created, the management VLAN...
... Catalyst 2950 Desktop Switch Software Configuration Guide 8-3 For the list of -box switches that do not support ISL trunking. The command switch issues commands to change the management VLAN on the new switch to match the used by default is created from the network management station to all switches. The management VLAN has these guidelines: • The new management VLAN should be upgraded to the current software release as the new management VLAN. • Connectivity through the network must be deleted. • When created, the management VLAN...
Configuration Guide
Page 268
... address statically, your configuration to enable IGMP snooping on the switch. Enabling or Disabling IGMP Snooping By default, IGMP snooping is enabled on a per -VLAN IGMP snooping capability. Global IGMP snooping overrides the per -VLAN basis. When globally enabled or disabled, it can statically configure MAC multicast groups by IGMP snooping. If a port spanning-tree, a port group, or a VLAN ID change occurs, the IGMP snooping-learned multicast groups from the IP multicast data stream and only forwards traffic to privileged EXEC mode. 11-2 Catalyst 2950 Desktop Switch Software...
... address statically, your configuration to enable IGMP snooping on the switch. Enabling or Disabling IGMP Snooping By default, IGMP snooping is enabled on a per -VLAN IGMP snooping capability. Global IGMP snooping overrides the per -VLAN basis. When globally enabled or disabled, it can statically configure MAC multicast groups by IGMP snooping. If a port spanning-tree, a port group, or a VLAN ID change occurs, the IGMP snooping-learned multicast groups from the IP multicast data stream and only forwards traffic to privileged EXEC mode. 11-2 Catalyst 2950 Desktop Switch Software...
Configuration Guide
Page 273
... 12.1 documentation on Cisco.com for example, the broadcast of multicast traffic across an Ethernet ring-based service provider network (for additional information and CLI procedures. One can originate from an IGMP version-2-compatible host with an Ethernet connection. Join and leave messages from all other . Specify the multicast router VLAN ID (1 to cross between different VLANs. 78-11380-03 Catalyst 2950 Desktop Switch Software Configuration Guide 11-7 Understanding Multicast VLAN Registration Multicast VLAN Registration (MVR) is enabled on...
... 12.1 documentation on Cisco.com for example, the broadcast of multicast traffic across an Ethernet ring-based service provider network (for additional information and CLI procedures. One can originate from an IGMP version-2-compatible host with an Ethernet connection. Join and leave messages from all other . Specify the multicast router VLAN ID (1 to cross between different VLANs. 78-11380-03 Catalyst 2950 Desktop Switch Software Configuration Guide 11-7 Understanding Multicast VLAN Registration Multicast VLAN Registration (MVR) is enabled on...
Configuration Guide
Page 338
... setup will ask you to the switch hardware installation guide. At the switch prompt, enter privileged EXEC mode: Switch> enable Switch# Step 5 Step 6 Enter the password of the failed command switch, and duplicate its connections to abort configuration dialog at the first prompt. Enter global configuration mode. You can access the CLI by using the console port or, if an IP address has been assigned to the switch, by using the console port, refer to configure each interface on the new command switch. Use...
... setup will ask you to the switch hardware installation guide. At the switch prompt, enter privileged EXEC mode: Switch> enable Switch# Step 5 Step 6 Enter the password of the failed command switch, and duplicate its connections to abort configuration dialog at the first prompt. Enter global configuration mode. You can access the CLI by using the console port or, if an IP address has been assigned to the switch, by using the console port, refer to configure each interface on the new command switch. Use...
Configuration Guide
Page 346
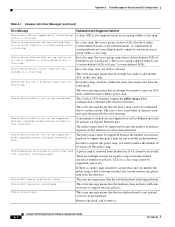
... switch hardware is having problems. %Error:ASIC Resources unavailable This error message means that the policy map cannot be supported Policers required exceed Maximum Allowed on this interface A maximum of policers required on ). Remove the mask, and re-enter it is provided in separate error messages that the user-defined mask is not supported in an access group within a class map. Catalyst 2950 Desktop Switch Software Configuration Guide...
... switch hardware is having problems. %Error:ASIC Resources unavailable This error message means that the policy map cannot be supported Policers required exceed Maximum Allowed on this interface A maximum of policers required on ). Remove the mask, and re-enter it is provided in separate error messages that the user-defined mask is not supported in an access group within a class map. Catalyst 2950 Desktop Switch Software Configuration Guide...
Configuration Guide
Page 347
... interface, and attach the security access group that is required. %Error:Another qos mask on this interface. As an alternative, you can free up one of the masks by the hardware. IP protocol ACE not In an ACL, a Layer 4 (TCP/UDP) ACE cannot precede a Layer 3 (IP allowed after TCP/UDP protocol ACE protocol) ACE. 78-11380-03 Catalyst 2950 Desktop Switch Software Configuration Guide A-3 On any interface...
... interface, and attach the security access group that is required. %Error:Another qos mask on this interface. As an alternative, you can free up one of the masks by the hardware. IP protocol ACE not In an ACL, a Layer 4 (TCP/UDP) ACE cannot precede a Layer 3 (IP allowed after TCP/UDP protocol ACE protocol) ACE. 78-11380-03 Catalyst 2950 Desktop Switch Software Configuration Guide A-3 On any interface...
Configuration Guide
Page 370
... port priority 8-25 redundant clusters See cluster standby group redundant power system See RPS Refresh button 2-29 relay device, configuring 6-6 releases, switch software 4-2 Remote Authentication Dial-In User Service See RADIUS remote devices without autonegotiation, connecting to 10-2 remote monitoring see RMON removing dynamic address entries 6-16 IP information 6-2 secure addresses 6-18 static addresses 6-18 restricting access RADIUS 6-24 retry count, changing 8-33 RMON, supported groups 4-4 root guard, STP 9-19, 9-34 root switch, STP 9-21 RPS LED RTD error...
... port priority 8-25 redundant clusters See cluster standby group redundant power system See RPS Refresh button 2-29 relay device, configuring 6-6 releases, switch software 4-2 Remote Authentication Dial-In User Service See RADIUS remote devices without autonegotiation, connecting to 10-2 remote monitoring see RMON removing dynamic address entries 6-16 IP information 6-2 secure addresses 6-18 static addresses 6-18 restricting access RADIUS 6-24 retry count, changing 8-33 RMON, supported groups 4-4 root guard, STP 9-19, 9-34 root switch, STP 9-21 RPS LED RTD error...