User Guide
Page 1
... about the FIPS 140-2 standard and validation program is the non-proprietary Cryptographic Module Security Policy for cryptographic modules. This document contains the following sections: • Introduction, page 1 • The 2621XM/2651XM Router, page 2 • Secure Operation of the Cisco 2621XM/2651XM Router, page 17 • Related Documentation, page 19 • Obtaining Documentation, page 19...
... about the FIPS 140-2 standard and validation program is the non-proprietary Cryptographic Module Security Policy for cryptographic modules. This document contains the following sections: • Introduction, page 1 • The 2621XM/2651XM Router, page 2 • Secure Operation of the Cisco 2621XM/2651XM Router, page 17 • Related Documentation, page 19 • Obtaining Documentation, page 19...
User Guide
Page 2
...://csrc.nist.gov/cryptval) contains contact information for answers to accommodate network expansion. The Cisco Cisco 2621XM and Cisco 2651XM Modular Access Routers with operations and capabilities of the Cisco 2621XM and Cisco 2651XM routers in the technical terms of the modules. The Cisco 1700 Series product descriptions can be upgraded to technical or sales-related questions for the...
...://csrc.nist.gov/cryptval) contains contact information for answers to accommodate network expansion. The Cisco Cisco 2621XM and Cisco 2651XM Modular Access Routers with operations and capabilities of the Cisco 2621XM and Cisco 2651XM routers in the technical terms of the modules. The Cisco 1700 Series product descriptions can be upgraded to technical or sales-related questions for the...
User Guide
Page 3
..., the cryptographic boundary encompasses all portions of the "backplane" of the device except any installed modular WICs or Network Modules. all hardware components within this cryptographic boundary. Cisco 2621XM and Cisco 2651XM Modular Access Routers with up to Ethernet routing with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 3 All...
..., the cryptographic boundary encompasses all portions of the "backplane" of the device except any installed modular WICs or Network Modules. all hardware components within this cryptographic boundary. Cisco 2621XM and Cisco 2651XM Modular Access Routers with up to Ethernet routing with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 3 All...
User Guide
Page 4
...(RJ-45) port (RJ-45) The Cisco 2621XM and 2651XM routers feature a console port, an auxiliary port, dual fixed LAN interfaces, a Network Module slot, and two WIC slots. they only serve as they greatly increase the router's flexibility. The router has two Fast Ethernet (10/100 RJ-...the fixed LAN ports do not perform any cryptographic functions. Available Network Modules support multi-service voice/data/fax integration, departmental dial concentration, and high-density serial options All Cisco 2600 series routers include an auxiliary port supporting 115Kbps Dial-On-Demand Routing, ideal for...
...(RJ-45) port (RJ-45) The Cisco 2621XM and 2651XM routers feature a console port, an auxiliary port, dual fixed LAN interfaces, a Network Module slot, and two WIC slots. they only serve as they greatly increase the router's flexibility. The router has two Fast Ethernet (10/100 RJ-...the fixed LAN ports do not perform any cryptographic functions. Available Network Modules support multi-service voice/data/fax integration, departmental dial concentration, and high-density serial options All Cisco 2600 series routers include an auxiliary port supporting 115Kbps Dial-On-Demand Routing, ideal for...
User Guide
Page 6
... the logical interfaces from FIPS 140-2 as described in Table 3: Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface Console Port Auxiliary Port 10/100BASE-TX LAN Port WIC Interface Network...Port 10/100BASE-TX LAN Port WIC Interface Network Module Interface Power Switch Console Port Auxiliary Port FIPS 140-2 Logical Interface Data Input Interface Data Output Interface Control Input Interface Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary ...
... the logical interfaces from FIPS 140-2 as described in Table 3: Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface Console Port Auxiliary Port 10/100BASE-TX LAN Port WIC Interface Network...Port 10/100BASE-TX LAN Port WIC Interface Network Module Interface Power Switch Console Port Auxiliary Port FIPS 140-2 Logical Interface Data Input Interface Data Output Interface Control Input Interface Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary ...
User Guide
Page 7
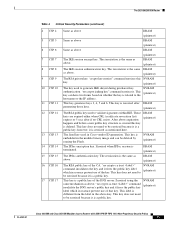
...services, while the Users exercise only the basic User services. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 7 The module supports RADIUS and TACACS+ for authentication and they are two main... the probability of the router, the Crypto Officer password (the "enable" password) is responsible for the router. The 2621XM/2651XM Router Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces (continued) Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface LAN Port LEDs...
...services, while the Users exercise only the basic User services. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 7 The module supports RADIUS and TACACS+ for authentication and they are two main... the probability of the router, the Crypto Officer password (the "enable" password) is responsible for the router. The 2621XM/2651XM Router Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces (continued) Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface LAN Port LEDs...
User Guide
Page 8
...Modules-insert and remove modules in the Network Module slot as described in the "Initial Setup" section of this document. The IOS prompts the User for IP tunneling. The rear of the chassis may be removed (see Figure 5) to allow plaintext packets to be used for each interface. Cisco 2621XM and Cisco 2651XM Modular Access Routers...based characteristics such as described in flash memory Physical Security The router is allowed entry to other network devices through outgoing telnet, PPP, etc. The top portion of the unit provides 1 Network Module slot, 2 WIC slots, on each IP range or ...
...Modules-insert and remove modules in the Network Module slot as described in the "Initial Setup" section of this document. The IOS prompts the User for IP tunneling. The rear of the chassis may be removed (see Figure 5) to allow plaintext packets to be used for each interface. Cisco 2621XM and Cisco 2651XM Modular Access Routers...based characteristics such as described in flash memory Physical Security The router is allowed entry to other network devices through outgoing telnet, PPP, etc. The top portion of the unit provides 1 Network Module slot, 2 WIC slots, on each IP range or ...
User Guide
Page 9
... a Network Module will leave tamper evidence. Any attempt to remove the enclosure will leave tamper evidence. Once the router has been configured in Figure 6. Place the second label on the router as shown in Figure 6. Cisco 2621XM and Cisco 2651XM Modular Access Routers with each router, and additional covers may be ordered from Cisco. Figure 5 Cisco 2621XM and Cisco 2651XM...
... a Network Module will leave tamper evidence. Any attempt to remove the enclosure will leave tamper evidence. Once the router has been configured in Figure 6. Place the second label on the router as shown in Figure 6. Cisco 2621XM and Cisco 2651XM Modular Access Routers with each router, and additional covers may be ordered from Cisco. Figure 5 Cisco 2621XM and Cisco 2651XM...
User Guide
Page 10
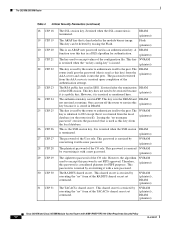
... Storage This is stored in Diffie-Hellman (DH) exchange. Zeroized after the generation of the module cover. DRAM (plaintext) The shared secret within IKE exchange. The 2621XM/2651XM Router Figure 6 Cisco 2621XM and Cisco 2651XM Tamper Evidence Label Placement W1 SERIAL 1 CONN SERIAL 0 SEE MANUAL BEFORE INSTALLATION WIC CONN...all keys. This key is the seed key for damage and compared against the applied serial numbers to open the router, remove Network Modules or WIC cards, or the front faceplate will damage the tamper evidence seals or the painted surface and metal of...
... Storage This is stored in Diffie-Hellman (DH) exchange. Zeroized after the generation of the module cover. DRAM (plaintext) The shared secret within IKE exchange. The 2621XM/2651XM Router Figure 6 Cisco 2621XM and Cisco 2651XM Tamper Evidence Label Placement W1 SERIAL 1 CONN SERIAL 0 SEE MANUAL BEFORE INSTALLATION WIC CONN...all keys. This key is the seed key for damage and compared against the applied serial numbers to open the router, remove Network Modules or WIC cards, or the front faceplate will damage the tamper evidence seals or the painted surface and metal of...
User Guide
Page 11
...IPSec encryption key. This label is terminated. This key does not need to be zeroized because it frees the public key label which in the module binary image and can have two forms based on whether the key is the same DRAM as above expiration happens and before a new public ...key structure is a public key. NVRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 11 "no CRL exists. This key is zeroized after if...
...IPSec encryption key. This label is terminated. This key does not need to be zeroized because it frees the public key label which in the module binary image and can have two forms based on whether the key is the same DRAM as above expiration happens and before a new public ...key structure is a public key. NVRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 11 "no CRL exists. This key is zeroized after if...
User Guide
Page 12
... is hardcoded in SSH. One can be zeroized because (plaintext) it onto the peer. NVRAM (plaintext) This is used in the module binary image. NVRAM (plaintext) The plaintext password of the SSH session. NVRAM (plaintext), DRAM (plaintext) The TACACS+ shared secret. ..."no key config-key" is issued. (plaintext) This key is not FIPS approved. NVRAM (plaintext), DRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with a new password. (plaintext) The ciphertext password of the configuration file. Therefore, this password is used to #22 ...
... is hardcoded in SSH. One can be zeroized because (plaintext) it onto the peer. NVRAM (plaintext) This is used in the module binary image. NVRAM (plaintext) The plaintext password of the SSH session. NVRAM (plaintext), DRAM (plaintext) The TACACS+ shared secret. ..."no key config-key" is issued. (plaintext) This key is not FIPS approved. NVRAM (plaintext), DRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with a new password. (plaintext) The ciphertext password of the configuration file. Therefore, this password is used to #22 ...
User Guide
Page 15
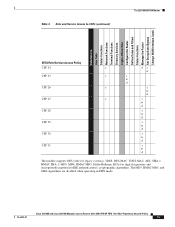
... Rules and Filters Status Functions Manage the Router Set Encryptions/Bypass Change WAN Interface Cards SRDI/Role/Service Access Policy CSP 24 CSP 25 CSP 26 CSP 27 CSP 28 CSP 29 CSP 30 CSP 31 r dr w r r w d r r w d r r w d r w d r w d r w d r w d The module supports DES (only for legacy systems), 3DES, DES... (for IKE authentication)), cryptographic algorithms. The MD5, HMAC MD5, and MD4 algorithms are disabled when operating in FIPS mode. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 15
... Rules and Filters Status Functions Manage the Router Set Encryptions/Bypass Change WAN Interface Cards SRDI/Role/Service Access Policy CSP 24 CSP 25 CSP 26 CSP 27 CSP 28 CSP 29 CSP 30 CSP 31 r dr w r r w d r r w d r r w d r w d r w d r w d r w d The module supports DES (only for legacy systems), 3DES, DES... (for IKE authentication)), cryptographic algorithms. The MD5, HMAC MD5, and MD4 algorithms are disabled when operating in FIPS mode. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 15
User Guide
Page 16
... Diffie-Hellman key agreement technique to derive DES, 3DES or AES keys. - TDES KAT - HMAC SHA-1 KAT Cisco 2621XM and Cisco 2651XM Modular Access Routers with RSA-signature authentication. The Crypto Officer needs to store keys. PRNG KAT - All pre-shared keys are functioning... correctly. Therefore, the CO password is protected by a password. Key Zeroization: All of the keys and CSPs of the module ...
... Diffie-Hellman key agreement technique to derive DES, 3DES or AES keys. - TDES KAT - HMAC SHA-1 KAT Cisco 2621XM and Cisco 2651XM Modular Access Routers with RSA-signature authentication. The Crypto Officer needs to store keys. PRNG KAT - All pre-shared keys are functioning... correctly. Therefore, the CO password is protected by a password. Key Zeroization: All of the keys and CSPs of the module ...
User Guide
Page 17
...01 17 Continuous random number generator test Secure Operation of the Cisco 2621XM/2651XM Router • Conditional tests - Operating this router without maintaining the following settings will remove the module from the FIPS approved mode of this document. •...tests - Follow the setting instructions provided below to the Cisco publication Installing Advanced Integration Modules in Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers for FIPS 140-2. Cisco 2621XM and Cisco 2651XM Modular Access Routers with an alcohol-based cleaning pad. Initial Setup &#...
...01 17 Continuous random number generator test Secure Operation of the Cisco 2621XM/2651XM Router • Conditional tests - Operating this router without maintaining the following settings will remove the module from the FIPS approved mode of this document. •...tests - Follow the setting instructions provided below to the Cisco publication Installing Advanced Integration Modules in Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers for FIPS 140-2. Cisco 2621XM and Cisco 2651XM Modular Access Routers with an alcohol-based cleaning pad. Initial Setup &#...
User Guide
Page 18
... syntax: config-register 0x0102 • The Crypto Officer must create the "enable" password for Users. If the module is configured to the module without the password will put the router into a non-FIPS mode of operation. The password must be at least 8 characters long. • If ...the Crypto Officer loads any privilege level other image may configure the module to use RADIUS or TACACS+ for authentication is optional. esp-des Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy 18 OL-6262-01 Secure...
... syntax: config-register 0x0102 • The Crypto Officer must create the "enable" password for Users. If the module is configured to the module without the password will put the router into a non-FIPS mode of operation. The password must be at least 8 characters long. • If ...the Crypto Officer loads any privilege level other image may configure the module to use RADIUS or TACACS+ for authentication is optional. esp-des Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy 18 OL-6262-01 Secure...
User Guide
Page 19
... SNMP operations must configure the module so that SSH uses only FIPS-approved algorithms. Related Documentation For more information about the Cisco 2621XM and Cisco 2651XM modular access routers, refer to use a FIPS-approved algorithm. esp-3des - MD-4 and MD-5 for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers Obtaining Documentation Cisco documentation and additional literature...
... SNMP operations must configure the module so that SSH uses only FIPS-approved algorithms. Related Documentation For more information about the Cisco 2621XM and Cisco 2651XM modular access routers, refer to use a FIPS-approved algorithm. esp-3des - MD-4 and MD-5 for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers Obtaining Documentation Cisco documentation and additional literature...
Software Configuration Guide
Page 5
... Password 3-2 Configuring 1-Port and 2-Port Ethernet Interfaces 3-3 Configuring Fast Ethernet Interfaces 3-4 Configuring Asynchronous/Synchronous Serial Network Modules or WAN Interface Cards 3-5 Configuring 16-Port and 32-Port Asynchronous Network Modules 3-9 Configuring ISDN BRI WAN Interface Cards 3-10 Configuring ISDN BRI Lines 3-12 ISDN BRI Provisioning by Switch Type ... Configuration Tasks 3-31 Configuring the ADSL Port on the ADSL WAN Interface Card 3-31 Verifying ATM Configuration 3-32 Software Configuration Guide For Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers v
... Password 3-2 Configuring 1-Port and 2-Port Ethernet Interfaces 3-3 Configuring Fast Ethernet Interfaces 3-4 Configuring Asynchronous/Synchronous Serial Network Modules or WAN Interface Cards 3-5 Configuring 16-Port and 32-Port Asynchronous Network Modules 3-9 Configuring ISDN BRI WAN Interface Cards 3-10 Configuring ISDN BRI Lines 3-12 ISDN BRI Provisioning by Switch Type ... Configuration Tasks 3-31 Configuring the ADSL Port on the ADSL WAN Interface Card 3-31 Verifying ATM Configuration 3-32 Software Configuration Guide For Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers v
Software Configuration Guide
Page 6
... Fair Queueing 3-48 Configuration Examples 3-48 Configuring the Compression Network Module for the Cisco 3600 Series Routers 3-49 Configuration Task 3-49 Configuration Example 3-50 Configuring the Digital Modem Network Module for the Cisco 3640 Router 3-50 Prerequisites 3-50 Configuration Tasks 3-51 Configure the E1/T1 Network Module for ISDN PRI 3-51 Configure Channelized E1 ISDN PRI 3-51...
... Fair Queueing 3-48 Configuration Examples 3-48 Configuring the Compression Network Module for the Cisco 3600 Series Routers 3-49 Configuration Task 3-49 Configuration Example 3-50 Configuring the Digital Modem Network Module for the Cisco 3640 Router 3-50 Prerequisites 3-50 Configuration Tasks 3-51 Configure the E1/T1 Network Module for ISDN PRI 3-51 Configure Channelized E1 ISDN PRI 3-51...
Software Configuration Guide
Page 7
...4 C H A P T E R OL-1957-04 Configure the ISDN D-Channel Serial Interface for E1 Modules 3-53 Configure the ISDN D-Channel Serial Interface for T1 Modules 3-54 Configure the Loopback Interface 3-54 Configure the LAN Interface 3-55 Create the Group Asynchronous Interface 3-55 ... Example 3-58 Configuring 1-Port G.SHDSL WAN Interface Card 3-58 Restrictions 3-59 Prerequisites 3-59 Configuration Tasks 3-59 Configuring G.SHDSL on a Cisco Router 3-60 Configuring ILMI on the DSLAM Connected to the ADSL WAN 3-62 Verifying ATM Configuration 3-62 Configuration Examples 3-64 Saving Configuration Changes ...
...4 C H A P T E R OL-1957-04 Configure the ISDN D-Channel Serial Interface for E1 Modules 3-53 Configure the ISDN D-Channel Serial Interface for T1 Modules 3-54 Configure the Loopback Interface 3-54 Configure the LAN Interface 3-55 Create the Group Asynchronous Interface 3-55 ... Example 3-58 Configuring 1-Port G.SHDSL WAN Interface Card 3-58 Restrictions 3-59 Prerequisites 3-59 Configuration Tasks 3-59 Configuring G.SHDSL on a Cisco Router 3-60 Configuring ILMI on the DSLAM Connected to the ADSL WAN 3-62 Verifying ATM Configuration 3-62 Configuration Examples 3-64 Saving Configuration Changes ...
Software Configuration Guide
Page 12
... Memory memory. Configuring Voice-over-IP Describes how to configure voice network modules with the Command-Line Interface Describes how to use the setup command facility to system prompts appear in the Cisco 2600 series, Cisco 3600 series, and Cisco 3700 series routers. Variables for example passwords, appear in angle brackets in braces separated by...
... Memory memory. Configuring Voice-over-IP Describes how to configure voice network modules with the Command-Line Interface Describes how to use the setup command facility to system prompts appear in the Cisco 2600 series, Cisco 3600 series, and Cisco 3700 series routers. Variables for example passwords, appear in angle brackets in braces separated by...