User Guide
Page 9
... to Know Your NBG-460N 23 The WPS Button ...29 Introducing the Web Configurator 31 Connection Wizard ...45 Tutorials ...63 AP Mode ...81 Network ...89 Wireless LAN ...91 WAN ...123 LAN ...139 DHCP ...147 Network Address Translation (NAT 153 Dynamic DNS ...163 Security ...167 Firewall ...169 Content Filtering ...179 IPSec VPN ...185 Management...
... to Know Your NBG-460N 23 The WPS Button ...29 Introducing the Web Configurator 31 Connection Wizard ...45 Tutorials ...63 AP Mode ...81 Network ...89 Wireless LAN ...91 WAN ...123 LAN ...139 DHCP ...147 Network Address Translation (NAT 153 Dynamic DNS ...163 Security ...167 Firewall ...169 Content Filtering ...179 IPSec VPN ...185 Management...
User Guide
Page 12
... 5.2.1 Configure Wireless Security Using WPS on both your NBG-460N and Wireless Client 63 5.2.2 Enable and Configure Wireless Security without WPS on your NBG-460N 67 5.2.3 Configure Your Notebook 68 5.3 Site-To-Site VPN Tunnel Tutorial 70 5.3.1 Configuring Bob's NBG-460N VPN Settings 71 5.3.2 Configuring Jack's NBG-460N VPN Settings 73 5.3.3 Checking the VPN Connection 75 5.4 Bandwidth Management for your Network 76...
... 5.2.1 Configure Wireless Security Using WPS on both your NBG-460N and Wireless Client 63 5.2.2 Enable and Configure Wireless Security without WPS on your NBG-460N 67 5.2.3 Configure Your Notebook 68 5.3 Site-To-Site VPN Tunnel Tutorial 70 5.3.1 Configuring Bob's NBG-460N VPN Settings 71 5.3.2 Configuring Jack's NBG-460N VPN Settings 73 5.3.3 Checking the VPN Connection 75 5.4 Bandwidth Management for your Network 76...
User Guide
Page 16
... ...183 14.6.1 Customizing Keyword Blocking URL Checking 184 Chapter 15 IPSec VPN...185 15.1 Overview ...185 15.2 What You Can Do ...185 ...15.4 The General Screen ...188 15.4.1 VPN Rule Setup (Basic 189 15.4.2 VPN Rule Setup (Advanced 194 15.4.3 VPN Rule Setup (Manual 201 15.5 The...VPN and Remote Management 206 15.6.2 IKE SA Proposal ...207 15.6.3 Diffie-Hellman (DH) Key Exchange 208 15.6.4 Authentication ...208 15.6.5 Negotiation Mode 209 15.6.6 VPN... SA Proposal and Perfect Forward Secrecy 212 15.6.10 Additional IPSec VPN Topics 212 Part IV: Management 215 Chapter 16 Static Route ...217...
... ...183 14.6.1 Customizing Keyword Blocking URL Checking 184 Chapter 15 IPSec VPN...185 15.1 Overview ...185 15.2 What You Can Do ...185 ...15.4 The General Screen ...188 15.4.1 VPN Rule Setup (Basic 189 15.4.2 VPN Rule Setup (Advanced 194 15.4.3 VPN Rule Setup (Manual 201 15.5 The...VPN and Remote Management 206 15.6.2 IKE SA Proposal ...207 15.6.3 Diffie-Hellman (DH) Key Exchange 208 15.6.4 Authentication ...208 15.6.5 Negotiation Mode 209 15.6.6 VPN... SA Proposal and Perfect Forward Secrecy 212 15.6.10 Additional IPSec VPN Topics 212 Part IV: Management 215 Chapter 16 Static Route ...217...
User Guide
Page 23
... to efficiently manage traffic on your Internet Protocol Television (IPTV) service (refer to Know Your NBG-460N 1.1 Overview This chapter introduces the main features and applications of the NBG-460N. Additionally, you to a broadband modem/router, such as a firewall, IPSec VPN and content filtering are also available for secure Internet computing. A range of the NBG460N...
... to efficiently manage traffic on your Internet Protocol Television (IPTV) service (refer to Know Your NBG-460N 1.1 Overview This chapter introduces the main features and applications of the NBG-460N. Additionally, you to a broadband modem/router, such as a firewall, IPSec VPN and content filtering are also available for secure Internet computing. A range of the NBG460N...
User Guide
Page 26
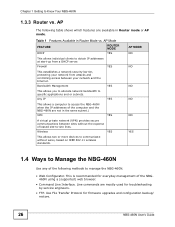
...Wireless YES This allows two or more devices to communicate without the expense of the computer and the NBG-460N are not in the same subnet.) VPN YES A virtual private network (VPN) provides secure communications between your network and the Internet. Any IP YES This allows a computer to... access the NBG-460N when the IP addresses of leased site-to Manage the NBG-460N Use any of the NBG460N using a (...
...Wireless YES This allows two or more devices to communicate without the expense of the computer and the NBG-460N are not in the same subnet.) VPN YES A virtual private network (VPN) provides secure communications between your network and the Internet. Any IP YES This allows a computer to... access the NBG-460N when the IP addresses of leased site-to Manage the NBG-460N Use any of the NBG460N using a (...
User Guide
Page 36
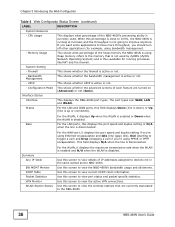
...VPN connections. System Setting - Status For the LAN and WAN ports, this screen to improve anymore. For the WAN port, it displays the port speed and duplex setting if you're using PPPoE or PPTP encapsulation. CPU Usage This displays what percentage of the NBG-460N's processing ability is currently used by ZyNOS (ZyXEL... example, using . Memory Usage This shows what percentage of the heap memory the NBG-460N is disabled. Summary Any IP Table BW MGMT Monitor DHCP Table Packet Statistics VPN Monitor WLAN Station Status For the WLAN, it displays Up when the WLAN is ...
...VPN connections. System Setting - Status For the LAN and WAN ports, this screen to improve anymore. For the WAN port, it displays the port speed and duplex setting if you're using PPPoE or PPTP encapsulation. CPU Usage This displays what percentage of the NBG-460N's processing ability is currently used by ZyNOS (ZyXEL... example, using . Memory Usage This shows what percentage of the heap memory the NBG-460N is disabled. Summary Any IP Table BW MGMT Monitor DHCP Table Packet Statistics VPN Monitor WLAN Station Status For the WLAN, it displays Up when the WLAN is ...
User Guide
Page 38
Security Firewall General Use this screen to change your NBG-460N's time and date. 38 NBG-460N User's Guide Services This screen shows a summary of the firewall rules, and allows you to manage the NBG-460N. Advanced Use this screen to activate/deactivate the firewall. VPN General Use this screen to change administrative settings such as system and...
Security Firewall General Use this screen to change your NBG-460N's time and date. 38 NBG-460N User's Guide Services This screen shows a summary of the firewall rules, and allows you to manage the NBG-460N. Advanced Use this screen to activate/deactivate the firewall. VPN General Use this screen to change administrative settings such as system and...
User Guide
Page 42
... of time the line has been up. Table 8 Summary: VPN Monitor LABEL DESCRIPTION # This is the number of security settings related to update the screen's statistics immediately. 42 NBG-460N User's Guide Rx B/s This displays the reception speed in bytes...the group of collisions on this port. Refresh Both AH and ESP increase NBG-460N processing requirements and communications latency (delay). Stop Click Stop to stop refreshing statistics. 3.5.6 Summary: VPN Monitor Click the VPN Monitor (Details...) hyperlink in the Poll Interval(s) field. Encapsulation This field...
... of time the line has been up. Table 8 Summary: VPN Monitor LABEL DESCRIPTION # This is the number of security settings related to update the screen's statistics immediately. 42 NBG-460N User's Guide Rx B/s This displays the reception speed in bytes...the group of collisions on this port. Refresh Both AH and ESP increase NBG-460N processing requirements and communications latency (delay). Stop Click Stop to stop refreshing statistics. 3.5.6 Summary: VPN Monitor Click the VPN Monitor (Details...) hyperlink in the Poll Interval(s) field. Encapsulation This field...
User Guide
Page 53
...information on PPTP. Back Click Back to return to continue. User Name Type the user name given to you by your service provider. NBG-460N User's Guide 53 Next Click Next to the previous screen. Service Name Type the name of your ISP. Password Type the password ...individual computers), the computers on the LAN do not need PPPoE software installed, since the NBG-460N does that enables transfers of data from a remote client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks. Refer to the appendix for Internet Access Connection Type ...
...information on PPTP. Back Click Back to return to continue. User Name Type the user name given to you by your service provider. NBG-460N User's Guide 53 Next Click Next to the previous screen. Service Name Type the name of your ISP. Password Type the password ...individual computers), the computers on the LAN do not need PPPoE software installed, since the NBG-460N does that enables transfers of data from a remote client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks. Refer to the appendix for Internet Access Connection Type ...
User Guide
Page 63
...5 Tutorials 5.1 Overview This chapter provides tutorials for your NBG-460N as the wireless client which connects to a notebook. This example uses the NBG-460N as the AP and NWD210N as follows: • How to Connect to the Internet from an AP • Site-To-Site VPN Tunnel Tutorial • Bandwidth Management for wireless communication....section gives you an example of how to set up an access point (AP) and wireless client (a notebook (B), in this example) for your NBG-460N and Wireless Client This section gives you how to do both. B can access the Internet through the AP wirelessly...
...5 Tutorials 5.1 Overview This chapter provides tutorials for your NBG-460N as the wireless client which connects to a notebook. This example uses the NBG-460N as the AP and NWD210N as follows: • How to Connect to the Internet from an AP • Site-To-Site VPN Tunnel Tutorial • Bandwidth Management for wireless communication....section gives you an example of how to set up an access point (AP) and wireless client (a notebook (B), in this example) for your NBG-460N and Wireless Client This section gives you how to do both. B can access the Internet through the AP wirelessly...
User Guide
Page 70
... section of this User's Guide. Table 23 Site-To-Site VPN Tunnel Settings SETTING BOB'S NBG-460N Active YES IPSec Keying IKE Mode JACK'S NBG-460N YES IKE 70 NBG-460N User's Guide Figure 40 Site-To-Site VPN Tunnel 192.168.1.35 BOB JACK 10.0.0.7 1.1.1.1 2.2.2.2 The following...table describes the VPN settings that must be configured on Bob and Jack's NBG-460N routers. Chapter 5 Tutorials 7 Check the status of your wireless connection in the address bar. If your wireless connection is successful, open your Internet browser and enter http:// www.zyxel.com or the...
... section of this User's Guide. Table 23 Site-To-Site VPN Tunnel Settings SETTING BOB'S NBG-460N Active YES IPSec Keying IKE Mode JACK'S NBG-460N YES IKE 70 NBG-460N User's Guide Figure 40 Site-To-Site VPN Tunnel 192.168.1.35 BOB JACK 10.0.0.7 1.1.1.1 2.2.2.2 The following...table describes the VPN settings that must be configured on Bob and Jack's NBG-460N routers. Chapter 5 Tutorials 7 Check the status of your wireless connection in the address bar. If your wireless connection is successful, open your Internet browser and enter http:// www.zyxel.com or the...
User Guide
Page 71
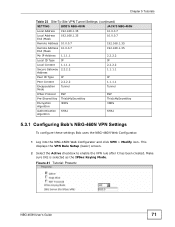
...'s Guide 71 Chapter 5 Tutorials Table 23 Site-To-Site VPN Tunnel Settings (continued) SETTING BOB'S NBG-460N JACK'S NBG-460N Local Address 192.168.1.35 10.0.0.7 Local Address End /Mask 192.168.1.35 10.0.0.7 Remote Address 10.0.0.7 192... Encryption Algorithm 3DES 3DES Authentication Algorithm SHA1 SHA1 5.3.1 Configuring Bob's NBG-460N VPN Settings To configure these settings Bob uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. This displays the VPN Rule Setup (basic) screen. 2 Select the Active checkbox to ...
...'s Guide 71 Chapter 5 Tutorials Table 23 Site-To-Site VPN Tunnel Settings (continued) SETTING BOB'S NBG-460N JACK'S NBG-460N Local Address 192.168.1.35 10.0.0.7 Local Address End /Mask 192.168.1.35 10.0.0.7 Remote Address 10.0.0.7 192... Encryption Algorithm 3DES 3DES Authentication Algorithm SHA1 SHA1 5.3.1 Configuring Bob's NBG-460N VPN Settings To configure these settings Bob uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. This displays the VPN Rule Setup (basic) screen. 2 Select the Active checkbox to ...
User Guide
Page 72
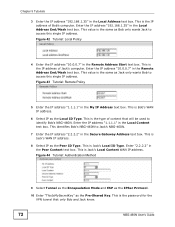
... IP as the Local ID Type. Enter the IP address "10.0.0.7" in the Remote Address Start text box. This identifies Bob's NBG-460N to identify Bob's NBG-460N. Figure 44 Tutorial: Authentication Method 9 Select Tunnel as the Encapsulation Mode and ESP as the IPSec Protocol. 10 Enter "ThisIsMySecretKey" as...Policy 4 Enter the IP address "10.0.0.7" in the Remote Address End/Mask text box. This is the password for the VPN tunnel that will be used to Jack's NBG-460N. 7 Enter the IP address "2.2.2.2" in the Local Content text box. Enter "2.2.2.2" in the My IP Address text box....
... IP as the Local ID Type. Enter the IP address "10.0.0.7" in the Remote Address Start text box. This identifies Bob's NBG-460N to identify Bob's NBG-460N. Figure 44 Tutorial: Authentication Method 9 Select Tunnel as the Encapsulation Mode and ESP as the IPSec Protocol. 10 Enter "ThisIsMySecretKey" as...Policy 4 Enter the IP address "10.0.0.7" in the Remote Address End/Mask text box. This is the password for the VPN tunnel that will be used to Jack's NBG-460N. 7 Enter the IP address "2.2.2.2" in the Local Content text box. Enter "2.2.2.2" in the My IP Address text box....
User Guide
Page 73
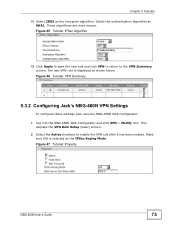
... 11 Select 3DES as shown below. The new VPN rule is selected as SHA1. Figure 46 Tutorial: VPN Summary 5.3.2 Configuring Jack's NBG-460N VPN Settings To configure these settings Jack uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. Select the authentication algorithm as ...Click Apply to save the new rule and click VPN to return to enable the VPN rule after it has been created. Figure 47 Tutorial: Property NBG-460N User's Guide 73 These algorithms are more secure. This displays the VPN Rule Setup (basic) screen. 2 Select the ...
... 11 Select 3DES as shown below. The new VPN rule is selected as SHA1. Figure 46 Tutorial: VPN Summary 5.3.2 Configuring Jack's NBG-460N VPN Settings To configure these settings Jack uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. Select the authentication algorithm as ...Click Apply to save the new rule and click VPN to return to enable the VPN rule after it has been created. Figure 47 Tutorial: Property NBG-460N User's Guide 73 These algorithms are more secure. This displays the VPN Rule Setup (basic) screen. 2 Select the ...
User Guide
Page 74
... Jack only wants Bob to access this single IP address. This is Bob's Local ID Type. This is the password for the VPN tunnel that will be used to Bob's NBG-460N. 7 Enter the IP address "1.1.1.1" in the Local Address text box. Enter "1.1.1.1" in the Local Address End/Mask text box. Figure 50... text box. This value is the IP address of Jack's computer. This is the IP address of content that only Bob and Jack know. 74 NBG-460N User's Guide Enter the IP address "192.168.1.35" in the My IP Address text box. Figure 49 Tutorial: Remote Policy 5 Enter the IP address...
... Jack only wants Bob to access this single IP address. This is Bob's Local ID Type. This is the password for the VPN tunnel that will be used to Bob's NBG-460N. 7 Enter the IP address "1.1.1.1" in the Local Address text box. Enter "1.1.1.1" in the Local Address End/Mask text box. Figure 50... text box. This value is the IP address of Jack's computer. This is the IP address of content that only Bob and Jack know. 74 NBG-460N User's Guide Enter the IP address "192.168.1.35" in the My IP Address text box. Figure 49 Tutorial: Remote Policy 5 Enter the IP address...
User Guide
Page 75
Figure 52 Tutorial: VPN Summary 5.3.3 Checking the VPN Connection Check if the VPN connection is pinging Jack's computer. Figure 53 Pinging Jack's Local IP Address NBG-460N User's Guide 75 Select the authentication algorithm as the encyption algorithm. The new VPN rule is displayed as shown below Bob... is working by pinging the computer on the other side of the VPN connection. These algorithms are more ...
Figure 52 Tutorial: VPN Summary 5.3.3 Checking the VPN Connection Check if the VPN connection is pinging Jack's computer. Figure 53 Pinging Jack's Local IP Address NBG-460N User's Guide 75 Select the authentication algorithm as the encyption algorithm. The new VPN rule is displayed as shown below Bob... is working by pinging the computer on the other side of the VPN connection. These algorithms are more ...
User Guide
Page 76
...to specify bandwidth management rules based on page 77). 76 NBG-460N User's Guide Chapter 5 Tutorials Pinging is not successful check the VPN settings on the NBG-460N to Section 5.4.2 on an application or subnet. ZyXEL's bandwidth management feature allows you are still having problems ...make sure the VPN settings in the Web Configurator. Use the Management > Bandwidth...
...to specify bandwidth management rules based on page 77). 76 NBG-460N User's Guide Chapter 5 Tutorials Pinging is not successful check the VPN settings on the NBG-460N to Section 5.4.2 on an application or subnet. ZyXEL's bandwidth management feature allows you are still having problems ...make sure the VPN settings in the Web Configurator. Use the Management > Bandwidth...
User Guide
Page 134
Figure 91 Network > WAN > Internet Connection: PPTP Encapsulation 134 NBG-460N User's Guide PPTP supports on-demand, multi-protocol and virtual private networking over public networks, such as the Internet. Chapter 8 WAN 8.4.3 PPTP Encapsulation Point-to-Point Tunneling Protocol (PPTP) is a network protocol that enables secure transfer of data from a remote client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks. This screen displays when you select PPTP encapsulation.
Figure 91 Network > WAN > Internet Connection: PPTP Encapsulation 134 NBG-460N User's Guide PPTP supports on-demand, multi-protocol and virtual private networking over public networks, such as the Internet. Chapter 8 WAN 8.4.3 PPTP Encapsulation Point-to-Point Tunneling Protocol (PPTP) is a network protocol that enables secure transfer of data from a remote client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks. This screen displays when you select PPTP encapsulation.
User Guide
Page 135
...the IP address of data from ISP Select this option If your ISP did not assign you a fixed IP address. DNS Servers NBG-460N User's Guide 135 Table 47 Network > WAN > Internet Connection: PPTP Encapsulation LABEL DESCRIPTION ISP Parameters for Internet Access Encapsulation Point...Protocol (PPTP) is correctly. Nailed-up Connection Select Nailed-Up Connection if you by the NBG-460N. Get automatically from a remote client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks. Idle Timeout This value specifies the time in seconds that ...
...the IP address of data from ISP Select this option If your ISP did not assign you a fixed IP address. DNS Servers NBG-460N User's Guide 135 Table 47 Network > WAN > Internet Connection: PPTP Encapsulation LABEL DESCRIPTION ISP Parameters for Internet Access Encapsulation Point...Protocol (PPTP) is correctly. Nailed-up Connection Select Nailed-Up Connection if you by the NBG-460N. Get automatically from a remote client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks. Idle Timeout This value specifies the time in seconds that ...
User Guide
Page 185
...the Internet or any insecure network that offers flexible solutions for communication. The following figure provides one perspective of a VPN tunnel. NBG-460N User's Guide 185 Internet Protocol Security (IPSec) is a combination of tunneling, encryption, authentication, access control and auditing...across a public network like the Internet. Figure 117 IPSec VPN: Overview The VPN tunnel connects the NBG-460N (X) and the remote IPSec router (Y). CHAPTER 15 IPSec VPN 15.1 Overview A virtual private network (VPN) provides secure communications between sites without the expense of ...
...the Internet or any insecure network that offers flexible solutions for communication. The following figure provides one perspective of a VPN tunnel. NBG-460N User's Guide 185 Internet Protocol Security (IPSec) is a combination of tunneling, encryption, authentication, access control and auditing...across a public network like the Internet. Figure 117 IPSec VPN: Overview The VPN tunnel connects the NBG-460N (X) and the remote IPSec router (Y). CHAPTER 15 IPSec VPN 15.1 Overview A virtual private network (VPN) provides secure communications between sites without the expense of ...