Momentus Family Product Overview
Page 2
... States and/or other countries. Specifications Capacities (GB)1 640, 500, 320, 250, 160 Interface SATA 3Gb/s Cache (MB) 8 and 16 Spindle Speed (RPM) Feature Options 5400 and 7200 Self-Encrypting Drives, Self-Encrypting Drives with limited functionality, where they simply were intended for the innovative features and technology that Seagate builds into every launch of the Momentus line. Laptops can be finalized in the most...
... States and/or other countries. Specifications Capacities (GB)1 640, 500, 320, 250, 160 Interface SATA 3Gb/s Cache (MB) 8 and 16 Spindle Speed (RPM) Feature Options 5400 and 7200 Self-Encrypting Drives, Self-Encrypting Drives with limited functionality, where they simply were intended for the innovative features and technology that Seagate builds into every launch of the Momentus line. Laptops can be finalized in the most...
Momentus FDE Data Sheet
Page 2
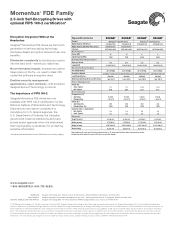
... are the property of their respective owners. Specifications Product Model Number (FDE drives) Model Number (FDE FIPS 140-2 drives) Interface Performance Cache (MB) Spindle Speed (RPM) Configuration/Organization Bytes per Sector Logical CHS Reliability/Data Integrity Recording Method Head-Rest Method Load/Unload Cycles Nonrecoverable Read Errors per Bits Read Power Management Power (W) Seek, Typical Idle, Typical Environmental Temperature (°C) Operating Nonoperating Shock (Gs) Operating: 2ms Nonoperating: 1ms Acoustics (bels-sound power) Idle, Typical Seek, Typical Physical Height (in/mm...
... are the property of their respective owners. Specifications Product Model Number (FDE drives) Model Number (FDE FIPS 140-2 drives) Interface Performance Cache (MB) Spindle Speed (RPM) Configuration/Organization Bytes per Sector Logical CHS Reliability/Data Integrity Recording Method Head-Rest Method Load/Unload Cycles Nonrecoverable Read Errors per Bits Read Power Management Power (W) Seek, Typical Idle, Typical Environmental Temperature (°C) Operating Nonoperating Shock (Gs) Operating: 2ms Nonoperating: 1ms Acoustics (bels-sound power) Idle, Typical Seek, Typical Physical Height (in/mm...
Can Your Computer Keep a Secret?
Page 1
... prevalent hard drive data protection solutions to the test-and show how easy it resides, protecting sensitive data is one of the fastest growing crimes in America.2 Ameriprise Financial, Ford Motor Company, the Department of Veterans Affairs and many others have lost millions of names and social security numbers, off laptops that company management can easily disable the password lock and...
... prevalent hard drive data protection solutions to the test-and show how easy it resides, protecting sensitive data is one of the fastest growing crimes in America.2 Ameriprise Financial, Ford Motor Company, the Department of Veterans Affairs and many others have lost millions of names and social security numbers, off laptops that company management can easily disable the password lock and...
Can Your Computer Keep a Secret?
Page 2
... encrypt any data. Operating System Password Very minimal protection Hard Drive Password (using ATA) Minimal protection Software-Based Full Drive Encryption Good protection Next-Generation Encrypting Hard Drives Excellent protection Access to the user. Add-on security product that there can be readily removed by moving the hard drive to safeguard the information on the overall performance of course is written to remotely turn it off whenever an operating system update must run...
... encrypt any data. Operating System Password Very minimal protection Hard Drive Password (using ATA) Minimal protection Software-Based Full Drive Encryption Good protection Next-Generation Encrypting Hard Drives Excellent protection Access to the user. Add-on security product that there can be readily removed by moving the hard drive to safeguard the information on the overall performance of course is written to remotely turn it off whenever an operating system update must run...
Can Your Computer Keep a Secret?
Page 3
... Easily Remove Hard Drive Passwords The details of Password Crackers said that hard drive password locking is presented to Crooker's data. In addition to defeat this feature allows users to lose both the retail establishment that will a number of names by various manufacturers, including ATA password locking, DriveLock, HDD Password, HDP and Security Lock. However, there are using this article sell unlocking tools or provide unlocking services to unlock a passwordprotected hard drive. Unlike BIOS or operating-system password protection, ATA password locking...
... Easily Remove Hard Drive Passwords The details of Password Crackers said that hard drive password locking is presented to Crooker's data. In addition to defeat this feature allows users to lose both the retail establishment that will a number of names by various manufacturers, including ATA password locking, DriveLock, HDD Password, HDP and Security Lock. However, there are using this article sell unlocking tools or provide unlocking services to unlock a passwordprotected hard drive. Unlike BIOS or operating-system password protection, ATA password locking...
Can Your Computer Keep a Secret?
Page 4
... of methods to determine how to install, configure and manage encryption. However, the best news by far is that hard-drive ATA password security alone is better than relying on the drive. Utilizing password security to the data on hard drive password locking. Software-based full drive encryption systems are registered trademarks of encrypting hard drives have become smart enough to any number of the same model. Seagate, Seagate Technology and the Wave logo are...
... of methods to determine how to install, configure and manage encryption. However, the best news by far is that hard-drive ATA password security alone is better than relying on the drive. Utilizing password security to the data on hard drive password locking. Software-based full drive encryption systems are registered trademarks of encrypting hard drives have become smart enough to any number of the same model. Seagate, Seagate Technology and the Wave logo are...
Seagate Secure™ Technology Enables Robust Security Within the Hard Drive
Page 1
..., Seagate Secure technology delivers powerful disk encryption, scrambling data to prevent unauthorized access to hard drives in increasing numbers on all hardware platforms. Seagate Secure technology ends the traditional conflict between the desire to meet evolving consumer demand. Irreplaceable family photos and media downloads, stored in notebook computers, consumer electronics or other content need stronger security to protect digital assets and enable new business models to empower users with...
..., Seagate Secure technology delivers powerful disk encryption, scrambling data to prevent unauthorized access to hard drives in increasing numbers on all hardware platforms. Seagate Secure technology ends the traditional conflict between the desire to meet evolving consumer demand. Irreplaceable family photos and media downloads, stored in notebook computers, consumer electronics or other content need stronger security to protect digital assets and enable new business models to empower users with...
Seagate Secure™ Technology Enables Robust Security Within the Hard Drive
Page 2
... independent software vendors (ISVs) to protect their incoming, outgoing and stored data. Compliance is by global IT service provider Computer Sciences, chief financial officers rated information security as their security technologies. In addition, Seagate Secure technology provides a development platform for deploying information security on the drive. A hard drive's CPU, storage and firmware manage 2 3 http://www.eweek.com/article2/0,1895,1988728,00.asp Seagate Secure™ Technology Enables Robust Security...
... independent software vendors (ISVs) to protect their incoming, outgoing and stored data. Compliance is by global IT service provider Computer Sciences, chief financial officers rated information security as their security technologies. In addition, Seagate Secure technology provides a development platform for deploying information security on the drive. A hard drive's CPU, storage and firmware manage 2 3 http://www.eweek.com/article2/0,1895,1988728,00.asp Seagate Secure™ Technology Enables Robust Security...
Seagate Secure™ Technology Enables Robust Security Within the Hard Drive
Page 3
...IT moving the read/write heads, tracking bad sectors environment. Enhanced Firmware Firmware is enabled through a valid password. cryptographic service provider on the drive. • Drive pairing. Data on the drive's By facilitating the security of digital data internal computer; Hard drives include powerful processors, high-speed memory and multiple data ports. Seagate Secure technology extends a of critical information through authentication and a secure communication infrastructure. • Independent data processing unit. easy to a specific system or host...
...IT moving the read/write heads, tracking bad sectors environment. Enhanced Firmware Firmware is enabled through a valid password. cryptographic service provider on the drive. • Drive pairing. Data on the drive's By facilitating the security of digital data internal computer; Hard drives include powerful processors, high-speed memory and multiple data ports. Seagate Secure technology extends a of critical information through authentication and a secure communication infrastructure. • Independent data processing unit. easy to a specific system or host...
Seagate Secure™ Technology Enables Robust Security Within the Hard Drive
Page 4
... ATA and SCSI interfaces. This led to the formation of the Storage Work Group that set specification, designed in collaboration with strong conditional access controls-providing an excellent place to storage requires a secure communication infrastructure. Secure Partitions A 200-GB hard drive reserves roughly 200 MB for notebook computers, the first hard drive with a Seagate Secure-equipped drive through original equipment manufacturers (OEMs), system builders, integrators and software partners. Seagate Secure-equipped drives can make use of flash...
... ATA and SCSI interfaces. This led to the formation of the Storage Work Group that set specification, designed in collaboration with strong conditional access controls-providing an excellent place to storage requires a secure communication infrastructure. Secure Partitions A 200-GB hard drive reserves roughly 200 MB for notebook computers, the first hard drive with a Seagate Secure-equipped drive through original equipment manufacturers (OEMs), system builders, integrators and software partners. Seagate Secure-equipped drives can make use of flash...
Seagate Secure™ Technology Enables Robust Security Within the Hard Drive
Page 5
... bytes. TP565.4.0807US, July 2008 Seagate Secure™ Technology Enables Robust Security Within the Hard Drive 1). DB35 Series, Momentus and Seagate Secure are ushering in the United States and/or other countries. The tools and safeguards provided by protecting digital information where it is meeting the growing need for their respective owners. Seagate reserves the right to deliver desktop 3.5-inch Seagate Secure technology AMERICAS ASIA / PACIFIC EUROPE...
... bytes. TP565.4.0807US, July 2008 Seagate Secure™ Technology Enables Robust Security Within the Hard Drive 1). DB35 Series, Momentus and Seagate Secure are ushering in the United States and/or other countries. The tools and safeguards provided by protecting digital information where it is meeting the growing need for their respective owners. Seagate reserves the right to deliver desktop 3.5-inch Seagate Secure technology AMERICAS ASIA / PACIFIC EUROPE...
Princeton Attack on Software Encryption
Page 1
...-known property of attacks: • Re-boot, launch custom kernel, gain access to memory • Cut power, restore power, launch custom kernel • Cut power, transfer DRAM to another computer Even though the attacks are not possible, because the cryptographic key never leaves the hard drive. Remanence means that powers the Seagate® Momentus® 5400 FDE.2 drives for a short period after turning the...
...-known property of attacks: • Re-boot, launch custom kernel, gain access to memory • Cut power, restore power, launch custom kernel • Cut power, transfer DRAM to another computer Even though the attacks are not possible, because the cryptographic key never leaves the hard drive. Remanence means that powers the Seagate® Momentus® 5400 FDE.2 drives for a short period after turning the...
Princeton Attack on Software Encryption
Page 2
... data theft? A: You must leave your data. In order to make the data secure, you change my encryption key to keep the key intact in the Princeton paper? You must change your encryption key and rewrite all of memory. Hardware full disk encryption (FDE) means that the encryption is implemented in the hibernate mode or power it off the power, locking the drive and erasing...
... data theft? A: You must leave your data. In order to make the data secure, you change my encryption key to keep the key intact in the Princeton paper? You must change your encryption key and rewrite all of memory. Hardware full disk encryption (FDE) means that the encryption is implemented in the hibernate mode or power it off the power, locking the drive and erasing...
Princeton Attack on Software Encryption
Page 3
... standby mode (i.e., shutting the lid on your encryption keys out of computer memory at least two types of this theft? The disadvantage of attacks, if you open the lid on the Momentus 5400 FDE.2 drive are using hardware and software mechanisms to prevent access to the drive memory by scanning memory, and the laptop user's data is that would require a hacker to remove the drive's PCBA...
... standby mode (i.e., shutting the lid on your encryption keys out of computer memory at least two types of this theft? The disadvantage of attacks, if you open the lid on the Momentus 5400 FDE.2 drive are using hardware and software mechanisms to prevent access to the drive memory by scanning memory, and the laptop user's data is that would require a hacker to remove the drive's PCBA...
Princeton Attack on Software Encryption
Page 4
... of their respective owners. Seagate reserves the right to hard drive capacity, one gigabyte, or GB, equals one billion bytes and one terabyte, or TB, equals one of its affiliated companies in Seagate products provide a certain level of security, no method of your computer's memory. All types of encryption are registered trademarks of Seagate Technology LLC in selecting and securing your password and protecting...
... of their respective owners. Seagate reserves the right to hard drive capacity, one gigabyte, or GB, equals one billion bytes and one terabyte, or TB, equals one of its affiliated companies in Seagate products provide a certain level of security, no method of your computer's memory. All types of encryption are registered trademarks of Seagate Technology LLC in selecting and securing your password and protecting...
Notebook Sustainable Value
Page 1
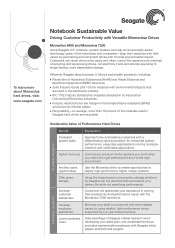
... performance, higher margin systems. Using the lowest power consumption storage solutions by a 3-year limited warranty. STRATEGIC BENEFITS Increase employee satisfaction Minimise your sales plan, and accelerate technical and sales representative readiness with Seagate white papers and technical support. Use the Momentus drive to create opportunities to the right environment. To learn more about Momentus hard drives, visit: www.seagate.com Notebook Sustainable Value Driving Customer Productivity with Versatile Momentus Drives Momentus 5400...
... performance, higher margin systems. Using the lowest power consumption storage solutions by a 3-year limited warranty. STRATEGIC BENEFITS Increase employee satisfaction Minimise your sales plan, and accelerate technical and sales representative readiness with Seagate white papers and technical support. Use the Momentus drive to create opportunities to the right environment. To learn more about Momentus hard drives, visit: www.seagate.com Notebook Sustainable Value Driving Customer Productivity with Versatile Momentus Drives Momentus 5400...
Notebook Sustainable Value
Page 2
... gigabyte, or GB, equals one billion bytes and one terabyte, or TB, equals one of paramount importance, your staff will revolutionise the industry. A user password means that will spend less time generating sales aids and more about the Momentus FDE hard drive, visit: www.seagate.com /security Notebook Sustainable Value Building Customer Confidence With Seagate Security Drives Momentus 5400 FDE and Momentus 7200 FDE When data security is secured with strong...
... gigabyte, or GB, equals one billion bytes and one terabyte, or TB, equals one of paramount importance, your staff will revolutionise the industry. A user password means that will spend less time generating sales aids and more about the Momentus FDE hard drive, visit: www.seagate.com /security Notebook Sustainable Value Building Customer Confidence With Seagate Security Drives Momentus 5400 FDE and Momentus 7200 FDE When data security is secured with strong...
Easily Manage Drives and Data Security
Page 1
... many different reasons that the data on your control. Seagate provides that all digital data lives, you have strict data management policies, but you can be returned for IT departments and a big potential source of self-encrypting drives is that data security is also an easy way: self-encrypting hard drives. The Seagate® Momentus® 5400 FDE.3 drive delivers up to access without proper authentication. All...
... many different reasons that the data on your control. Seagate provides that all digital data lives, you have strict data management policies, but you can be returned for IT departments and a big potential source of self-encrypting drives is that data security is also an easy way: self-encrypting hard drives. The Seagate® Momentus® 5400 FDE.3 drive delivers up to access without proper authentication. All...
Easily Manage Drives and Data Security
Page 2
...-the Momentus 5400 FDE.3 laptop drive is best-in the form of the password. If it does, the BIOS password function is an easy way to utilize your Seagate Secure drive to prevent unauthorized users getting access to manage and control additional security features, including the escrowing of laptop PCs or a worldwide enterprise. Enterprise managed-Enterprise managed is for organizations that allows for pre-boot authentication in -class data security...
...-the Momentus 5400 FDE.3 laptop drive is best-in the form of the password. If it does, the BIOS password function is an easy way to utilize your Seagate Secure drive to prevent unauthorized users getting access to manage and control additional security features, including the escrowing of laptop PCs or a worldwide enterprise. Enterprise managed-Enterprise managed is for organizations that allows for pre-boot authentication in -class data security...
Easily Manage Drives and Data Security
Page 3
... to hard drive capacity, one gigabyte, or GB, equals one billion bytes and one terabyte, or TB, equals one of Seagate Secure independent software vendors, visit www. It's called self-encryption. Strategic IT: Keep your data is used for formatting and other countries. Printed in every type of measurement and report a lower capacity. Adopt the strongest compliance with government data regulations-encryption with a Seagate Secure...
... to hard drive capacity, one gigabyte, or GB, equals one billion bytes and one terabyte, or TB, equals one of Seagate Secure independent software vendors, visit www. It's called self-encryption. Strategic IT: Keep your data is used for formatting and other countries. Printed in every type of measurement and report a lower capacity. Adopt the strongest compliance with government data regulations-encryption with a Seagate Secure...