FVS318 Reference Manual
Page 8
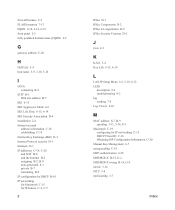
... ...B-1 Basic Router Concepts B-1 What is a Router B-1 Routing Information Protocol B-2 IP Addresses and the Internet B-2 Netmask ...B-4 Subnet Addressing B-4 Private IP Addresses B-7 Single IP Address Operation Using NAT B-8 MAC Addresses and Address Resolution Protocol B-9 viii Contents M-10146-01
... ...B-1 Basic Router Concepts B-1 What is a Router B-1 Routing Information Protocol B-2 IP Addresses and the Internet B-2 Netmask ...B-4 Subnet Addressing B-4 Private IP Addresses B-7 Single IP Address Operation Using NAT B-8 MAC Addresses and Address Resolution Protocol B-9 viii Contents M-10146-01
FVS318 Reference Manual
Page 17
About the FVS318 The FVS318 is a complete security solution that rely on Network Address Translation (NAT) for security, the FVS318 uses Stateful Packet Inspection for up to 253 users. Virtual Private Networking (VPN) The FVS318 VPN Firewall... Management • Helpful Status Indicators A description of these key features follows. The 8-port FVS318 provides highly reliable Internet access for Denial of the NETGEAR FVS318 Broadband ProSafe VPN Firewall . Key Features The FVS318 offers the following VPN features: Introduction 2-1 M-10146-01 Chapter 2 Introduction This chapter describes...
About the FVS318 The FVS318 is a complete security solution that rely on Network Address Translation (NAT) for security, the FVS318 uses Stateful Packet Inspection for up to 253 users. Virtual Private Networking (VPN) The FVS318 VPN Firewall... Management • Helpful Status Indicators A description of these key features follows. The 8-port FVS318 provides highly reliable Internet access for Denial of the NETGEAR FVS318 Broadband ProSafe VPN Firewall . Key Features The FVS318 offers the following VPN features: Introduction 2-1 M-10146-01 Chapter 2 Introduction This chapter describes...
FVS318 Reference Manual
Page 18
... or IKE keying methods, standard MD5 and SHA-1 authentication methods, and standard DES, 3DES, and AES encryption methods. A Powerful, True Firewall Unlike simple Internet sharing NAT routers, the FVS318 is compatible with many other VPN products. • Supports up to Internet locations or services that you at specified intervals.
... or IKE keying methods, standard MD5 and SHA-1 authentication methods, and standard DES, 3DES, and AES encryption methods. A Powerful, True Firewall Unlike simple Internet sharing NAT routers, the FVS318 is compatible with many other VPN products. • Supports up to Internet locations or services that you at specified intervals.
FVS318 Reference Manual
Page 19
... • DNS Proxy When DHCP is enabled and no DNS addresses are specified, the firewall provides its own address as Network Address Translation (NAT), allows the use of an inexpensive single-user ISP account. • Automatic Configuration of Attached PCs by your dynamic IP address. Protocol Support...the ISP during connection setup and forwards DNS requests from the LAN. • PPP over Ethernet (PPPoE) PPP over a DSL connection by NAT The FVS318 allows several networked PCs to the attached PCs. This technique, known as a DNS server to share an Internet account using the ...
... • DNS Proxy When DHCP is enabled and no DNS addresses are specified, the firewall provides its own address as Network Address Translation (NAT), allows the use of an inexpensive single-user ISP account. • Automatic Configuration of Attached PCs by your dynamic IP address. Protocol Support...the ISP during connection setup and forwards DNS requests from the LAN. • PPP over Ethernet (PPPoE) PPP over a DSL connection by NAT The FVS318 allows several networked PCs to the attached PCs. This technique, known as a DNS server to share an Internet account using the ...
FVS318 Reference Manual
Page 51
... that PC's IP address is entered as the Default DMZ Server, it loses much of the protection of these applications and to work properly with NAT. Chapter 5 Advanced WAN and LAN Configuration This chapter describes how to configure the advanced features of configuring your LAN TCP/IP settings. These features are...
... that PC's IP address is entered as the Default DMZ Server, it loses much of the protection of these applications and to work properly with NAT. Chapter 5 Advanced WAN and LAN Configuration This chapter describes how to configure the advanced features of configuring your LAN TCP/IP settings. These features are...
FVS318 Reference Manual
Page 55
...01 What Does UPnP Support Do for the Model FVS318 Broadband ProSafe VPN Firewall 3. As IP packets from the private LAN traverse the gateway, NAT translates a private IP address and port number to a public IP address and port number, tracking those translations to use a public address, ... FVS318 VPN Firewall that people increasingly want to keep individual sessions intact. These features can automatically solve many of the browser interface. UPnP NAT Traversal can be 26902. 4. Click Apply. These applications will not work if they a use the supplied number in the default listing ...
...01 What Does UPnP Support Do for the Model FVS318 Broadband ProSafe VPN Firewall 3. As IP packets from the private LAN traverse the gateway, NAT translates a private IP address and port number to a public IP address and port number, tracking those translations to use a public address, ... FVS318 VPN Firewall that people increasingly want to keep individual sessions intact. These features can automatically solve many of the browser interface. UPnP NAT Traversal can be 26902. 4. Click Apply. These applications will not work if they a use the supplied number in the default listing ...
FVS318 Reference Manual
Page 65
VPN communications paths are between two or more NETGEAR VPN-enabled routers is enabled and remote computers have been assigned private IP addresses. • Secure access from a remote PC, such as a branch or home ... between two or more networks, and between networks, such as a telecommuter connecting to an office network. VPN tunnels also enable access to network resources when NAT is a good way to use the virtual private networking (VPN) features of VPN Configuration Two common scenarios for configuring VPN tunnels are called tunnels. Virtual...
VPN communications paths are between two or more NETGEAR VPN-enabled routers is enabled and remote computers have been assigned private IP addresses. • Secure access from a remote PC, such as a branch or home ... between two or more networks, and between networks, such as a telecommuter connecting to an office network. VPN tunnels also enable access to network resources when NAT is a good way to use the virtual private networking (VPN) features of VPN Configuration Two common scenarios for configuring VPN tunnels are called tunnels. Virtual...
FVS318 Reference Manual
Page 68
...page B-4. 3. Enter the Local LAN start and finish Local IP addresses. 4. For a discussion of the following four options: 1. Then enter the NAT router's public (WAN) IP address or FQDN in the other VPN endpoint as the Local IPSec Identifier. A subnet of the VPN tunnel. Tunnel... mask. Each tunnel should have a unique name. A single remote address, such as members of a department on the remote LAN communications through a NAT router, select "A subnet of local addresses, such as a single PC. • If the PC is connected directly to the Internet, enter the...
...page B-4. 3. Enter the Local LAN start and finish Local IP addresses. 4. For a discussion of the following four options: 1. Then enter the NAT router's public (WAN) IP address or FQDN in the other VPN endpoint as the Local IPSec Identifier. A subnet of the VPN tunnel. Tunnel... mask. Each tunnel should have a unique name. A single remote address, such as members of a department on the remote LAN communications through a NAT router, select "A subnet of local addresses, such as a single PC. • If the PC is connected directly to the Internet, enter the...
FVS318 Reference Manual
Page 127
...specifically for private networks: 10.0.0.0 - 10.255.255.255 172.16.0.0 - 172.31.255.255 192.168.0.0 - 192.168.255.255 NETGEAR recommends that a local router or bridge recognizes which addresses are remote Private IP Addresses If your local network is isolated from this range. For... Routing, and Firewall Basics B-7 M-10146-01 In order for Management of your private network number from the Internet (for example, when using NAT), you choose your particular situation, do not create an arbitrary IP address; always follow the guidelines explained here. Regardless of IP Address Space....
...specifically for private networks: 10.0.0.0 - 10.255.255.255 172.16.0.0 - 172.31.255.255 192.168.0.0 - 192.168.255.255 NETGEAR recommends that a local router or bridge recognizes which addresses are remote Private IP Addresses If your local network is isolated from this range. For... Routing, and Firewall Basics B-7 M-10146-01 In order for Management of your private network number from the Internet (for example, when using NAT), you choose your particular situation, do not create an arbitrary IP address; always follow the guidelines explained here. Regardless of IP Address Space....
FVS318 Reference Manual
Page 128
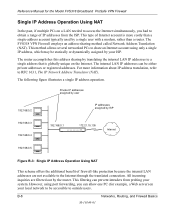
...assigned by ISP 192.168.0.3 192.168.0.4 192.168.0.1 172.21.15.105 Internet 192.168.0.5 Figure B-3: Single IP Address Operation Using NAT This scheme offers the additional benefit of Internet account is globally unique on a LAN needed to access the Internet simultaneously, you can allow ...one PC (for the Model FVS318 Broadband ProSafe VPN Firewall Single IP Address Operation Using NAT In the past, if multiple PCs on the Internet. All incoming inquiries are not available to the Internet through the translated connection. The...
...assigned by ISP 192.168.0.3 192.168.0.4 192.168.0.1 172.21.15.105 Internet 192.168.0.5 Figure B-3: Single IP Address Operation Using NAT This scheme offers the additional benefit of Internet account is globally unique on a LAN needed to access the Internet simultaneously, you can allow ...one PC (for the Model FVS318 Broadband ProSafe VPN Firewall Single IP Address Operation Using NAT In the past, if multiple PCs on the Internet. All incoming inquiries are not available to the Internet through the translated connection. The...
FVS318 Reference Manual
Page 129
...1597, Address Allocation for Private Internets, and RFC 1466, Guidelines for Management of network resources to RFC 1631, The IP Network Address Translator (NAT). The technique that only the station with a MAC address is sent, the address can be translated to an IP address in an ARP ...message so that associates the IP address with this IP address responds to resolve MAC addresses. The next time data is known as www.NETGEAR.com. Related Documents The station with the correct IP address responds with the required destination MAC address. To send data between LAN devices...
...1597, Address Allocation for Private Internets, and RFC 1466, Guidelines for Management of network resources to RFC 1631, The IP Network Address Translator (NAT). The technique that only the station with a MAC address is sent, the address can be translated to an IP address in an ARP ...message so that associates the IP address with this IP address responds to resolve MAC addresses. The next time data is known as www.NETGEAR.com. Related Documents The station with the correct IP address responds with the required destination MAC address. To send data between LAN devices...
FVS318 Reference Manual
Page 130
...the Internet through a router, an opportunity is provided by a firewall router. A greater degree of the Network Address Translation (NAT) process, the network behind the NAT router is installed, each PC on the network. B-10 M-10146-01 Networks, Routing, and Firewall Basics Many large organizations,...) server. A device on the Internet. However, there are methods by DHCP. Reference Manual for outsiders to look up addresses. A NAT router provides some protection because by outsiders on the network may act as gateway and DNS addresses) that it first contacts a DNS server...
...the Internet through a router, an opportunity is provided by a firewall router. A greater degree of the Network Address Translation (NAT) process, the network behind the NAT router is installed, each PC on the network. B-10 M-10146-01 Networks, Routing, and Firewall Basics Many large organizations,...) server. A device on the Internet. However, there are methods by DHCP. Reference Manual for outsiders to look up addresses. A NAT router provides some protection because by outsiders on the network may act as gateway and DNS addresses) that it first contacts a DNS server...
FVS318 Reference Manual
Page 131
... analyzed for state-related information associated with the ISP of the hacker. Using information from the log, the administrator can create complex patterns of the NAT router, while adding features for dealing with a hacker intrusion or attack. Stateful Packet Inspection Unlike simple Internet sharing routers, a firewall uses a process called stateful packet...
... analyzed for state-related information associated with the ISP of the hacker. Using information from the log, the administrator can create complex patterns of the NAT router, while adding features for dealing with a hacker intrusion or attack. Stateful Packet Inspection Unlike simple Internet sharing routers, a firewall uses a process called stateful packet...
FVS318 Reference Manual
Page 154
... VPN Firewall Verifying the Readiness of Your Internet Account For broadband access to the Internet, you need to accomplish this is called Network Address Translation (NAT) or IP masquerading.
... VPN Firewall Verifying the Readiness of Your Internet Account For broadband access to the Internet, you need to accomplish this is called Network Address Translation (NAT) or IP masquerading.
FVS318 Reference Manual
Page 187
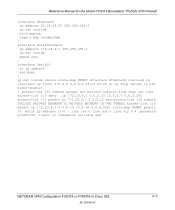
line con 0 line aux 0 line vty 0 4 password pctg5tcd3 login! ip nat inside speed auto ! access-list 110 remark except the private network from that nat rule access-list 110 deny ip 172.23.9.1 0.0.0.15 10.5.6.0 0.0.0.255 access-list 110 permit ip 172.23.9.1 0.0.0.15 ...NONAT permit 10 match ip address 110! ! interface Serial0 no scheduler allocate end NETGEAR VPN Configuration FVS318 or FVM318 to Cisco IOS F-7 M-10146-01 interface FastEthernet0 ip address 172.23.9.1 255.255.255.0 ip nat inside source route-map NONAT interface Ethernet0 overload ip classless ip route 0.0.0.0 0.0.0.0 22...
line con 0 line aux 0 line vty 0 4 password pctg5tcd3 login! ip nat inside speed auto ! access-list 110 remark except the private network from that nat rule access-list 110 deny ip 172.23.9.1 0.0.0.15 10.5.6.0 0.0.0.255 access-list 110 permit ip 172.23.9.1 0.0.0.15 ...NONAT permit 10 match ip address 110! ! interface Serial0 no scheduler allocate end NETGEAR VPN Configuration FVS318 or FVM318 to Cisco IOS F-7 M-10146-01 interface FastEthernet0 ip address 172.23.9.1 255.255.255.0 ip nat inside source route-map NONAT interface Ethernet0 overload ip classless ip route 0.0.0.0 0.0.0.0 22...
FVS318 Reference Manual
Page 211
...-way hash function, one -way hash function, meaning that it takes a message and converts it into a fixed string of the number having the most value. N NAT See "Network Address Translation" on pins 1 and 2. In MDI wiring, a PC transmits on page 10. At the hub, switch, router, or access point, the perspective...
...-way hash function, one -way hash function, meaning that it takes a message and converts it into a fixed string of the number having the most value. N NAT See "Network Address Translation" on pins 1 and 2. In MDI wiring, a PC transmits on page 10. At the hub, switch, router, or access point, the perspective...
FVS318 Reference Manual
Page 220
..., 6-19 IKE Security Association D-4 installation 2-4 Internet account address information C-18 establishing C-18 Internet Key Exchange (IKE) D-3 Internet Protocol security D-1 Intranets D-1 IP addresses C-19, C-20 and NAT B-8 and the Internet B-2 assigning B-2, B-9 auto-generated 8-3 private B-7 translating B-9 IP configuration by DHCP B-10 IP networking for Macintosh C-15 for Windows C-2, C-7 2 IPSec D-1 IPSec Components D-2 IPSec SA...
..., 6-19 IKE Security Association D-4 installation 2-4 Internet account address information C-18 establishing C-18 Internet Key Exchange (IKE) D-3 Internet Protocol security D-1 Intranets D-1 IP addresses C-19, C-20 and NAT B-8 and the Internet B-2 assigning B-2, B-9 auto-generated 8-3 private B-7 translating B-9 IP configuration by DHCP B-10 IP networking for Macintosh C-15 for Windows C-2, C-7 2 IPSec D-1 IPSec Components D-2 IPSec SA...
FVS318 Reference Manual
Page 221
... Time Protocol 4-10, 8-8 NTP 4-10, 8-8 P package contents 2-5 password restoring 8-7 PC, using to configure C-21 Perfect Forward Secrecy 6-15, 6-19 ping 5-3 Port Forwarding 5-2 port forwarding behind NAT B-8 Port Forwarding Menu 5-3 port numbers 4-5 PPP over Ethernet 2-3, C-18 PPPoE 2-3, 3-9, C-18 PPTP 3-8, 3-15 PreShared Key 6-11, 6-15, 6-17, 6-19, 6-31, 6-32 Primary DNS Server 3-9, 3-10...
... Time Protocol 4-10, 8-8 NTP 4-10, 8-8 P package contents 2-5 password restoring 8-7 PC, using to configure C-21 Perfect Forward Secrecy 6-15, 6-19 ping 5-3 Port Forwarding 5-2 port forwarding behind NAT B-8 Port Forwarding Menu 5-3 port numbers 4-5 PPP over Ethernet 2-3, C-18 PPPoE 2-3, 3-9, C-18 PPTP 3-8, 3-15 PreShared Key 6-11, 6-15, 6-17, 6-19, 6-31, 6-32 Primary DNS Server 3-9, 3-10...