User Guide
Page 4
... 54 Security Precautions 54 Security Threats Facing Wireless Networks 54 Appendix C: Upgrading Firmware 57 Appendix D: Windows Help 58 Appendix E: Finding the MAC Address and IP Address for Your Ethernet Adapter59 Windows 2000 or XP Instructions 59 Windows Vista Instructions 59 For the Router's Web-based Utility 60 Appendix F: Glossary 61 Appendix G: Specifications 68...
... 54 Security Precautions 54 Security Threats Facing Wireless Networks 54 Appendix C: Upgrading Firmware 57 Appendix D: Windows Help 58 Appendix E: Finding the MAC Address and IP Address for Your Ethernet Adapter59 Windows 2000 or XP Instructions 59 Windows Vista Instructions 59 For the Router's Web-based Utility 60 Appendix F: Glossary 61 Appendix G: Specifications 68...
User Guide
Page 5
... Figure 5-10: Router IP 17 Figure 5-11: Network Address Server Settings 17 Figure 5-12: Time Setting 17 Figure 5-13: Setup Tab - DDNS 18 Figure 5-14: Setup Tab - Wireless Security (WPA2 Enterprise) 22 Figure 5-22: Wireless Tab - Basic Wireless Settings 20 Figure 5-18: Wireless Tab - Wireless-G Broadband Router List of Figures Figure 3-1: The Router's Back Panel 6 Figure 3-2: The Router's Front Panel...
... Figure 5-10: Router IP 17 Figure 5-11: Network Address Server Settings 17 Figure 5-12: Time Setting 17 Figure 5-13: Setup Tab - DDNS 18 Figure 5-14: Setup Tab - Wireless Security (WPA2 Enterprise) 22 Figure 5-22: Wireless Tab - Basic Wireless Settings 20 Figure 5-18: Wireless Tab - Wireless-G Broadband Router List of Figures Figure 3-1: The Router's Back Panel 6 Figure 3-2: The Router's Front Panel...
User Guide
Page 8
..., which is why the network is called a WLAN, or Wireless Local Area Network. wpa (wi-fi protected access): a wireless security protocol using the Setup CD-ROM for choosing the Linksys Wireless-G Broadband Router. PCs on the Setup CD-ROM, then use , browser-based...multiplayer video games. All the while, the Wireless-G Broadband Router protects your network. spi (stateful packet inspection) firewall: a technology that allows access to secure your home or office. nat (network address translation): NAT technology translates IP addresses of a local area network to ...
..., which is why the network is called a WLAN, or Wireless Local Area Network. wpa (wi-fi protected access): a wireless security protocol using the Setup CD-ROM for choosing the Linksys Wireless-G Broadband Router. PCs on the Setup CD-ROM, then use , browser-based...multiplayer video games. All the while, the Wireless-G Broadband Router protects your network. spi (stateful packet inspection) firewall: a technology that allows access to secure your home or office. nat (network address translation): NAT technology translates IP addresses of a local area network to ...
User Guide
Page 9
... the MAC filtering and/or MAC address cloning feature of the Router. • Appendix F: Glossary This appendix gives a brief glossary of wireless networking and some problems and solutions, as well as installing the TCP/IP protocol. • Appendix E: Finding the MAC Address and IP Address for instructions about networking, such as frequently asked questions...
... the MAC filtering and/or MAC address cloning feature of the Router. • Appendix F: Glossary This appendix gives a brief glossary of wireless networking and some problems and solutions, as well as installing the TCP/IP protocol. • Appendix E: Finding the MAC Address and IP Address for instructions about networking, such as frequently asked questions...
User Guide
Page 17
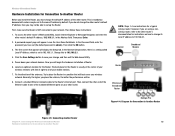
... the Router is NOT connected to your mobile stations. 7. Then follow these instructions: 1. The first screen that will be able to set up the Router. Try to place the Router in the Address field. Then, connect the other router. Then...Linksys router; NOTE: Steps 1-4 are using a nonLinksys router, refer to the other router. First, make sure the Router is usually at the center of your network devices. In the Network Setup section, there is a setting called Local IP Address, which is set to all of the other router's documentation for instructions on your wireless...
... the Router is NOT connected to your mobile stations. 7. Then follow these instructions: 1. The first screen that will be able to set up the Router. Try to place the Router in the Address field. Then, connect the other router. Then...Linksys router; NOTE: Steps 1-4 are using a nonLinksys router, refer to the other router. First, make sure the Router is usually at the center of your network devices. In the Network Setup section, there is a setting called Local IP Address, which is set to all of the other router's documentation for instructions on your wireless...
User Guide
Page 19
...The first time you open the Web-based Utility, use this protocol. HAVE YOU: Enabled TCP/IP on your ISP. • Management. Figure 5-1: Password Screen Chapter 6: Configuring the Wireless-G Broadband Router 12 Overview The utility can be available after you can set a new password from its default.... Utility to run the Setup Wizard on the Setup CD-ROM, then you click one of the Router. Wireless-G Broadband Router Chapter 5: Configuring the Wireless-G Broadband Router Overview Linksys recommends using the Setup Wizard on the Setup CD-ROM. If you do not wish to configure the...
...The first time you open the Web-based Utility, use this protocol. HAVE YOU: Enabled TCP/IP on your ISP. • Management. Figure 5-1: Password Screen Chapter 6: Configuring the Wireless-G Broadband Router 12 Overview The utility can be available after you can set a new password from its default.... Utility to run the Setup Wizard on the Setup CD-ROM, then you click one of the Router. Wireless-G Broadband Router Chapter 5: Configuring the Wireless-G Broadband Router Overview Linksys recommends using the Setup Wizard on the Setup CD-ROM. If you do not wish to configure the...
User Guide
Page 20
... you with the Subnet Mask. Basic Setup Figure 5-3: DHCP Connection Type Chapter 6: Configuring the Wireless-G Broadband Router The Setup Tab - This allows you are connecting through your ISP supports DHCP or you are required to use a permanent IP address to connect to Automatic Configuration - Most of Internet connection your changes. If you to...
... you with the Subnet Mask. Basic Setup Figure 5-3: DHCP Connection Type Chapter 6: Configuring the Wireless-G Broadband Router The Setup Tab - This allows you are connecting through your ISP supports DHCP or you are required to use a permanent IP address to connect to Automatic Configuration - Most of Internet connection your changes. If you to...
User Guide
Page 21
...Connect on Demand: Max Idle Time. To use this option, click the radio button next to Keep Alive. Chapter 6: Configuring the Wireless-G Broadband Router The Setup Tab - If they use PPPoE (Point-to-Point Protocol over Ethernet) to check the Internet connection. If your Internet connection... on Demand: Max Idle Time. Specify Internet IP Address. Gateway. In the Max Idle Time field, enter the number of minutes you want to access the Internet again. The default Redial Period is 30 seconds. • PPTP. Wireless-G Broadband Router • PPPoE. In the Max Idle Time...
...Connect on Demand: Max Idle Time. To use this option, click the radio button next to Keep Alive. Chapter 6: Configuring the Wireless-G Broadband Router The Setup Tab - If they use PPPoE (Point-to-Point Protocol over Ethernet) to check the Internet connection. If your Internet connection... on Demand: Max Idle Time. Specify Internet IP Address. Gateway. In the Max Idle Time field, enter the number of minutes you want to access the Internet again. The default Redial Period is 30 seconds. • PPTP. Wireless-G Broadband Router • PPPoE. In the Max Idle Time...
User Guide
Page 22
... Password. Figure 5-7: L2TP Connection Type Figure 5-8: HeartBeat Signal Connection Type Chapter 6: Configuring the Wireless-G Broadband Router 15 The Setup Tab - If you select this option, the Router will periodically check your ISP is used by some ISP's in Australia only. Heart Beat Server.... If you wish to activate Connect on Demand: Max Idle Time. Wireless-G Broadband Router • L2TP. Connect on Demand, click the radio button. Specify IP Address of time (Max Idle Time). Layer 2 Tunneling Protocol (L2TP) is Telstra, then select ...
... Password. Figure 5-7: L2TP Connection Type Figure 5-8: HeartBeat Signal Connection Type Chapter 6: Configuring the Wireless-G Broadband Router 15 The Setup Tab - If you select this option, the Router will periodically check your ISP is used by some ISP's in Australia only. Heart Beat Server.... If you wish to activate Connect on Demand: Max Idle Time. Wireless-G Broadband Router • L2TP. Connect on Demand, click the radio button. Specify IP Address of time (Max Idle Time). Layer 2 Tunneling Protocol (L2TP) is Telstra, then select ...
User Guide
Page 24
...Internet addresses or URLs. Enter a value for daylight savings time.)4 Figure 5-10: Router IP Figure 5-11: Network Address Server Settings Figure 5-12: Time Setting Chapter 6: Configuring the Wireless-G Broadband Router 17 The Setup Tab - Otherwise, leave this pull-down menu. (You can ... Domain Name System (DNS) is 192.168.1.100. You can be allowed connection to the Router with when issuing IP addresses. Wireless-G Broadband Router Router IP This presents both the Router's IP Address and Subnet Mask as a DHCP server for quicker access to functioning DNS servers. Network ...
...Internet addresses or URLs. Enter a value for daylight savings time.)4 Figure 5-10: Router IP Figure 5-11: Network Address Server Settings Figure 5-12: Time Setting Chapter 6: Configuring the Wireless-G Broadband Router 17 The Setup Tab - Otherwise, leave this pull-down menu. (You can ... Domain Name System (DNS) is 192.168.1.100. You can be allowed connection to the Router with when issuing IP addresses. Wireless-G Broadband Router Router IP This presents both the Router's IP Address and Subnet Mask as a DHCP server for quicker access to functioning DNS servers. Network ...
User Guide
Page 25
... the MAC address. To have membership. Clone Your PC's MAC Address. DDNS Figure 5-14: Setup Tab - Status. User Name. Internet IP Address. Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to access the Internet. ...Enter the User Name for identification. MAC Address Clone Chapter 6: Configuring the Wireless-G Broadband Router 18 The Setup Tab - From this button will require you assign a fixed host and domain name to cancel your ISP, you may...
... the MAC address. To have membership. Clone Your PC's MAC Address. DDNS Figure 5-14: Setup Tab - Status. User Name. Internet IP Address. Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to access the Internet. ...Enter the User Name for identification. MAC Address Clone Chapter 6: Configuring the Wireless-G Broadband Router 18 The Setup Tab - From this button will require you assign a fixed host and domain name to cancel your ISP, you may...
User Guide
Page 26
...Subnet Mask determines which portion of advanced functions you whether the Destination IP Address is the IP address of hops between the source and the destination. Wireless-G Broadband Router The Setup Tab - Destination LAN IP. Advanced Routing (Bridge) Click the Show Routing Table button to ...select the type(s) of a Destination LAN IP address is a pre-determined pathway that allows for ...
...Subnet Mask determines which portion of advanced functions you whether the Destination IP Address is the IP address of hops between the source and the destination. Wireless-G Broadband Router The Setup Tab - Destination LAN IP. Advanced Routing (Bridge) Click the Show Routing Table button to ...select the type(s) of a Destination LAN IP address is a pre-determined pathway that allows for ...
User Guide
Page 28
... - Select the type of 8-63 characters. Enter the RADIUS server's IP Address and port number, along with a RADIUS server. Wireless Security This option features WPA used when a RADIUS server is stronger than WEP encryption. Then enter a Group Key Renewal period, which instructs the Router how often it should only be used in your...
... - Select the type of 8-63 characters. Enter the RADIUS server's IP Address and port number, along with a RADIUS server. Wireless Security This option features WPA used when a RADIUS server is stronger than WEP encryption. Then enter a Group Key Renewal period, which instructs the Router how often it should only be used in your...
User Guide
Page 29
...WPA2 used when a RADIUS server is connected to use, AES, or TKIP + AES. Wireless Security Figure 5-21: Wireless Tab - Then enter a Group Key Renewal period, which instructs the Router how often it should only be used in coordination with a RADIUS server. (This should ...between the Router and the server. Last, enter a Key Renewal Timeout, which instructs the Router how often it should change the encryption keys. Enter the RADIUS server's IP Address and port number, along with dynamic encryption keys. Select the type of 8-63 characters. Wireless-G Broadband Router WPA2 Personal...
...WPA2 used when a RADIUS server is connected to use, AES, or TKIP + AES. Wireless Security Figure 5-21: Wireless Tab - Then enter a Group Key Renewal period, which instructs the Router how often it should only be used in coordination with a RADIUS server. (This should ...between the Router and the server. Last, enter a Key Renewal Timeout, which instructs the Router how often it should change the encryption keys. Enter the RADIUS server's IP Address and port number, along with dynamic encryption keys. Select the type of 8-63 characters. Wireless-G Broadband Router WPA2 Personal...
User Guide
Page 30
Wireless Security (RADIUS) WEP. WEP is a basic encryption method, which is connected to the Router.) First, enter the RADIUS server's IP Address and port number, along with a RADIUS server. (This should only be used when a RADIUS server is not as ...If you are using WEP encryption, always remember that each device in coordination with a key shared between the Router and the server. Wireless Security Figure 5-23: Wireless Tab - Wireless Security (WEP) 23 Wireless-G Broadband Router RADIUS. Change these settings as WPA. To use WEP, select a Default Transmit Key (choose which Key...
Wireless Security (RADIUS) WEP. WEP is a basic encryption method, which is connected to the Router.) First, enter the RADIUS server's IP Address and port number, along with a RADIUS server. (This should only be used when a RADIUS server is not as ...If you are using WEP encryption, always remember that each device in coordination with a key shared between the Router and the server. Wireless Security Figure 5-23: Wireless Tab - Wireless Security (WEP) 23 Wireless-G Broadband Router RADIUS. Change these settings as WPA. To use WEP, select a Default Transmit Key (choose which Key...
User Guide
Page 34
...Figure 5-27: Security Tab - Both functions of your network environment. PPTP Pass-through an IP network. L2TP Pass-Through is enabled by default. Wireless-G Broadband Router The Security Tab - Enable the Block WAN Request feature by checking the box beside Block Anonymous... feature also reinforces your changes. Select Disabled to allow IP multicast packets to disable this feature. Select Enabled to filter port 113, or Disabled to be tunneled through . Chapter 6: Configuring the Wireless-G Broadband Router The Security Tab - Firewall Figure 5-28: Security Tab...
...Figure 5-27: Security Tab - Both functions of your network environment. PPTP Pass-through an IP network. L2TP Pass-Through is enabled by default. Wireless-G Broadband Router The Security Tab - Enable the Block WAN Request feature by checking the box beside Block Anonymous... feature also reinforces your changes. Select Disabled to allow IP multicast packets to disable this feature. Select Enabled to filter port 113, or Disabled to be tunneled through . Chapter 6: Configuring the Wireless-G Broadband Router The Security Tab - Firewall Figure 5-28: Security Tab...
User Guide
Page 35
... Deny or Allow, depending on whether you listed on this policy, click the radio button beside Enable. 3. Chapter 6: Configuring the Wireless-G Broadband Router The Access Restrictions Tab - Select the individual days during which the policy will display that policy's number and click the Delete button.... deleted from the drop-down menu will be enforced. Policies are disabled by MAC Address or IP Address. Internet Access 2. The List of PCs 28 Wireless-G Broadband Router Change these settings as described here and click the Save Settings button to apply your changes or...
... Deny or Allow, depending on whether you listed on this policy, click the radio button beside Enable. 3. Chapter 6: Configuring the Wireless-G Broadband Router The Access Restrictions Tab - Select the individual days during which the policy will display that policy's number and click the Delete button.... deleted from the drop-down menu will be enforced. Policies are disabled by MAC Address or IP Address. Internet Access 2. The List of PCs 28 Wireless-G Broadband Router Change these settings as described here and click the Save Settings button to apply your changes or...
User Guide
Page 36
...keyword in a separate field next to manage. Enter a Policy Name in the Service Name field. Inbound Traffic Chapter 6: Configuring the Wireless-G Broadband Router 29 The Access Restrictions Tab - If the service you want to block is not listed or you want to manage, or select Any.... To create an Inbound Traffic policy: 1. Enter the destination IP address whose traffic you want to Website Blocking by selecting services from the list on the right. Wireless-G Broadband Router 8. You can filter access to various services accessed over the Internet, such as...
...keyword in a separate field next to manage. Enter a Policy Name in the Service Name field. Inbound Traffic Chapter 6: Configuring the Wireless-G Broadband Router 29 The Access Restrictions Tab - If the service you want to block is not listed or you want to manage, or select Any.... To create an Inbound Traffic policy: 1. Enter the destination IP address whose traffic you want to Website Blocking by selecting services from the list on the right. Wireless-G Broadband Router 8. You can filter access to various services accessed over the Internet, such as...
User Guide
Page 37
... effect, or select Everyday. Start/End. Port Range Forward Chapter 6: Configuring the Wireless-G Broadband Router 30 The Applications and Gaming Tab - Application. IP Address. Figure 5-34: Applications and Gaming Tab - Decide which days and what ...running the specific application. Click the appropriate option, Deny or Allow, depending on each application, enter the IP Address of hours and minutes during which the policy will be up public services on your network, such... Change these settings as videoconferencing or online gaming. Wireless-G Broadband Router 6.
... effect, or select Everyday. Start/End. Port Range Forward Chapter 6: Configuring the Wireless-G Broadband Router 30 The Applications and Gaming Tab - Application. IP Address. Figure 5-34: Applications and Gaming Tab - Decide which days and what ...running the specific application. Click the appropriate option, Deny or Allow, depending on each application, enter the IP Address of hours and minutes during which the policy will be up public services on your network, such... Change these settings as videoconferencing or online gaming. Wireless-G Broadband Router 6.
User Guide
Page 38
.... Enter the ending port number of the trigger. Figure 5-35: Applications and Gaming Tab Port Triggering Chapter 6: Configuring the Wireless-G Broadband Router 31 The Applications & Gaming Tab - Enter the ending port number of IP address and port mapping rules. Forwarded Range For each application, list the triggered port number range. Port Triggering Check...
.... Enter the ending port number of the trigger. Figure 5-35: Applications and Gaming Tab Port Triggering Chapter 6: Configuring the Wireless-G Broadband Router 31 The Applications & Gaming Tab - Enter the ending port number of IP address and port mapping rules. Forwarded Range For each application, list the triggered port number range. Port Triggering Check...