Security Guide
Page 3
... Security Policy, the FIPS 140-2 Validation Documentation is proprietary to Lexmark and is releasable only under appropriate non-disclosure agreements. For access to this document, the Submission Package contains: Vendor Evidence document Finite State Machine Other supporting documentation as PrintCryption, PrintCryption module, cryptographic module, firmware module, or module. More information about the FIPS 140-2 standard and validation program...
... Security Policy, the FIPS 140-2 Validation Documentation is proprietary to Lexmark and is releasable only under appropriate non-disclosure agreements. For access to this document, the Submission Package contains: Vendor Evidence document Finite State Machine Other supporting documentation as PrintCryption, PrintCryption module, cryptographic module, firmware module, or module. More information about the FIPS 140-2 standard and validation program...
Security Guide
Page 7
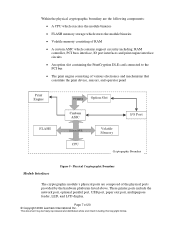
...memory storage which stores the module binaries • Volatile memory consisting of RAM • A custom ASIC which contains support circuitry including: RAM controller, PCI buss interface, IO port interfaces and print engine interface circuits. • An option slot containing the PrintCryption DLE card connected to the PCI bus... Print Engine FLASH PCI BUS Option Slot Custom ASIC System BUS CPU Volatile Memory I/O Port Cryptographic Boundary Module Interfaces Figure 5 - Within the physical cryptographic boundary are composed of 20 © Copyright 2009 Lexmark International Inc.
...memory storage which stores the module binaries • Volatile memory consisting of RAM • A custom ASIC which contains support circuitry including: RAM controller, PCI buss interface, IO port interfaces and print engine interface circuits. • An option slot containing the PrintCryption DLE card connected to the PCI bus... Print Engine FLASH PCI BUS Option Slot Custom ASIC System BUS CPU Volatile Memory I/O Port Cryptographic Boundary Module Interfaces Figure 5 - Within the physical cryptographic boundary are composed of 20 © Copyright 2009 Lexmark International Inc.
Security Guide
Page 9
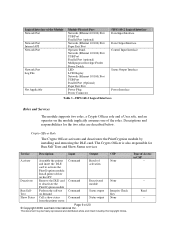
... Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on the module implicitly assumes one of the Module Network Port Network Port Internal API Network Port Network Port Log File Not Applicable Module Physical Port Network (Ethernet... © Copyright 2009 Lexmark International Inc. Crypto Officer Role The Crypto Officer activates and deactivates the PrintCryption module by installing and removing the DLE card. Type of Access to deactivate the PrintCryption module Perform the self-test on host PC Remove the DLE card to CSP -- -Read...
... Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on the module implicitly assumes one of the Module Network Port Network Port Internal API Network Port Network Port Log File Not Applicable Module Physical Port Network (Ethernet... © Copyright 2009 Lexmark International Inc. Crypto Officer Role The Crypto Officer activates and deactivates the PrintCryption module by installing and removing the DLE card. Type of Access to deactivate the PrintCryption module Perform the self-test on host PC Remove the DLE card to CSP -- -Read...
Security Guide
Page 11
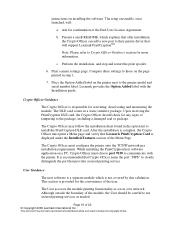
... method uses a 1024bit key length providing 80-bits of 20 © Copyright 2009 Lexmark International Inc. Zeroized by overwriting the flash image. Stored on flash in plaintext. Held... of Key and Critical Security Parameters Page 11 of security. PKCS#1.5 SHS- Imported in encrypted form (RSA key transport) Internally generated according to FIPS PUB 186-3 and IG A.6 Internally...data for printing Key transport Key transport Firmware Integrity test RNG RNG Table 7 - The module supports the following FIPS-Approved algorithms. Algorithm AES ECB, CBC mode decryption - Zeroized after the...
... method uses a 1024bit key length providing 80-bits of 20 © Copyright 2009 Lexmark International Inc. Zeroized by overwriting the flash image. Stored on flash in plaintext. Held... of Key and Critical Security Parameters Page 11 of security. PKCS#1.5 SHS- Imported in encrypted form (RSA key transport) Internally generated according to FIPS PUB 186-3 and IG A.6 Internally...data for printing Key transport Key transport Firmware Integrity test RNG RNG Table 7 - The module supports the following FIPS-Approved algorithms. Algorithm AES ECB, CBC mode decryption - Zeroized after the...
Security Guide
Page 16
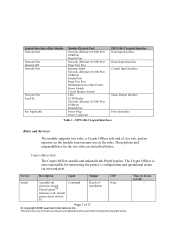
... the Crypto Officer can add a new port to their printer driver that Lexmark PrintCryption Card is responsible for activating, deactivating and monitoring the module. c. Print a menu settings page. Lexmark provides the Option Added label with the printer. The DLE card comes in step 1. 7. The Crypto Officer may be careful to use secured...the Installation guide. Crypto Officer Guidance The Crypto Officer is displayed under the Installed Features section of 20 © Copyright 2009 Lexmark International Inc. The setup executable, once launched, will support Lexmark PrintCryptionTM.
... the Crypto Officer can add a new port to their printer driver that Lexmark PrintCryption Card is responsible for activating, deactivating and monitoring the module. c. Print a menu settings page. Lexmark provides the Option Added label with the printer. The DLE card comes in step 1. 7. The Crypto Officer may be careful to use secured...the Installation guide. Crypto Officer Guidance The Crypto Officer is displayed under the Installed Features section of 20 © Copyright 2009 Lexmark International Inc. The setup executable, once launched, will support Lexmark PrintCryptionTM.
Security Target
Page 3
...PrintCryption, PrintCryption module, cryptographic module, firmware module, or module. More information about the FIPS 140-2 standard and validation program is available on the module from the following sources: • The Lexmark International website (http://www.lexmark.com) contains information on the National Institute of the module...Other supporting documentation as part of the Level 1 FIPS 140-2 validation of Standards and Technology (NIST) Cryptographic Module Validation Program (CMVP) website at http://csrc.nist.gov/cryptval/. Security Requirements for cryptographic modules. ...
...PrintCryption, PrintCryption module, cryptographic module, firmware module, or module. More information about the FIPS 140-2 standard and validation program is available on the module from the following sources: • The Lexmark International website (http://www.lexmark.com) contains information on the National Institute of the module...Other supporting documentation as part of the Level 1 FIPS 140-2 validation of Standards and Technology (NIST) Cryptographic Module Validation Program (CMVP) website at http://csrc.nist.gov/cryptval/. Security Requirements for cryptographic modules. ...
Security Target
Page 7
Install PrintCryptionTM firmware card; This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Power Plug Power Connector FIPS 140-2 Logical Interface Data Input ... © Copyright 2006 Lexmark International Inc. FIPS 140-2 Logical Interfaces Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on host PC Command Result of installation None Page 7 of the roles. Crypto Officer Role The Crypto Officer installs and uninstalls the PrintCryption. Descriptions and responsibilities for...
Install PrintCryptionTM firmware card; This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Power Plug Power Connector FIPS 140-2 Logical Interface Data Input ... © Copyright 2006 Lexmark International Inc. FIPS 140-2 Logical Interfaces Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on host PC Command Result of installation None Page 7 of the roles. Crypto Officer Role The Crypto Officer installs and uninstalls the PrintCryption. Descriptions and responsibilities for...
Security Target
Page 9
The module supports the following FIPS-approved algorithms. • AES ECB, CBC mode decryption - ...358, #359, #360, and #470) (Note: The FIPS approved X9.31 Appendix A.2.4 PRNG utilizes 2 key TDES algorithm). Imported in encrypted form (RSA key transport) 1024 bit RSA public key (80bits of ANSI X9.31 (certificate #100, #101, #102, #103, #... © Copyright 2006 Lexmark International Inc. Operational Environment The operational environment is non-modifiable and thus not applicable for single-user mode by overwriting the flash image. The PrintCryption module runs on the Linux...
The module supports the following FIPS-approved algorithms. • AES ECB, CBC mode decryption - ...358, #359, #360, and #470) (Note: The FIPS approved X9.31 Appendix A.2.4 PRNG utilizes 2 key TDES algorithm). Imported in encrypted form (RSA key transport) 1024 bit RSA public key (80bits of ANSI X9.31 (certificate #100, #101, #102, #103, #... © Copyright 2006 Lexmark International Inc. Operational Environment The operational environment is non-modifiable and thus not applicable for single-user mode by overwriting the flash image. The PrintCryption module runs on the Linux...
Security Target
Page 13
... card is responsible for confirmation of 17 © Copyright 2006 Lexmark International Inc. The setup executable, once launched, will support Lexmark PrintCryptionTM. b. Print a menu settings page. Lexmark provides the Option Added label with the printer. Ask for installing, uninstalling and monitoring the module.... the package, including a damaged seal or package. Upon receiving the PrintCryption card, the Crypto Officer should check for longer than 45 seconds, turn off the printer and reinstall the card. 4. Place the Option Added label on a PC, Crypto Officer ...
... card is responsible for confirmation of 17 © Copyright 2006 Lexmark International Inc. The setup executable, once launched, will support Lexmark PrintCryptionTM. b. Print a menu settings page. Lexmark provides the Option Added label with the printer. Ask for installing, uninstalling and monitoring the module.... the package, including a damaged seal or package. Upon receiving the PrintCryption card, the Crypto Officer should check for longer than 45 seconds, turn off the printer and reinstall the card. 4. Place the Option Added label on a PC, Crypto Officer ...