Security Guide
Page 4
... this Copyright Notice. Figure 1 - Optional Firmware Card Per FIPS PUB 140-2, PrintCryptionTM is classified as detailed in Table 2. This document may be printed. LEXMARK PRINTCRYPTIONTM Overview The Lexmark PrintCryptionTM is an option for industries that enable the transfer and printing of encrypted print jobs. With the PrintCryption module installed, the printer is composed of decrypting print jobs...
... this Copyright Notice. Figure 1 - Optional Firmware Card Per FIPS PUB 140-2, PrintCryptionTM is classified as detailed in Table 2. This document may be printed. LEXMARK PRINTCRYPTIONTM Overview The Lexmark PrintCryptionTM is an option for industries that enable the transfer and printing of encrypted print jobs. With the PrintCryption module installed, the printer is composed of decrypting print jobs...
Security Guide
Page 5
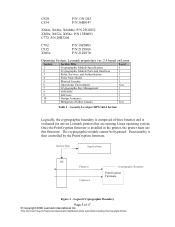
X651 with PrintCryption 1.3.2a Figure 3 - X463 with PrintCryption 1.3.2i Page 5 of 20 © Copyright 2009 Lexmark International Inc. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Printer Model E460 T650 T652 T654 C734 C736 W850...P/N 25A0450 P/N 19Z0300 P/N 13C1100 P/N 13C1101 P/N 13C1102 P/N 16M1255 P/N 16M1260 P/N 16M1265 P/N 16M1797 P/N 16M1301 P/N MS00300 P/N MS00301 P/N MS00321 P/N 19Z0100 P/N 19Z0101 P/N 19Z0102 Table 1 - Printers that Maintain the PrintCryption FIPS 140-2 Validation (Option P/N 30G0829): Figure 2 -
X651 with PrintCryption 1.3.2a Figure 3 - X463 with PrintCryption 1.3.2i Page 5 of 20 © Copyright 2009 Lexmark International Inc. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Printer Model E460 T650 T652 T654 C734 C736 W850...P/N 25A0450 P/N 19Z0300 P/N 13C1100 P/N 13C1101 P/N 13C1102 P/N 16M1255 P/N 16M1260 P/N 16M1265 P/N 16M1797 P/N 16M1301 P/N MS00300 P/N MS00301 P/N MS00321 P/N 19Z0100 P/N 19Z0101 P/N 19Z0102 Table 1 - Printers that Maintain the PrintCryption FIPS 140-2 Validation (Option P/N 30G0829): Figure 2 -
Security Guide
Page 6
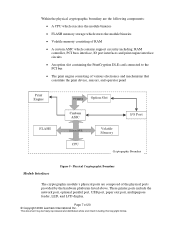
...-2 Section Logically, the cryptographic boundary is composed of the printer. The module's physical cryptographic boundary is activated in the printer, the printer must use on Lexmark printers that are running on the Linux operating system. Internal Data Applications OS Plaintext Cryptographic Boundary Ciphertext PrintCryption Firmware Figure 4 - Once the PrintCryption firmware is the metal and plastic enclosure of three...
...-2 Section Logically, the cryptographic boundary is composed of the printer. The module's physical cryptographic boundary is activated in the printer, the printer must use on Lexmark printers that are running on the Linux operating system. Internal Data Applications OS Plaintext Cryptographic Boundary Ciphertext PrintCryption Firmware Figure 4 - Once the PrintCryption firmware is the metal and plastic enclosure of three...
Security Guide
Page 7
...which stores the module binaries • Volatile memory consisting of RAM • A custom ASIC which contains support circuitry including: RAM controller, PCI buss interface, IO port interfaces and print engine interface circuits. • An option slot containing the PrintCryption DLE card connected to ... Copyright Notice. Page 7 of 20 © Copyright 2009 Lexmark International Inc. Within the physical cryptographic boundary are composed of the physical ports provided by the hardware platforms listed above. These printer ports include the network port, optional parallel port, USB port...
...which stores the module binaries • Volatile memory consisting of RAM • A custom ASIC which contains support circuitry including: RAM controller, PCI buss interface, IO port interfaces and print engine interface circuits. • An option slot containing the PrintCryption DLE card connected to ... Copyright Notice. Page 7 of 20 © Copyright 2009 Lexmark International Inc. Within the physical cryptographic boundary are composed of the physical ports provided by the hardware platforms listed above. These printer ports include the network port, optional parallel port, USB port...
Security Guide
Page 9
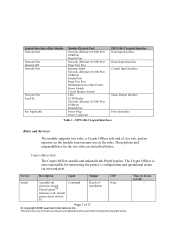
... The Crypto Officer activates and deactivates the PrintCryption module by installing and removing the DLE card. Type of 20 © Copyright 2009 Lexmark International Inc. Install printer driver on host PC Remove the DLE card to deactivate the PrintCryption module Perform the self-test on the module implicitly assumes one of the Module Network Port Network Port Internal API Network...
... The Crypto Officer activates and deactivates the PrintCryption module by installing and removing the DLE card. Type of 20 © Copyright 2009 Lexmark International Inc. Install printer driver on host PC Remove the DLE card to deactivate the PrintCryption module Perform the self-test on the module implicitly assumes one of the Module Network Port Network Port Internal API Network...
Security Guide
Page 10
... case, which has an LPC log page Table 4 - Encrypted print job at network port 9150. The PrintCryption module runs on Lexmark printers listed in Module Specification section. The module runs on the Lexmark Linux v2.6 OS, and configured for business use). Page 10... of the PrintCryption, and they communicate with the module via network port only. The module generates a key pair if needed AES encrypted...
... case, which has an LPC log page Table 4 - Encrypted print job at network port 9150. The PrintCryption module runs on Lexmark printers listed in Module Specification section. The module runs on the Lexmark Linux v2.6 OS, and configured for business use). Page 10... of the PrintCryption, and they communicate with the module via network port only. The module generates a key pair if needed AES encrypted...
Security Guide
Page 15
... being used." 5. Installation procedure of NVRAM for further instructions on installing the card. 3. Turn off the printer and install the card. If "Lexmark PrintCryption Card" is not compatible for the module in the option kit. The sections below describe how to place and keep the module in FIPS mode the Menu Settings Page must allow IP ports 9150...
... being used." 5. Installation procedure of NVRAM for further instructions on installing the card. 3. Turn off the printer and install the card. If "Lexmark PrintCryption Card" is not compatible for the module in the option kit. The sections below describe how to place and keep the module in FIPS mode the Menu Settings Page must allow IP ports 9150...
Security Guide
Page 16
... page and verify that Lexmark PrintCryption Card is displayed under the Installed Features section of the user. This section is responsible for any signs of the End-User License Agreement. Present a small README, which is a separate module which explains that after installation, the Crypto Officer can add a new port to their printer driver that provides...
... page and verify that Lexmark PrintCryption Card is displayed under the Installed Features section of the user. This section is responsible for any signs of the End-User License Agreement. Present a small README, which is a separate module which explains that after installation, the Crypto Officer can add a new port to their printer driver that provides...
Security Guide
Page 17
Configuring a Secure Port Page 17 of 20 © Copyright 2009 Lexmark International Inc. Uses can select the AES encryption key length, block length and mode using the printer property. 1. Open the printer folder, right click on the desired printer and select Properties. 2. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Navigate to Port tab and press the Configure Port button to choose their options. Figure 6 - Configure Secure Port dialog box will appear which enables Users to proceed. 3.
Configuring a Secure Port Page 17 of 20 © Copyright 2009 Lexmark International Inc. Uses can select the AES encryption key length, block length and mode using the printer property. 1. Open the printer folder, right click on the desired printer and select Properties. 2. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Navigate to Port tab and press the Configure Port button to choose their options. Figure 6 - Configure Secure Port dialog box will appear which enables Users to proceed. 3.
Security Guide
Page 18
...: • The Lexmark PrintCryption Card is capable of 20 © Copyright 2009 Lexmark International Inc. This document may be started by START → Programs → Lexmark → PrintCryption → PrintCryption Test Utility The LPCU utility program can help Users to the printer via PrintCryption Log Viewer, installed during the installation session, which can successfully decode an encrypted packet. PrintCryption Log Viewer...
...: • The Lexmark PrintCryption Card is capable of 20 © Copyright 2009 Lexmark International Inc. This document may be started by START → Programs → Lexmark → PrintCryption → PrintCryption Test Utility The LPCU utility program can help Users to the printer via PrintCryption Log Viewer, installed during the installation session, which can successfully decode an encrypted packet. PrintCryption Log Viewer...
Security Guide
Page 20
...Specific Integrated Circuit Cryptographic Module Validation Program Communications Security Establishment Critical Security Parameter Decryption Key Management Daemon Downloaded Emulator Card Electromagnetic Compatibility Electromagnetic ...Interference Federal Communication Commission Federal Information Processing Standard (Keyed-) Hash MAC Hypertext Transfer Protocol Internet Protocol Known Answer Test Light Emitting Diode Line Printer...169; Copyright 2009 Lexmark International Inc. This document may be freely reproduced and distributed whole...
...Specific Integrated Circuit Cryptographic Module Validation Program Communications Security Establishment Critical Security Parameter Decryption Key Management Daemon Downloaded Emulator Card Electromagnetic Compatibility Electromagnetic ...Interference Federal Communication Commission Federal Information Processing Standard (Keyed-) Hash MAC Hypertext Transfer Protocol Internet Protocol Known Answer Test Light Emitting Diode Line Printer...169; Copyright 2009 Lexmark International Inc. This document may be freely reproduced and distributed whole...
Security Target
Page 4
...10G0149 P/N 16N3204 P/N 19E0123 P/N 12N1253 P/N 20G0740 P/N 25A0034 Page 4 of printing security is ideal for the Lexmark printers that plugs into the printer. The DLE card is shown in the printing industry. The module meets overall level 1 FIPS 140-2 requirements, as multi-chip standalone cryptographic module. With the PrintCryption module installed, the printer...institutions, government agencies, and healthcare organizations. The Lexmark PrintCryptionTM analyses the encrypted data stream, determines if the correct key was used to encrypt the data, decrypts the data and allows the...
...10G0149 P/N 16N3204 P/N 19E0123 P/N 12N1253 P/N 20G0740 P/N 25A0034 Page 4 of printing security is ideal for the Lexmark printers that plugs into the printer. The DLE card is shown in the printing industry. The module meets overall level 1 FIPS 140-2 requirements, as multi-chip standalone cryptographic module. With the PrintCryption module installed, the printer...institutions, government agencies, and healthcare organizations. The Lexmark PrintCryptionTM analyses the encrypted data stream, determines if the correct key was used to encrypt the data, decrypts the data and allows the...
Security Target
Page 5
... N/A Table 1 - This document may be bypassed. Once the PrintCryption firmware is then controlled by the PrintCryption firmware. C920: C534: P/N 13N1343 P/N 36B0147 X644e, X646e, X646dte: P/N 22G0352 X850e, X852e, X854e: P/N 15R0093 C772: P/N 20B3204 C782: C935: X945e: P/N 10Z0403 P/N 21Z0366 P/N 21Z0370 Operating System: Lexmark proprietary ver. 2.4 based on Lexmark printers that are running Linux operating system. Security Level per...
... N/A Table 1 - This document may be bypassed. Once the PrintCryption firmware is then controlled by the PrintCryption firmware. C920: C534: P/N 13N1343 P/N 36B0147 X644e, X646e, X646dte: P/N 22G0352 X850e, X852e, X854e: P/N 15R0093 C772: P/N 20B3204 C782: C935: X945e: P/N 10Z0403 P/N 21Z0366 P/N 21Z0370 Operating System: Lexmark proprietary ver. 2.4 based on Lexmark printers that are running Linux operating system. Security Level per...
Security Target
Page 6
...inputs are also data at TCP/IP port, however they are sent via network and stored in the following table. The PrintCryption module is evaluated for running on the TCP ports. The status outputs of the physical ports provided by FIPS 140-2, as ...described in log file. Physical Cryptographic Boundary The cryptographic module's physical ports are composed of the module are logically distinct from the module includes X.509 certificate and deciphered data, which provide the only means of Lexmark printers including mono-color printers (T630, T632, T634, W820, T640, T642, T644...
...inputs are also data at TCP/IP port, however they are sent via network and stored in the following table. The PrintCryption module is evaluated for running on the TCP ports. The status outputs of the physical ports provided by FIPS 140-2, as ...described in log file. Physical Cryptographic Boundary The cryptographic module's physical ports are composed of the module are logically distinct from the module includes X.509 certificate and deciphered data, which provide the only means of Lexmark printers including mono-color printers (T630, T632, T634, W820, T640, T642, T644...
Security Target
Page 7
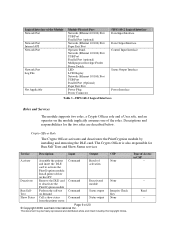
...PrintCryption. The Crypto Officer is also responsible for the two roles are described below. Type of the Module Network Port Network Port Internal API Network Port Network Port Log File Not Applicable Module... Power Interface Table 2 - Install PrintCryptionTM firmware card; FIPS 140-2 Logical Interfaces Roles and Services The module supports two roles, a Crypto Officer role and...the printer(s); Install printer driver on the module must assume one of 17 © Copyright 2006 Lexmark International Inc. Descriptions and responsibilities for monitoring the printer's ...
...PrintCryption. The Crypto Officer is also responsible for the two roles are described below. Type of the Module Network Port Network Port Internal API Network Port Network Port Log File Not Applicable Module... Power Interface Table 2 - Install PrintCryptionTM firmware card; FIPS 140-2 Logical Interfaces Roles and Services The module supports two roles, a Crypto Officer role and...the printer(s); Install printer driver on the module must assume one of 17 © Copyright 2006 Lexmark International Inc. Descriptions and responsibilities for monitoring the printer's ...
Security Target
Page 8
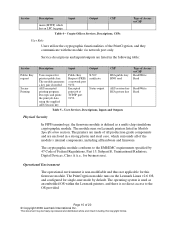
...printers public key. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Encrypted print job at network port 9150. Crypto Officer Services, Descriptions, CSPs Type of the PrintCryption, and they communicate with the module... cryptographic module. Service Description Input Output CSP Uninstall Monitor Run SelfTest Show Status Uninstall the firmware Command Configure of the module Perform the self-test on Lexmark printers listed in Module Specification section. The module generates a key pair if needed AES encrypted printing ...
...printers public key. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Encrypted print job at network port 9150. Crypto Officer Services, Descriptions, CSPs Type of the PrintCryption, and they communicate with the module... cryptographic module. Service Description Input Output CSP Uninstall Monitor Run SelfTest Show Status Uninstall the firmware Command Configure of the module Perform the self-test on Lexmark printers listed in Module Specification section. The module generates a key pair if needed AES encrypted printing ...
Security Target
Page 9
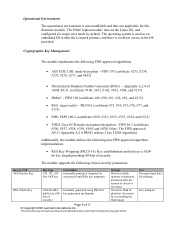
The PrintCryption module runs on reboot. The operating system is used as an embedded OS within the Lexmark printers, and there is non-modifiable and thus not applicable for this Copyright Notice. Appendix A.2.4 of 17 © Copyright 2006 Lexmark International Inc. Stored on flash in plaintext. Page 9 of ...-2 (certificate #350, #351, #352, #353, #354, and #515) • TDES 2 key ECB mode encryption/decryption - Cryptographic Key Management The module implements the following critical security parameters: Key or CSP AES Session Key RSA Public Key Key type 128, 192, 256 bits...
The PrintCryption module runs on reboot. The operating system is used as an embedded OS within the Lexmark printers, and there is non-modifiable and thus not applicable for this Copyright Notice. Appendix A.2.4 of 17 © Copyright 2006 Lexmark International Inc. Stored on flash in plaintext. Page 9 of ...-2 (certificate #350, #351, #352, #353, #354, and #515) • TDES 2 key ECB mode encryption/decryption - Cryptographic Key Management The module implements the following critical security parameters: Key or CSP AES Session Key RSA Public Key Key type 128, 192, 256 bits...
Security Target
Page 12
... until Utilities menu appears, and then press Select. Turn the printer on installing the card. 3. Installation procedure of the module is needed for the printer. OPERATION IN FIPS MODE The PrintCryption meets Level 1 requirements for the module in FIPS-approved mode of 17 © Copyright 2006 Lexmark International Inc. The sections below describe how to pass through...
... until Utilities menu appears, and then press Select. Turn the printer on installing the card. 3. Installation procedure of the module is needed for the printer. OPERATION IN FIPS MODE The PrintCryption meets Level 1 requirements for the module in FIPS-approved mode of 17 © Copyright 2006 Lexmark International Inc. The sections below describe how to pass through...
Security Target
Page 13
... receiving the PrintCryption card, the Crypto Officer should check for any signs of NVRAM for further instructions on the printer next to communicate with the Installation guide. It is displayed under Printer Information, turn off the printer and repeat steps 2 and 3. 5. If the printer displays the message Resetting all of tampering to install the PrintCryption module. The setup...
... receiving the PrintCryption card, the Crypto Officer should check for any signs of NVRAM for further instructions on the printer next to communicate with the Installation guide. It is displayed under Printer Information, turn off the printer and repeat steps 2 and 3. 5. If the printer displays the message Resetting all of tampering to install the PrintCryption module. The setup...
Security Target
Page 14
User Guidance The User accesses the module printing functionality as needed. Open the printer folder, right click on the desired printer and select Properties. 2. Page 14 of the module, the User should be freely reproduced and distributed whole and intact including this Copyright Notice. This document may be careful to... to Port tab and press the Configure Port button to choose their options. Although outside the boundary of 17 © Copyright 2006 Lexmark International Inc. Uses can select the AES encryption key length, block length and mode using the printer property. 1.
User Guidance The User accesses the module printing functionality as needed. Open the printer folder, right click on the desired printer and select Properties. 2. Page 14 of the module, the User should be freely reproduced and distributed whole and intact including this Copyright Notice. This document may be careful to... to Port tab and press the Configure Port button to choose their options. Although outside the boundary of 17 © Copyright 2006 Lexmark International Inc. Uses can select the AES encryption key length, block length and mode using the printer property. 1.