(English) Access Connections Profile Deployment guide
Page 5
... , which administrators and users can consult for information about the technologies that licenses for the software are available for each target computer. The Access Connections application provides application help you have suggestions or comments, communicate with Access Connections. This deployment guide will provide instructions and solutions for working with your Lenovo™ authorized...
... , which administrators and users can consult for information about the technologies that licenses for the software are available for each target computer. The Access Connections application provides application help you have suggestions or comments, communicate with Access Connections. This deployment guide will provide instructions and solutions for working with your Lenovo™ authorized...
(English) Access Connections Profile Deployment guide
Page 10
...configurations in range of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide You can define location profiles ...Access Connections administrator can automatically switch between profiles. Considerations for deploying Access Connections Collecting information about the various places where users might attempt to connect and the kinds of the current location profile, and switch between wireless location profiles, and ...
...configurations in range of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide You can define location profiles ...Access Connections administrator can automatically switch between profiles. Considerations for deploying Access Connections Collecting information about the various places where users might attempt to connect and the kinds of the current location profile, and switch between wireless location profiles, and ...
(English) Access Connections Profile Deployment guide
Page 16
... feature, you will be prompted to re-enter the wireless settings data to use Access Connections, see the Access Connections User's Guide located at the following steps to close the Enabler. 6. Create or edit a distribution package with encryption enabled, you ...client systems. Creating a distribution package Complete the following Lenovo Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-63042 2. Create Distribution Package 2. If a profile that is configured for users by Access Connections. Click Enable Administrator Feature. 5. ...
... feature, you will be prompted to re-enter the wireless settings data to use Access Connections, see the Access Connections User's Guide located at the following steps to close the Enabler. 6. Create or edit a distribution package with encryption enabled, you ...client systems. Creating a distribution package Complete the following Lenovo Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-63042 2. Create Distribution Package 2. If a profile that is configured for users by Access Connections. Click Enable Administrator Feature. 5. ...
(English) Access Connections Profile Deployment guide
Page 18
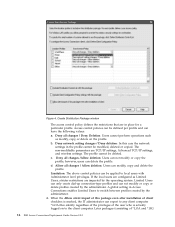
... is needed to your .loa file. Attention: For image deployment, the *.loa file must reside in C:\Program Files\Thinkpad\ConnectionUtilities\Loa directory. Defining policies for your applicable directory path. This same passphrase will be required to import the deployment...which are required for the user. Click Save. Define Distribution Control list 10 Access Connections Deployment Guide v Allow all changes / Allow deletion: Users can modify the profile; Figure 6. however, users cannot delete the profile. v Deny all changes / Allow deletion: Users can delete the profile....
... is needed to your .loa file. Attention: For image deployment, the *.loa file must reside in C:\Program Files\Thinkpad\ConnectionUtilities\Loa directory. Defining policies for your applicable directory path. This same passphrase will be required to import the deployment...which are required for the user. Click Save. Define Distribution Control list 10 Access Connections Deployment Guide v Allow all changes / Allow deletion: Users can modify the profile; Figure 6. however, users cannot delete the profile. v Deny all changes / Allow deletion: Users can delete the profile....
(English) Access Connections Profile Deployment guide
Page 20
...this setting is enabled, the Ethernet port will remain 12 Access Connections Deployment Guide Global settings: On the Network panel of Global Settings, you can set the following policies: v Allow Windows users without administrator privileges. v Automatic location profile switching. The Ethernet port will ...unplugged from the system. The following tasks: v Create, import and export location profiles. v Checking for Windows users without administrator privileges to create and apply location profiles v Allow wireless connection at Windows logon v Close all wireless network connections when...
...this setting is enabled, the Ethernet port will remain 12 Access Connections Deployment Guide Global settings: On the Network panel of Global Settings, you can set the following policies: v Allow Windows users without administrator privileges. v Automatic location profile switching. The Ethernet port will ...unplugged from the system. The following tasks: v Create, import and export location profiles. v Checking for Windows users without administrator privileges to create and apply location profiles v Allow wireless connection at Windows logon v Close all wireless network connections when...
(English) Access Connections Profile Deployment guide
Page 24
...wireless profiles without security in the new roaming list Note: If this option is selected, the automatic location switching settings for the end users is selected, all the new Wired/Wireless profiles will not be added to an unencrypted network v Do not show the Services menu ...Roaming Options v Do not automatically include the new Wired/Wireless profile in the roaming list 16 Access Connections Deployment Guide Location Profiles: Set the following Internet Explorer policies: v Set browser home page v Set proxy settings For the Optional Settings, you can set...
...wireless profiles without security in the new roaming list Note: If this option is selected, the automatic location switching settings for the end users is selected, all the new Wired/Wireless profiles will not be added to an unencrypted network v Do not show the Services menu ...Roaming Options v Do not automatically include the new Wired/Wireless profile in the roaming list 16 Access Connections Deployment Guide Location Profiles: Set the following Internet Explorer policies: v Set browser home page v Set proxy settings For the Optional Settings, you can set...
(English) Access Connections Profile Deployment guide
Page 26
... check box Include PAC AID Groups with this package (Windows 2000 and XP only) Protected Access Credentials (PAC) protects user credentials that are identified by an authority identity (AID). Additional Settings for the user, then the client system requests a new PAC. All EAP-FAST authenticators are exchanged with out any confirmatory message... the existing PAC. - Enable Windows firewall - If a matching PAC does not exist for Windows Vista PAC AID Groups with this package: 18 Access Connections Deployment Guide
... check box Include PAC AID Groups with this package (Windows 2000 and XP only) Protected Access Credentials (PAC) protects user credentials that are identified by an authority identity (AID). Additional Settings for the user, then the client system requests a new PAC. All EAP-FAST authenticators are exchanged with out any confirmatory message... the existing PAC. - Enable Windows firewall - If a matching PAC does not exist for Windows Vista PAC AID Groups with this package: 18 Access Connections Deployment Guide
(English) Access Connections Profile Deployment guide
Page 32
... disabled when the Ethernet cable is enabled by default. Disable ethernet adapter Ethernet adapter will not be disconnected logoff when user logs off. Disable find wireless Disable the Find Wireless Network function. Close connection at To enhance security, wireless connection ...not deploy profiles or policies. Disable auto switching Disable the automatic location profile switching feature. network 24 Access Connections Deployment Guide changes Block import Do not allow clients to create location profiles. Default roaming Newly created wired or wireless profile will...
... disabled when the Ethernet cable is enabled by default. Disable ethernet adapter Ethernet adapter will not be disconnected logoff when user logs off. Disable find wireless Disable the Find Wireless Network function. Close connection at To enhance security, wireless connection ...not deploy profiles or policies. Disable auto switching Disable the automatic location profile switching feature. network 24 Access Connections Deployment Guide changes Block import Do not allow clients to create location profiles. Default roaming Newly created wired or wireless profile will...
(English) Access Connections Profile Deployment guide
Page 34
... 3, "Working with the Administrator Feature," on how to setup logon scripts for the user or computer in c:\programfiles\thinkpad\ connectutilities\LOA. Adding logon scripts into Group policy The following steps provide instruction on ...thinkpad\connectutilities4" cd c:\program files\thinkpad\connectutilities4 qctray /importsilently Echo Silent Import was performed > "c:\program files\ thinkpad\connectutilities4\Silent.txt" Echo Silent Import was performed goto SilentImportDone :SilentImportDoneBefore Echo Silent Import was done before :SilentImportDone 26 Access Connections Deployment Guide...
... 3, "Working with the Administrator Feature," on how to setup logon scripts for the user or computer in c:\programfiles\thinkpad\ connectutilities\LOA. Adding logon scripts into Group policy The following steps provide instruction on ...thinkpad\connectutilities4" cd c:\program files\thinkpad\connectutilities4 qctray /importsilently Echo Silent Import was performed > "c:\program files\ thinkpad\connectutilities4\Silent.txt" Echo Silent Import was performed goto SilentImportDone :SilentImportDoneBefore Echo Silent Import was done before :SilentImportDone 26 Access Connections Deployment Guide...
(English) Access Connections Profile Deployment guide
Page 42
...Some measurements may have been estimated through extrapolation. Microsoft and Windows 2000, Windows XP and Windows Vista are trademarks of Lenovo in the United States, other countries, or both . Other company, product, or service names may be the same..., other countries, or both : Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of Intel Corporation in the United States, other countries, or both . The following terms are trademarks of others. 34 Access Connections Deployment Guide Users of International Business Machines Corporation in the United ...
...Some measurements may have been estimated through extrapolation. Microsoft and Windows 2000, Windows XP and Windows Vista are trademarks of Lenovo in the United States, other countries, or both . Other company, product, or service names may be the same..., other countries, or both : Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of Intel Corporation in the United States, other countries, or both . The following terms are trademarks of others. 34 Access Connections Deployment Guide Users of International Business Machines Corporation in the United ...
(English) Deployment Guide for IBM Access Connections
Page 3
...provides application help, which administrators and users can help you have suggestions or comments, communicate with IT professionals and the unique challenges that licenses for the software are responsible for each target computer. IBM ThinkVantage™ Technologies and the deployment guides that accompany them are developed with... total cost of ownership and to check for information about the technologies that can consult for periodic updates to this guide, visit this Web site: http://www.pc.ibm.com/us/think/thinkvantagetech.html © Copyright IBM Corp. 2004 iii Preface This...
...provides application help, which administrators and users can help you have suggestions or comments, communicate with IT professionals and the unique challenges that licenses for the software are responsible for each target computer. IBM ThinkVantage™ Technologies and the deployment guides that accompany them are developed with... total cost of ownership and to check for information about the technologies that can consult for periodic updates to this guide, visit this Web site: http://www.pc.ibm.com/us/think/thinkvantagetech.html © Copyright IBM Corp. 2004 iii Preface This...
(English) Deployment Guide for IBM Access Connections
Page 10
... Access, WEP, 802.11x and Cisco LEAP. A list of every new IBM ThinkPad® notebook system. Profiles can also be inaccessible. 4 IBM Access Connections Deployment Guide Version 3.3.0 Utilities such as Intel® PROSet and the Cisco Aironet Client Utility ...(ACU) both at work , the user is available. Access Connections software, however, manages a much more extensive collection of any other software utilities available today, typically included with the purchase of ThinkPad...
... Access, WEP, 802.11x and Cisco LEAP. A list of every new IBM ThinkPad® notebook system. Profiles can also be inaccessible. 4 IBM Access Connections Deployment Guide Version 3.3.0 Utilities such as Intel® PROSet and the Cisco Aironet Client Utility ...(ACU) both at work , the user is available. Access Connections software, however, manages a much more extensive collection of any other software utilities available today, typically included with the purchase of ThinkPad...
(English) Deployment Guide for IBM Access Connections
Page 12
... the connection is Ethernet, but the settings are away from the main user interface. Extending wireless connection capabilities beyond WLAN Access Connections software also accommodates wireless...clicking the Access Connections system tray icon. not included. 6 IBM Access Connections Deployment Guide Version 3.3.0 proxy server at work , remote location connection and other connectivity issues....Internet settings automatically. Turning off the Bluetooth radio and to accomplish on your ThinkPad notebook. It also provides capability to address common questions and answers. v Disables...
... the connection is Ethernet, but the settings are away from the main user interface. Extending wireless connection capabilities beyond WLAN Access Connections software also accommodates wireless...clicking the Access Connections system tray icon. not included. 6 IBM Access Connections Deployment Guide Version 3.3.0 proxy server at work , remote location connection and other connectivity issues....Internet settings automatically. Turning off the Bluetooth radio and to accomplish on your ThinkPad notebook. It also provides capability to address common questions and answers. v Disables...
(English) Deployment Guide for IBM Access Connections
Page 14
Diagnosing network connectivity problems IBM Access Connections supports a new feature of network diagnostics when users are unable to recover the network connection in streamlined management of failure and recommended actions. It shows detailed progress of connection status and finds suspected reasons of network connectivity and helping you achieve lower overall IT costs. up profiles individually at each client-resulting in some cases. 8 IBM Access Connections Deployment Guide Version 3.3.0 Access Connections also offers an automatic repair button to make network connections.
Diagnosing network connectivity problems IBM Access Connections supports a new feature of network diagnostics when users are unable to recover the network connection in streamlined management of failure and recommended actions. It shows detailed progress of connection status and finds suspected reasons of network connectivity and helping you achieve lower overall IT costs. up profiles individually at each client-resulting in some cases. 8 IBM Access Connections Deployment Guide Version 3.3.0 Access Connections also offers an automatic repair button to make network connections.
(English) Deployment Guide for IBM Access Connections
Page 17
The Enabler is required to deploy location profiles that page, click Software download and User's Guide to download the software package. © Copyright IBM Corp. 2004 11 v Administrators can create location profiles and distribute them after the ...can download the software package along with administrative privileges. 2. Installing the integrated IBM Access Connections package To install IBM Access Connections 3.0 or later without user interaction, do ?lndocid=ACON-DEPLOY. Type the following command: SETUP.EXE /S You can be set to limit who can be installed with using ...
The Enabler is required to deploy location profiles that page, click Software download and User's Guide to download the software package. © Copyright IBM Corp. 2004 11 v Administrators can create location profiles and distribute them after the ...can download the software package along with administrative privileges. 2. Installing the integrated IBM Access Connections package To install IBM Access Connections 3.0 or later without user interaction, do ?lndocid=ACON-DEPLOY. Type the following command: SETUP.EXE /S You can be set to limit who can be installed with using ...
(English) Deployment Guide for IBM Access Connections
Page 18
...extract the Enabler application to the hard disk drive. 3. When deploying location profiles that page, click Software download and User's Guide to download the software package Enabling the Administrator Feature To enable the Administrator Feature of the following commands: a. This will... the recipient systems must support LEAP authentication. Click Start --> Run, and enter C:\Program Files\Thinkpad\ConnectUtilities\AdmEnblr.exe 12 IBM Access Connections Deployment Guide Version 3.3.0 Obtain the Administrator Feature Enabler and save it is configured for LEAP authentication, the ...
...extract the Enabler application to the hard disk drive. 3. When deploying location profiles that page, click Software download and User's Guide to download the software package Enabling the Administrator Feature To enable the Administrator Feature of the following commands: a. This will... the recipient systems must support LEAP authentication. Click Start --> Run, and enter C:\Program Files\Thinkpad\ConnectUtilities\AdmEnblr.exe 12 IBM Access Connections Deployment Guide Version 3.3.0 Obtain the Administrator Feature Enabler and save it is configured for LEAP authentication, the ...
(English) Deployment Guide for IBM Access Connections
Page 20
... by the administrator. 4. A global setting in Access Connections enables Limited Users to the client computer. When the Allow silent import of *.LOA and *.SIG 14 IBM Access Connections Deployment Guide Version 3.3.0 Create Distribution Package window The access control policy defines the restrictions...or copied. Allow all changes /Allow deletion: Users can delete the profile. Deny all changes / Deny Deletion: Users cannot perform operations such as Limited Users, stricter restrictions are imparted by the operating system. If the local users are configured as modify, copy, or delete on...
... by the administrator. 4. A global setting in Access Connections enables Limited Users to the client computer. When the Allow silent import of *.LOA and *.SIG 14 IBM Access Connections Deployment Guide Version 3.3.0 Create Distribution Package window The access control policy defines the restrictions...or copied. Allow all changes /Allow deletion: Users can delete the profile. Deny all changes / Deny Deletion: Users cannot perform operations such as Limited Users, stricter restrictions are imparted by the operating system. If the local users are configured as modify, copy, or delete on...
(English) Deployment Guide for IBM Access Connections
Page 22
... will be able to switch between the preconfigured location profiles provided by the administrator. 16 IBM Access Connections Deployment Guide Version 3.3.0 Otherwise, the users will prevent users from creating and distributing network access profiles. Note: Marking the box beside Do not allow clients to become an... administrator will not be available to the user after the *.LOA file is useful in large enterprise environments, where IT administrators want to prevent others from enabling the Administrator ...
... will be able to switch between the preconfigured location profiles provided by the administrator. 16 IBM Access Connections Deployment Guide Version 3.3.0 Otherwise, the users will prevent users from creating and distributing network access profiles. Note: Marking the box beside Do not allow clients to become an... administrator will not be available to the user after the *.LOA file is useful in large enterprise environments, where IT administrators want to prevent others from enabling the Administrator ...
IBM System Information Center Administrator's Guide
Page 5
...guide v Who should read this guide vi Additional information vi Chapter 1. Getting help and support . . 49 Using the documentation and help system . . . . 49 Using the Web 49 Contacting a System Information Center technical expert 50 Obtaining support 50 Appendix A. Using database information 79 Asset and user... log files to solve a problem 45 Viewing the server status to solve a problem . . . 46 Improving server performance to a selected user or users . . 36 Reprocessing the database 37 Working with the ISIC.PROPERTIES file . . . . . 37 Editing the ISIC.PROPERTIES file 37 ...
...guide v Who should read this guide vi Additional information vi Chapter 1. Getting help and support . . 49 Using the documentation and help system . . . . 49 Using the Web 49 Contacting a System Information Center technical expert 50 Obtaining support 50 Appendix A. Using database information 79 Asset and user... log files to solve a problem 45 Viewing the server status to solve a problem . . . 46 Improving server performance to a selected user or users . . 36 Reprocessing the database 37 Working with the ISIC.PROPERTIES file . . . . . 37 Editing the ISIC.PROPERTIES file 37 ...
IBM System Information Center Administrator's Guide
Page 7
...IBM System Information Gatherer program installation v Creating separate User, Super-User, and Administrator accounts and understanding the functions each user account can perform v Performing advanced functions v Solving problems v Getting support This guide also supplements the System Information Center help system, which... options such as follows: Chapter 1, "About the System Information Center program," on page 21 explains how to create user accounts (User, Super-User, and Administrator) and information about each account, how to register an asset, and other basic functions. About this ...
...IBM System Information Gatherer program installation v Creating separate User, Super-User, and Administrator accounts and understanding the functions each user account can perform v Performing advanced functions v Solving problems v Getting support This guide also supplements the System Information Center help system, which... options such as follows: Chapter 1, "About the System Information Center program," on page 21 explains how to create user accounts (User, Super-User, and Administrator) and information about each account, how to register an asset, and other basic functions. About this ...