ThinkPad R40 Ethernet Controller - Lenovo
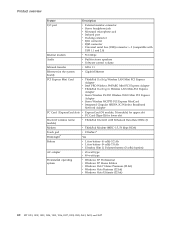
ThinkPad R40 Ethernet Controller

View Results Below
Free Lenovo ThinkPad R40 manuals!
Problems with Lenovo ThinkPad R40?
Ask a Question
Free Lenovo ThinkPad R40 manuals!
Problems with Lenovo ThinkPad R40?
Ask a Question
Related Manual Pages
Similar Questions
Driver Ethernet Para Windows 10 Pro
actualice el equipo a win 10 pro y no consigo el driver de red ethernet
actualice el equipo a win 10 pro y no consigo el driver de red ethernet
(Posted by a1sandro 2 years ago)
Smartfan Control
i just purchased a G580 ,not sure how to control the smartfan noise control,will you please help
i just purchased a G580 ,not sure how to control the smartfan noise control,will you please help
(Posted by Anonymous-131713 10 years ago)
Problem With The Wireless Connection.
I have bought a new lenovo g580 machine.Installed windows 7 Sp1.Using the enclosed Cd installed al...
I have bought a new lenovo g580 machine.Installed windows 7 Sp1.Using the enclosed Cd installed al...
(Posted by bubu48 11 years ago)