magicolor 8650 Security Operations User Manual
Page 10
... files left in the data space used . - Image files stored in the queue - Temporary data files generated during print image file processing This machine offers specific functions as image files - Security 1 1.3 Data to be Protected The underlying concept of this machine toward security is "to protect data that can be discarded...
... files left in the data space used . - Image files stored in the queue - Temporary data files generated during print image file processing This machine offers specific functions as image files - Security 1 1.3 Data to be Protected The underlying concept of this machine toward security is "to protect data that can be discarded...
magicolor 8650 Security Operations User Manual
Page 25
... does not meet the requirements of Admin. If the password set for a particular box before this case, the Administrator must first newly set a password that specific box was changed back from [Not Installed] to [Installed], be sure first to make the settings for the types of Password Rules, see "Password Rules...
... does not meet the requirements of Admin. If the password set for a particular box before this case, the Administrator must first newly set a password that specific box was changed back from [Not Installed] to [Installed], be sure first to make the settings for the types of Password Rules, see "Password Rules...
magicolor 8650 Security Operations User Manual
Page 34
... Operations 2 4 Click the [User Box Setting]. ? What steps should be used when entering the User Box Password? % If [Public] is set for confirming whether the specific User Box can definitely be performed to delete a User Box? % To delete a User Box, click [Delete User Box]. Perform steps 4 through 6 once again. To change...
... Operations 2 4 Click the [User Box Setting]. ? What steps should be used when entering the User Box Password? % If [Public] is set for confirming whether the specific User Box can definitely be performed to delete a User Box? % To delete a User Box, click [Delete User Box]. Perform steps 4 through 6 once again. To change...
magicolor 8650 Security Operations User Manual
Page 77
... Box? % To delete a User Box, click [Delete User Box]. To change a User Box Password, select the "User Box Password is set for confirming whether the specific User Box can be changed ." For details of Password Rules, see "Password Rules" on page 1-8. % Enter the same User Box Password as that meets the...
... Box? % To delete a User Box, click [Delete User Box]. To change a User Box Password, select the "User Box Password is set for confirming whether the specific User Box can be changed ." For details of Password Rules, see "Password Rules" on page 1-8. % Enter the same User Box Password as that meets the...
magicolor 8650 Safety Information Guide
Page 2
... shock or blindness. • Do not modify the printer, as a fire, electrical shock, or breakdown could result in this manual may not apply to your specific printer. ■ Warning and Caution Symbols Both this manual and the printer use this could result in a fire or malfunction. • Do not use a multiple...
... shock or blindness. • Do not modify the printer, as a fire, electrical shock, or breakdown could result in this manual may not apply to your specific printer. ■ Warning and Caution Symbols Both this manual and the printer use this could result in a fire or malfunction. • Do not use a multiple...
HDD Backup Utility User Guide
Page 5
This library is free for commercial and non-commercial use as long as such any Windows specific code (or a derivative thereof) from the library being used in documentation (online or textual) provided with the distribution. 3. Copyright remains Eric Young's, and as the ...
This library is free for commercial and non-commercial use as long as such any Windows specific code (or a derivative thereof) from the library being used in documentation (online or textual) provided with the distribution. 3. Copyright remains Eric Young's, and as the ...
Log Management Utility User Guide
Page 6
... you must reproduce the above copyright no- not just the SSL code. All advertising materials mentioning features or use as long as such any Windows specific code (or a derivative thereof) from the library being used in binary form must include an acknowledgement: "This product includes software written by Eric Young (eay...
... you must reproduce the above copyright no- not just the SSL code. All advertising materials mentioning features or use as long as such any Windows specific code (or a derivative thereof) from the library being used in binary form must include an acknowledgement: "This product includes software written by Eric Young (eay...
Device Set Up User Guide
Page 6
... the Readme file for this software. - Unused hard drive capacity 100 MB or more - Getting Started 1 1 Getting Started 1.1 System Requirements Systems must have the following specifications in application. Memory (RAM) According to use this software is pre-installed on . Network TCP/IP protocol - Applications Microsoft Internet Explorer 6.0 (SP1) or later Microsoft... and so on Windows 7. - color or better - Supported Devices For details of the copier and the printer (supported device of the plug-in application) of KONICA MINOLTA, see the Readme of your operating system. -
... the Readme file for this software. - Unused hard drive capacity 100 MB or more - Getting Started 1 1 Getting Started 1.1 System Requirements Systems must have the following specifications in application. Memory (RAM) According to use this software is pre-installed on . Network TCP/IP protocol - Applications Microsoft Internet Explorer 6.0 (SP1) or later Microsoft... and so on Windows 7. - color or better - Supported Devices For details of the copier and the printer (supported device of the plug-in application) of KONICA MINOLTA, see the Readme of your operating system. -
Device Set Up User Guide
Page 39
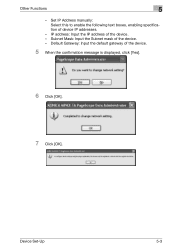
Set IP Address manually: Select this to enable the following text boxes, enabling specification of the device. - Subnet Mask: Input the Subnet mask of device IP addresses. - Other Functions 5 - Default Gateway: Input the default gateway of the device. - IP address: Input the IP address of the device. 5 When the confirmation message is displayed, click [Yes]. 6 Click [OK]. 7 Click [OK]. Device Set-Up 5-3
Set IP Address manually: Select this to enable the following text boxes, enabling specification of the device. - Subnet Mask: Input the Subnet mask of device IP addresses. - Other Functions 5 - Default Gateway: Input the default gateway of the device. - IP address: Input the IP address of the device. 5 When the confirmation message is displayed, click [Yes]. 6 Click [OK]. 7 Click [OK]. Device Set-Up 5-3
User Guide
Page 7
......6-22 Parameter details for the OS 9 printer driver 6-24 Page Attributes ...6-24 Setting Custom Page Sizes ...6-24 General ...6-25 Layout (Pages per sheet) ...6-26 Printer specific options (Finishing Options 1 to 5 6-26 7 Function detail description 7.1 7.1.1 7.1.2 7.2 7.2.1 Proof print...7-2 Setting up the printer driver...7-2 For Windows...7-2 For Mac OS X ...7-3 Recalling a job from the control...
......6-22 Parameter details for the OS 9 printer driver 6-24 Page Attributes ...6-24 Setting Custom Page Sizes ...6-24 General ...6-25 Layout (Pages per sheet) ...6-26 Printer specific options (Finishing Options 1 to 5 6-26 7 Function detail description 7.1 7.1.1 7.1.2 7.2 7.2.1 Proof print...7-2 Setting up the printer driver...7-2 For Windows...7-2 For Mac OS X ...7-3 Recalling a job from the control...
User Guide
Page 13
... Cleaning...12-2 Housing...12-2 Control panel ...12-2 Electrostatic charger wire ...12-3 Print head ...12-3 When the message "Time for periodic device check." appears 12-5 13 Specifications 13.1 13.1.1 13.1.2 13.1.3 13.1.4 13.1.5 13.1.6 13.1.7 13.1.8 13.1.9 13.1.10 13.1.11 13.1.12 13.2 13.2.1 13... FS-519 11-23 11.5.2 To empty the punch scrap box in the finisher FS-609 11-24 12 Care of the cover ...14-20 Specifications...14-21 Troubleshooting...14-22 15 Authentication unit (IC card type AU-201) 15.1 Safety information ...15-2 15.1.1 Important information ...15-2 8650 x-12 RADIO ...
... Cleaning...12-2 Housing...12-2 Control panel ...12-2 Electrostatic charger wire ...12-3 Print head ...12-3 When the message "Time for periodic device check." appears 12-5 13 Specifications 13.1 13.1.1 13.1.2 13.1.3 13.1.4 13.1.5 13.1.6 13.1.7 13.1.8 13.1.9 13.1.10 13.1.11 13.1.12 13.2 13.2.1 13... FS-519 11-23 11.5.2 To empty the punch scrap box in the finisher FS-609 11-24 12 Care of the cover ...14-20 Specifications...14-21 Troubleshooting...14-22 15 Authentication unit (IC card type AU-201) 15.1 Safety information ...15-2 15.1.1 Important information ...15-2 8650 x-12 RADIO ...
User Guide
Page 14
...-6 Registering users ...15-9 Install version checking ...15-9 Setup ...15-10 Registering users ...15-14 Care of authentication unit (IC card type) AU-201 15-19 Specifications...15-20 Troubleshooting...15-21 16 Installing options 16.1 16.2 16.3 16.3.1 16.3.2 16.4 16.4.1 16.4.2 Introduction ...16-2 Installing the mount kit MK-713 ...16...
...-6 Registering users ...15-9 Install version checking ...15-9 Setup ...15-10 Registering users ...15-14 Care of authentication unit (IC card type) AU-201 15-19 Specifications...15-20 Troubleshooting...15-21 16 Installing options 16.1 16.2 16.3 16.3.1 16.3.2 16.4 16.4.1 16.4.2 Introduction ...16-2 Installing the mount kit MK-713 ...16...
User Guide
Page 16
..., PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; If this package is free for use in the form of any Windows specific code (or a derivative thereof) from the library being used . Redistribution and use in source and binary forms, with or without modification, are permitted provided that...
..., PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; If this package is free for use in the form of any Windows specific code (or a derivative thereof) from the library being used . Redistribution and use in source and binary forms, with or without modification, are permitted provided that...
User Guide
Page 17
...code cannot be used in supporting documentation, and that the above copyright notice, this list of its documentation for any purpose and without specific written permission. LOSS OF USE, DATA, OR PROFITS;OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN ... the Networks Associates Technology, Inc nor the names of conditions and the following disclaimer in source and binary forms, with or without specific prior written permission. THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, ...
...code cannot be used in supporting documentation, and that the above copyright notice, this list of its documentation for any purpose and without specific written permission. LOSS OF USE, DATA, OR PROFITS;OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN ... the Networks Associates Technology, Inc nor the names of conditions and the following disclaimer in source and binary forms, with or without specific prior written permission. THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, ...
User Guide
Page 18
... notice, this software without modification, are permitted provided that the following disclaimer in source and binary forms, with or without specific prior written permission. Sun, Sun Microsystems, the Sun logo and Solaris are met: - - Redistributions of source code must...- and other materials provided with the distribution. - in binary form must retain the above copyright notice, this software without specific prior written permission. nor the names of its contributors may include materials developed by third parties. Redistributions in the U.S. LOSS ...
... notice, this software without modification, are permitted provided that the following disclaimer in source and binary forms, with or without specific prior written permission. Sun, Sun Microsystems, the Sun logo and Solaris are met: - - Redistributions of source code must...- and other materials provided with the distribution. - in binary form must retain the above copyright notice, this software without specific prior written permission. nor the names of its contributors may include materials developed by third parties. Redistributions in the U.S. LOSS ...
User Guide
Page 19
...name of Cisco, Inc, Beijing University of Posts and Telecommunications, nor the names of any purpose and without fee is " without specific prior written permission. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY... x-18 WITHIN THAT CONSTRAINT, permission to convey information (although in advertising or publicity pertaining to distribution of the software without specific, written prior permission. Export of this software and its documentation for -profit manner. not be used in doing so, ...
...name of Cisco, Inc, Beijing University of Posts and Telecommunications, nor the names of any purpose and without fee is " without specific prior written permission. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY... x-18 WITHIN THAT CONSTRAINT, permission to convey information (although in advertising or publicity pertaining to distribution of the software without specific, written prior permission. Export of this software and its documentation for -profit manner. not be used in doing so, ...
User Guide
Page 20
... its contributors may be used to , correctness and fitness for purpose. distributions in source and binary forms, with or without specific, written prior permission. Zero-Knowledge Systems, Inc. Redistribution and use of this software in both that copyright notice and this ... Gladman , Worcester, UK. The implementation of the AES encryption algorithm in respect of any purpose is allowed (with or without specific prior written permission. distributions of this source code include the above copyright notice, this list of conditions and the following disclaimer in...
... its contributors may be used to , correctness and fitness for purpose. distributions in source and binary forms, with or without specific, written prior permission. Zero-Knowledge Systems, Inc. Redistribution and use of this software in both that copyright notice and this ... Gladman , Worcester, UK. The implementation of the AES encryption algorithm in respect of any purpose is allowed (with or without specific prior written permission. distributions of this source code include the above copyright notice, this list of conditions and the following disclaimer in...
User Guide
Page 21
...specific, written prior authorization. Information included in the hope that it , with or without even the implied warranty of this notice is subject to the use , copy, create derivative works and redistribute this software and such derivative works for any advertising or publicity pertaining to change without permission. - KONICA MINOLTA... or FITNESS FOR A PARTICULAR PURPOSE. maintains the copyright of this printing system or User's Guide. - KONICA MINOLTA BUSINESS TECHNOLOGIES, INC. The pkcs11.h file included in full without notice. - THE REGENTS OF THE UNIVERSITY...
...specific, written prior authorization. Information included in the hope that it , with or without even the implied warranty of this notice is subject to the use , copy, create derivative works and redistribute this software and such derivative works for any advertising or publicity pertaining to change without permission. - KONICA MINOLTA... or FITNESS FOR A PARTICULAR PURPOSE. maintains the copyright of this printing system or User's Guide. - KONICA MINOLTA BUSINESS TECHNOLOGIES, INC. The pkcs11.h file included in full without notice. - THE REGENTS OF THE UNIVERSITY...
User Guide
Page 27
IF YOU DO NOT AGREE TO BE BOUND BY ALL OF THESE TERMS, YOU MAY NOT USE THE PROFILE. 1. All rights not specifically granted in this License Agreement. 2. c. License Method and Restrictions a. You may not make or distribute copies, fix, alter, merge, modify, adapt, sublicense, transfer, sell, rent, ...
IF YOU DO NOT AGREE TO BE BOUND BY ALL OF THESE TERMS, YOU MAY NOT USE THE PROFILE. 1. All rights not specifically granted in this License Agreement. 2. c. License Method and Restrictions a. You may not make or distribute copies, fix, alter, merge, modify, adapt, sublicense, transfer, sell, rent, ...
User Guide
Page 35
... quality of paper. Referred to as the "HDD" throughout the manual. *1 Parts marked with computer printing) and feed them into the appropriate tray assigned to a specific individual or group. Part name Description 3 Authentication unit (IC card Performs user authentication by reading the information registered on the floor. Referred to the mount...
... quality of paper. Referred to as the "HDD" throughout the manual. *1 Parts marked with computer printing) and feed them into the appropriate tray assigned to a specific individual or group. Part name Description 3 Authentication unit (IC card Performs user authentication by reading the information registered on the floor. Referred to the mount...