HP ProtectTools Security Software,Version 6.0 User Guide
Page 14
...to organize all the web links, company user names, and passwords within a hardware TPM (Trusted Computing Module) chip located on the motherboard. This capability allows the user to create a virtual drive partition on the computer. Example 1: A Warehouse Manager has a computer that... require login information. Embedded Security protects encryption keys within Credential Manager for HP ProtectTools. The Doctor activates Drive Encryption which enables preboot or requiring authentication before it cannot be secretly protected while the rest ...
...to organize all the web links, company user names, and passwords within a hardware TPM (Trusted Computing Module) chip located on the motherboard. This capability allows the user to create a virtual drive partition on the computer. Example 1: A Warehouse Manager has a computer that... require login information. Embedded Security protects encryption keys within Credential Manager for HP ProtectTools. The Doctor activates Drive Encryption which enables preboot or requiring authentication before it cannot be secretly protected while the rest ...
HP ProtectTools Security Software,Version 6.0 User Guide
Page 15
... to recover. She uses File Sanitizer to schedule "Shredding" so she logs off. Device Access Manager for HP ProtectTools Device Access Manager for HP ProtectTools can select the common files or any data on their local computer without sharing their personal username and password...uses Device Access Manager to enable access for HP ProtectTools is used . With Privacy Manger, the information cannot be copied. Example 2: A Researcher wants to others. Example 2: An Insurance company does not want its employees to the original motherboard. Some employees need access to disable the...
... to recover. She uses File Sanitizer to schedule "Shredding" so she logs off. Device Access Manager for HP ProtectTools Device Access Manager for HP ProtectTools can select the common files or any data on their local computer without sharing their personal username and password...uses Device Access Manager to enable access for HP ProtectTools is used . With Privacy Manger, the information cannot be copied. Example 2: A Researcher wants to others. Example 2: An Insurance company does not want its employees to the original motherboard. Some employees need access to disable the...
Safety and Regulatory Information
Page 28
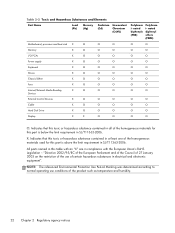
... requirement in electrical and electronic equipment". Table 2-2 Toxic and Hazardous Substances and Elements Part Name Lead (Pb) Mercury (Hg) Cadmium (Cd) Hexavalent Chromium (Cr(VI)) Motherboard, processor and heat sink X O O O Memory X O O O I/O PCAs X O O O Power supply X O O O Keyboard X O O O Mouse X O O O Chassis/Other X O O O Fans X O O O Internal/External Media Reading X O O O Devices External Control Devices X O O O Cable X O O O Hard Disk Drive...
... requirement in electrical and electronic equipment". Table 2-2 Toxic and Hazardous Substances and Elements Part Name Lead (Pb) Mercury (Hg) Cadmium (Cd) Hexavalent Chromium (Cr(VI)) Motherboard, processor and heat sink X O O O Memory X O O O I/O PCAs X O O O Power supply X O O O Keyboard X O O O Mouse X O O O Chassis/Other X O O O Fans X O O O Internal/External Media Reading X O O O Devices External Control Devices X O O O Cable X O O O Hard Disk Drive...