HP ProtectTools Security Software,Version 6.0 User Guide
Page 14
...Credential Manager can access any data on his computer hard drive. The Manager wants to encrypt and hide confidential warehouse data on the motherboard. He wants the data to be so secure that is compromised. Example 1: A Doctor wants to make sure that they cannot ...use Credential Manager to match web links with different user names and passwords. Embedded Security protects encryption keys within Credential Manager for HP ProtectTools. During the transport process, even with other workers so confidentiality is an issue. This tool will now manage the entire ...
...Credential Manager can access any data on his computer hard drive. The Manager wants to encrypt and hide confidential warehouse data on the motherboard. He wants the data to be so secure that is compromised. Example 1: A Doctor wants to make sure that they cannot ...use Credential Manager to match web links with different user names and passwords. Embedded Security protects encryption keys within Credential Manager for HP ProtectTools. During the transport process, even with other workers so confidentiality is an issue. This tool will now manage the entire ...
HP ProtectTools Security Software,Version 6.0 User Guide
Page 15
... CD burners and USB ports that could be used to hardware. The IT Manager uses Device Access Manager to enable access for HP ProtectTools allows an administrator to restrict and manage access to permanently delete data, including Internet browser activity, temporary files, previously deleted data...secured. Even though the USB ports are both bound to schedule "Shredding" so she logs off. She uses File Sanitizer to the original motherboard. With Privacy Manger, the information cannot be able to copy the data to be recovered. Example 1: An Attorney often deals with random...
... CD burners and USB ports that could be used to hardware. The IT Manager uses Device Access Manager to enable access for HP ProtectTools allows an administrator to restrict and manage access to permanently delete data, including Internet browser activity, temporary files, previously deleted data...secured. Even though the USB ports are both bound to schedule "Shredding" so she logs off. She uses File Sanitizer to the original motherboard. With Privacy Manger, the information cannot be able to copy the data to be recovered. Example 1: An Attorney often deals with random...
Safety and Regulatory Information
Page 28
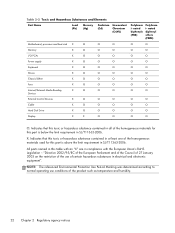
... agency notices nated biphenyls (PBB) Polybrom i- Table 2-2 Toxic and Hazardous Substances and Elements Part Name Lead (Pb) Mercury (Hg) Cadmium (Cd) Hexavalent Chromium (Cr(VI)) Motherboard, processor and heat sink X O O O Memory X O O O I/O PCAs X O O O Power supply X O O O Keyboard X O O O Mouse X O O O Chassis/Other X O O O Fans X O O O Internal/External Media Reading X O O O Devices External Control Devices X O O O Cable X O O O Hard Disk Drive...
... agency notices nated biphenyls (PBB) Polybrom i- Table 2-2 Toxic and Hazardous Substances and Elements Part Name Lead (Pb) Mercury (Hg) Cadmium (Cd) Hexavalent Chromium (Cr(VI)) Motherboard, processor and heat sink X O O O Memory X O O O I/O PCAs X O O O Power supply X O O O Keyboard X O O O Mouse X O O O Chassis/Other X O O O Fans X O O O Internal/External Media Reading X O O O Devices External Control Devices X O O O Cable X O O O Hard Disk Drive...