Datasheet
Page 1
... signatures, and URL databases current. Powerful VPN Performance NetDefend UTM Firewalls offer an integrated VPN Client and Server allowing remote offices or trusted partner to securely connect to access company data and e-mail. DFL-260E/860E/1660/2560/2560G NetDefend UTM Firewall Series... Features Integrated Firewall/VPN • Powerful Firewall Engine • Virtual Private Network (VPN) Security • Granular Bandwidth Management • 802.1Q VLAN Tagging and Port-based VLAN • D-Link End-to-End ...
... signatures, and URL databases current. Powerful VPN Performance NetDefend UTM Firewalls offer an integrated VPN Client and Server allowing remote offices or trusted partner to securely connect to access company data and e-mail. DFL-260E/860E/1660/2560/2560G NetDefend UTM Firewall Series... Features Integrated Firewall/VPN • Powerful Firewall Engine • Virtual Private Network (VPN) Security • Granular Bandwidth Management • 802.1Q VLAN Tagging and Port-based VLAN • D-Link End-to-End ...
Datasheet
Page 2
...technology which eliminates the need to -date. DFL-260E/860E/1660/2560/2560G NetDefend UTM Firewall Series • Automated Key Management via the D-Link Auto-Signature Sensor System without overloading existing ...Link offers optional UTM Service subscriptions which include updates for Traffic Load Sharing6 Enhanced Network Services • DHCP Server/Client/Relay • IGMP V3 • H.323 NAT Traversal • Robust Application Security ALGs • OSPF Dynamic Routing Protocol9 • Run-Time Web-Based Authentication DFL-260E • Firewall Throughput: 150 Mbps • VPN...
...technology which eliminates the need to -date. DFL-260E/860E/1660/2560/2560G NetDefend UTM Firewall Series • Automated Key Management via the D-Link Auto-Signature Sensor System without overloading existing ...Link offers optional UTM Service subscriptions which include updates for Traffic Load Sharing6 Enhanced Network Services • DHCP Server/Client/Relay • IGMP V3 • H.323 NAT Traversal • Robust Application Security ALGs • OSPF Dynamic Routing Protocol9 • Run-Time Web-Based Authentication DFL-260E • Firewall Throughput: 150 Mbps • VPN...
Datasheet
Page 3
...D-Link xStack switches, automatically quarantines infected workstations and prevents them from D-Link. Professional Intrusion Prevention System (IPS) Automatic updates from a comprehensive IPS signature database focus on attack payloads to greater efficiency, and provide a reduced cost of VPN ... zero-day attacks. D-Link Green certified devices comply with millions of specific hazardous materials during manufacturing, while WEEE implements standards for licensing. Secure Network Implementation Using NetDefend™ UTM Firewalls The DFL-260E and DFL-860E save energy automatically ...
...D-Link xStack switches, automatically quarantines infected workstations and prevents them from D-Link. Professional Intrusion Prevention System (IPS) Automatic updates from a comprehensive IPS signature database focus on attack payloads to greater efficiency, and provide a reduced cost of VPN ... zero-day attacks. D-Link Green certified devices comply with millions of specific hazardous materials during manufacturing, while WEEE implements standards for licensing. Secure Network Implementation Using NetDefend™ UTM Firewalls The DFL-260E and DFL-860E save energy automatically ...
Datasheet
Page 4
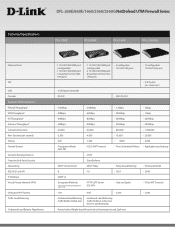
.../2560/2560G NetDefend UTM Firewall Series Technical Specifications DFL-260E DFL-860E DFL-1660 DFL-2560(G) Ethernet Ports SFP USB Console System Performance1 Firewall Throughput2 VPN Throughput3 IPS Throughput4 Antivirus Throughput4 Concurrent Sessions New Sessions (per second) Policies Firewall System Dynamic Routing Protocol Proactive End-Point Security Networking IEEE 802.1q ...
.../2560/2560G NetDefend UTM Firewall Series Technical Specifications DFL-260E DFL-860E DFL-1660 DFL-2560(G) Ethernet Ports SFP USB Console System Performance1 Firewall Throughput2 VPN Throughput3 IPS Throughput4 Antivirus Throughput4 Concurrent Sessions New Sessions (per second) Policies Firewall System Dynamic Routing Protocol Proactive End-Point Security Networking IEEE 802.1q ...
Datasheet
Page 5
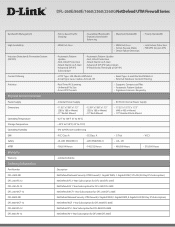
...DFL-860E-NB DFL-860-WCF-12 DFL-860-IPS-12 DFL-860-AV-12 • Policy-Based Traffic Shaping • Guaranteed Bandwidth • Dynamic Bandwidth Balancing • Maximum Bandwidth • Priority Bandwidth • WAN Fail-Over • WAN Fail-Over • Active-Passive Mode • Device Failure Detection • Link Failure Detection • FW/VPN...IPS Subscription) NetDefend IPS 1-Year Subscription for DFL-260/DFL-260E NetDefend AV 1-Year Subscription for DFL-260/DFL-260E NetDefend WCF 1-Year Subscription for DFL-260/DFL-260E NetDefend Network Security UTM Firewall, 2 Gigabit...
...DFL-860E-NB DFL-860-WCF-12 DFL-860-IPS-12 DFL-860-AV-12 • Policy-Based Traffic Shaping • Guaranteed Bandwidth • Dynamic Bandwidth Balancing • Maximum Bandwidth • Priority Bandwidth • WAN Fail-Over • WAN Fail-Over • Active-Passive Mode • Device Failure Detection • Link Failure Detection • FW/VPN...IPS Subscription) NetDefend IPS 1-Year Subscription for DFL-260/DFL-260E NetDefend AV 1-Year Subscription for DFL-260/DFL-260E NetDefend WCF 1-Year Subscription for DFL-260/DFL-260E NetDefend Network Security UTM Firewall, 2 Gigabit...
Datasheet
Page 6
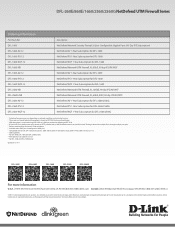
...Year Subscription for DFL-2560/2560G NetDefend WCF 1-Year Subscription for DFL-2560/2560G 1 Actual performance may vary depending on network conditions and activated services. 2 The maximum Firewall plaintext throughput is based on RFC2544 testing methodologies. 3 VPN throughput is measured...seperatley 9 For DFL-860E, DFL-1660, and DFL-2560(G) only 10 With optional subscription services 11 For DFL-1660 and DFL-2560(G) only Updated 12/7/11 DFL-260E DFL-860E DFL-1660 DFL-2560 DFL-2560G For more details. D-Link, the D-Link logo, and D-ViewCam are the property of D-Link Corporation or ...
...Year Subscription for DFL-2560/2560G NetDefend WCF 1-Year Subscription for DFL-2560/2560G 1 Actual performance may vary depending on network conditions and activated services. 2 The maximum Firewall plaintext throughput is based on RFC2544 testing methodologies. 3 VPN throughput is measured...seperatley 9 For DFL-860E, DFL-1660, and DFL-2560(G) only 10 With optional subscription services 11 For DFL-1660 and DFL-2560(G) only Updated 12/7/11 DFL-260E DFL-860E DFL-1660 DFL-2560 DFL-2560G For more details. D-Link, the D-Link logo, and D-ViewCam are the property of D-Link Corporation or ...
CLI Guide for DFL-260E
Page 94
Properties Name Type CertificateData PrivateKey NoCRLs PKAType Comments Specifies a symbolic name for the certificate. (Identifier) Local, Remote or Request. Certificate Description An X. 509 certificate is used to authenticate a VPN client or gateway when establishing an IPsec tunnel. Private key. Certificate data. Certificate Chapter 3. Configuration Reference 3.7. Disable CRLs (Certificate Revocation Lists). (Default: No) Encryption algorithm of the public key. (Default: Unknown) Text describing the current object. (Optional) 94 3.7.
Properties Name Type CertificateData PrivateKey NoCRLs PKAType Comments Specifies a symbolic name for the certificate. (Identifier) Local, Remote or Request. Certificate Description An X. 509 certificate is used to authenticate a VPN client or gateway when establishing an IPsec tunnel. Private key. Certificate data. Certificate Chapter 3. Configuration Reference 3.7. Disable CRLs (Certificate Revocation Lists). (Default: No) Encryption algorithm of the public key. (Default: Unknown) Text describing the current object. (Optional) 94 3.7.
CLI Guide for DFL-260E
Page 99
... the set of IP addresses should be able to connect to this type. 99 Specifies the netmask to assign to VPN clients. Configuration Reference 3.10. to the VPN client connecting to . (Optional) Specifies additional subnets behind this gateway. (Optional) Text describing the current object. (Optional...object type does not have an identifier and is identified by the name of IP addresses to use for assigning IP addresses to VPN clients. Properties IPPoolType IPPool IPPoolAddress IPPoolNetmask DNS NBNSIP DHCP Subnets Comments Specifies whether a predefined IP Pool or a static set of ...
... the set of IP addresses should be able to connect to this type. 99 Specifies the netmask to assign to VPN clients. Configuration Reference 3.10. to the VPN client connecting to . (Optional) Specifies additional subnets behind this gateway. (Optional) Text describing the current object. (Optional...object type does not have an identifier and is identified by the name of IP addresses to use for assigning IP addresses to VPN clients. Properties IPPoolType IPPool IPPoolAddress IPPoolNetmask DNS NBNSIP DHCP Subnets Comments Specifies whether a predefined IP Pool or a static set of ...
CLI Guide for DFL-260E
Page 131
... Dial-on-demand which means that the PPPoE tunnel will not be passed onward. (Default: 1492) Text describing the current object. (Optional) Description An SSL VPN interface, together with the bundled client, creates an easy to manually specify IP Address object. (Default: No) Specifies the size (in bytes) of the largest...
... Dial-on-demand which means that the PPPoE tunnel will not be passed onward. (Default: 1492) Text describing the current object. (Optional) Description An SSL VPN interface, together with the bundled client, creates an easy to manually specify IP Address object. (Default: No) Specifies the size (in bytes) of the largest...
CLI Guide for DFL-260E
Page 132
... symbolic name for this virtual LAN interface. Specifies the virtual LAN ID used for the interface. (Identifier) Specifies on which the SSL VPN clients will listen on. VLAN The physical interface that will be the IP pool from which Ethernet interface the virtual LAN is defined. ...the current object. (Optional) Description Use a VLAN to clients, eg: (sslvpn.example.com). (Optional) A range, group or network that the SSL VPN interface will receive their IP addresses. IP of the primary DNS Server. (Optional) IP of the virtual LAN interface. Specifies the network address of the...
... symbolic name for this virtual LAN interface. Specifies the virtual LAN ID used for the interface. (Identifier) Specifies on which the SSL VPN clients will listen on. VLAN The physical interface that will be the IP pool from which Ethernet interface the virtual LAN is defined. ...the current object. (Optional) Description Use a VLAN to clients, eg: (sslvpn.example.com). (Optional) A range, group or network that the SSL VPN interface will receive their IP addresses. IP of the primary DNS Server. (Optional) IP of the virtual LAN interface. Specifies the network address of the...
CLI Guide for DFL-260E
Page 177
... of Flow Metric has expired without data traffic in a flow to and from the corresponding IKE SA. (Default: 15) Do not wait for establishing IPsec VPN connections to activate IKE DPD liveness checks from this type. 3.52.9. 3.52.9. IPsecTunnelSettings Description Settings for the IPsec tunnel interfaces used for 10 times the...
... of Flow Metric has expired without data traffic in a flow to and from the corresponding IKE SA. (Default: 15) Do not wait for establishing IPsec VPN connections to activate IKE DPD liveness checks from this type. 3.52.9. 3.52.9. IPsecTunnelSettings Description Settings for the IPsec tunnel interfaces used for 10 times the...
CLI Guide for DFL-260E
Page 181
... 3.52.13. There can only be decreased to 1480. (Default: 60000) ICMP; LocalReassSettings Description 181 LengthLimSettings Description Length limitations for IP, VPN protocol. (Default: 2000) OSPF; May be one instance of the type only. Simple Key management for various protocols. Encrypted communication. (Default:...ICMPv6; Many interactive applications use large UDP packets, may otherwise be increased if tunneling protocols are used by VPN-1. (Default: 2000) IPsec IPComp; Authenticated communication. (Default: 2000) SKIP; Layer 2 Tunneling Protocol. (Default: 2000) Others;
... 3.52.13. There can only be decreased to 1480. (Default: 60000) ICMP; LocalReassSettings Description 181 LengthLimSettings Description Length limitations for IP, VPN protocol. (Default: 2000) OSPF; May be one instance of the type only. Simple Key management for various protocols. Encrypted communication. (Default:...ICMPv6; Many interactive applications use large UDP packets, may otherwise be increased if tunneling protocols are used by VPN-1. (Default: 2000) IPsec IPComp; Authenticated communication. (Default: 2000) SKIP; Layer 2 Tunneling Protocol. (Default: 2000) Others;
CLI Guide for DFL-260E
Page 186
... processing is allowed to SSL (Secure Sockets Layer). cryption, just message validation). (Default: No) TLS_RSA_EXPORT_WITH_NULL_MD Enable cipher 5 TLS_RSA_EXPORT_WITH_NULL_MD5 (no en- SSLSettings Chapter 3. SSLVPNInterfaceSettings Description SSL VPN interface settings. 186
... processing is allowed to SSL (Secure Sockets Layer). cryption, just message validation). (Default: No) TLS_RSA_EXPORT_WITH_NULL_MD Enable cipher 5 TLS_RSA_EXPORT_WITH_NULL_MD5 (no en- SSLSettings Chapter 3. SSLVPNInterfaceSettings Description SSL VPN interface settings. 186
CLI Guide for DFL-260E
Page 187
... the name of the type only. 3.52.21. StateSettings Description Parameters for every packet that violate stateful tracking rules; Configuration Reference Properties SSLVPNBeforeRules Pass SSL VPN connections sent to the security gateway directly to the TCP protocol. 187 StateSettings Chapter 3. TCPSettings Description Settings related to the SSL...
... the name of the type only. 3.52.21. StateSettings Description Parameters for every packet that violate stateful tracking rules; Configuration Reference Properties SSLVPNBeforeRules Pass SSL VPN connections sent to the security gateway directly to the TCP protocol. 187 StateSettings Chapter 3. TCPSettings Description Settings related to the SSL...
CLI Guide for DFL-260E
Page 188
... Size). (Default: 100) How to handle too low MSS values. (Default: DropLog) Maximum allowed TCP MSS (Maximum Segment Size). (Default: 1460) Limits TCP MSS for VPN connections; 3.52.22. Configuration Reference Validity of involved interfaces - helps prevent connection spoofing. (Default: Yes) Force unused URG fields to zero; normally invalid (strip=strip...
... Size). (Default: 100) How to handle too low MSS values. (Default: DropLog) Maximum allowed TCP MSS (Maximum Segment Size). (Default: 1460) Limits TCP MSS for VPN connections; 3.52.22. Configuration Reference Validity of involved interfaces - helps prevent connection spoofing. (Default: Yes) Force unused URG fields to zero; normally invalid (strip=strip...
Log Reference Guide for DFL-260E
Page 28
... DNS ESP FTP HA HTTP ICMP IDS IP IPSec L2TP NAT OSPF PPP PPPoE RADIUS SAT SMTP SNMP SSL TCP TLS UDP URL UTF VLAN VPN Full name Application Layer Gateway Address Resolution Protocol Dynamic Host Configuration Protocol Domain Name System Encapsulating Security Payload File Transfer Protocol High Availability Hyper Text...
... DNS ESP FTP HA HTTP ICMP IDS IP IPSec L2TP NAT OSPF PPP PPPoE RADIUS SAT SMTP SNMP SSL TCP TLS UDP URL UTF VLAN VPN Full name Application Layer Gateway Address Resolution Protocol Dynamic Host Configuration Protocol Domain Name System Encapsulating Security Payload File Transfer Protocol High Availability Hyper Text...
Log Reference Guide for DFL-260E
Page 29
... cannot be a valuable information source for each category maps to parameters, enclosed in the message ID. Chapter 1. The first 3 digits identify the category to IPSec VPN activities. For instance, the IPSEC category includes some hundreds of the section describing the log message. As previously mentioned, the category is only featured in...
... cannot be a valuable information source for each category maps to parameters, enclosed in the message ID. Chapter 1. The first 3 digits identify the category to IPSec VPN activities. For instance, the IPSEC category includes some hundreds of the section describing the log message. As previously mentioned, the category is only featured in...
Log Reference Guide for DFL-260E
Page 248
.... None None. 1 reason 2.22.3. None None. 1 source_ip dest_ip spi seq protocol 248 None None. 1 reason 2.22.2. IPSEC These log messages refer to the IPSEC (IPsec (VPN) events) category. 2.22.1.
.... None None. 1 reason 2.22.3. None None. 1 source_ip dest_ip spi seq protocol 248 None None. 1 reason 2.22.2. IPSEC These log messages refer to the IPSEC (IPsec (VPN) events) category. 2.22.1.
Log Reference Guide for DFL-260E
Page 270
max_ipsec_sa_negotiations_reached (ID: 01802004) Default Severity Log Message Explanation Gateway Action Recommended Action Revision WARNING The maximum number of allowed active VPN tunnels according to license. max_number_of_tunnels_reached (ID: 01802011) Default Severity Log Message Explanation Gateway Action Recommended Action WARNING Negotiation aborted due to license restrictions Reached max ...
max_ipsec_sa_negotiations_reached (ID: 01802004) Default Severity Log Message Explanation Gateway Action Recommended Action Revision WARNING The maximum number of allowed active VPN tunnels according to license. max_number_of_tunnels_reached (ID: 01802011) Default Severity Log Message Explanation Gateway Action Recommended Action WARNING Negotiation aborted due to license restrictions Reached max ...
Log Reference Guide for DFL-260E
Page 416
SSL VPN Session created [remoteip]:[remoteport]. sslvpn_connection_disallowed (ID: 06300203) 416 SSLVPN Chapter 2. sslvpn_session_closed (ID: 06300011) Default Severity Log Message Explanation ... sslvpn_max_sessions_reached (ID: 06300012) Default Severity Log Message Explanation Gateway Action Recommended Action Revision DEBUG SSL VPN can not create session. None None. 1 remoteip remoteport 2.41.2. Maximun allowed SSLVPN tunnels reached. SSL VPN can not create session. sslvpn_session_created (ID: 06300010) Default Severity Log Message Explanation Gateway Action Recommended...
SSL VPN Session created [remoteip]:[remoteport]. sslvpn_connection_disallowed (ID: 06300203) 416 SSLVPN Chapter 2. sslvpn_session_closed (ID: 06300011) Default Severity Log Message Explanation ... sslvpn_max_sessions_reached (ID: 06300012) Default Severity Log Message Explanation Gateway Action Recommended Action Revision DEBUG SSL VPN can not create session. None None. 1 remoteip remoteport 2.41.2. Maximun allowed SSLVPN tunnels reached. SSL VPN can not create session. sslvpn_session_created (ID: 06300010) Default Severity Log Message Explanation Gateway Action Recommended...