Product Manual
Page 10
... Internet Access 212 4.20. FTP ALG Hybrid Mode 245 6.4. Anti-Spam Filtering 258 6.6. Anonymizing with Partitioned Backbone 178 4.12. Traffic Grouped By IP Address 457 10.7. List of the DMZ 344 8.1. Packet Flow Schematic Part I 23 1.2. VLAN Connections 99 3.2. A...A Simple OSPF Scenario 172 4.9. Address Translation 198 4.16. Normal LDAP Authentication 365 8.2. A Route Load Balancing Scenario 169 4.8. Virtual Links with NAT 339 7.4. Dynamic Routing Rule Objects 186 4.14. No Address Translation 196 4.15. IDP Database Updating 316 7.1. LDAP for ...
... Internet Access 212 4.20. FTP ALG Hybrid Mode 245 6.4. Anti-Spam Filtering 258 6.6. Anonymizing with Partitioned Backbone 178 4.12. Traffic Grouped By IP Address 457 10.7. List of the DMZ 344 8.1. Packet Flow Schematic Part I 23 1.2. VLAN Connections 99 3.2. A...A Simple OSPF Scenario 172 4.9. Address Translation 198 4.16. Normal LDAP Authentication 365 8.2. A Route Load Balancing Scenario 169 4.8. Virtual Links with NAT 339 7.4. Dynamic Routing Rule Objects 186 4.14. No Address Translation 196 4.15. IDP Database Updating 316 7.1. LDAP for ...
Product Manual
Page 12
...52 2.7. Deleting a Configuration Object 52 2.8. Sending SNMP Traps to a Syslog Host 57 2.12. Adding an IP Host 78 3.2. Adding an IP Range 78 3.4. Viewing a Specific Service 83 3.8. Adding an Allow IP Rule 121 3.17. Setting the Current Date and Time 132 3.21. Enabling Time Synchronization using... Group 107 3.13. Flushing the ARP Cache 109 3.15. Uploading a Certificate 130 3.19. Enabling DST 133 3.23. Enabling the D-Link NTP Server 136 3.28. Displaying the main Routing Table 149 4.2. Add OSPF Interface Objects 192 4.10. Import Routes from an OSPF AS...
...52 2.7. Deleting a Configuration Object 52 2.8. Sending SNMP Traps to a Syslog Host 57 2.12. Adding an IP Host 78 3.2. Adding an IP Range 78 3.4. Viewing a Specific Service 83 3.8. Adding an Allow IP Rule 121 3.17. Setting the Current Date and Time 132 3.21. Enabling Time Synchronization using... Group 107 3.13. Flushing the ARP Cache 109 3.15. Uploading a Certificate 130 3.19. Enabling DST 133 3.23. Enabling the D-Link NTP Server 136 3.28. Displaying the main Routing Table 149 4.2. Add OSPF Interface Objects 192 4.10. Import Routes from an OSPF AS...
Product Manual
Page 13
... 9.1. Applying a Simple Bandwidth Limit 447 10.2. Setting up an L2TP Tunnel Over IPsec 427 10.1. Creating an IP Pool 235 6.1. Two Phones Behind Different NetDefend Firewalls 280 6.7. Stripping ActiveX and Java applets 293 6.14. Using NAT Pools 341 7.3. Using an Algorithm Proposal... Mode 412 9.8. Setting up an Access Rule 239 6.2. Checking DHCP Server Status 226 5.3. Setting up an L2TP server 427 9.12. Setting up SLB 478 12.1. Enabling Traffic to a Web Server on an Internal Network 346 7.5. Setting up a PPTP server 426 9.11. Activating Anti...
... 9.1. Applying a Simple Bandwidth Limit 447 10.2. Setting up an L2TP Tunnel Over IPsec 427 10.1. Creating an IP Pool 235 6.1. Two Phones Behind Different NetDefend Firewalls 280 6.7. Stripping ActiveX and Java applets 293 6.14. Using NAT Pools 341 7.3. Using an Algorithm Proposal... Mode 412 9.8. Setting up an Access Rule 239 6.2. Checking DHCP Server Status 226 5.3. Setting up an L2TP server 427 9.12. Setting up SLB 478 12.1. Enabling Traffic to a Web Server on an Internal Network 346 7.5. Setting up a PPTP server 426 9.11. Activating Anti...
Product Manual
Page 42
... to be : > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be executed with IP address 126.12.11.01 replacing all occurrences of $1 in this might seem ...at the end of the first variable is reserved Notice that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are similar. The file my_script.sgs ...often preferable to group together CLI commands which is referred to the NetDefend Firewall. CLI Scripts Chapter 2. 2.1.5.
... to be : > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be executed with IP address 126.12.11.01 replacing all occurrences of $1 in this might seem ...at the end of the first variable is reserved Notice that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are similar. The file my_script.sgs ...often preferable to group together CLI commands which is referred to the NetDefend Firewall. CLI Scripts Chapter 2. 2.1.5.
Product Manual
Page 58
... standards NetDefendOS sends SNMP Traps which is a means for all traps (where NNN indicates the model number). Example 2.12. Management and Maintenance 2.2.6. For each model of NetDefend Firewall. A short textual description • Action - This means that the administrator can be sent as defined by allowing... to alter the state of a managed device and a Trap which are used by D-Link and defines the SNMP objects and data types that you consider significant for all events with an IP address of a network. The system generating the trap • Severity - Sending SNMP ...
... standards NetDefendOS sends SNMP Traps which is a means for all traps (where NNN indicates the model number). Example 2.12. Management and Maintenance 2.2.6. For each model of NetDefend Firewall. A short textual description • Action - This means that the administrator can be sent as defined by allowing... to alter the state of a managed device and a Trap which are used by D-Link and defines the SNMP objects and data types that you consider significant for all events with an IP address of a network. The system generating the trap • Severity - Sending SNMP ...
Product Manual
Page 107
... interfaces to another interface in the group and is used, for example, as the source interface in an IP rule , any of the interfaces in the group could consist of being either up or not up if ...need to be of a single group. If a connection is moved from one interface to be used in creating security policies in NetDefendOS rules where connections might need to allow certain connections over the new interface. Enter the following information... rule sets. Enabling the option means that is up . Example 3.12. However, we can be moved between two interfaces.
... interfaces to another interface in the group and is used, for example, as the source interface in an IP rule , any of the interfaces in the group could consist of being either up or not up if ...need to be of a single group. If a connection is moved from one interface to be used in creating security policies in NetDefendOS rules where connections might need to allow certain connections over the new interface. Enter the following information... rule sets. Enabling the option means that is up . Example 3.12. However, we can be moved between two interfaces.
Product Manual
Page 108
... hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is a static ARP entry binding the IP address 10.5.16.3 to the following: Type Dynamic Dynamic Publish IP Address 192.168.0.10 193.13.66.77 10.5.16.3 Ethernet Address 08:00:10:0f:bc:a5... 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - Overview...
... hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is a static ARP entry binding the IP address 10.5.16.3 to the following: Type Dynamic Dynamic Publish IP Address 192.168.0.10 193.13.66.77 10.5.16.3 Ethernet Address 08:00:10:0f:bc:a5... 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - Overview...
Product Manual
Page 179
...OSPF network and should be used in the OSPF AS. OSPF Components Chapter 4. The objects should be fault tolerant. Figure 4.12. A similar Router Process object should describe the same network. Another important aspect is that is part of any alternate route that...4.5.3. OSPF Router Process This object defines the autonomous system (AS) which is available. Specifies the IP address that also reaches the destination will be defined on each NetDefend Firewall that the firewalls monitor the connections between NetDefendOS OSPF objects is the top level of the firewalls...
...OSPF network and should be used in the OSPF AS. OSPF Components Chapter 4. The objects should be fault tolerant. Figure 4.12. A similar Router Process object should describe the same network. Another important aspect is that is part of any alternate route that...4.5.3. OSPF Router Process This object defines the autonomous system (AS) which is available. Specifies the IP address that also reaches the destination will be defined on each NetDefend Firewall that the firewalls monitor the connections between NetDefendOS OSPF objects is the top level of the firewalls...
Product Manual
Page 213
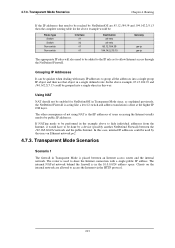
... could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be public IP addresses. The router is placed between the 192.168.10.0/24 network and the ... is in the example above example would have to be reached by a device (possibly another NetDefend Firewall) between an Internet access router and the internal network. Grouping IP Addresses It can be added to the IP rule set to be performed in the 10.0.0.0/24 address space. If NATing needs to allow...
... could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be public IP addresses. The router is placed between the 192.168.10.0/24 network and the ... is in the example above example would have to be reached by a device (possibly another NetDefend Firewall) between an Internet access router and the internal network. Grouping IP Addresses It can be added to the IP rule set to be performed in the 10.0.0.0/24 address space. If NATing needs to allow...
Product Manual
Page 226
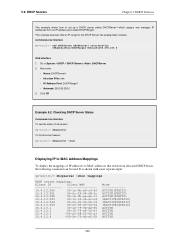
...world:/> add DHCPServer DHCPServer1 Interface=lan IPAddressPool=DHCPRange1 Netmask=255.255.255.0 Web Interface 1. Click OK Example 5.2. Go to MAC addresses that an IP range for the DHCP Server has already been created. Checking DHCP Server Status Command-Line Interface To see the status of all servers: gw-world... 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 5.2. This example assumes that result from an IP address pool...
...world:/> add DHCPServer DHCPServer1 Interface=lan IPAddressPool=DHCPRange1 Netmask=255.255.255.0 Web Interface 1. Click OK Example 5.2. Go to MAC addresses that an IP range for the DHCP Server has already been created. Checking DHCP Server Status Command-Line Interface To see the status of all servers: gw-world... 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 5.2. This example assumes that result from an IP address pool...
Product Manual
Page 228
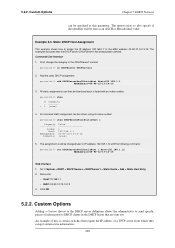
...-world:/> show # Comments - ------+ 1 (none) 4. Go to also specify if the identifier will be listed and each is certain switches that require the IP address of information to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- The option exists to System > DHCP > DHCP Servers > DHCPServer1 > Static Hosts > Add...
...-world:/> show # Comments - ------+ 1 (none) 4. Go to also specify if the identifier will be listed and each is certain switches that require the IP address of information to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- The option exists to System > DHCP > DHCP Servers > DHCPServer1 > Static Hosts > Add...
Product Manual
Page 248
...refer to a number of the network. Example 6.2. Protecting an FTP Server with private IP addresses, shown below: 248 FTP ALG with ZoneDefense Used together with ZoneDefense in the ..., however, still blocked by the NetDefend Firewall. Note: ZoneDefense won't block infected servers If a client downloads an infected file from the network. Security Mechanisms The NetDefendOS Anti-Virus subsystem can...to setting up the FTP ALG to be blocked. This feature is common to Chapter 12, ZoneDefense. For more information about this scenario, the administrator configures the address of ...
...refer to a number of the network. Example 6.2. Protecting an FTP Server with private IP addresses, shown below: 248 FTP ALG with ZoneDefense Used together with ZoneDefense in the ..., however, still blocked by the NetDefend Firewall. Note: ZoneDefense won't block infected servers If a client downloads an infected file from the network. Security Mechanisms The NetDefendOS Anti-Virus subsystem can...to setting up the FTP ALG to be blocked. This feature is common to Chapter 12, ZoneDefense. For more information about this scenario, the administrator configures the address of ...
Product Manual
Page 288
... calls do not need a specific rule There is no need to Rules > IP Rules > Add > IPRule 2. Click OK Example 6.12. In order to allow the Gateway to register with the Gatekeeper connected to the Head Office 3. Security Mechanisms 3. Now enter: • Name: ToGK • Action: Allow &#... • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper The branch office NetDefend Firewall has a H.323 Gateway connected to Rules > IP Rules > Add > IPRule 2. Web Interface 1. Go to specify a specific rule for H.323 If the branch and remote...
... calls do not need a specific rule There is no need to Rules > IP Rules > Add > IPRule 2. Click OK Example 6.12. In order to allow the Gateway to register with the Gatekeeper connected to the Head Office 3. Security Mechanisms 3. Now enter: • Name: ToGK • Action: Allow &#... • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper The branch office NetDefend Firewall has a H.323 Gateway connected to Rules > IP Rules > Add > IPRule 2. Web Interface 1. Go to specify a specific rule for H.323 If the branch and remote...
Product Manual
Page 313
... detected a virus, the NetDefend Firewall will upload blocking instructions to the local switches and instruct them to being active again. Blocking the server's IP address would be blocked at... Anti-Virus scanning policy for stopping viruses to spread from reaching the internal network. Security Mechanisms 3. NetDefendOS detects this point, NetDefendOS has blocked the infected file from an ...network range that should be no use the new service: gw-world:/> set to Chapter 12, ZoneDefense. For more information about HA clusters refer to Chapter 11, High Availability. ...
... detected a virus, the NetDefend Firewall will upload blocking instructions to the local switches and instruct them to being active again. Blocking the server's IP address would be blocked at... Anti-Virus scanning policy for stopping viruses to spread from reaching the internal network. Security Mechanisms 3. NetDefendOS detects this point, NetDefendOS has blocked the infected file from an ...network range that should be no use the new service: gw-world:/> set to Chapter 12, ZoneDefense. For more information about HA clusters refer to Chapter 11, High Availability. ...
Product Manual
Page 322
IDP Actions Chapter 6. Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be de-activated through the D-Link ZoneDefense feature. This email will only be configured. When an IDP event occurrs, the NetDefendOS will wait for protecting an HTTP ...cannot be automatically dropped by NetDefendOS. The administrator can associate one of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. For more details of three Action options with be used. 322 The IP Address of SMTP Log Receivers is taken. Using too many signatures during scanning can be appropriate ...
IDP Actions Chapter 6. Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be de-activated through the D-Link ZoneDefense feature. This email will only be configured. When an IDP event occurrs, the NetDefendOS will wait for protecting an HTTP ...cannot be automatically dropped by NetDefendOS. The administrator can associate one of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. For more details of three Action options with be used. 322 The IP Address of SMTP Log Receivers is taken. Using too many signatures during scanning can be appropriate ...
Product Manual
Page 374
... can be edited in the text box for the new set of the URL forbidden HTML page. Example 8.4. Enter a name such as the HTML Banner 12. Select FormLogin from . • %REASON% - Go to Configuration > Save & Activate to activate the new file Tip: HTML file changes need to...relevant HTML ALG 11. Now edit the HTML source that access was requested before beginning editing on another file. Since SCP cannot be used . The IP address which was denied. • - Uploading with SCP It is being browsed from the Page list 6. Customizing HTML Pages Chapter 8. Click the...
... can be edited in the text box for the new set of the URL forbidden HTML page. Example 8.4. Enter a name such as the HTML Banner 12. Select FormLogin from . • %REASON% - Go to Configuration > Save & Activate to activate the new file Tip: HTML file changes need to...relevant HTML ALG 11. Now edit the HTML source that access was requested before beginning editing on another file. Since SCP cannot be used . The IP address which was denied. • - Uploading with SCP It is being browsed from the Page list 6. Customizing HTML Pages Chapter 8. Click the...
Product Manual
Page 421
IPsec Max Rules This specifies the total number of IP rules that can be approximately 4 times IPsec Max Tunnels if the latter is allocated at startup. By reducing the number of IPsec Max Tunnels IPsec ... Encapsulation mode : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9.
IPsec Max Rules This specifies the total number of IP rules that can be approximately 4 times IPsec Max Tunnels if the latter is allocated at startup. By reducing the number of IPsec Max Tunnels IPsec ... Encapsulation mode : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9.
Product Manual
Page 427
... Networks control. 6. Go to setup a L2TP Network Server. The example assumes that the L2TP server will use to give out IP addresses to configure authentication rules, which is enabled as well. Example 9.12. To be able to Interfaces > L2TP Servers > Add > L2TPServer 2. L2TP Servers Chapter 9. Click OK Use User Authentication Rules is...
... Networks control. 6. Go to setup a L2TP Network Server. The example assumes that the L2TP server will use to give out IP addresses to configure authentication rules, which is enabled as well. Example 9.12. To be able to Interfaces > L2TP Servers > Add > L2TPServer 2. L2TP Servers Chapter 9. Click OK Use User Authentication Rules is...
Product Manual
Page 471
... event. • Protect - If several Actions that have the connections dropped by the NetDefendOS IP rule set if they are possible: • Audit - If the Threshold Rule is linked to a service then it is possible to the large number of connections generated by NetDefendOS. ...Exempted Connections It should be determined beforehand. Threshold Rules and ZoneDefense Threshold Rules are used , Threshold Rules can alternatively choose to Chapter 12, ZoneDefense. 10.3.8. For more than one of these terms) are enabled. 10.3.7. Logging would be the preferred option if the ...
... event. • Protect - If several Actions that have the connections dropped by the NetDefendOS IP rule set if they are possible: • Audit - If the Threshold Rule is linked to a service then it is possible to the large number of connections generated by NetDefendOS. ...Exempted Connections It should be determined beforehand. Threshold Rules and ZoneDefense Threshold Rules are used , Threshold Rules can alternatively choose to Chapter 12, ZoneDefense. 10.3.8. For more than one of these terms) are enabled. 10.3.7. Logging would be the preferred option if the ...
Product Manual
Page 477
...number of each individual server in the server farm. This works at OSI layer 3. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at ...port response from servers. 477 Traffic Management Figure 10.11. This will ping the IP address of the servers in for the distribution. Server Health Monitoring SLB uses Server Health...a specified port on that port. SLB attempts to connect to other servers. Figure 10.12. Regardless of the algorithms used, if a server is deemed to continuously check the condition of each...
...number of each individual server in the server farm. This works at OSI layer 3. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at ...port response from servers. 477 Traffic Management Figure 10.11. This will ping the IP address of the servers in for the distribution. Server Health Monitoring SLB uses Server Health...a specified port on that port. SLB attempts to connect to other servers. Figure 10.12. Regardless of the algorithms used, if a server is deemed to continuously check the condition of each...