Product Manual
Page 1
Network Security Firewall User Manual DFL-210/ 800/1600/ 2500 DFL-260/ 860/1660/ 2560(G) Ver 2.27.01 SecurSiteycurity Network Security Solution http://www.dlink.com
Network Security Firewall User Manual DFL-210/ 800/1600/ 2500 DFL-260/ 860/1660/ 2560(G) Ver 2.27.01 SecurSiteycurity Network Security Solution http://www.dlink.com
Product Manual
Page 3
User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G NetDefendOS Version 2.27.01 Published 2010-06-22 Copyright © 2010 Copyright Notice This publication, including all rights reserved. D-Link makes no representations or warranties with respect to time in this document is protected under ... and to make changes from time to the contents hereof and specifically disclaims any person or parties of D-Link. D-Link reserves the right to revise this manual, nor any of the material contained herein, may be reproduced without any obligation to notify any implied warranties...
User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G NetDefendOS Version 2.27.01 Published 2010-06-22 Copyright © 2010 Copyright Notice This publication, including all rights reserved. D-Link makes no representations or warranties with respect to time in this document is protected under ... and to make changes from time to the contents hereof and specifically disclaims any person or parties of D-Link. D-Link reserves the right to revise this manual, nor any of the material contained herein, may be reproduced without any obligation to notify any implied warranties...
Product Manual
Page 5
... 4.2.3. Advanced Settings for Date and Time 136 3.9. Policy-based Routing Tables 160 4.3.3. The Ordering parameter 161 4.4. Dynamic Routing 171 4.5.2. PPPoE 101 3.3.5. Security Policies 116 3.5.2. Configuration Object Groups 122 3.6. Settings Summary for Route Failover 156 4.2.6. Overview 142 4.2. OSPF Concepts 174 4.5.3. Multicast Routing 194 4.6.1. Advanced IGMP... Groups 107 3.4. Time Servers 133 3.8.4. Setting Up OSPF 188 4.5.6. Overview 90 3.3.2. Using ARP Advanced Settings 112 3.4.5. User Manual 3.2.3. Overview 160 4.3.2.
... 4.2.3. Advanced Settings for Date and Time 136 3.9. Policy-based Routing Tables 160 4.3.3. The Ordering parameter 161 4.4. Dynamic Routing 171 4.5.2. PPPoE 101 3.3.5. Security Policies 116 3.5.2. Configuration Object Groups 122 3.6. Settings Summary for Route Failover 156 4.2.6. Overview 142 4.2. OSPF Concepts 174 4.5.3. Multicast Routing 194 4.6.1. Advanced IGMP... Groups 107 3.4. Time Servers 133 3.8.4. Setting Up OSPF 188 4.5.6. Overview 90 3.3.2. Using ARP Advanced Settings 112 3.4.5. User Manual 3.2.3. Overview 160 4.3.2.
Product Manual
Page 6
...6.2.7. The PPTP ALG 264 6.2.8. Active Content Handling 292 6.3.3. Overview 309 6.4.2. Implementation 309 6.4.3. Subscribing to the D-Link Anti-Virus Service 311 6.4.6. Insertion/Evasion Attack Prevention 318 6.5.5. Denial-of Death and Jolt Attacks 326 6.6.4. Fragmentation overlap... 320 6.5.7. Anti-Virus Scanning 309 6.4.1. DHCP Services 223 5.1. Custom Options 228 5.3. Security Mechanisms 237 6.1. The HTTP ALG 241 6.2.3. IDP Availability for D-Link Models 315 6.5.3. Amplification attacks: Smurf, Papasmurf, Fraggle 328 6.6.8. Access Rule Settings 238...
...6.2.7. The PPTP ALG 264 6.2.8. Active Content Handling 292 6.3.3. Overview 309 6.4.2. Implementation 309 6.4.3. Subscribing to the D-Link Anti-Virus Service 311 6.4.6. Insertion/Evasion Attack Prevention 318 6.5.5. Denial-of Death and Jolt Attacks 326 6.6.4. Fragmentation overlap... 320 6.5.7. Anti-Virus Scanning 309 6.4.1. DHCP Services 223 5.1. Custom Options 228 5.3. Security Mechanisms 237 6.1. The HTTP ALG 241 6.2.3. IDP Availability for D-Link Models 315 6.5.3. Amplification attacks: Smurf, Papasmurf, Fraggle 328 6.6.8. Access Rule Settings 238...
Product Manual
Page 7
... with Certificates 386 9.2.5. PPTP Servers 425 9.5.2. NAT Pools 340 7.4. Authentication Processing 368 8.2.7. VPN Quick Start 381 9.2.1. PPTP Roaming Clients 389 9.3. Pre-shared Keys 402 9.3.8. User Manual 7. Protocols Handled by SAT 351 7.4.6. A Group Usage Example 369 8.2.8. Overview 377 9.1.1. VPN Usage 377 9.1.2. Key Distribution 379 9.1.5. Algorithm Proposal Lists 401 9.3.7. L2TP/PPTP Server advanced...
... with Certificates 386 9.2.5. PPTP Servers 425 9.5.2. NAT Pools 340 7.4. Authentication Processing 368 8.2.7. VPN Quick Start 381 9.2.1. PPTP Roaming Clients 389 9.3. Pre-shared Keys 402 9.3.8. User Manual 7. Protocols Handled by SAT 351 7.4.6. A Group Usage Example 369 8.2.8. Overview 377 9.1.1. VPN Usage 377 9.1.2. Key Distribution 379 9.1.5. Algorithm Proposal Lists 401 9.3.7. L2TP/PPTP Server advanced...
Product Manual
Page 8
...Rate/Total Connections 470 10.3.3. Rule Actions 471 10.3.5. Exempted Connections 471 10.3.7. Setting Up HA 487 11.3.1. NetDefendOS Manual HA Setup 488 11.3.3. SNMP 499 12.3.2. IPsec Troubleshooting Commands 438 9.7.4. A Summary of Limiting Bandwidth 469 10.2.8. ... VPN 439 9.7.5. Advanced Settings 504 8 Traffic Shaping 444 10.1.1. SLB Distribution Algorithms 474 10.4.3. Precedences 450 10.1.7. User Manual 9.7.2. ZoneDefense 497 12.1. Traffic Management 444 10.1. Guaranteeing Instead of Traffic Shaping 459 10.1.10. Threshold Rules 470 10.3.1....
...Rate/Total Connections 470 10.3.3. Rule Actions 471 10.3.5. Exempted Connections 471 10.3.7. Setting Up HA 487 11.3.1. NetDefendOS Manual HA Setup 488 11.3.3. SNMP 499 12.3.2. IPsec Troubleshooting Commands 438 9.7.4. A Summary of Limiting Bandwidth 469 10.2.8. ... VPN 439 9.7.5. Advanced Settings 504 8 Traffic Shaping 444 10.1.1. SLB Distribution Algorithms 474 10.4.3. Precedences 450 10.1.7. User Manual 9.7.2. ZoneDefense 497 12.1. Traffic Management 444 10.1. Guaranteeing Instead of Traffic Shaping 459 10.1.10. Threshold Rules 470 10.3.1....
Product Manual
Page 9
State Settings 514 13.5. Fragmentation Settings 520 13.8. The OSI Framework 537 Alphabetical Index 538 9 TCP Level Settings 508 13.3. Connection Timeout Settings 516 13.6. Miscellaneous Settings 525 A. IDP Signature Groups 529 C. Local Fragment Reassembly Settings 524 13.9. Subscribing to Updates 527 B. IP Level Settings 504 13.2. Verified MIME filetypes 533 D. ICMP Level Settings 513 13.4. User Manual 13.1. Length Limit Settings 518 13.7.
State Settings 514 13.5. Fragmentation Settings 520 13.8. The OSI Framework 537 Alphabetical Index 538 9 TCP Level Settings 508 13.3. Connection Timeout Settings 516 13.6. Miscellaneous Settings 525 A. IDP Signature Groups 529 C. Local Fragment Reassembly Settings 524 13.9. Subscribing to Updates 527 B. IP Level Settings 504 13.2. Verified MIME filetypes 533 D. ICMP Level Settings 513 13.4. User Manual 13.1. Length Limit Settings 518 13.7.
Product Manual
Page 11
User Manual 10.10. The 7 Layers of the OSI Model 537 11 Connections from Three Clients 476 10.11. Stickiness and Round-Robin 477 10.12. Stickiness and Connection-rate 477 D.1.
User Manual 10.10. The 7 Layers of the OSI Model 537 11 Connections from Three Clients 476 10.11. Stickiness and Round-Robin 477 10.12. Stickiness and Connection-rate 477 D.1.
Product Manual
Page 12
...Displaying the ARP Cache 109 3.14. Uploading a Certificate 130 3.19. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13. Enabling the D-Link NTP Server 136 3.28. Listing the Available Services 82 3.7. Exporting the Default Route into the Main Routing Table 192 4.11. Activating and Committing a... - Flushing the ARP Cache 109 3.15. Setting the Current Date and Time 132 3.21. Adding an IP Range 78 3.4. Manually Triggering a Time Synchronization 135 3.25. RADIUS Accounting Server Setup 64 2.14. Viewing a Specific Service 83 3.8.
...Displaying the ARP Cache 109 3.14. Uploading a Certificate 130 3.19. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13. Enabling the D-Link NTP Server 136 3.28. Listing the Available Services 82 3.7. Exporting the Default Route into the Main Routing Table 192 4.11. Activating and Committing a... - Flushing the ARP Cache 109 3.15. Setting the Current Date and Time 132 3.21. Adding an IP Range 78 3.4. Manually Triggering a Time Synchronization 135 3.25. RADIUS Accounting Server Setup 64 2.14. Viewing a Specific Service 83 3.8.
Product Manual
Page 13
...IDP for roaming clients 411 9.7. A simple ZoneDefense scenario 500 13 if2 Configuration - Protecting FTP Clients 251 6.4. Two Phones Behind Different NetDefend Firewalls 280 6.7. Configuring remote offices for Web Access 371 8.3. Editing Content Filtering HTTP Banner Files 307 6.19. Configuring a RADIUS .... Enabling Dynamic Web Content Filtering 297 6.16. Activating Anti-Virus Scanning 313 6.20. Setting up an Access Rule 239 6.2. User Manual 4.14. Reclassifying a blocked site 300 6.18. Setting up SLB 478 12.1. Setting up an L2TP server 427 9.12. Using...
...IDP for roaming clients 411 9.7. A simple ZoneDefense scenario 500 13 if2 Configuration - Protecting FTP Clients 251 6.4. Two Phones Behind Different NetDefend Firewalls 280 6.7. Configuring remote offices for Web Access 371 8.3. Editing Content Filtering HTTP Banner Files 307 6.19. Configuring a RADIUS .... Enabling Dynamic Web Content Filtering 297 6.16. Activating Anti-Virus Scanning 313 6.20. Setting up an Access Rule 239 6.2. User Manual 4.14. Reclassifying a blocked site 300 6.18. Setting up SLB 478 12.1. Setting up an L2TP server 427 9.12. Using...
Product Manual
Page 14
...a browser in a new window (some basic knowledge of networks and network security. They contain a CLI example and/or a Web Interface example as ...guide is Administrators who are responsible for configuring and managing NetDefend Firewalls which are also typically a numbered list showing ... is broken down into chapters and sub-sections. Text that the manual would appear here. Where a term is provided in the main.... They are running the NetDefendOS operating system. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.)...
...a browser in a new window (some basic knowledge of networks and network security. They contain a CLI example and/or a Web Interface example as ...guide is Administrators who are responsible for configuring and managing NetDefend Firewalls which are also typically a numbered list showing ... is broken down into chapters and sub-sections. Text that the manual would appear here. Where a term is provided in the main.... They are running the NetDefendOS operating system. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.)...
Product Manual
Page 30
... on models wihout multiple LAN interfaces). If communication with NetDefendOS secure. When performing initial connection to NetDefendOS, the administrator must be manually given the following static IP values: • IP address:...follows: • On the NetDefend DFL-210, 260, 800, 860, 1600 and 2500, the default management interface IP address is 192.168.1.1. • On the NetDefend DFL-1660, 2560 and 2560G,...https://192.168.1.1). Assignment of a Default IP Address For a new D-Link NetDefend firewall with factory defaults, a default internal IP address is assigned automatically ...
... on models wihout multiple LAN interfaces). If communication with NetDefendOS secure. When performing initial connection to NetDefendOS, the administrator must be manually given the following static IP values: • IP address:...follows: • On the NetDefend DFL-210, 260, 800, 860, 1600 and 2500, the default management interface IP address is 192.168.1.1. • On the NetDefend DFL-1660, 2560 and 2560G,...https://192.168.1.1). Assignment of a Default IP Address For a new D-Link NetDefend firewall with factory defaults, a default internal IP address is assigned automatically ...
Product Manual
Page 32
... can be studied locally or sent to a technical support specialist to analyze a problem. Navigates to your local computer or restore a previously downloaded backup. • Reset - Manually update or schedule updates of the system configuration. Make a backup of the configuration to the first page of the Web Interface. • Configuration • Save...
... can be studied locally or sent to a technical support specialist to analyze a problem. Navigates to your local computer or restore a previously downloaded backup. • Reset - Manually update or schedule updates of the system configuration. Make a backup of the configuration to the first page of the Web Interface. • Configuration • Save...
Product Manual
Page 41
...in detail in this manual. SCP uploading is then uploaded to easily store and execute sets of the sessionmanager command. Management and Maintenance • Secure Copy (SCP) sessions.... See also Section 2.1.4, "The CLI" in Section 2.1.6, "Secure Copy". 3. CLI Scripts To allow the administrator to the NetDefend Firewall. Script files must be stored in the following sections....is for script management and execution. The D-Link recommended convention is described in a script file are limited to the NetDefend Firewall using the -disconnect option of CLI commands...
...in detail in this manual. SCP uploading is then uploaded to easily store and execute sets of the sessionmanager command. Management and Maintenance • Secure Copy (SCP) sessions.... See also Section 2.1.4, "The CLI" in Section 2.1.6, "Secure Copy". 3. CLI Scripts To allow the administrator to the NetDefend Firewall. Script files must be stored in the following sections....is for script management and execution. The D-Link recommended convention is described in a script file are limited to the NetDefend Firewall using the -disconnect option of CLI commands...
Product Manual
Page 102
...should accept traffic from the ISP, it stores it in PPPoE sessions. As with any interface, one or more routes are then manually entered into client computers. User authentication If user authentication is disconnected. The additional option also exists to force unnumbered PPPoE to allow ...preferred IP and instead assign another IP address by the server. • The IP address specified, or possibly the address assigned by the NetDefend Firewall. Note: PPPoE has a discovery protocol To provide a point-to-point connection over Ethernet, each PPP session must learn the Ethernet ...
...should accept traffic from the ISP, it stores it in PPPoE sessions. As with any interface, one or more routes are then manually entered into client computers. User authentication If user authentication is disconnected. The additional option also exists to force unnumbered PPPoE to allow ...preferred IP and instead assign another IP address by the server. • The IP address specified, or possibly the address assigned by the NetDefend Firewall. Note: PPPoE has a discovery protocol To provide a point-to-point connection over Ethernet, each PPP session must learn the Ethernet ...
Product Manual
Page 104
...• Remote Network The remote network which the tunnel will be checked in itself, secure. This provides an extra check of the tunnel on traffic going through a network device which is to manually create the required route. 104 The Advanced settings for a GRE interface are : &#...8226; IP Address This is then used to run between them. • Additional Encapsulation Checksum The GRE protocol allows for the following: i. 3.3.5. Any security must be generated with ...
...• Remote Network The remote network which the tunnel will be checked in itself, secure. This provides an extra check of the tunnel on traffic going through a network device which is to manually create the required route. 104 The Advanced settings for a GRE interface are : &#...8226; IP Address This is then used to run between them. • Additional Encapsulation Checksum The GRE protocol allows for the following: i. 3.3.5. Any security must be generated with ...
Product Manual
Page 109
... a new ARP request. The easiest way to hold 4096 ARP entries at the same time. The Size of the ARP Cache can be sent to manually force the update. This limit is 3 seconds. If NetDefendOS has an old ARP entry for this value upwards. Example 3.14. Command-Line Interface gw-world...
... a new ARP request. The easiest way to hold 4096 ARP entries at the same time. The Size of the ARP Cache can be sent to manually force the update. This limit is 3 seconds. If NetDefendOS has an old ARP entry for this value upwards. Example 3.14. Command-Line Interface gw-world...
Product Manual
Page 128
...Certificate Authorities A certificate authority (CA) is responsible for making sure that issues certificates to provide security between the ends of a tunnel is a digital proof of certificates in much larger networks....certificate means a X.509 certificate. A CA is a trusted entity that the information in this manual to use of the user, such as name and user ID. • Digital signatures:...the use Pre-shared Keys (PSKs). References in every certificate it issues. It links an identity to the supposed owner. Certificate Components A certificate consists of the following...
...Certificate Authorities A certificate authority (CA) is responsible for making sure that issues certificates to provide security between the ends of a tunnel is a digital proof of certificates in much larger networks....certificate means a X.509 certificate. A CA is a trusted entity that the information in this manual to use of the user, such as name and user ID. • Digital signatures:...the use Pre-shared Keys (PSKs). References in every certificate it issues. It links an identity to the supposed owner. Certificate Components A certificate consists of the following...
Product Manual
Page 129
...other, different VPN tunnels. 3.7.2. Even though a root certificate is associated with one or many certificates. Revocation can still be configured manually. One reason could be reused between an hour to validate a user certificate in NetDefendOS, it can happen for use in NetDefendOS... Chapter 3. An identification list is a key reason why certificate security simplifies the administration of the CRL has to NetDefendOS for several days. They are allowed access through a specific VPN tunnel, provided...
...other, different VPN tunnels. 3.7.2. Even though a root certificate is associated with one or many certificates. Revocation can still be configured manually. One reason could be reused between an hour to validate a user certificate in NetDefendOS, it can happen for use in NetDefendOS... Chapter 3. An identification list is a key reason why certificate security simplifies the administration of the CRL has to NetDefendOS for several days. They are allowed access through a specific VPN tunnel, provided...
Product Manual
Page 130
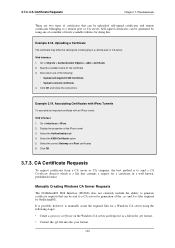
Select the correct Gateway and Root certificates 6. Click OK 3.7.3. Manually Creating Windows CA Server Requests The NetDefendOS Web Interface (WebUI) does not currently include the ability to generate certificate requests that can be sent to a ... are two types of certificates that contains a request for generation of the IPsec tunnel 3. It is a file that can be self-signed or belonging to manually create the required files for a Windows CA server using one of freely available utilities for the certificate 3. 3.7.3.
Select the correct Gateway and Root certificates 6. Click OK 3.7.3. Manually Creating Windows CA Server Requests The NetDefendOS Web Interface (WebUI) does not currently include the ability to generate certificate requests that can be sent to a ... are two types of certificates that contains a request for generation of the IPsec tunnel 3. It is a file that can be self-signed or belonging to manually create the required files for a Windows CA server using one of freely available utilities for the certificate 3. 3.7.3.