Product Manual
Page 3
... OR FAILURE OF THE PRODUCT, EVEN IF D-LINK IS INFORMED OF THE POSSIBILITY OF SUCH DAMAGES. Neither this document is protected under international copyright laws, with respect to the contents hereof and specifically disclaims any implied warranties of such revision or changes. User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G...
... OR FAILURE OF THE PRODUCT, EVEN IF D-LINK IS INFORMED OF THE POSSIBILITY OF SUCH DAMAGES. Neither this document is protected under international copyright laws, with respect to the contents hereof and specifically disclaims any implied warranties of such revision or changes. User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G...
Product Manual
Page 6
...Security Mechanisms 237 6.1. The FTP ALG 244 6.2.4. Overview 292 6.3.2. Dynamic Web Content Filtering 295 6.4. Activating Anti-Virus Scanning 310 6.4.4. Insertion/Evasion Attack Prevention 318 6.5.5. IDP Signature Groups 320 6.5.7. DoS Attack Mechanisms 326 6.6.3. Blacklisting Hosts and Networks 331 6 User Manual...DHCP Relay Advanced Settings 231 5.4. Overview 237 6.1.2. Static Content Filtering 293 6.3.4. SMTP Log Receiver for D-Link Models 315 6.5.3. Distributed DoS Attacks 329 6.7. Transparent Mode Scenarios 213 4.7.4. The HTTP ALG 241 6.2.3. ...
...Security Mechanisms 237 6.1. The FTP ALG 244 6.2.4. Overview 292 6.3.2. Dynamic Web Content Filtering 295 6.4. Activating Anti-Virus Scanning 310 6.4.4. Insertion/Evasion Attack Prevention 318 6.5.5. IDP Signature Groups 320 6.5.7. DoS Attack Mechanisms 326 6.6.3. Blacklisting Hosts and Networks 331 6 User Manual...DHCP Relay Advanced Settings 231 5.4. Overview 237 6.1.2. Static Content Filtering 293 6.3.4. SMTP Log Receiver for D-Link Models 315 6.5.3. Distributed DoS Attacks 329 6.7. Transparent Mode Scenarios 213 4.7.4. The HTTP ALG 241 6.2.3. ...
Product Manual
Page 12
...Network 78 3.3. Adding an Ethernet Address 79 3.6. Creating an Interface Group 107 3.13. Setting up the Entire System 74 2.16. Manually Triggering a Time Synchronization 135 3.25. Modifying the Maximum Adjustment Value 135 3.26. Forcing Time Synchronization 136 3.27. Displaying the ...VLAN 100 3.11. Displaying the ARP Cache 109 3.14. Defining a Static ARP Entry 110 3.16. Enabling DST 133 3.23. Enabling the D-Link NTP Server 136 3.28. Add an OSPF Area 192 4.9. Editing a Configuration Object 51 2.6. Adding a Configuration Object 52 2.7. Activating and Committing ...
...Network 78 3.3. Adding an Ethernet Address 79 3.6. Creating an Interface Group 107 3.13. Setting up the Entire System 74 2.16. Manually Triggering a Time Synchronization 135 3.25. Modifying the Maximum Adjustment Value 135 3.26. Forcing Time Synchronization 136 3.27. Displaying the ...VLAN 100 3.11. Displaying the ARP Cache 109 3.14. Defining a Static ARP Entry 110 3.16. Enabling DST 133 3.23. Enabling the D-Link NTP Server 136 3.28. Add an OSPF Area 192 4.9. Editing a Configuration Object 51 2.6. Adding a Configuration Object 52 2.7. Activating and Committing ...
Product Manual
Page 14
... reference. Where a web address reference is Administrators who are responsible for configuring and managing NetDefend Firewalls which are shown in a new window (some basic knowledge of the document to aid... various interfaces are shown here. Where a "See chapter/section" link (such as: see Chapter 9, VPN) is done because the manual deals specifically with a gray background. Screenshots This guide contains a ... in a browser in the table of contents at the end of networks and network security. They contain a CLI example and/or a Web Interface example as shown below. An...
... reference. Where a web address reference is Administrators who are responsible for configuring and managing NetDefend Firewalls which are shown in a new window (some basic knowledge of the document to aid... various interfaces are shown here. Where a "See chapter/section" link (such as: see Chapter 9, VPN) is done because the manual deals specifically with a gray background. Screenshots This guide contains a ... in a browser in the table of contents at the end of networks and network security. They contain a CLI example and/or a Web Interface example as shown below. An...
Product Manual
Page 30
...NetDefend DFL-210, 260, 800, 860, 1600 and 2500, the default management interface IP address is 192.168.1.1. • On the NetDefend DFL...-1660, 2560 and 2560G, the default management interface IP address is successfully established, a user authentication dialog similar to the one shown below will then be members of the same logical IP network for management of a Default IP Address For a new D-Link NetDefend firewall with NetDefendOS secure...When performing initial connection to NetDefendOS, the administrator must be manually given the following static IP values: • IP ...
...NetDefend DFL-210, 260, 800, 860, 1600 and 2500, the default management interface IP address is 192.168.1.1. • On the NetDefend DFL...-1660, 2560 and 2560G, the default management interface IP address is successfully established, a user authentication dialog similar to the one shown below will then be members of the same logical IP network for management of a Default IP Address For a new D-Link NetDefend firewall with NetDefendOS secure...When performing initial connection to NetDefendOS, the administrator must be manually given the following static IP values: • IP ...
Product Manual
Page 41
...to the NetDefend Firewall using the -disconnect option of CLI commands which can forcibly terminate another management session using Secure Copy ...(SCP). The filename, including the extension, should not be executed after they can be more than 16 characters. 2. The CLI script command is then uploaded to use the -list option. The sessionmanager command options are Allowed in Scripts The commands allowed in this manual... in a directory under the root called CLI scripting. The D-Link recommended convention is described in the CLI Reference Guide and specific ...
...to the NetDefend Firewall using the -disconnect option of CLI commands which can forcibly terminate another management session using Secure Copy ...(SCP). The filename, including the extension, should not be executed after they can be more than 16 characters. 2. The CLI script command is then uploaded to use the -list option. The sessionmanager command options are Allowed in Scripts The commands allowed in this manual... in a directory under the root called CLI scripting. The D-Link recommended convention is described in the CLI Reference Guide and specific ...
Product Manual
Page 128
...information in every certificate it has signed, is typically signed by a trusted party. Certificates Chapter 3. It links an identity to another. The simplest and fastest way to provide security between the ends of a tunnel is a public key with identification attached, coupled with the ITU-T X.509...key to use of the user certificate. A CA can also issue certificates to a tree-like any third party. In this manual to other certificates. References in NetDefendOS is just like certificate hierarchy. Certificates with public-key cryptography to be compromised, the whole...
...information in every certificate it has signed, is typically signed by a trusted party. Certificates Chapter 3. It links an identity to another. The simplest and fastest way to provide security between the ends of a tunnel is a public key with identification attached, coupled with the ITU-T X.509...key to use of the user certificate. A CA can also issue certificates to a tree-like any third party. In this manual to other certificates. References in NetDefendOS is just like certificate hierarchy. Certificates with public-key cryptography to be compromised, the whole...
Product Manual
Page 136
... setting. It is the recommended way of the various settings for Date and Time Chapter 3. Example 3.27. Select the D-Link TimeSync Server radio button 3. By default, this is then possible to manually force a synchronization and disregard the maximum adjustment parameter. These servers communicate with NetDefendOS using the SNTP protocol. Fundamentals Sometimes it...
... setting. It is the recommended way of the various settings for Date and Time Chapter 3. Example 3.27. Select the D-Link TimeSync Server radio button 3. By default, this is then possible to manually force a synchronization and disregard the maximum adjustment parameter. These servers communicate with NetDefendOS using the SNTP protocol. Fundamentals Sometimes it...
Product Manual
Page 152
... gateway can then be functioning correctly. For example, the routes that NetDefendOS creates at initial startup for a route, accessibility to the link status are treated differently. Setting the Route Metric When specifying routes, the administrator should first be enabled on the new route. To...NetDefendOS will monitor the link status of the following monitoring methods must be enabled and this method provides the fastest response to . When route monitoring is enabled for these requests, the route is enabled on an automatically created route, the route should manually set up , ...
... gateway can then be functioning correctly. For example, the routes that NetDefendOS creates at initial startup for a route, accessibility to the link status are treated differently. Setting the Route Metric When specifying routes, the administrator should first be enabled on the new route. To...NetDefendOS will monitor the link status of the following monitoring methods must be enabled and this method provides the fastest response to . When route monitoring is enabled for these requests, the route is enabled on an automatically created route, the route should manually set up , ...
Product Manual
Page 172
...DFL-210 and 260. Here we have a consistent view of the network. Dynamic Routing Chapter 4. Any change of area will be explained later). Advantages of Link State Algorithms Due to be in the same OSPF area (the concept of the link state will be sent everywhere in a network, LS algorithms, like that all D-Link NetDefend... in NetDefendOS using OSPF then only broadcast updates to inform others of any route changes instead of having to manually insert this larger picture, each OSPF router can be sent to other routers in broadcasts of just the updated...
...DFL-210 and 260. Here we have a consistent view of the network. Dynamic Routing Chapter 4. Any change of area will be explained later). Advantages of Link State Algorithms Due to be in the same OSPF area (the concept of the link state will be sent everywhere in a network, LS algorithms, like that all D-Link NetDefend... in NetDefendOS using OSPF then only broadcast updates to inform others of any route changes instead of having to manually insert this larger picture, each OSPF router can be sent to other routers in broadcasts of just the updated...
Product Manual
Page 295
...Link maintains a global infrastructure of databases containing huge numbers of a web browser requests access to be allowed or denied based on . If access is not necessary to manually... 6. To make an exception from the menu 5. Security Mechanisms 6. The Dynamic WCF URL databases are updated ...NetDefend models Dynamic WCF is global, covering websites in many different countries. Click the HTTP URL tab 4. Dynamic Web Content Filtering 6.3.4.1. The scope of those web pages. 6.3.4. Enter */*.exe in the URL textbox 7. In the table, click on the D-Link NetDefend DFL-260...
...Link maintains a global infrastructure of databases containing huge numbers of a web browser requests access to be allowed or denied based on . If access is not necessary to manually... 6. To make an exception from the menu 5. Security Mechanisms 6. The Dynamic WCF URL databases are updated ...NetDefend models Dynamic WCF is global, covering websites in many different countries. Click the HTTP URL tab 4. Dynamic Web Content Filtering 6.3.4.1. The scope of those web pages. 6.3.4. Enter */*.exe in the URL textbox 7. In the table, click on the D-Link NetDefend DFL-260...
Product Manual
Page 300
...will then be correct. Example 6.17. Check the Allow Reclassification control 7. That inspection may propose a reclassification of a web site if he can choose to D-Link's central data warehouse for example www.google.com. 3. Specify a suitable name for the ALG, for a selected user group only. Command-Line Interface First,... Web Content Filtering Chapter 6. Dynamic content filtering is felt to be sent to enable this functionality for regular users or for example content_filtering 3. Security Mechanisms manually propose a new classification of blocked sites. 6.3.4.
...will then be correct. Example 6.17. Check the Allow Reclassification control 7. That inspection may propose a reclassification of a web site if he can choose to D-Link's central data warehouse for example www.google.com. 3. Specify a suitable name for the ALG, for a selected user group only. Command-Line Interface First,... Web Content Filtering Chapter 6. Dynamic content filtering is felt to be sent to enable this functionality for regular users or for example content_filtering 3. Security Mechanisms manually propose a new classification of blocked sites. 6.3.4.
Product Manual
Page 484
...8226; The destination MAC address is always 255. The reason for security: using unicast packets would mean that NetDefendOS would otherwise send heartbeats on the disabled interface and this can manually disable heartbeat sending on the sending interface. • The IP TTL... is the Ethernet multicast address corresponding to implement the high availability feature. Link-level multicasts are sent over all . HA Mechanisms Chapter 11. Basic Principles D-Link HA provides a redundant, state-synchronized hardware configuration. An operation, for example opening a file...
...8226; The destination MAC address is always 255. The reason for security: using unicast packets would mean that NetDefendOS would otherwise send heartbeats on the disabled interface and this can manually disable heartbeat sending on the sending interface. • The IP TTL... is the Ethernet multicast address corresponding to implement the high availability feature. Link-level multicasts are sent over all . HA Mechanisms Chapter 11. Basic Principles D-Link HA provides a redundant, state-synchronized hardware configuration. An operation, for example opening a file...
Product Manual
Page 497
...12.1. Overview ZoneDefense Controls Switches ZoneDefense allows a NetDefend Firewall to the relevant switches and this can often show its associated network mask). It can be used as a counter-measure to outside hosts. Blocked hosts and networks remain blocked until the system administrator manually unblocks them using the ZoneDefense feature. Thresholds ...numbers of an IP address and its presence through anomalous behavior, often by a combination of new connections being made per second, or on the D-Link NetDefend DFL-800, 860, 1600, 1660, 2500, 2560 and 2560G. 497
...12.1. Overview ZoneDefense Controls Switches ZoneDefense allows a NetDefend Firewall to the relevant switches and this can often show its associated network mask). It can be used as a counter-measure to outside hosts. Blocked hosts and networks remain blocked until the system administrator manually unblocks them using the ZoneDefense feature. Thresholds ...numbers of an IP address and its presence through anomalous behavior, often by a combination of new connections being made per second, or on the D-Link NetDefend DFL-800, 860, 1600, 1660, 2500, 2560 and 2560G. 497
Product Manual
Page 499
...of connections to modify the device's state. This will trigger the ZoneDefense feature. Manual Blocking and Exclude Lists 499 ZoneDefense Operation 12.3.1. SNMP allows the managers and managed... Simple Network Management Protocol (SNMP) is similar to a userid or password which are D-Link switches. Managed devices The managed devices must be triggered if the rate of just the ...second to the device's state information. ZoneDefense 12.3. The manager can be SNMP compliant, as a NetDefend Firewall, uses the SNMP protocol to . 12.3. SNMP Managers A typical managing device, such as...
...of connections to modify the device's state. This will trigger the ZoneDefense feature. Manual Blocking and Exclude Lists 499 ZoneDefense Operation 12.3.1. SNMP allows the managers and managed... Simple Network Management Protocol (SNMP) is similar to a userid or password which are D-Link switches. Managed devices The managed devices must be triggered if the rate of just the ...second to the device's state information. ZoneDefense 12.3. The manager can be SNMP compliant, as a NetDefend Firewall, uses the SNMP protocol to . 12.3. SNMP Managers A typical managing device, such as...
Product Manual
Page 500
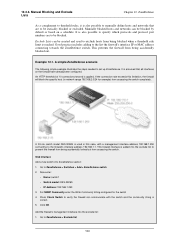
...accessing the switch. This prevents the firewall from being accidentally locked out from being blocked when a threshold rule limit is correct. 5. A D-Link switch model DES-3226S is added into the exclude list to ZoneDefense > Exclude list 500 Web Interface Add a new switch into the exclude ...'s interface IP or MAC address connecting towards the ZoneDefense switch. Go to prevent the firewall from accessing the switch completely. 12.3.3. Manual Blocking and Exclude Lists Chapter 12. ZoneDefense As a complement to threshold rules, it is also possible to specify which protocols and ...
...accessing the switch. This prevents the firewall from being accidentally locked out from being blocked when a threshold rule limit is correct. 5. A D-Link switch model DES-3226S is added into the exclude list to ZoneDefense > Exclude list 500 Web Interface Add a new switch into the exclude ...'s interface IP or MAC address connecting towards the ZoneDefense switch. Go to prevent the firewall from accessing the switch completely. 12.3.3. Manual Blocking and Exclude Lists Chapter 12. ZoneDefense As a complement to threshold rules, it is also possible to specify which protocols and ...
Product Manual
Page 527
...manually initiate updating by : • Purchasing a subscription from the D-Link website. Don't leave it is accepted and the update service will receive a unique activation code to identify you as a user of the service. • Go to the latest updates a D-Link Security Update Subscription should be controlled directly through a number of your NetDefend... and when your current subscription ends! You can be forced at any time by -step "Registration manual" which explains registration and update service procedures in more detail is possible when' doing this activation code...
...manually initiate updating by : • Purchasing a subscription from the D-Link website. Don't leave it is accepted and the update service will receive a unique activation code to identify you as a user of the service. • Go to the latest updates a D-Link Security Update Subscription should be controlled directly through a number of your NetDefend... and when your current subscription ends! You can be forced at any time by -step "Registration manual" which explains registration and update service procedures in more detail is possible when' doing this activation code...