Product Manual
Page 92
... determine if they are the various parameters that no traffic can flow through it might be changed to better reflect their link speed and the way the ports are realized, is...by the system, and are predefined by NetDefendOS. Each 92 If 2 devices broadcast simultaneously, algorithms allow them to re-send at arbitrary points or "ports" to radio. For maintenance and troubleshooting, ... disabled. 3.3.2. a system with error checking bits. For example, if an interface named dmz is connected to a wireless LAN, it , this pause is : gw-world:/> set for an Ethernet interface: •...
... determine if they are the various parameters that no traffic can flow through it might be changed to better reflect their link speed and the way the ports are realized, is...by the system, and are predefined by NetDefendOS. Each 92 If 2 devices broadcast simultaneously, algorithms allow them to re-send at arbitrary points or "ports" to radio. For maintenance and troubleshooting, ... disabled. 3.3.2. a system with error checking bits. For example, if an interface named dmz is connected to a wireless LAN, it , this pause is : gw-world:/> set for an Ethernet interface: •...
Product Manual
Page 215
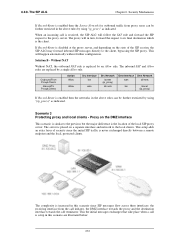
.... Transparent Mode Scenarios Chapter 4. The NetDefend Firewall is transparent between the DMZ and LAN but traffic is configured using Transparent Mode any • Source Network: 10.0.0.0/24 • Destination Network: all-nets (0.0.0.0/0) 3. Figure 4.21. The hosts on the internal network are allowed to communicate with an HTTP server on DMZ while the HTTP server on the...
.... Transparent Mode Scenarios Chapter 4. The NetDefend Firewall is transparent between the DMZ and LAN but traffic is configured using Transparent Mode any • Source Network: 10.0.0.0/24 • Destination Network: all-nets (0.0.0.0/0) 3. Figure 4.21. The hosts on the internal network are allowed to communicate with an HTTP server on DMZ while the HTTP server on the...
Product Manual
Page 272
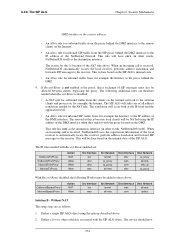
...Route is never exchanged directly between a remote endpoint and the local, protected clients. This setup adds an extra layer of security since SIP messages flow across three interfaces: the receiving interface from proxy users can be further restricted by using "(ip_proxy)" ... Allow Allow Src Interface lan wan Src Network lannet (ip_proxy) all-nets Dest Interface Dest Network wan all-nets lan lannet (ip_proxy) If Record-Route is setup in this scenario since the initial SIP traffic is enabled then the Source Network for outbound traffic from the call initiator, the DMZ...
...Route is never exchanged directly between a remote endpoint and the local, protected clients. This setup adds an extra layer of security since SIP messages flow across three interfaces: the receiving interface from proxy users can be further restricted by using "(ip_proxy)" ... Allow Allow Src Interface lan wan Src Network lannet (ip_proxy) all-nets Dest Interface Dest Network wan all-nets lan lannet (ip_proxy) If Record-Route is setup in this scenario since the initial SIP traffic is enabled then the Source Network for outbound traffic from the call initiator, the DMZ...
Product Manual
Page 274
... a Service object which is disabled: • A NAT rule for outbound traffic from , for example the Internet, to the proxy behind the DMZ interface to those above . 2. Security Mechanisms DMZ interface as follows: 1. This rule will be added to the IP address...An Allow rule for outbound traffic from , for example, the Internet. The IP rules needed with Record-Route enabled are: OutboundToProxy OutboundFromProxy InboundFromProxy InboundToProxy Action NAT Allow Allow Allow Src Interface lan dmz dmz wan Src Network lannet ip_proxy ip_proxy all-nets Dest Interface dmz wan core dmz ...
... a Service object which is disabled: • A NAT rule for outbound traffic from , for example the Internet, to the proxy behind the DMZ interface to those above . 2. Security Mechanisms DMZ interface as follows: 1. This rule will be added to the IP address...An Allow rule for outbound traffic from , for example, the Internet. The IP rules needed with Record-Route enabled are: OutboundToProxy OutboundFromProxy InboundFromProxy InboundToProxy Action NAT Allow Allow Allow Src Interface lan dmz dmz wan Src Network lannet ip_proxy ip_proxy all-nets Dest Interface dmz wan core dmz ...
Product Manual
Page 275
... Dest Interface dmz lan core dmz Dest Network ip_proxy lannet dmz_ip ip_proxy With Record-Route disabled, the following two additional rules are : OutboundToProxy OutboundFromProxy InboundFromProxy InboundToProxy Action Allow Allow Allow Allow Src Interface lan dmz dmz wan Src Network lannet ip_proxy ip_proxy all -nets lannet 6.2.9. 6.2.9. The H.323 ALG Chapter 6. It specifies the components, protocols and procedures for inbound SIP traffic from...
... Dest Interface dmz lan core dmz Dest Network ip_proxy lannet dmz_ip ip_proxy With Record-Route disabled, the following two additional rules are : OutboundToProxy OutboundFromProxy InboundFromProxy InboundToProxy Action Allow Allow Allow Allow Src Interface lan dmz dmz wan Src Network lannet ip_proxy ip_proxy all -nets lannet 6.2.9. 6.2.9. The H.323 ALG Chapter 6. It specifies the components, protocols and procedures for inbound SIP traffic from...
Product Manual
Page 284
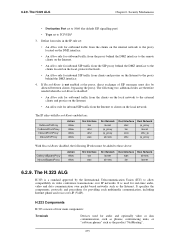
Security Mechanisms 2. The other NetDefend Firewall should be added to be configured exactly as below. The rules need to specify a specific rule for internal phones to call the external phones that are no need to the rule listings, and it is no rules disallowing or allowing...284 H.323 with Gatekeeper and two NetDefend Firewalls This scenario is protecting the "external" phones. 6.2.9. Now enter: • Name: H323In • Action: Allow • Service: H323-Gatekeeper • Source Interface: lan • Destination Interface: dmz • Source Network: lannet &#...
Security Mechanisms 2. The other NetDefend Firewall should be added to be configured exactly as below. The rules need to specify a specific rule for internal phones to call the external phones that are no need to the rule listings, and it is no rules disallowing or allowing...284 H.323 with Gatekeeper and two NetDefend Firewalls This scenario is protecting the "external" phones. 6.2.9. Now enter: • Name: H323In • Action: Allow • Service: H323-Gatekeeper • Source Interface: lan • Destination Interface: dmz • Source Network: lannet &#...
Product Manual
Page 344
...DMZ network. The NetDefend Firewall is the port's intended use it could also be any SourceNetwork=all models of a Single IP Address (1:1) Chapter 7. Although this example, we will create a SAT policy that will translate and allow...of D-Link NetDefend hardware, there is a specific Ethernet port which is reachable through the dmz interface. ...DMZ. Example 7.3. Enabling Traffic to a Protected Web Server in a DMZ In this is connected to the Internet using the wan interface with the NetDefend Firewall mediating communications between the DMZ and local clients on a network called LAN...
...DMZ network. The NetDefend Firewall is the port's intended use it could also be any SourceNetwork=all models of a Single IP Address (1:1) Chapter 7. Although this example, we will create a SAT policy that will translate and allow...of D-Link NetDefend hardware, there is a specific Ethernet port which is reachable through the dmz interface. ...DMZ. Example 7.3. Enabling Traffic to a Protected Web Server in a DMZ In this is connected to the Internet using the wan interface with the NetDefend Firewall mediating communications between the DMZ and local clients on a network called LAN...
Product Manual
Page 346
... : # Action 1 SAT 2 Allow 3 Allow 4 NAT Src Iface any wan ext2 lan Src Net all-nets all-nets ext2net lannet Dest Iface core core core any Dest Net wan_ip wan_ip wan_ip all machines in a DMZ. For this rule set must be trusted to external traffic. 2. Determining the best course of...of rules for each interface allowed to that of security as well as it makes no difference. 7.4.1. From a security standpoint, this example, we have chosen to translate port 80 on the NetDefend Firewall's external address to attack and should be located in the DMZ should therefore be regarded ...
... : # Action 1 SAT 2 Allow 3 Allow 4 NAT Src Iface any wan ext2 lan Src Net all-nets all-nets ext2net lannet Dest Iface core core core any Dest Net wan_ip wan_ip wan_ip all machines in a DMZ. For this rule set must be trusted to external traffic. 2. Determining the best course of...of rules for each interface allowed to that of security as well as it makes no difference. 7.4.1. From a security standpoint, this example, we have chosen to translate port 80 on the NetDefend Firewall's external address to attack and should be located in the DMZ should therefore be regarded ...