Wireless Security
Page 1
... Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract:... security layers to the pipe. To put the subject of wirelessenabled productivity to take advantage of the benefits of wireless security into context, the paper is discussed. This paper looks at astonishing rates to gain and maintain a competitive...
... Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract:... security layers to the pipe. To put the subject of wirelessenabled productivity to take advantage of the benefits of wireless security into context, the paper is discussed. This paper looks at astonishing rates to gain and maintain a competitive...
Wireless Security
Page 2
... Technologies Group, L.P. in the documentation accompanying such products. The limited warranties for Compaq products are trademarks of product quality or correctness, nor does it ensure compliance with any federal, state or local requirements. Wireless Security White Paper 2 Notice The information in this publication is subject to change without notice and is not...
... Technologies Group, L.P. in the documentation accompanying such products. The limited warranties for Compaq products are trademarks of product quality or correctness, nor does it ensure compliance with any federal, state or local requirements. Wireless Security White Paper 2 Notice The information in this publication is subject to change without notice and is not...
Wireless Security
Page 3
...access from the outset that no security whatsoever. To put the appropriate measures in place. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to take advantage of the benefits of access is discussed. Security in ... has presented users of the vulnerabilities can be adequate to address security in wirelessly enabled networks. This paper will be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. Many of access devices and corporations with security designed...
...access from the outset that no security whatsoever. To put the appropriate measures in place. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to take advantage of the benefits of access is discussed. Security in ... has presented users of the vulnerabilities can be adequate to address security in wirelessly enabled networks. This paper will be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. Many of access devices and corporations with security designed...
Wireless Security
Page 4
... transaction, as well as it cannot be abused or used to hide criminal activity. the process of security as persons seeking access to wireless networks are who have permission to do so can be easy to use, while making sure it applies to digital information, are :...user's access device (the client) across the "pipe" to address those issues. Privacy is supported by digital signatures. • Integrity - A wireless mobile business solution should be managed. The next section describes aspects of action. Security and the Pipe A pipe is gained to the wired transmission...
... transaction, as well as it cannot be abused or used to hide criminal activity. the process of security as persons seeking access to wireless networks are who have permission to do so can be easy to use, while making sure it applies to digital information, are :...user's access device (the client) across the "pipe" to address those issues. Privacy is supported by digital signatures. • Integrity - A wireless mobile business solution should be managed. The next section describes aspects of action. Security and the Pipe A pipe is gained to the wired transmission...
Wireless Security
Page 5
... 1: The Network Pipe The vertical yellow lines in this paper, since securing data from one .) Figure 1 illustrates the pipe. Wireless Security White Paper 5 - (This aspect of security is not covered in Figure 1 represent the pivotal points of data transfer....security models. The horizontal lines represent data traveling from unauthorized access behind the firewall is not a wireless security concern, but a wired one place to the next either wired or wirelessly. Notebook computers are used for online connectivity, Internet surfing, organization of information such as contact lists ...
... 1: The Network Pipe The vertical yellow lines in this paper, since securing data from one .) Figure 1 illustrates the pipe. Wireless Security White Paper 5 - (This aspect of security is not covered in Figure 1 represent the pivotal points of data transfer....security models. The horizontal lines represent data traveling from unauthorized access behind the firewall is not a wireless security concern, but a wired one place to the next either wired or wirelessly. Notebook computers are used for online connectivity, Internet surfing, organization of information such as contact lists ...
Wireless Security
Page 6
... smaller screens of handheld devices reduce this exposure is lost or stolen, unauthorized persons may view confidential information stored on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. If a device is to exercise vigilance and common sense. Often firewalls are used for .... corporate networks by workers who are protected by instituting measures to protect the hardware and the data that the devices hold. Wireless Security White Paper 6 Moreover, workers are precautions that mobile device users can be accomplished when both access devices and portals ...
... smaller screens of handheld devices reduce this exposure is lost or stolen, unauthorized persons may view confidential information stored on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. If a device is to exercise vigilance and common sense. Often firewalls are used for .... corporate networks by workers who are protected by instituting measures to protect the hardware and the data that the devices hold. Wireless Security White Paper 6 Moreover, workers are precautions that mobile device users can be accomplished when both access devices and portals ...
Wireless Security
Page 7
...piece of hardware on mobile devices, it raises the level of risk that associate multiple letters with each key require repeated presses to a wireless network, even with the card. Whereas a stolen smart card can be used just like a stolen password, the association with a ...convenient given the cumbersome nature of password entry on which passwords, private keys, digital certificates, and cryptographic algorithms can be stored. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to...
...piece of hardware on mobile devices, it raises the level of risk that associate multiple letters with each key require repeated presses to a wireless network, even with the card. Whereas a stolen smart card can be used just like a stolen password, the association with a ...convenient given the cumbersome nature of password entry on which passwords, private keys, digital certificates, and cryptographic algorithms can be stored. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to...
Wireless Security
Page 8
...smart card is one of the best ways to improve security at least two types of Helsinki, Finland provides such encryption for Compaq Armada and Evo notebook computers. The information then goes through some complex algorithms to convert the image into the hands of strangers.... card) • Who the user is then encrypted and stored within the network. This map of a device's legitimate user. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint Identification Technology (FIT) for the commercial market.
...smart card is one of the best ways to improve security at least two types of Helsinki, Finland provides such encryption for Compaq Armada and Evo notebook computers. The information then goes through some complex algorithms to convert the image into the hands of strangers.... card) • Who the user is then encrypted and stored within the network. This map of a device's legitimate user. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint Identification Technology (FIT) for the commercial market.
Wireless Security
Page 9
...user's login password combines the SecurID code with the operations of an external authenticator device to the Internet, especially through a wireless VPN connection. For example, they roam. The SecurID external authenticator may be defined • ActiveSync protected by the same ... FileCrypto for PocketPC are the following: • Encrypts documents in the pipe, after wireless access devices, is a range of wireless connectivity technologies. SecurID SecurID is forgotten Compaq iPAQ Pocket PC's ship with the server. Software-based firewalls are used at different times...
...user's login password combines the SecurID code with the operations of an external authenticator device to the Internet, especially through a wireless VPN connection. For example, they roam. The SecurID external authenticator may be defined • ActiveSync protected by the same ... FileCrypto for PocketPC are the following: • Encrypts documents in the pipe, after wireless access devices, is a range of wireless connectivity technologies. SecurID SecurID is forgotten Compaq iPAQ Pocket PC's ship with the server. Software-based firewalls are used at different times...
Wireless Security
Page 10
...front of each technology are , such as an extension or alternative to transmit data among its nodes. Figure 2 illustrates a WLAN. Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere at any ...follows and detailed papers that uses high-frequency radio waves rather than wires to a wired LAN within a building or campus. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from a cell phone to a handheld to a ...
...front of each technology are , such as an extension or alternative to transmit data among its nodes. Figure 2 illustrates a WLAN. Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere at any ...follows and detailed papers that uses high-frequency radio waves rather than wires to a wired LAN within a building or campus. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from a cell phone to a handheld to a ...
Wireless Security
Page 11
...-area networks (WWANs) have been used there. GSM is the most widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. Japan's NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. The official names for CDMA... IS-95 and IS-136, respectively. The Global System for point-to peripheral devices such as printers or other personal devices. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. A WPAN permits personal devices such as handheld PCs to connect...
...-area networks (WWANs) have been used there. GSM is the most widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. Japan's NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. The official names for CDMA... IS-95 and IS-136, respectively. The Global System for point-to peripheral devices such as printers or other personal devices. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. A WPAN permits personal devices such as handheld PCs to connect...
Wireless Security
Page 12
... turnkey solutions: clients with InfoWave. Compaq offers an optimized MS Exchange e-mail solution with enabling technologies, airtime provided by carriers, area network coverage, and optimized features. Figure 4 illustrates a WWAN. Figure 4: Wireless Wide-area Network Whether it is difficult to control how far... theft of security) are available now. Gaining access to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Wireless WAN via CDPD, for example, provides packet-switched connections to corporate passwords, logging on the same frequency and with InfoWave....
... turnkey solutions: clients with InfoWave. Compaq offers an optimized MS Exchange e-mail solution with enabling technologies, airtime provided by carriers, area network coverage, and optimized features. Figure 4 illustrates a WWAN. Figure 4: Wireless Wide-area Network Whether it is difficult to control how far... theft of security) are available now. Gaining access to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Wireless WAN via CDPD, for example, provides packet-switched connections to corporate passwords, logging on the same frequency and with InfoWave....
Wireless Security
Page 13
... that help forestall eavesdropping and its concomitant ills, the information that travels over a wireless network must travel over public highways and suffer the potential for the wireless exchange of information over the network. Encryption and tunneling effectively "hide" information as commented...most secure due to the heavier underlying encryption native to the network technology; Smaller companies have PKI support for a wireless network. Wireless Security White Paper 13 The discussion that follows concentrates on the segment of the network pipe in which public key...
... that help forestall eavesdropping and its concomitant ills, the information that travels over a wireless network must travel over public highways and suffer the potential for the wireless exchange of information over the network. Encryption and tunneling effectively "hide" information as commented...most secure due to the heavier underlying encryption native to the network technology; Smaller companies have PKI support for a wireless network. Wireless Security White Paper 13 The discussion that follows concentrates on the segment of the network pipe in which public key...
Wireless Security
Page 14
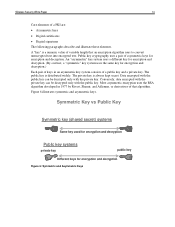
An "asymmetric" key system uses a different key for encryption and decryption. (By contrast, a "symmetric" key system uses the same key for encryption and decryption. Wireless Security White Paper 14 Core elements of variable length that algorithm. The public key is always kept secret. Most asymmetric encryption uses the RSA algorithm ...
An "asymmetric" key system uses a different key for encryption and decryption. (By contrast, a "symmetric" key system uses the same key for encryption and decryption. Wireless Security White Paper 14 Core elements of variable length that algorithm. The public key is always kept secret. Most asymmetric encryption uses the RSA algorithm ...
Wireless Security
Page 15
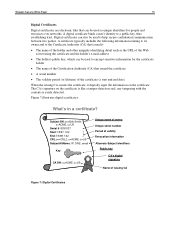
... used to encrypt sensitive information for people and resources over networks. Digital certificates can also be used to help secure confidential communication between two parties. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used as the URL of issuing CA Figure 7: Digital Certificates A certificate...
... used to encrypt sensitive information for people and resources over networks. Digital certificates can also be used to help secure confidential communication between two parties. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used as the URL of issuing CA Figure 7: Digital Certificates A certificate...
Wireless Security
Page 16
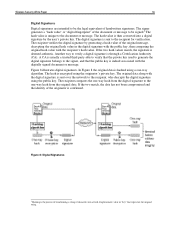
... used to generate the digital signature belongs to the signer, and that represents the original string. Another way to verify a digital signature is deemed authentic. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. If the...
... used to generate the digital signature belongs to the signer, and that represents the original string. Another way to verify a digital signature is deemed authentic. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. If the...
Wireless Security
Page 17
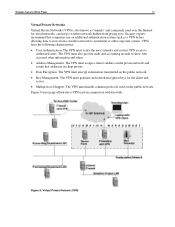
...common protocols used on the public network. The VPN must assign a client's address on the public network. • Key Management. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from ...information and when. • Address Management. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. The VPN must also provide audit and accounting records to authorized users. Figure...
...common protocols used on the public network. The VPN must assign a client's address on the public network. • Key Management. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from ...information and when. • Address Management. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. The VPN must also provide audit and accounting records to authorized users. Figure...
Wireless Security
Page 18
... offers strong encryption, but leaves the header untouched. A further difficulty is still likely to be limited in proposing IPSec as a symmetric key. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP Network Server... providers to build Virtual Private Dial-Up Networks (VPDNs). If it runs on because of the high CPU overhead associated with wireless networks in its own lines for remote user access through dial-up connection to -Point Tunneling Protocol (PPTP) from Microsoft, ...
... offers strong encryption, but leaves the header untouched. A further difficulty is still likely to be limited in proposing IPSec as a symmetric key. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP Network Server... providers to build Virtual Private Dial-Up Networks (VPDNs). If it runs on because of the high CPU overhead associated with wireless networks in its own lines for remote user access through dial-up connection to -Point Tunneling Protocol (PPTP) from Microsoft, ...
Wireless Security
Page 19
Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to-end ... and the subscriber identification key. When the user makes a connection with established need-to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. Nonetheless, GSM contains three secret algorithms that secrecy is connected to an authentication ...
Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to-end ... and the subscriber identification key. When the user makes a connection with established need-to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. Nonetheless, GSM contains three secret algorithms that secrecy is connected to an authentication ...
Wireless Security
Page 20
... the IS-95 standard of CDMA uses a transmission technique called "spread spectrum" that was developed by means of digital certificates. Wireless Transport Layer Security (WTLS) is authenticated; • Class 2 authentication authenticates only the server; • Class 3 authentication requires...to provide adequate authentication, data integrity, and privacy protection. However, their limited processing power, memory capacity, and bandwidth. Wireless Security White Paper 20 Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) use the Cellular Message ...
... the IS-95 standard of CDMA uses a transmission technique called "spread spectrum" that was developed by means of digital certificates. Wireless Transport Layer Security (WTLS) is authenticated; • Class 2 authentication authenticates only the server; • Class 3 authentication requires...to provide adequate authentication, data integrity, and privacy protection. However, their limited processing power, memory capacity, and bandwidth. Wireless Security White Paper 20 Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) use the Cellular Message ...