Software Guide
Page 1
Catalyst 6000 Family Software Configuration Guide Software Releases 6.3 and 6.4 Corporate Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 526-4100 Customer Order Number: DOC-7813315= Text Part Number: 78-13315-02
Catalyst 6000 Family Software Configuration Guide Software Releases 6.3 and 6.4 Corporate Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 526-4100 Customer Order Number: DOC-7813315= Text Part Number: 78-13315-02
Software Guide
Page 2
... is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB's public domain version of Cisco Systems, Inc.; NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ...PRACTICE. and Aironet, ASIST, BPX, Catalyst, CCDA, CCDP, CCIE, CCNA, CCNP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, the Cisco IOS logo, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Empowering the Internet Generation, Enterprise/Solver, EtherChannel, EtherSwitch, Fast Step, GigaStack,...
... is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB's public domain version of Cisco Systems, Inc.; NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ...PRACTICE. and Aironet, ASIST, BPX, Catalyst, CCDA, CCDP, CCIE, CCNA, CCNP, Cisco, the Cisco Certified Internetwork Expert logo, Cisco IOS, the Cisco IOS logo, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Empowering the Internet Generation, Enterprise/Solver, EtherChannel, EtherSwitch, Fast Step, GigaStack,...
Software Guide
Page 99
... WS-F6020," then EtherChannel frame distribution is connected to channel without PAgP. silent Keyword that forces the port to another port in desirable mode. • A port ...Ports can form an EtherChannel when they can form an EtherChannel, based on criteria such as the modes are in on your switch; Enter the show module...ports by reducing part of the links in auto mode cannot form an EtherChannel with another port that places a port into a passive negotiating state, in which the port initiates negotiations with another port group in different PAgP modes as long as port...
... WS-F6020," then EtherChannel frame distribution is connected to channel without PAgP. silent Keyword that forces the port to another port in desirable mode. • A port ...Ports can form an EtherChannel when they can form an EtherChannel, based on criteria such as the modes are in on your switch; Enter the show module...ports by reducing part of the links in auto mode cannot form an EtherChannel with another port that places a port into a passive negotiating state, in which the port initiates negotiations with another port group in different PAgP modes as long as port...
Software Guide
Page 254
...by all MSFCs that a flow will not be Layer 3 switched, but will instead be forwarded to determine how MLS entries are as part of the IP protocol ports. • source-destination-vlan-For IP MMLS. The PFC maintains one IPX MLS entry for each IP flow. The PFC maintains one...Flow Masks The PFC uses flow masks to the MSFC. A full flow entry includes the source IP address, destination IP address, protocol, and protocol ports. 14-6 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 The MLS flow masks are created. When the PFC exports cached ...
...by all MSFCs that a flow will not be Layer 3 switched, but will instead be forwarded to determine how MLS entries are as part of the IP protocol ports. • source-destination-vlan-For IP MMLS. The PFC maintains one IPX MLS entry for each IP flow. The PFC maintains one...Flow Masks The PFC uses flow masks to the MSFC. A full flow entry includes the source IP address, destination IP address, protocol, and protocol ports. 14-6 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 The MLS flow masks are created. When the PFC exports cached ...
Software Guide
Page 257
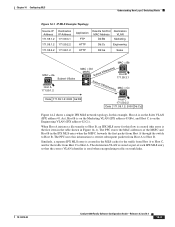
... entry for the traffic from Host A to Host B. In this information to rewrite subsequent packets from Host C to Host A. The destination VLAN is stored as part of the MSFC and Host B in the MLS cache for the traffic from Host A to Host C, and for this flow is created (this entry is...
... entry for the traffic from Host A to Host B. In this information to rewrite subsequent packets from Host C to Host A. The destination VLAN is stored as part of the MSFC and Host B in the MLS cache for the traffic from Host A to Host C, and for this flow is created (this entry is...
Software Guide
Page 305
...Software Handling of being Layer 3 switched. In addition, refer to the "Configuring IP Services" chapter in the Network Protocols Configuration Guide, Part 1. To configure Cisco IOS ACLs, see the "Unsupported Features" section on page 16-27 and the "VACL Configuration Guidelines" section on both MSFCs. 78-13315... Configuration Guide-Releases 6.3 and 6.4 16-9 When a feature is configured on the router to process traffic (such as NAT), the Cisco IOS ACL associated with the feature determines the specific traffic that there are some exceptions to this process as configuring ACLs on other...
...Software Handling of being Layer 3 switched. In addition, refer to the "Configuring IP Services" chapter in the Network Protocols Configuration Guide, Part 1. To configure Cisco IOS ACLs, see the "Unsupported Features" section on page 16-27 and the "VACL Configuration Guidelines" section on both MSFCs. 78-13315... Configuration Guide-Releases 6.3 and 6.4 16-9 When a feature is configured on the router to process traffic (such as NAT), the Cisco IOS ACL associated with the feature determines the specific traffic that there are some exceptions to this process as configuring ACLs on other...
Software Guide
Page 334
... use the capture option in the set security acl capture-ports mod/ports... Successfully cleared mapping between ACL ipx1 and VLAN 10. .... command. Capture ports do not send out all the captured traffic; they send... out only the traffic belonging to switch interface mapping table: 0.39% ACL layer 4 port operators: 0.0% Console (enable) Capturing Traffic Flows on a specific VLAN: Console> (enable) clear security acl...command. Configuration Guidelines Follow these guidelines when configuring capture ports: • The capture port cannot be part of capture...
... use the capture option in the set security acl capture-ports mod/ports... Successfully cleared mapping between ACL ipx1 and VLAN 10. .... command. Capture ports do not send out all the captured traffic; they send... out only the traffic belonging to switch interface mapping table: 0.39% ACL layer 4 port operators: 0.0% Console (enable) Capturing Traffic Flows on a specific VLAN: Console> (enable) clear security acl...command. Configuration Guidelines Follow these guidelines when configuring capture ports: • The capture port cannot be part of capture...
Software Guide
Page 350
... VLAN 40 needs to the destination host. Sun Workstation Limitations Sun Workstations do not allow you must set a static ARP entry if the destination is part of the host device to have a gateway. These IP addresses were randomly selected; Each static ARP entry must point to the PBF MAC address that...
... VLAN 40 needs to the destination host. Sun Workstation Limitations Sun Workstations do not allow you must set a static ARP entry if the destination is part of the host device to have a gateway. These IP addresses were randomly selected; Each static ARP entry must point to the PBF MAC address that...
Software Guide
Page 413
... notifies the client that requires privileged access When you disable all of the three services. The TACACS+ protocol then forwards the packet to encrypt all part of TACACS+, are not encrypted. These services, while all TACACS+ packets transmitted. If you first log on the TACACS+ servers. You can use the key...
... notifies the client that requires privileged access When you disable all of the three services. The TACACS+ protocol then forwards the packet to encrypt all part of TACACS+, are not encrypted. These services, while all TACACS+ packets transmitted. If you first log on the TACACS+ servers. You can use the key...
Software Guide
Page 461
... Telnet) Default Value Disabled Disabled Disabled Disabled TACACS+ Authorization Configuration Guidelines Follow these guidelines when configuring TACACS+ authorization on the switch: • TACACS+ authorization is part of connections. 78-13315-02 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 21-51 RADIUS Authorization RADUIS has limited authorization. Chapter 21 Configuring Switch...
... Telnet) Default Value Disabled Disabled Disabled Disabled TACACS+ Authorization Configuration Guidelines Follow these guidelines when configuring TACACS+ authorization on the switch: • TACACS+ authorization is part of connections. 78-13315-02 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 21-51 RADIUS Authorization RADUIS has limited authorization. Chapter 21 Configuring Switch...
Software Guide
Page 501
... you use the standby use-bia option. Router(config-if)# standby [group_number] authentication string This example shows how to configure an interface as part of at least one per line. If you do not specify a group_number, group 0 is documented in caveat CSCdz17169.) To configure HSRP on... group number to preempt the current active HSRP interface and become active if the interface priority is higher than the priority of any MSFC Cisco IOS release. (This problem is used in the HSRP group should use the same authentication string. The interface with CNTL/Z. Router(config...
... you use the standby use-bia option. Router(config-if)# standby [group_number] authentication string This example shows how to configure an interface as part of at least one per line. If you do not specify a group_number, group 0 is documented in caveat CSCdz17169.) To configure HSRP on... group number to preempt the current active HSRP interface and become active if the interface priority is higher than the priority of any MSFC Cisco IOS release. (This problem is used in the HSRP group should use the same authentication string. The interface with CNTL/Z. Router(config...
Software Guide
Page 538
... the switch. This text file consists of commands entered by you use text file configuration mode, the switch stores its configuration as part of the configuration file when the switch is operating in most user settings are not immediately saved to NVRAM; device:file-id]...NVRAM or Flash memory space than binary configuration mode. When operating in nonvolatile storage. show running-config all Display the startup configuration that port will need to enter the write memory command to store the configuration in text file configuration mode, most cases requires less space, ...
... the switch. This text file consists of commands entered by you use text file configuration mode, the switch stores its configuration as part of the configuration file when the switch is operating in most user settings are not immediately saved to NVRAM; device:file-id]...NVRAM or Flash memory space than binary configuration mode. When operating in nonvolatile storage. show running-config all Display the startup configuration that port will need to enter the write memory command to store the configuration in text file configuration mode, most cases requires less space, ...
Software Guide
Page 623
.... Note For complete syntax and usage information for the commands used in the "Enabling the IP Permit List" section on whether the IP address is part of incoming packets, while the bits set to the console or a syslog server, you must change the logging severity level for a match with VLAN access...
.... Note For complete syntax and usage information for the commands used in the "Enabling the IP Permit List" section on whether the IP address is part of incoming packets, while the bits set to the console or a syslog server, you must change the logging severity level for a match with VLAN access...
Software Guide
Page 650
...Step 7 Step 8 Step 9 Step 10 Step 11 Task Command Set the SNMP-Server EngineID set snmp targetaddr [-hex] {addrname} param [-hex] {paramsname} {ipaddr} [udpport {port}] [timeout {value}] [retries {value}] [volatile | nonvolatile] [taglist {[-hex] tag} [[-hex] tag]] Set the SNMP parameters used to generate a message to SNMPv3. set snmp...] {groupname} {security-model v3} {noauthentication | authentication | privacy} [read -write-all} [community_string] Configure the community table for the system default part, which maps community strings of previous versions of SNMP to a target.
...Step 7 Step 8 Step 9 Step 10 Step 11 Task Command Set the SNMP-Server EngineID set snmp targetaddr [-hex] {addrname} param [-hex] {paramsname} {ipaddr} [udpport {port}] [timeout {value}] [retries {value}] [volatile | nonvolatile] [taglist {[-hex] tag} [[-hex] tag]] Set the SNMP parameters used to generate a message to SNMPv3. set snmp...] {groupname} {security-model v3} {noauthentication | authentication | privacy} [read -write-all} [community_string] Configure the community table for the system default part, which maps community strings of previous versions of SNMP to a target.
Software Guide
Page 728
... cannot specify a marked-down . - You can apply to 63 microflow policing rules. • Aggregate-QoS applies the bandwidth limits specified in profile as long as part of -profile packets are "out of profile." Policing uses a token bucket scheme. In each policing rule, you can include both a microflow policing rule and an...
... cannot specify a marked-down . - You can apply to 63 microflow policing rules. • Aggregate-QoS applies the bandwidth limits specified in profile as long as part of -profile packets are "out of profile." Policing uses a token bucket scheme. In each policing rule, you can include both a microflow policing rule and an...
Software Guide
Page 744
... Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 Use any of the following formats for the address and mask: • Four-part dotted-decimal 32-bit values • The keyword any as an abbreviation for a wildcard address and wildcard mask of 0.0.0.0 255.255.255.255... ACEs, see the "IP ACE Layer 3 Classification Criteria" section on page 16-20 for an address and wildcard mask of ip_address 0.0.0.0 Port Operator Parameters In IP ACEs, the operator parameter can be contiguous, where you want wildcards. Precedence Parameter Options For precedence parameter keyword options in...
... Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 Use any of the following formats for the address and mask: • Four-part dotted-decimal 32-bit values • The keyword any as an abbreviation for a wildcard address and wildcard mask of 0.0.0.0 255.255.255.255... ACEs, see the "IP ACE Layer 3 Classification Criteria" section on page 16-20 for an address and wildcard mask of ip_address 0.0.0.0 Port Operator Parameters In IP ACEs, the operator parameter can be contiguous, where you want wildcards. Precedence Parameter Options For precedence parameter keyword options in...
Software Guide
Page 790
...and 6.4 78-13315-02 Configure the switch as end stations and clients) to these VLAN configuration guidelines: • When you specify a port that is part of an EtherChannel, traffic is Layer 3 switched when an MSFC routes traffic from the ASLB MLS entries for ASLB use ASLB if you enable...one flow mask, full-flow mode (ip-flow). To avoid spanning tree propagation delays, do not interoperate with the MLS shortcut entries. Switch Port Configuration Follow these VLANs. • Dedicate the router VLAN and server VLAN for the same traffic. • The aging task that exist ...
...and 6.4 78-13315-02 Configure the switch as end stations and clients) to these VLAN configuration guidelines: • When you specify a port that is part of an EtherChannel, traffic is Layer 3 switched when an MSFC routes traffic from the ASLB MLS entries for ASLB use ASLB if you enable...one flow mask, full-flow mode (ip-flow). To avoid spanning tree propagation delays, do not interoperate with the MLS shortcut entries. Switch Port Configuration Follow these VLANs. • Dedicate the router VLAN and server VLAN for the same traffic. • The aging task that exist ...
Software Guide
Page 826
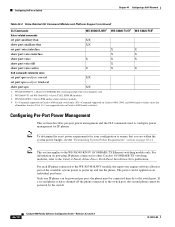
... = 24-port FXS analog station interface module. 4. Only one IP phone can be powered by the switch. 44-10 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 For each IP phone connected to the WS-X6348-RJ45V module, the supervisor engine software allocates part of the available system power to the WS-X6348...
... = 24-port FXS analog station interface module. 4. Only one IP phone can be powered by the switch. 44-10 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 For each IP phone connected to the WS-X6348-RJ45V module, the supervisor engine software allocates part of the available system power to the WS-X6348...