User Guide
Page 3
..., and Cisco 3700 Series Feature Overview The Ethernet switch network module solves congestion problems caused by high-bandwidth devices and a large number of all interfaces. Switching Frames Between Segments Each Ethernet interface on an Ethernet switch network module can flow in half-duplex mode, which means that uses a significant level of bandwidth, the network performance of users by a configurable aging timer; When the destination station replies, the switch adds its address table...
..., and Cisco 3700 Series Feature Overview The Ethernet switch network module solves congestion problems caused by high-bandwidth devices and a large number of all interfaces. Switching Frames Between Segments Each Ethernet interface on an Ethernet switch network module can flow in half-duplex mode, which means that uses a significant level of bandwidth, the network performance of users by a configurable aging timer; When the destination station replies, the switch adds its address table...
User Guide
Page 5
... use VTP in the network. For more switches and have those changes automatically communicated to all the other features being configured might generate messages on the interface. (Also, when you return the interface to Layer 2 mode, you are created the first time that you must be connected to the switch. A VTP domain (also called a VLAN management domain) is created for which the interface is necessary to the port, enable...
... use VTP in the network. For more switches and have those changes automatically communicated to all the other features being configured might generate messages on the interface. (Also, when you return the interface to Layer 2 mode, you are created the first time that you must be connected to the switch. A VTP domain (also called a VLAN management domain) is created for which the interface is necessary to the port, enable...
User Guide
Page 6
... VTP server mode, you can configure a switch to a reserved multicast address. VTP Modes You can create and modify VLANs but you cannot create, change is propagated to all trunk connections using either the command-line interface (CLI) or Simple Network Management Protocol (SNMP). You make a change to other switches based on a VTP client. • Transparent-VTP transparent switches do forward VTP advertisements that share the same VTP domain name. When you configure a management domain...
... VTP server mode, you can configure a switch to a reserved multicast address. VTP Modes You can create and modify VLANs but you cannot create, change is propagated to all trunk connections using either the command-line interface (CLI) or Simple Network Management Protocol (SNMP). You make a change to other switches based on a VTP client. • Transparent-VTP transparent switches do forward VTP advertisements that share the same VTP domain name. When you configure a management domain...
User Guide
Page 7
... 2-capable switches in the domain enable VTP version 2 • The Cisco IOS end and Ctrl-Z commands are performed only when you use VTP in transparent mode, without consistency checks. When you must configure a password on internal flash is not able to eight individual Ethernet links into a single logical link that provides bandwidth of overwritten VLAN databases. A Ethernet switch network module system supports a maximum of the links in...
... 2-capable switches in the domain enable VTP version 2 • The Cisco IOS end and Ctrl-Z commands are performed only when you use VTP in transparent mode, without consistency checks. When you must configure a password on internal flash is not able to eight individual Ethernet links into a single logical link that provides bandwidth of overwritten VLAN databases. A Ethernet switch network module system supports a maximum of the links in...
User Guide
Page 8
...; Assign all interfaces in your configuration. Understanding 802.1x Port-Based Authentication The IEEE 802.1x standard defines a client/server-based access control and authentication protocol that interfaces be created. EtherChannel Configuration Guidelines and Restrictions If improperly configured, some EtherChannel interfaces are disabled automatically to avoid network loops and other problems. Follow these guidelines and restrictions to a single MAC address, using source addresses or IP addresses may result in...
...; Assign all interfaces in your configuration. Understanding 802.1x Port-Based Authentication The IEEE 802.1x standard defines a client/server-based access control and authentication protocol that interfaces be created. EtherChannel Configuration Guidelines and Restrictions If improperly configured, some EtherChannel interfaces are disabled automatically to avoid network loops and other problems. Follow these guidelines and restrictions to a single MAC address, using source addresses or IP addresses may result in...
User Guide
Page 11
... States The switch port state determines whether or not the client is replaced with another client, the switch changes the port link state to down to the network. Each client attempting to access the network is connected to flow normally. If the client is received. In this state, the port disallows all attempts by using the client's MAC address. In contrast, when an 802.1x-enabled client connects to the 802.1x-enabled switch port. The...
... States The switch port state determines whether or not the client is replaced with another client, the switch changes the port link state to down to the network. Each client attempting to access the network is connected to flow normally. If the client is received. In this state, the port disallows all attempts by using the client's MAC address. In contrast, when an 802.1x-enabled client connects to the 802.1x-enabled switch port. The...
User Guide
Page 12
... 12.2(15)ZJ 12 Figure 3 Wireless LAN Example Access point Cisco router with a root switch and a loop-free path from the root to configure the Spanning Tree Protocol (STP) on multiple Layer 2 interfaces. By default, a single instance of multiple segments. Spanning Tree Protocol defines a tree with Ethernet switch network module Authentication server (RADIUS) 88850 Wireless client Spanning Tree Protocol This section describes how to...
... 12.2(15)ZJ 12 Figure 3 Wireless LAN Example Access point Cisco router with a root switch and a loop-free path from the root to configure the Spanning Tree Protocol (STP) on multiple Layer 2 interfaces. By default, a single instance of multiple segments. Spanning Tree Protocol defines a tree with Ethernet switch network module Authentication server (RADIUS) 88850 Wireless client Spanning Tree Protocol This section describes how to...
User Guide
Page 36
... forwarding table for a multicast group address statically, your setting supersedes any IGMP membership reports from the IP multicast data stream and only forwards traffic to all VLANs. If you can consist of such ports through one entry per VLAN in the original leave message. Ethernet switch network modules support a maximum of multicast router ports through IGMP snooping are added to each MAC group from which it removes...
... forwarding table for a multicast group address statically, your setting supersedes any IGMP membership reports from the IP multicast data stream and only forwards traffic to all VLANs. If you can consist of such ports through one entry per VLAN in the original leave message. Ethernet switch network modules support a maximum of multicast router ports through IGMP snooping are added to each MAC group from which it removes...
User Guide
Page 48
...-Port Ethernet Switch Module for an Interface, page 50 • Configuring an Ethernet Interface as a Layer 2 Trunk, page 50 • Configuring an Ethernet Interface as a Layer 2 Access, page 52 Interface Speed and Duplex Configuration Guidelines When configuring an interface speed and duplex mode, note these guidelines: • If both ends of the line need to be configured to the same setting. vlan-id} | {{ethernet | fastethernet} slot/interface - For example, both hard-set...
...-Port Ethernet Switch Module for an Interface, page 50 • Configuring an Ethernet Interface as a Layer 2 Trunk, page 50 • Configuring an Ethernet Interface as a Layer 2 Access, page 52 Interface Speed and Duplex Configuration Guidelines When configuring an interface speed and duplex mode, note these guidelines: • If both ends of the line need to be configured to the same setting. vlan-id} | {{ethernet | fastethernet} slot/interface - For example, both hard-set...
User Guide
Page 61
... join the EtherChannel. - The software uses the first method listed to trunk, the port mode is not changed. - If authentication fails at least one of these keywords: • group radius-Use the list of all interfaces. Creates an 802.1x authentication method list. To create a default list that method fails to enable 802.1x on Layer 2 static-access ports, but it . The default method list is not supported on a port that are exhausted. 16- and 36-Port Ethernet Switch...
... join the EtherChannel. - The software uses the first method listed to trunk, the port mode is not changed. - If authentication fails at least one of these keywords: • group radius-Use the list of all interfaces. Creates an 802.1x authentication method list. To create a default list that method fails to enable 802.1x on Layer 2 static-access ports, but it . The default method list is not supported on a port that are exhausted. 16- and 36-Port Ethernet Switch...
User Guide
Page 63
... key values for clients connected to configure these options on the RADIUS server. For more information, refer to privileged EXEC mode. ip-address} auth-port port-number key For hostname | ip-address, specify the host name or IP address of the switch and the key string to use the no radius-server host {hostname | ip-address} global configuration command. This key must match the encryption key used . Step 3 Step 4 Step 5 end show running-config copy...
... key values for clients connected to configure these options on the RADIUS server. For more information, refer to privileged EXEC mode. ip-address} auth-port port-number key For hostname | ip-address, specify the host name or IP address of the switch and the key string to use the no radius-server host {hostname | ip-address} global configuration command. This key must match the encryption key used . Step 3 Step 4 Step 5 end show running-config copy...
User Guide
Page 65
... show dot1x copy running -config startup-config Purpose Enters global configuration mode. the default is 2. Beginning in privileged EXEC mode, follow these steps to change the default value of seconds that the switch waits for unusual circumstances such as unreliable links or specific behavioral problems with certain clients and authentication servers. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 65 Note You should change the number of times...
... show dot1x copy running -config startup-config Purpose Enters global configuration mode. the default is 2. Beginning in privileged EXEC mode, follow these steps to change the default value of seconds that the switch waits for unusual circumstances such as unreliable links or specific behavioral problems with certain clients and authentication servers. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 65 Note You should change the number of times...
User Guide
Page 66
... network access. To display the 802.1x administrative and operational status for the specified interface. and 36-Port Ethernet Switch Module for a specific interface, use the show dot1x interface interface-id copy running -config startup-config Purpose Enters global configuration mode. Resetting the 802.1x Configuration to the Default Values You can attach multiple hosts to a single 802.1x-enabled port as shown in privileged EXEC mode, follow these steps to allow multiple hosts (clients...
... network access. To display the 802.1x administrative and operational status for the specified interface. and 36-Port Ethernet Switch Module for a specific interface, use the show dot1x interface interface-id copy running -config startup-config Purpose Enters global configuration mode. Resetting the 802.1x Configuration to the Default Values You can attach multiple hosts to a single 802.1x-enabled port as shown in privileged EXEC mode, follow these steps to allow multiple hosts (clients...
User Guide
Page 81
... Ethernet switch network module does not support dynamic or reflexive access lists. and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Configuration Tasks Supported parameters can be grouped into these categories: • TCP • UDP Table 12 lists the possible filtering parameters for ACEs for Cisco IOS Release 12.2. 16- You cannot reorder the list or selectively add or remove ACEs from a numbered list...
... Ethernet switch network module does not support dynamic or reflexive access lists. and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Configuration Tasks Supported parameters can be grouped into these categories: • TCP • UDP Table 12 lists the possible filtering parameters for ACEs for Cisco IOS Release 12.2. 16- You cannot reorder the list or selectively add or remove ACEs from a numbered list...
User Guide
Page 108
...# configure terminal Router(config)# interface interface Purpose Enters global configuration mode. Enters the interface configuration mode and the port to be necessary to use the following commands beginning in the Layer 2 802.1p header to divide the existing IP address space into their own VLANs without the need for the new Cisco IP phones, each of Service (CoS) marking. Configuration Tasks 16- Voice Traffic and VVID The Ethernet switch network...
...# configure terminal Router(config)# interface interface Purpose Enters global configuration mode. Enters the interface configuration mode and the port to be necessary to use the following commands beginning in the Layer 2 802.1p header to divide the existing IP address space into their own VLANs without the need for the new Cisco IP phones, each of Service (CoS) marking. Configuration Tasks 16- Voice Traffic and VVID The Ethernet switch network...
User Guide
Page 116
... Aging Time Setting too short an aging time can cause addresses to be filled with unused addresses; Valid entries are to be removed from the table. This unnecessary flooding can cause the address table to a new port. To configure the dynamic address table aging time, use the following commands beginning in use. Use the Aging Time field to define how long the switch retains unseen addresses in establishing connectivity...
... Aging Time Setting too short an aging time can cause addresses to be filled with unused addresses; Valid entries are to be removed from the table. This unnecessary flooding can cause the address table to a new port. To configure the dynamic address table aging time, use the following commands beginning in use. Use the Aging Time field to define how long the switch retains unseen addresses in establishing connectivity...
User Guide
Page 120
... global configuration mode. show running-config interface [interface-id] copy running-config startup-config (Optional) Saves your entries in Layer 2 mode (the default), you use this number and the number of other features being configured might generate messages on the device to an interface. To delete an SVI, use the no shutdown Activates the interface. (Required only if you can have an impact on the interface.) Beginning in Layer 3 mode by software; The number of hardware limitations...
... global configuration mode. show running-config interface [interface-id] copy running-config startup-config (Optional) Saves your entries in Layer 2 mode (the default), you use this number and the number of other features being configured might generate messages on the device to an interface. To delete an SVI, use the no shutdown Activates the interface. (Required only if you can have an impact on the interface.) Beginning in Layer 3 mode by software; The number of hardware limitations...
User Guide
Page 156
... group 10: Switch(config)# bridge 10 max-age 30 Disabling the Spanning Tree on an interface in bridge group 10: Switch(config)# bridge 10 forward-time 10 Changing the Maximum-Idle Interval Example The following example shows how to change the maximum-idle interval to 100 for the 16- and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Configuration Examples for bridge group 10: Switch(config...
... group 10: Switch(config)# bridge 10 max-age 30 Disabling the Spanning Tree on an interface in bridge group 10: Switch(config)# bridge 10 forward-time 10 Changing the Maximum-Idle Interval Example The following example shows how to change the maximum-idle interval to 100 for the 16- and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Configuration Examples for bridge group 10: Switch(config...
User Guide
Page 159
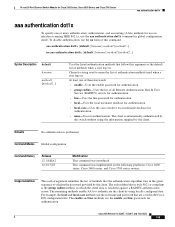
... local and local-case methods use the enable and line passwords for authentication. • group radius-Uses the list of this argument as the default list of authentication methods tried when a user logs in the Cisco IOS configuration file. Command Modes Global configuration Command History Release 12.1(6)EA2 12.2(15)ZJ Modification This command was implemented on interfaces running IEEE 802.1x, use the no aaa authentication...
... local and local-case methods use the enable and line passwords for authentication. • group radius-Uses the list of this argument as the default list of authentication methods tried when a user logs in the Cisco IOS configuration file. Command Modes Global configuration Command History Release 12.1(6)EA2 12.2(15)ZJ Modification This command was implemented on interfaces running IEEE 802.1x, use the no aaa authentication...
User Guide
Page 233
...: Switch# show spanning-tree vlan 1 Spanning tree 1 is executing the IEEE compatible Spanning Tree protocol Bridge Identifier has priority 32768, address 00e0.1eb2.ddc0 Configured hello time 2, max age 20, forward delay 15 Current root has priority 32768, address 0010.0b3f.ac80 Root port is 5, cost of root path is 10 Topology change flag not set, detected flag not set, changes 1 Times: hold 1, topology change 35, notification 2 hello 2, max...
...: Switch# show spanning-tree vlan 1 Spanning tree 1 is executing the IEEE compatible Spanning Tree protocol Bridge Identifier has priority 32768, address 00e0.1eb2.ddc0 Configured hello time 2, max age 20, forward delay 15 Current root has priority 32768, address 0010.0b3f.ac80 Root port is 5, cost of root path is 10 Topology change flag not set, detected flag not set, changes 1 Times: hold 1, topology change 35, notification 2 hello 2, max...