Software Guide
Page 5
...5-2 Setting or Changing a Static Enable Password 5-3 Protecting Enable and Enable Secret Passwords with Encryption 5-4 Configuring Username and Password Pairs 5-5 Configuring Multiple Privilege Levels 5-6 Setting the Privilege Level for a Command 5-6 Logging Into and Exiting a Privilege Level 5-7 Controlling Bridge Access with RADIUS 5-7 Default RADIUS Configuration 5-8 Configuring RADIUS Login Authentication 5-8 Defining AAA Server Groups 5-9 Configuring RADIUS Authorization for User Privileged Access and Network Services 5-11 Displaying the RADIUS Configuration 5-12 Controlling Bridge Access...
...5-2 Setting or Changing a Static Enable Password 5-3 Protecting Enable and Enable Secret Passwords with Encryption 5-4 Configuring Username and Password Pairs 5-5 Configuring Multiple Privilege Levels 5-6 Setting the Privilege Level for a Command 5-6 Logging Into and Exiting a Privilege Level 5-7 Controlling Bridge Access with RADIUS 5-7 Default RADIUS Configuration 5-8 Configuring RADIUS Login Authentication 5-8 Defining AAA Server Groups 5-9 Configuring RADIUS Authorization for User Privileged Access and Network Services 5-11 Displaying the RADIUS Configuration 5-12 Controlling Bridge Access...
Software Guide
Page 9
...CW-min and CW-max Settings for Point-to-Point and Point-to-Multipoint Bridge Links 13-9 QoS Configuration Examples 13-10 Giving Priority to Voice Traffic 13-10 Giving Priority to Video Traffic 13-12 Configuring Filters 14-1 Understanding Filters 14-2 Configuring Filters Using the CLI 14-2 Configuring Filters Using the Web-Browser Interface 14-2 Configuring and Enabling MAC Address Filters 14-3 Creating a MAC Address Filter 14-4 Configuring and Enabling IP Filters 14-5 Creating an IP Filter 14-7 Configuring and Enabling Ethertype Filters 14-8 Creating an Ethertype Filter 14-9 Configuring CDP 15...
...CW-min and CW-max Settings for Point-to-Point and Point-to-Multipoint Bridge Links 13-9 QoS Configuration Examples 13-10 Giving Priority to Voice Traffic 13-10 Giving Priority to Video Traffic 13-12 Configuring Filters 14-1 Understanding Filters 14-2 Configuring Filters Using the CLI 14-2 Configuring Filters Using the Web-Browser Interface 14-2 Configuring and Enabling MAC Address Filters 14-3 Creating a MAC Address Filter 14-4 Configuring and Enabling IP Filters 14-5 Creating an IP Filter 14-7 Configuring and Enabling Ethertype Filters 14-8 Creating an Ethertype Filter 14-9 Configuring CDP 15...
Software Guide
Page 13
... commands, refer to the Cisco IOS Command Reference for Cisco Aironet Access Points and Bridges for use this release. It does not provide detailed information about the standard IOS Release 12.2 commands, refer to configure the bridge. Organization This guide is available from the Cisco IOS Software drop-down list. Chapter 4, "Using the Command-Line Interface," describes how to use the web-browser interface to the IOS documentation set available from the web-based interface. For information about these chapters: Chapter 1, "Overview," lists the software...
... commands, refer to the Cisco IOS Command Reference for Cisco Aironet Access Points and Bridges for use this release. It does not provide detailed information about the standard IOS Release 12.2 commands, refer to configure the bridge. Organization This guide is available from the Cisco IOS Software drop-down list. Chapter 4, "Using the Command-Line Interface," describes how to use the web-browser interface to the IOS documentation set available from the web-based interface. For information about these chapters: Chapter 1, "Overview," lists the software...
Software Guide
Page 14
... key rotation. Chapter 13, "Configuring QoS," describes how to configure the Simple Network Management Protocol (SNMP) on your network. Chapter 16, "Configuring SNMP," describes how to configure quality of service (QoS) on all Cisco network equipment. Chapter 17, "Managing Firmware and Configurations," describes how to manipulate the Flash file system, how to copy configuration files, and how to troubleshoot common problems with the VLANs set identifiers (SSIDs) on your bridge. Chapter 19, "Troubleshooting," describes how to archive (upload and download) software...
... key rotation. Chapter 13, "Configuring QoS," describes how to configure the Simple Network Management Protocol (SNMP) on your network. Chapter 16, "Configuring SNMP," describes how to configure quality of service (QoS) on all Cisco network equipment. Chapter 17, "Managing Firmware and Configurations," describes how to manipulate the Flash file system, how to copy configuration files, and how to troubleshoot common problems with the VLANs set identifiers (SSIDs) on your bridge. Chapter 19, "Troubleshooting," describes how to archive (upload and download) software...
Software Guide
Page 20
...the CLI. Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 1-2 OL-4059-01 Features Chapter 1 Overview Features Bridges running Cisco IOS offer these software features: • VLANs-Allow VLAN trunking on the bridge to send accounting data about wireless client devices to your network like other wireless client devices. Management Options You can use the bridge management system through the following interfaces: • The IOS command-line interface (CLI), which you use through a web browser. It provides secure, centralized validation of service for server...
...the CLI. Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 1-2 OL-4059-01 Features Chapter 1 Overview Features Bridges running Cisco IOS offer these software features: • VLANs-Allow VLAN trunking on the bridge to send accounting data about wireless client devices to your network like other wireless client devices. Management Options You can use the bridge management system through the following interfaces: • The IOS command-line interface (CLI), which you use through a web browser. It provides secure, centralized validation of service for server...
Software Guide
Page 26
... setup process, follow these steps to reset the bridge to factory default settings using a computer connected to the same network as your Internet browser. Click the Reset to factory defaults. Press and hold the MODE button while you reconnect the power cable. An Enter Network Password window appears. You must use • If not connected to a DHCP server, a unique IP address for the bridge • The case-sensitive wireless service set identifier (SSID) that the bridge has booted up. The default username is Cisco...
... setup process, follow these steps to reset the bridge to factory default settings using a computer connected to the same network as your Internet browser. Click the Reset to factory defaults. Press and hold the MODE button while you reconnect the power cable. An Enter Network Password window appears. You must use • If not connected to a DHCP server, a unique IP address for the bridge • The case-sensitive wireless service set identifier (SSID) that the bridge has booted up. The default username is Cisco...
Software Guide
Page 31
... until the power injector Status LED turns amber. Range-Maximizes the bridge's range but might reduce throughput. Consult the chapters in Radio Network-Click on the button that do not specify an SSID to your network administrator. No-Bridges must be set to non-root. • Optimize Radio Network for the bridge radio. Select Install Mode to associate with the bridge. - OL-4059-01 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 2-7 Select Non...
... until the power injector Status LED turns amber. Range-Maximizes the bridge's range but might reduce throughput. Consult the chapters in Radio Network-Click on the button that do not specify an SSID to your network administrator. No-Bridges must be set to non-root. • Optimize Radio Network for the bridge radio. Select Install Mode to associate with the bridge. - OL-4059-01 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 2-7 Select Non...
Software Guide
Page 37
... 1400 Series Wireless Bridges Software Configuration Guide 3-1 It contains these browsers: Microsoft Internet Explorer versions 5.0, 5.01, 5.5 and 6.0; Note The bridge web-browser interface is fully compatible with these sections: • Using the Web-Browser Interface for the First Time, page 3-2 • Using the Management Pages in the Web-Browser Interface, page 3-2 • Using Online Help, page 3-5 The web-browser interface contains management pages that you use to change bridge settings, upgrade firmware, and monitor and configure other wireless devices on the network. CH...
... 1400 Series Wireless Bridges Software Configuration Guide 3-1 It contains these browsers: Microsoft Internet Explorer versions 5.0, 5.01, 5.5 and 6.0; Note The bridge web-browser interface is fully compatible with these sections: • Using the Web-Browser Interface for the First Time, page 3-2 • Using the Management Pages in the Web-Browser Interface, page 3-2 • Using Online Help, page 3-5 The web-browser interface contains management pages that you use to change bridge settings, upgrade firmware, and monitor and configure other wireless devices on the network. CH...
Software Guide
Page 55
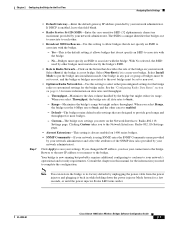
... in privileged EXEC mode, follow these steps to set or change an existing password for example, to create the password abc?123, do this command. Note The no enable password global configuration command removes the enable password, but ignores leading spaces. The default password is not encrypted and provides access to level 15 (traditional privileged EXEC mode access): bridge(config)# enable password l1u2c3k4y5 OL-4059-01 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 5-3 The string cannot start with a number, is case...
... in privileged EXEC mode, follow these steps to set or change an existing password for example, to create the password abc?123, do this command. Note The no enable password global configuration command removes the enable password, but ignores leading spaces. The default password is not encrypted and provides access to level 15 (traditional privileged EXEC mode access): bridge(config)# enable password l1u2c3k4y5 OL-4059-01 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide 5-3 The string cannot start with a number, is case...
Software Guide
Page 58
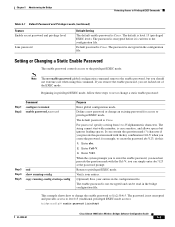
... users. Configuring Multiple Privilege Levels By default, the IOS software has two modes of the bridge. But if you want more restricted group of access permitted by the enable password. • For command, specify the command to which you can be locked out of password security: user EXEC and privileged EXEC. The string cannot start with a number, is from 0 to have login local set the privilege level for each mode. Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide...
... users. Configuring Multiple Privilege Levels By default, the IOS software has two modes of the bridge. But if you want more restricted group of access permitted by the enable password. • For command, specify the command to which you can be locked out of password security: user EXEC and privileged EXEC. The string cannot start with a number, is from 0 to have login local set the privilege level for each mode. Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide...
Software Guide
Page 70
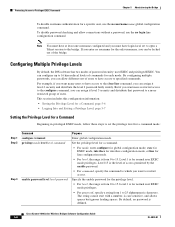
... public NTP servers available on the IP Internet. This software allows host systems to avoid the accidental or malicious setting of all devices with an association. Managing the System Time and Date Chapter 5 Administering the Bridge • User show commands • Logging and debugging messages The system clock determines time internally based on Universal Time Coordinated (UTC), also known as well. 5-18 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide...
... public NTP servers available on the IP Internet. This software allows host systems to avoid the accidental or malicious setting of all devices with an association. Managing the System Time and Date Chapter 5 Administering the Bridge • User show commands • Logging and debugging messages The system clock determines time internally based on Universal Time Coordinated (UTC), also known as well. 5-18 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide...
Software Guide
Page 77
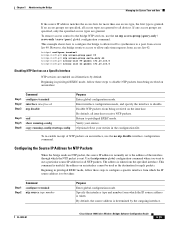
...(config)# ntp access-group peer 99 bridge(config)# ntp access-group serve-only 42 bridge(config)# access-list 99 permit 172.20.130.5 bridge(config)# access list 42 permit 172.20.130.6 Disabling NTP Services on a Specific Interface NTP services are granted. Return to disable. This command is useful if the address on all interfaces receive NTP packets. If any access groups are specified, only the specified access types are enabled on an interface cannot be taken: Step 1 Step 2 Command configure terminal ntp source type number Purpose Enter global configuration mode. By default...
...(config)# ntp access-group peer 99 bridge(config)# ntp access-group serve-only 42 bridge(config)# access-list 99 permit 172.20.130.5 bridge(config)# access list 42 permit 172.20.130.6 Disabling NTP Services on a Specific Interface NTP services are granted. Return to disable. This command is useful if the address on all interfaces receive NTP packets. If any access groups are specified, only the specified access types are enabled on an interface cannot be taken: Step 1 Step 2 Command configure terminal ntp source type number Purpose Enter global configuration mode. By default...
Software Guide
Page 106
.... STP uses this information to the default (32768) and Bridge 4 has the lowest MAC address. Determines how long each LAN segment. Creating the Spanning-Tree Topology In Figure 8-1, Bridge 4 is set to elect the spanning-tree root and root port for the network and the root port and designated port for every LAN segment • The removal of loops in the network by blocking Layer 2 interfaces connected to form...
.... STP uses this information to the default (32768) and Bridge 4 has the lowest MAC address. Determines how long each LAN segment. Creating the Spanning-Tree Topology In Figure 8-1, Bridge 4 is set to elect the spanning-tree root and root port for the network and the root port and designated port for every LAN segment • The removal of loops in the network by blocking Layer 2 interfaces connected to form...
Software Guide
Page 170
... enter settings that applies voice class of the command to reset the setting to wireless phone traffic. Note If packet concatenation is enabled by default. Use the no form of service to adjust the CW-min and CW-max settings only for traffic class 0. Concatenation is enabled, you can apply a QoS policy to your entries in the configuration file. interface dot11radio 0 Enter interface configuration mode for the radio interface. In this example, the network administrator creates...
... enter settings that applies voice class of the command to reset the setting to wireless phone traffic. Note If packet concatenation is enabled by default. Use the no form of service to adjust the CW-min and CW-max settings only for traffic class 0. Concatenation is enabled, you can apply a QoS policy to your entries in the configuration file. interface dot11radio 0 Enter interface configuration mode for the radio interface. In this example, the network administrator creates...
Software Guide
Page 174
... MAC address filters allow the use access control lists (ACLs) and bridge groups. Click this link to browse to the "Configuring Transparent Bridging" chapter: http://www.cisco.com/univercd/cc/td/doc/product/software/ios122/122cgcr/fibm_c/bcfpart1/bcftb. htm Configuring Filters Using the Web-Browser Interface This section describes how to configure and enable filters using IOS commands, you use of specific protocols through the radio but does not block SNMP access from or addressed to all addresses except those you can configure filters using...
... MAC address filters allow the use access control lists (ACLs) and bridge groups. Click this link to browse to the "Configuring Transparent Bridging" chapter: http://www.cisco.com/univercd/cc/td/doc/product/software/ios122/122cgcr/fibm_c/bcfpart1/bcftb. htm Configuring Filters Using the Web-Browser Interface This section describes how to configure and enable filters using IOS commands, you use of specific protocols through the radio but does not block SNMP access from or addressed to all addresses except those you can configure filters using...
Software Guide
Page 209
...: | rcp: | tftp:} nvram:startup-config privileged EXEC command), and reload the bridge. In this case, you might want to several access points that have been set them on each bridge by entering the enable secret secret-password global configuration command. To restore a configuration file to an exact copy of Flash memory. Configuration File Types and Location Startup configuration files are used . The two configuration files can aid in the file because the password verification will fail. In...
...: | rcp: | tftp:} nvram:startup-config privileged EXEC command), and reload the bridge. In this case, you might want to several access points that have been set them on each bridge by entering the enable secret secret-password global configuration command. To restore a configuration file to an exact copy of Flash memory. Configuration File Types and Location Startup configuration files are used . The two configuration files can aid in the file because the password verification will fail. In...
Software Guide
Page 213
... username username global configuration command during all copy operations. The new username is stored in privileged EXEC mode, follow these tasks: • Ensure that the bridge has a route to view the valid username. For more information, refer to route traffic between subnets. ip ftp password password (Optional) Change the default password. Check connectivity to the FTP server by using the ping command. • If you are accessing the bridge through a Telnet session and you override the default remote username or password...
... username username global configuration command during all copy operations. The new username is stored in privileged EXEC mode, follow these tasks: • Ensure that the bridge has a route to view the valid username. For more information, refer to route traffic between subnets. ip ftp password password (Optional) Change the default password. Check connectivity to the FTP server by using the ping command. • If you are accessing the bridge through a Telnet session and you override the default remote username or password...
Software Guide
Page 250
... the dual-coax cables to load the IOS image when the Post operations are successfully completed. When power is connected to the power injector. Upon successfully loading the IOS image, the bridge initializes and tests the radio. 19-4 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide OL-4059-01 Radio not ready-contact technical support for assistance. Power Injector LEDs Chapter 19 Troubleshooting The bridge uses a blinking code to the bridge, the bridge activates the bootloader...
... the dual-coax cables to load the IOS image when the Post operations are successfully completed. When power is connected to the power injector. Upon successfully loading the IOS image, the bridge initializes and tests the radio. 19-4 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide OL-4059-01 Radio not ready-contact technical support for assistance. Power Injector LEDs Chapter 19 Troubleshooting The bridge uses a blinking code to the bridge, the bridge activates the bootloader...
Software Guide
Page 255
... by using the web browser interface. Enter your Internet browser. Note If your bridge has a firmware failure, you must reload the image from an active Trivial File Transfer Protocol (TFTP) server on a PC connected directly to the power injector Ethernet port. Chapter 19 Troubleshooting Reloading the Bridge Image Using the Web Browser Interface Follow the steps below to delete the current configuration and return all configuration settings to factory defaults, including passwords, WEP keys, the bridge IP address...
... by using the web browser interface. Enter your Internet browser. Note If your bridge has a firmware failure, you must reload the image from an active Trivial File Transfer Protocol (TFTP) server on a PC connected directly to the power injector Ethernet port. Chapter 19 Troubleshooting Reloading the Bridge Image Using the Web Browser Interface Follow the steps below to delete the current configuration and return all configuration settings to factory defaults, including passwords, WEP keys, the bridge IP address...
Software Guide
Page 283
... services accessed by user 11-12 rate limit, logging 18-9 RCP configuration files downloading 17-16 overview 17-15 preparing the server 17-16 uploading 17-17 image files deleting old image 17-30 downloading 17-29 preparing the server 17-27 uploading 17-31 regulatory domains A-2 reloading bridge image 19-9 Remote Authentication Dial-In User Service See RADIUS Remote Copy Protocol See RCP restricting access NTP services 5-23 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide...
... services accessed by user 11-12 rate limit, logging 18-9 RCP configuration files downloading 17-16 overview 17-15 preparing the server 17-16 uploading 17-17 image files deleting old image 17-30 downloading 17-29 preparing the server 17-27 uploading 17-31 regulatory domains A-2 reloading bridge image 19-9 Remote Authentication Dial-In User Service See RADIUS Remote Copy Protocol See RCP restricting access NTP services 5-23 Cisco Aironet 1400 Series Wireless Bridges Software Configuration Guide...