Software Guide
Page 4
... Opening the CLI with Secure Shell 2-2 Obtaining and Assigning an IP Address 2-3 Assigning an IP Address By Using the Exec 2-3 Protecting Your Wireless LAN 2-4 Configuring Basic Security Settings 2-4 Using VLANs 2-4 Express Security Types 2-5 CLI Security Configuration Examples 2-6 Example: No ... Bridging 3-4 Redundant Bridging 3-5 Workgroup Bridge Role 3-6 Universal Workgroup Bridge (2.4-GHz Radios Only) 3-8 Configuring Universal Workgroup Bridge on a Cisco 3200 3-11 Assigning Dynamic MAC address for Universal Workgroup Bridge 3-12 World Mode (2.4 GHz Radio Only) 3-12 Supported Country Codes ...
... Opening the CLI with Secure Shell 2-2 Obtaining and Assigning an IP Address 2-3 Assigning an IP Address By Using the Exec 2-3 Protecting Your Wireless LAN 2-4 Configuring Basic Security Settings 2-4 Using VLANs 2-4 Express Security Types 2-5 CLI Security Configuration Examples 2-6 Example: No ... Bridging 3-4 Redundant Bridging 3-5 Workgroup Bridge Role 3-6 Universal Workgroup Bridge (2.4-GHz Radios Only) 3-8 Configuring Universal Workgroup Bridge on a Cisco 3200 3-11 Assigning Dynamic MAC address for Universal Workgroup Bridge 3-12 World Mode (2.4 GHz Radio Only) 3-12 Supported Country Codes ...
Software Guide
Page 5
... Username and Password Pairs 4-9 Configuring Multiple Privilege Levels 4-10 Setting the Privilege Level for a Command 4-10 Logging Into and Exiting a Privilege Level 4-11 Protecting the Wireless LAN 4-11 Using VLANs 4-11 Express Security Types 4-12 Security Configuration Examples 4-14 Configuring and Enabling RADIUS 4-19 Understanding RADIUS 4-19 RADIUS Operation...the RADIUS Configuration 4-31 Controlling WMIC Access with TACACS+ 4-32 Understanding TACACS+ 4-32 TACACS+ Operation 4-33 Default TACACS+ Configuration 4-33 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide v
... Username and Password Pairs 4-9 Configuring Multiple Privilege Levels 4-10 Setting the Privilege Level for a Command 4-10 Logging Into and Exiting a Privilege Level 4-11 Protecting the Wireless LAN 4-11 Using VLANs 4-11 Express Security Types 4-12 Security Configuration Examples 4-14 Configuring and Enabling RADIUS 4-19 Understanding RADIUS 4-19 RADIUS Operation...the RADIUS Configuration 4-31 Controlling WMIC Access with TACACS+ 4-32 Understanding TACACS+ 4-32 TACACS+ Operation 4-33 Default TACACS+ Configuration 4-33 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide v
Software Guide
Page 13
GLOSSARY INDEX Using CLI Commands to Enable Roaming 14-12 Management Frame Protection 15-1 Understanding Management Frame Protection 15-1 Protection of Unicast Management Frames 15-2 Protection of Broadcast Management Frames 15-2 Client MFP For Access Points in Root mode 15-2 Configuring Client MFP 15-2 Configuring Infrastructure MFP 15-3 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide xiii
GLOSSARY INDEX Using CLI Commands to Enable Roaming 14-12 Management Frame Protection 15-1 Understanding Management Frame Protection 15-1 Protection of Unicast Management Frames 15-2 Protection of Broadcast Management Frames 15-2 Client MFP For Access Points in Root mode 15-2 Configuring Client MFP 15-2 Configuring Infrastructure MFP 15-3 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide xiii
Software Guide
Page 31
... three advanced security features to any root device as long the encrption and authentication settings match. • Management Frame Protection (MFP)-Support management frame protection version 1 and 2. The 802.1x supplicant provides a secure method for prioritizing traffic on your wireless network's WEP ...with AES and Temporal Key Integrity Protocol (TKIP) encryption is required for Wi-Fi Protected Access 2 (WPA2) and IEEE 802.11i wireless LAN security. • Enhanced authentication for Cisco Centralized Key Management (CCKM). • Roaming-Support fast, secure roaming of client...
... three advanced security features to any root device as long the encrption and authentication settings match. • Management Frame Protection (MFP)-Support management frame protection version 1 and 2. The 802.1x supplicant provides a secure method for prioritizing traffic on your wireless network's WEP ...with AES and Temporal Key Integrity Protocol (TKIP) encryption is required for Wi-Fi Protected Access 2 (WPA2) and IEEE 802.11i wireless LAN security. • Enhanced authentication for Cisco Centralized Key Management (CCKM). • Roaming-Support fast, secure roaming of client...
Software Guide
Page 36
...the WMIC CLI by encrypting the session. A prompt for remote connections than Telnet. at this URL: http://www.ssh.com/) Cisco 3200 Series Wireless MIC Software Configuration Guide 2 Connect the DB-9 end of SSH Communications Security, Ltd. If Telnet is a ...steps are in the Open field, and press Enter. When the terminal emulator establishes communications, a router prompt displays. SSH features strong cryptographic authentication, strong encryption, and integrity protection. Use the following settings for SSH access. (For detailed information on your operating system. Type...
...the WMIC CLI by encrypting the session. A prompt for remote connections than Telnet. at this URL: http://www.ssh.com/) Cisco 3200 Series Wireless MIC Software Configuration Guide 2 Connect the DB-9 end of SSH Communications Security, Ltd. If Telnet is a ...steps are in the Open field, and press Enter. When the terminal emulator establishes communications, a router prompt displays. SSH features strong cryptographic authentication, strong encryption, and integrity protection. Use the following settings for SSH access. (For detailed information on your operating system. Type...
Software Guide
Page 38
... WEP with VLANs disabled, you cannot create additional SSIDs with another SSID, you can communicate beyond the physical boundaries of a building. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 Advanced security features are linked. If you find that you can assign to SSIDs are... to your access point, you must configure security settings to prevent unauthorized access to your network. Protecting Your Wireless LAN Configuring the WMIC for the First Time Protecting Your Wireless LAN After you assign basic settings to your WMIC, you need to configure security settings...
... WEP with VLANs disabled, you cannot create additional SSIDs with another SSID, you can communicate beyond the physical boundaries of a building. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 Advanced security features are linked. If you find that you can assign to SSIDs are... to your access point, you must configure security settings to prevent unauthorized access to your network. Protecting Your Wireless LAN Configuring the WMIC for the First Time Protecting Your Wireless LAN After you assign basic settings to your WMIC, you need to configure security settings...
Software Guide
Page 39
...with stronger algorithms than no key management, and open authentication. However, static WEP keys are used in a public space. Wi-Fi Protected Access (WPA) permits wireless access to users authenticated against a database through the services of an authentication server, and then encrypts their ... and requires you should use this option only for SSIDs that associate by using this setting, you to enter a WEP key. Cisco 3200 Series Wireless MIC Software Configuration Guide 5 Configuring the WMIC for an authentication server on your network. Table 1 Security Types on ...
...with stronger algorithms than no key management, and open authentication. However, static WEP keys are used in a public space. Wi-Fi Protected Access (WPA) permits wireless access to users authenticated against a database through the services of an authentication server, and then encrypts their ... and requires you should use this option only for SSIDs that associate by using this setting, you to enter a WEP key. Cisco 3200 Series Wireless MIC Software Configuration Guide 5 Configuring the WMIC for an authentication server on your network. Table 1 Security Types on ...
Software Guide
Page 40
ssid no_security-ssid Cisco 3200 Series Wireless MIC Software Configuration Guide 6 speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48.0 54.0 rts threshold 4000 station-role root infrastructure-client bridge-group 1 ! ssid static_wep_ssid vlan 20 authentication open guest-mode interface Dot11Radio0 no ip address no ip route-cache ! Protecting Your Wireless...
ssid no_security-ssid Cisco 3200 Series Wireless MIC Software Configuration Guide 6 speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48.0 54.0 rts threshold 4000 station-role root infrastructure-client bridge-group 1 ! ssid static_wep_ssid vlan 20 authentication open guest-mode interface Dot11Radio0 no ip address no ip route-cache ! Protecting Your Wireless...
Software Guide
Page 41
...group 1 block-unknown-source no bridge-group 1 source-learning no ip route-cache bridge-group 20 bridge-group 20 spanning-disabled ! Cisco 3200 Series Wireless MIC Software Configuration Guide 7 interface FastEthernet0 no ip address no ip route-cache bridge-group 20 bridge-group 20 ...30 authentication open eap eap_methods authentication network-eap eap_methods interface Dot11Radio0 no ip address no ip route-cache ! Configuring the WMIC for the First Time Protecting Your Wireless LAN ! speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48.0 54.0 rts threshold ...
...group 1 block-unknown-source no bridge-group 1 source-learning no ip route-cache bridge-group 20 bridge-group 20 spanning-disabled ! Cisco 3200 Series Wireless MIC Software Configuration Guide 7 interface FastEthernet0 no ip address no ip route-cache bridge-group 20 bridge-group 20 ...30 authentication open eap eap_methods authentication network-eap eap_methods interface Dot11Radio0 no ip address no ip route-cache ! Configuring the WMIC for the First Time Protecting Your Wireless LAN ! speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48.0 54.0 rts threshold ...
Software Guide
Page 42
... 1646 ! aaa group server radius rad_acct ! aaa group server radius rad_pmip ! bridge irb ! ! aaa group server radius rad_mac ! Cisco 3200 Series Wireless MIC Software Configuration Guide 8 aaa group server radius dummy ! aaa authentication login eap_methods group rad_eap aaa authentication login mac_methods ... bridge-group 30 no bridge-group 30 unicast-flooding bridge-group 30 spanning-disabled ! aaa group server radius rad_admin ! Protecting Your Wireless LAN Configuring the WMIC for the First Time interface Dot11Radio0.30 encapsulation dot1Q 30 no ip route-cache bridge-...
... 1646 ! aaa group server radius rad_acct ! aaa group server radius rad_pmip ! bridge irb ! ! aaa group server radius rad_mac ! Cisco 3200 Series Wireless MIC Software Configuration Guide 8 aaa group server radius dummy ! aaa authentication login eap_methods group rad_eap aaa authentication login mac_methods ... bridge-group 30 no bridge-group 30 unicast-flooding bridge-group 30 spanning-disabled ! aaa group server radius rad_admin ! Protecting Your Wireless LAN Configuring the WMIC for the First Time interface Dot11Radio0.30 encapsulation dot1Q 30 no ip route-cache bridge-...
Software Guide
Page 43
...Time Protecting Your Wireless LAN encryption vlan 40 mode ciphers tkip ! speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48 54.0 rts threshold 4000 station-role root infrastructure-client bridge-group 1 ! ip http server ip http help-path http://www.cisco....acct-port 1646 key 7 135445415F59 radius-server authorization permit missing Service-Type radius-server vsa send accounting bridge 1 route ip ! end Cisco 3200 Series Wireless MIC Software Configuration Guide 9 ssid no_security-ssid ! ! interface FastEthernet0 no ip address no ip route-cache bridge-group...
...Time Protecting Your Wireless LAN encryption vlan 40 mode ciphers tkip ! speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48 54.0 rts threshold 4000 station-role root infrastructure-client bridge-group 1 ! ip http server ip http help-path http://www.cisco....acct-port 1646 key 7 135445415F59 radius-server authorization permit missing Service-Type radius-server vsa send accounting bridge 1 route ip ! end Cisco 3200 Series Wireless MIC Software Configuration Guide 9 ssid no_security-ssid ! ! interface FastEthernet0 no ip address no ip route-cache bridge-group...
Software Guide
Page 44
Protecting Your Wireless LAN Configuring the WMIC for the First Time Cisco 3200 Series Wireless MIC Software Configuration Guide 10
Protecting Your Wireless LAN Configuring the WMIC for the First Time Cisco 3200 Series Wireless MIC Software Configuration Guide 10
Software Guide
Page 54
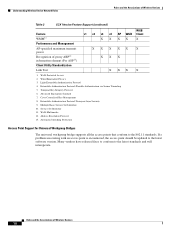
...Utility Standardization XXXX XXX Link Test XX 1. Multiple Basic Service Set Identifier 10. Wi-Fi Protected Access 2. Light Extensible Authentication Protocol 4. Wi-Fi Multimedia 12. Automatic Switching Protection WGB X X X WGB Client X X X Access Point Support for Universal Workgroup Bridges .... Extensible Authentication Protocol-Flexible Authentication via Secure Tunneling 5. Wired Equivalent Privacy 3. Temporal Key Integrity Protocol 6. Cisco Centralized Key Management 8. If a problem associating with an access point is encountered, the access point should be updated ...
...Utility Standardization XXXX XXX Link Test XX 1. Multiple Basic Service Set Identifier 10. Wi-Fi Protected Access 2. Light Extensible Authentication Protocol 4. Wi-Fi Multimedia 12. Automatic Switching Protection WGB X X X WGB Client X X X Access Point Support for Universal Workgroup Bridges .... Extensible Authentication Protocol-Flexible Authentication via Secure Tunneling 5. Wired Equivalent Privacy 3. Temporal Key Integrity Protocol 6. Cisco Centralized Key Management 8. If a problem associating with an access point is encountered, the access point should be updated ...
Software Guide
Page 69
...Step 5 Command configure terminal banner login c message c end show running-config copy running-config startup-config Purpose Enters global configuration mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 5 For message, enter a login message up to appear on all connected terminals. Note For...character of the banner text. The delimiting character signifies the beginning and end of your username and password. $ bridge(config)# Protecting Access to a network or network device. Returns to configure a login banner for Release 12.2. This example shows how to ...
...Step 5 Command configure terminal banner login c message c end show running-config copy running-config startup-config Purpose Enters global configuration mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 5 For message, enter a login message up to appear on all connected terminals. Note For...character of the banner text. The delimiting character signifies the beginning and end of your username and password. $ bridge(config)# Protecting Access to a network or network device. Returns to configure a login banner for Release 12.2. This example shows how to ...
Software Guide
Page 70
... enable password, you should use extreme care when using this command. The password is level 15 (privileged EXEC level). Protecting Access to Privileged EXEC Commands Administering the WMIC This section describes how to control access to the privileged EXEC mode. The... the enable password, but you are locked out of the EXEC mode. Default password is Cisco. The default enable password is Cisco. Default password is written to the configuration file. Cisco 3200 Series Wireless MIC Software Configuration Guide 6 Default Password and Privilege Level Configuration Table 2 ...
... enable password, you should use extreme care when using this command. The password is level 15 (privileged EXEC level). Protecting Access to Privileged EXEC Commands Administering the WMIC This section describes how to control access to the privileged EXEC mode. The... the enable password, but you are locked out of the EXEC mode. Default password is Cisco. The default enable password is Cisco. Default password is written to the configuration file. Cisco 3200 Series Wireless MIC Software Configuration Guide 6 Default Password and Privilege Level Configuration Table 2 ...
Software Guide
Page 71
...not encrypted and can establish an encrypted password that you configure the enable secret command, it allows spaces but ignores leading spaces. Cisco 3200 Series Wireless MIC Software Configuration Guide 7 We recommend that users must enter to access privileged EXEC mode (the default) ...-config Purpose Enters global configuration mode. If you use either the enable password or the enable secret command. Administering the WMIC Protecting Access to Privileged EXEC Commands To set or change a static enable password, follow these steps, beginning in the configuration file....
...not encrypted and can establish an encrypted password that you configure the enable secret command, it allows spaces but ignores leading spaces. Cisco 3200 Series Wireless MIC Software Configuration Guide 7 We recommend that users must enter to access privileged EXEC mode (the default) ...-config Purpose Enters global configuration mode. If you use either the enable password or the enable secret command. Administering the WMIC Protecting Access to Privileged EXEC Commands To set or change a static enable password, follow these steps, beginning in the configuration file....
Software Guide
Page 72
...The default level is from another WMIC configuration. For more information, see the "Configuring Multiple Privilege Levels" section on page 10. Protecting Access to define a password for a specific privilege level. You cannot recover a lost encrypted password by any method. (Optional) ...being readable in global configuration mode. By default, no password is defined. • (Optional) For encryption-type, only type 5, a Cisco proprietary encryption algorithm, is written. To disable password encryption, use the no enable password [level level] or no service password-encryption command ...
...The default level is from another WMIC configuration. For more information, see the "Configuring Multiple Privilege Levels" section on page 10. Protecting Access to define a password for a specific privilege level. You cannot recover a lost encrypted password by any method. (Optional) ...being readable in global configuration mode. By default, no password is defined. • (Optional) For encryption-type, only type 5, a Cisco proprietary encryption algorithm, is written. To disable password encryption, use the no enable password [level level] or no service password-encryption command ...
Software Guide
Page 73
The password must be from 0 to 15. Cisco 3200 Series Wireless MIC Software Configuration Guide 9 If you have at login time. Enters the username, privilege level, and password for a specific user, use the ... and Password Pairs You can configure username and password pairs, which are locally stored on the username specified in the configuration file. Administering the WMIC Protecting Access to Privileged EXEC Commands This example shows how to configure the encrypted password $1$FaD0$Xyti5Rkls3LoyxzS8 for the only username, you can be locked out...
The password must be from 0 to 15. Cisco 3200 Series Wireless MIC Software Configuration Guide 9 If you have at login time. Enters the username, privilege level, and password for a specific user, use the ... and Password Pairs You can configure username and password pairs, which are locally stored on the username specified in the configuration file. Administering the WMIC Protecting Access to Privileged EXEC Commands This example shows how to configure the encrypted password $1$FaD0$Xyti5Rkls3LoyxzS8 for the only username, you can be locked out...
Software Guide
Page 74
...For example, if you set a command to a privilege level, all commands whose syntax is for normal user EXEC mode privileges. Cisco 3200 Series Wireless MIC Software Configuration Guide 10 Level 1 is a subset of that command are automatically set the show ip route command...level level password end show running -config startup-config Purpose Enters global configuration mode. Protecting Access to Privileged EXEC Commands Administering the WMIC Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of access permitted by the enable password. • ...
...For example, if you set a command to a privilege level, all commands whose syntax is for normal user EXEC mode privileges. Cisco 3200 Series Wireless MIC Software Configuration Guide 10 Level 1 is a subset of that command are automatically set the show ip route command...level level password end show running -config startup-config Purpose Enters global configuration mode. Protecting Access to Privileged EXEC Commands Administering the WMIC Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of access permitted by the enable password. • ...
Software Guide
Page 75
...are applied to an interface, and no more SSIDs to eliminate the conflict. If a security setting for an SSID conflicts with Wi-Fi Protected Access (WPA) authentication cannot be created because of your network. If you do not use level 14 commands: bridge(config)# privilege exec ...Cipher Suites and WEP") • Dynamic WEP authentication (see Authentication Types) Using VLANs Assign SSIDs to the VLANs on the wireless LAN. Cisco 3200 Series Wireless MIC Software Configuration Guide 11 For level, the range is created with VLANs disabled, an additional SSID with another SSID, ...
...are applied to an interface, and no more SSIDs to eliminate the conflict. If a security setting for an SSID conflicts with Wi-Fi Protected Access (WPA) authentication cannot be created because of your network. If you do not use level 14 commands: bridge(config)# privilege exec ...Cipher Suites and WEP") • Dynamic WEP authentication (see Authentication Types) Using VLANs Assign SSIDs to the VLANs on the wireless LAN. Cisco 3200 Series Wireless MIC Software Configuration Guide 11 For level, the range is created with VLANs disabled, an additional SSID with another SSID, ...