Software Guide
Page 70
... Enable Policy Lookup Perform these steps to use a particular transform set for protecting data flow. Example: Router(config)# aaa authentication login rtr-remote local Router(config)# This example uses a local authentication database. Configure IPsec Transforms and ...users at both peers' configurations. This example implements a username of Cisco with an encrypted password of authorization. For details, see the Cisco IOS Security Configuration Guide and Cisco IOS Security Command Reference. Cisco Secure Router 520 Series Software Configuration Guide 6-6 OL-14210-01
... Enable Policy Lookup Perform these steps to use a particular transform set for protecting data flow. Example: Router(config)# aaa authentication login rtr-remote local Router(config)# This example uses a local authentication database. Configure IPsec Transforms and ...users at both peers' configurations. This example implements a username of Cisco with an encrypted password of authorization. For details, see the Cisco IOS Security Configuration Guide and Cisco IOS Security Command Reference. Cisco Secure Router 520 Series Software Configuration Guide 6-6 OL-14210-01
Software Guide
Page 81
... Configure a VPN Enable Policy Lookup Perform these steps to the protected traffic as a part of both peers. Example: Router(config)# aaa authentication login rtr-remote local Router(config)# This example uses a local authentication database. When such ...AAA access control model. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide 7-5 aaa authorization {network | exec | commands Specifies AAA authorization of cisco. Example: Router(config)# aaa authorization network rtr-remote local Router(config)# This example uses a local authorization ...
... Configure a VPN Enable Policy Lookup Perform these steps to the protected traffic as a part of both peers. Example: Router(config)# aaa authentication login rtr-remote local Router(config)# This example uses a local authentication database. When such ...AAA access control model. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide 7-5 aaa authorization {network | exec | commands Specifies AAA authorization of cisco. Example: Router(config)# aaa authorization network rtr-remote local Router(config)# This example uses a local authorization ...
Software Guide
Page 90
... Ethernet LAN interface (the inside interface for NAT) 3 PPPoE or PPPoA client and firewall implementation-Cisco Secure Router 520 Series router 4 Point at which NAT occurs 5 Protected network 6 Unprotected network 7 Fast Ethernet or ATM WAN interface (the outside WAN interface (FE4) and protects the Fast Ethernet LAN on FE0 by filtering and inspecting all traffic entering the...
... Ethernet LAN interface (the inside interface for NAT) 3 PPPoE or PPPoA client and firewall implementation-Cisco Secure Router 520 Series router 4 Point at which NAT occurs 5 Protected network 6 Unprotected network 7 Fast Ethernet or ATM WAN interface (the outside WAN interface (FE4) and protects the Fast Ethernet LAN on FE0 by filtering and inspecting all traffic entering the...
Software Guide
Page 96
You may have also configured DHCP, VLANs, and secure tunnels. See the Cisco IOS Commands for Access Points and Bridges for clients. Note The procedures in this network scenario: • Configure the Root ...assume that you have already configured basic router features as well as PPPoE or PPPoA with NAT," as Light Extensible Authentication Protocol [LEAP], Extensible Authentication Protocol-Transport Layer Security [EAP-TLS], or Protected Extensible Authentication Protocol [PEAP]) can use the access point. Cisco Secure Router 520 Series Software Configuration Guide 9-2 OL-14210-...
You may have also configured DHCP, VLANs, and secure tunnels. See the Cisco IOS Commands for Access Points and Bridges for clients. Note The procedures in this network scenario: • Configure the Root ...assume that you have already configured basic router features as well as PPPoE or PPPoA with NAT," as Light Extensible Authentication Protocol [LEAP], Extensible Authentication Protocol-Transport Layer Security [EAP-TLS], or Protected Extensible Authentication Protocol [PEAP]) can use the access point. Cisco Secure Router 520 Series Software Configuration Guide 9-2 OL-14210-...
Software Guide
Page 110
... IPsec and GRE configuration, see the EZVPN Server feature document. Configuring Cisco IOS Firewall IDS Chapter 11 Configuring Security Features Configuring Cisco IOS Firewall IDS Cisco IOS Firewall Intrusion Detection System (IDS) technology enhances perimeter firewall protection by Cisco Secure Router 520 Series routers, see the "Configuring IPsec Network Security" chapter of misuse in -line intrusion detection sensor, watching packets and...
... IPsec and GRE configuration, see the EZVPN Server feature document. Configuring Cisco IOS Firewall IDS Chapter 11 Configuring Security Features Configuring Cisco IOS Firewall IDS Cisco IOS Firewall Intrusion Detection System (IDS) technology enhances perimeter firewall protection by Cisco Secure Router 520 Series routers, see the "Configuring IPsec Network Security" chapter of misuse in -line intrusion detection sensor, watching packets and...
Software Guide
Page 127
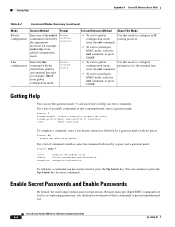
... mode, enter the disable • Configure your router configuration, access to this mode should be protected with a password as described in "Enable Secret Passwords and Enable Passwords" later in this guide. Router (config)# Interface configuration Enter the interface command (with...EXEC Access Method Begin a session with your exit or end command, or router as a whole. and serial interfaces or • To exit to your router. command. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide A-3 operating parameters. • To enter global configuration...
... mode, enter the disable • Configure your router configuration, access to this mode should be protected with a password as described in "Enable Secret Passwords and Enable Passwords" later in this guide. Router (config)# Interface configuration Enter the interface command (with...EXEC Access Method Begin a session with your exit or end command, or router as a whole. and serial interfaces or • To exit to your router. command. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide A-3 operating parameters. • To enter global configuration...
Software Guide
Page 128
... can continue to press the Up Arrow key for example, line 0, from global configuration mode. Cisco Secure Router 520 Series Software Configuration Guide A-4 OL-14210-01 Enable Secret Passwords and Enable Passwords By default, the router ships without password protection. To redisplay a command you enter commands. Router (configrouter)# Line configuration Enter the line command with no space...
... can continue to press the Up Arrow key for example, line 0, from global configuration mode. Cisco Secure Router 520 Series Software Configuration Guide A-4 OL-14210-01 Enable Secret Passwords and Enable Passwords By default, the router ships without password protection. To redisplay a command you enter commands. Router (configrouter)# Line configuration Enter the line command with no space...
Software Guide
Page 135
...a network topology in clear text (not scrambled or encrypted). • PAP provides no protection from playback or repeated trial-and-error attacks. • The remote office router controls the frequency and timing of IP addresses, asynchronous (start/stop) and bit-oriented synchronous...IP traffic over point-to-point links. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide B-3 After the PPP link is established, the corporate office router sends a challenge message to the remote office router. CHAP has the following characteristics: • The password portion...
...a network topology in clear text (not scrambled or encrypted). • PAP provides no protection from playback or repeated trial-and-error attacks. • The remote office router controls the frequency and timing of IP addresses, asynchronous (start/stop) and bit-oriented synchronous...IP traffic over point-to-point links. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide B-3 After the PPP link is established, the corporate office router sends a challenge message to the remote office router. CHAP has the following characteristics: • The password portion...
Software Guide
Page 159
...overloading, defined B-6 OL-14210-01 Index P packets, ATM, displaying 12-7 PAP B-3 parameters, setting up global 1-4 Password Authentication Protocol See PAP password protection A-4 passwords recovery 12-9 to 12-12 resetting 12-11 setting A-4 permanent virtual circuit See PVC permit command B-9 ping atm interface command 12-2 Point...PPPoE client 3-1 configuration example 3-8 configuring 3-1 verifying your configuration 3-8 prerequisites, for configuration 1-2 privileged EXEC commands, accessing A-5 privileged EXEC mode A-2, A-3 Cisco Secure Router 520 Series Software Configuration Guide IN-5
...overloading, defined B-6 OL-14210-01 Index P packets, ATM, displaying 12-7 PAP B-3 parameters, setting up global 1-4 Password Authentication Protocol See PAP password protection A-4 passwords recovery 12-9 to 12-12 resetting 12-11 setting A-4 permanent virtual circuit See PVC permit command B-9 ping atm interface command 12-2 Point...PPPoE client 3-1 configuration example 3-8 configuring 3-1 verifying your configuration 3-8 prerequisites, for configuration 1-2 privileged EXEC commands, accessing A-5 privileged EXEC mode A-2, A-3 Cisco Secure Router 520 Series Software Configuration Guide IN-5