User Manual
Page 1
Internet Security Router User's Manual Revision 1.1 Oct. 30, 2003
Internet Security Router User's Manual Revision 1.1 Oct. 30, 2003
User Manual
Page 17
Internet Security Router User's Manual Chapter 1. Introduction 1 Introduction Congratulations on becoming the owner of Ethernet-connected computers at one site. 1.3.2 Typographical conventions „ Italics are used to identify terms that ... for items you select from menus and drop-down lists, and text strings you are used interchangeably to refer to specific instructions or explanations. This User Manual will now be able to access the Internet using your high-speed broadband connection such as Internet Explorer v5.5 or later. 1.3 Using this product. 1.1 Features...
Internet Security Router User's Manual Chapter 1. Introduction 1 Introduction Congratulations on becoming the owner of Ethernet-connected computers at one site. 1.3.2 Typographical conventions „ Italics are used to identify terms that ... for items you select from menus and drop-down lists, and text strings you are used interchangeably to refer to specific instructions or explanations. This User Manual will now be able to access the Internet using your high-speed broadband connection such as Internet Explorer v5.5 or later. 1.3 Using this product. 1.1 Features...
User Manual
Page 18
WARNING Provides messages of high importance, including messages relating to many readers. These terms are also included in the Glossary. Chapter 1. Definition Explains terms or acronyms that may be unfamiliar to personal safety or system integrity. 2 Introduction Internet Security Router User's Manual Note Provides clarification or non-essential information on the current topic.
WARNING Provides messages of high importance, including messages relating to many readers. These terms are also included in the Glossary. Chapter 1. Definition Explains terms or acronyms that may be unfamiliar to personal safety or system integrity. 2 Introduction Internet Security Router User's Manual Note Provides clarification or non-essential information on the current topic.
User Manual
Page 19
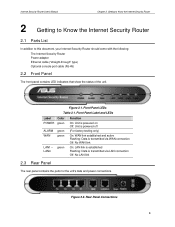
... connections. Rear Panel Connections 3 Front Panel Label and LEDs Label Color POWER green ALARM green WAN green LAN1 - Front Panel LEDs Table 2.1. Internet Security Router User's Manual Chapter 2. Figure 2.2. Getting to Know the Internet Security Router 2 Getting to Know the Internet Security Router 2.1 Parts List In addition to this document, your Internet...
... connections. Rear Panel Connections 3 Front Panel Label and LEDs Label Color POWER green ALARM green WAN green LAN1 - Front Panel LEDs Table 2.1. Internet Security Router User's Manual Chapter 2. Figure 2.2. Getting to Know the Internet Security Router 2 Getting to Know the Internet Security Router 2.1 Parts List In addition to this document, your Internet...
User Manual
Page 20
... host various services such as implemented in the map. „ Dynamic NAT - The Internet Security Router Firewall also provides reverse NAT capability, which enables SOHO users to the supplied power adapter Reset Resets the device CONSOLE RJ-45 serial port for translation. Also called IP Masquerading. P4 Connects to a globally valid... unregistered IP addresses of globally valid Internet IP addresses (n) with the globally valid Internet address; Getting to Know the Internet Security Router Internet Security Router User's Manual Table 2.2.
... host various services such as implemented in the map. „ Dynamic NAT - The Internet Security Router Firewall also provides reverse NAT capability, which enables SOHO users to the supplied power adapter Reset Resets the device CONSOLE RJ-45 serial port for translation. Also called IP Masquerading. P4 Connects to a globally valid... unregistered IP addresses of globally valid Internet IP addresses (n) with the globally valid Internet address; Getting to Know the Internet Security Router Internet Security Router User's Manual Table 2.2.
User Manual
Page 21
...the wild card for composing filter rules „ Filter Rule priorities „ Time based filters „ Application specific filters „ User group based filters for network security. This provides a solution which is a very appropriate measure for providing isolation of one of all ...Firewall provides protection from passing or allows it to Know the Internet Security Router „ Reverse Static - Internet Security Router User's Manual Chapter 2 Getting to pass based on different internal machines. All packets coming to the router can be used program to remotely...
...the wild card for composing filter rules „ Filter Rule priorities „ Time based filters „ Application specific filters „ User group based filters for network security. This provides a solution which is a very appropriate measure for providing isolation of one of all ...Firewall provides protection from passing or allows it to Know the Internet Security Router „ Reverse Static - Internet Security Router User's Manual Chapter 2 Getting to pass based on different internal machines. All packets coming to the router can be used program to remotely...
User Manual
Page 22
...for blocking „ ActiveX „ Java Archive „ Java Applets „ Microsoft Archives „ URLs based on network users access to generate custom reports. The Internet Security Router Firewall can define HTTP extension based filtering schemes for applications and open connections ... on the respective application parameter. You can also forward Syslog information to Know the Internet Security Router Internet Security Router User's Manual Port Scans TCP Attacks Protection with PF Rules Miscellaneous Attacks Flooder TCP XMAS Scan, TCP Null Scan TCP SYN Scan...
...for blocking „ ActiveX „ Java Archive „ Java Applets „ Microsoft Archives „ URLs based on network users access to generate custom reports. The Internet Security Router Firewall can define HTTP extension based filtering schemes for applications and open connections ... on the respective application parameter. You can also forward Syslog information to Know the Internet Security Router Internet Security Router User's Manual Port Scans TCP Attacks Protection with PF Rules Miscellaneous Attacks Flooder TCP XMAS Scan, TCP Null Scan TCP SYN Scan...
User Manual
Page 23
...Support Hardware Encryption Algorithm DES, 3DES Hardware Authentication Algorithm MD5, SHA-1 Transforms ESP, AH Key Management IKE (Pre-shared key), Manual Mode configuration for action. „ Supports the UNIX Syslog format. „ Sends log report e-mails as , the Internet comes...Router is authenticated successfully, the Internet Security Router Firewall dynamically activates the usergroup's set of access policies. Internet Security Router User's Manual Chapter 2 Getting to Know the Internet Security Router „ Alerts sent to the administrator via VPN are encrypted to all...
...Support Hardware Encryption Algorithm DES, 3DES Hardware Authentication Algorithm MD5, SHA-1 Transforms ESP, AH Key Management IKE (Pre-shared key), Manual Mode configuration for action. „ Supports the UNIX Syslog format. „ Sends log report e-mails as , the Internet comes...Router is authenticated successfully, the Internet Security Router Firewall dynamically activates the usergroup's set of access policies. Internet Security Router User's Manual Chapter 2 Getting to Know the Internet Security Router „ Alerts sent to the administrator via VPN are encrypted to all...
User Manual
Page 24
... of Internet Service Providers. At the same time, VPNs allow mobile workers, telecommuters and day extenders to Know the Internet Security Router Internet Security Router User's Manual „ Remote Access VPN - Chapter 2.
... of Internet Service Providers. At the same time, VPNs allow mobile workers, telecommuters and day extenders to Know the Internet Security Router Internet Security Router User's Manual „ Remote Access VPN - Chapter 2.
User Manual
Page 25
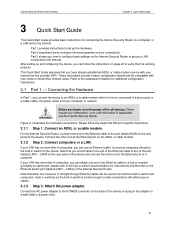
... built-in switch and computers, hubs or switches as the built-in the adapter to a hub or a switch (probably an uplink port; Internet Security Router User's Manual Chapter 3. Refer to the Ethernet switch port (labeled LAN1 - LAN4 on the device. Attach the power adapter. This Quick Start Guide assumes that you can...
... built-in switch and computers, hubs or switches as the built-in the adapter to a hub or a switch (probably an uplink port; Internet Security Router User's Manual Chapter 3. Refer to the Ethernet switch port (labeled LAN1 - LAN4 on the device. Attach the power adapter. This Quick Start Guide assumes that you can...
User Manual
Page 26
... data from your computer(s) and any LAN devices such as indicated in Table 3.1. LED Indicators This LED: POWER LAN1 - Quick Start Guide Internet Security Router User's Manual 3.1.4 Step 4. Turn on the Internet Security Router, the ADSL or cable modem and power up your LAN computer. Table 3.1. Solid green to indicate that the...
... data from your computer(s) and any LAN devices such as indicated in Table 3.1. LED Indicators This LED: POWER LAN1 - Quick Start Guide Internet Security Router User's Manual 3.1.4 Step 4. Turn on the Internet Security Router, the ADSL or cable modem and power up your LAN computer. Table 3.1. Solid green to indicate that the...
User Manual
Page 27
Note In some cases, you may want to configure network settings manually to some or all required Internet settings to your computers to the operating system installed on your network interface card (NIC) and select Properties. (Often ... the LEDs illuminate as an installed component, click button. 5. In the LAN or High-Speed Internet window, right-click on your PCs. Internet Security Router User's Manual Chapter 3. See "Assigning static IP addresses to your PCs" in the Network Protocols list, and then click button. 11 In the Internet Protocol (TCP/IP...
Note In some cases, you may want to configure network settings manually to some or all required Internet settings to your computers to the operating system installed on your network interface card (NIC) and select Properties. (Often ... the LEDs illuminate as an installed component, click button. 5. In the LAN or High-Speed Internet window, right-click on your PCs. Internet Security Router User's Manual Chapter 3. See "Assigning static IP addresses to your PCs" in the Network Protocols list, and then click button. 11 In the Internet Protocol (TCP/IP...
User Manual
Page 28
... Connections window, right-click the Local Area Connection icon, and then select Properties. 10. Double-click the Network icon. Quick Start Guide Internet Security Router User's Manual You may have to scroll down the list to add the default gateway entry. 11. In the Windows task bar, click the button, point to...
... Connections window, right-click the Local Area Connection icon, and then select Properties. 10. Double-click the Network icon. Quick Start Guide Internet Security Router User's Manual You may have to scroll down the list to add the default gateway entry. 11. In the Windows task bar, click the button, point to...
User Manual
Page 29
...to confirm and save your changes, and then close the Control Panel. 3.2.6 Assigning static IP addresses to your PCs In some cases, you manually assign IP information to all files are using a computer as the Internet Security Router's LAN port. In the Windows NT task bar, ...click the button, point to install files from a DHCP server. 11. If TCP/IP does not display as 192.168.1.1. Internet Security Router User's Manual Chapter 3. In the Control Panel window, double click the Network icon. 3. You may want to establish connection between the Internet Security Router and ...
...to confirm and save your changes, and then close the Control Panel. 3.2.6 Assigning static IP addresses to your PCs In some cases, you manually assign IP information to all files are using a computer as the Internet Security Router's LAN port. In the Windows NT task bar, ...click the button, point to install files from a DHCP server. 11. If TCP/IP does not display as 192.168.1.1. Internet Security Router User's Manual Chapter 3. In the Control Panel window, double click the Network icon. 3. You may want to establish connection between the Internet Security Router and ...
User Manual
Page 30
... Configuration pages guided by Setup Wizard. In IE, click "Tools" è "Internet Options..." è "Connections" tab è "LAN settings..." Quick Start Guide Internet Security Router User's Manual 3.3 Part 3 - Note the intent here is to the next configuration page. and then uncheck "Use proxy server for your PC is disabled in your browser...
... Configuration pages guided by Setup Wizard. In IE, click "Tools" è "Internet Options..." è "Connections" tab è "LAN settings..." Quick Start Guide Internet Security Router User's Manual 3.3 Part 3 - Note the intent here is to the next configuration page. and then uncheck "Use proxy server for your PC is disabled in your browser...
User Manual
Page 31
..., and then click to save the changes. 15 The Setup Wizard home page displays each time you log into this program, use these defaults: Default User Name: Default Password: admin admin Note You can change the password at any changes for the passwords and click the button to enter the Configuration... Password on the button to the next configuration page by clicking on page 15). Figure 3.3. Click on page 124). Quick Start Guide 3. Internet Security Router User's Manual Chapter 3.
..., and then click to save the changes. 15 The Setup Wizard home page displays each time you log into this program, use these defaults: Default User Name: Default Password: admin admin Note You can change the password at any changes for the passwords and click the button to enter the Configuration... Password on the button to the next configuration page by clicking on page 15). Figure 3.3. Click on page 124). Quick Start Guide 3. Internet Security Router User's Manual Chapter 3.
User Manual
Page 32
... the changes. Date/Time Configuration Page 6. button to go to the next configuration page. 16 Click on the button. Quick Start Guide Internet Security Router User's Manual 5. Setup Wizard - Set the time zone for the Internet Security Router by clicking on the button to proceed to There is no need to set...
... the changes. Date/Time Configuration Page 6. button to go to the next configuration page. 16 Click on the button. Quick Start Guide Internet Security Router User's Manual 5. Setup Wizard - Set the time zone for the Internet Security Router by clicking on the button to proceed to There is no need to set...
User Manual
Page 33
... 3.7. Setup Wizard - Depending on the button to proceed to configure the WAN settings for the Internet Security Router. DHCP Server Configuration Page 8. Internet Security Router User's Manual Chapter 3.
... 3.7. Setup Wizard - Depending on the button to proceed to configure the WAN settings for the Internet Security Router. DHCP Server Configuration Page 8. Internet Security Router User's Manual Chapter 3.
User Manual
Page 34
However, if you may enter them in the space provided. 18 Chapter 3. Quick Start Guide Internet Security Router User's Manual Connection Mode dropdown list Figure 3.9. Setup Wizard - WAN Dynamic IP Configuration Page a) PPPoE Connection Mode (see Figure 3.9) • You don't need to enter primary/secondary DNS IP addresses as PPPoE is able to automatically obtain this information for you from your favorite DNS servers, you prefer to use your ISP. Setup Wizard - WAN PPPoE Configuration Page Connection Mode dropdown list Figure 3.10.
However, if you may enter them in the space provided. 18 Chapter 3. Quick Start Guide Internet Security Router User's Manual Connection Mode dropdown list Figure 3.9. Setup Wizard - WAN Dynamic IP Configuration Page a) PPPoE Connection Mode (see Figure 3.9) • You don't need to enter primary/secondary DNS IP addresses as PPPoE is able to automatically obtain this information for you from your favorite DNS servers, you prefer to use your ISP. Setup Wizard - WAN PPPoE Configuration Page Connection Mode dropdown list Figure 3.10.
User Manual
Page 35
... and password provided by your ISP. You may enter them in the IP Address field. Internet Security Router User's Manual Chapter 3. This information should be provided by your ISP. • Enter Subnet Mask for the WAN. You may leave it empty if your ISP did ...
... and password provided by your ISP. You may enter them in the IP Address field. Internet Security Router User's Manual Chapter 3. This information should be provided by your ISP. • Enter Subnet Mask for the WAN. You may leave it empty if your ISP did ...