User Manual
Page 1
Internet Security Router User's Manual Revision 1.1 Oct. 30, 2003
Internet Security Router User's Manual Revision 1.1 Oct. 30, 2003
User Manual
Page 3
... or a LAN 9 3.1.3 Step 3. Table of Contents 1 Introduction 1 1.1 Features ...1 1.2 System Requirements 1 1.3 Using this Document 1 1.3.1 Notational conventions 1 1.3.2 Typographical conventions 1 1.3.3 Special messages 1 2 Getting to Know the Internet Security Router 3 2.1 Parts List ...3 2.2 Front Panel...3 2.3 Rear Panel ...3 2.4 Major Features...4 2.4.1 Firewall Features 4 2.4.1.1 Address Sharing and Management 4 2.4.1.1 ACL (Access Control List 5 2.4.1.2 Stateful Packet Inspection 5 2.4.1.3 Defense against DoS Attacks...
... or a LAN 9 3.1.3 Step 3. Table of Contents 1 Introduction 1 1.1 Features ...1 1.2 System Requirements 1 1.3 Using this Document 1 1.3.1 Notational conventions 1 1.3.2 Typographical conventions 1 1.3.3 Special messages 1 2 Getting to Know the Internet Security Router 3 2.1 Parts List ...3 2.2 Front Panel...3 2.3 Rear Panel ...3 2.4 Major Features...4 2.4.1 Firewall Features 4 2.4.1.1 Address Sharing and Management 4 2.4.1.1 ACL (Access Control List 5 2.4.1.2 Stateful Packet Inspection 5 2.4.1.3 Defense against DoS Attacks...
User Manual
Page 4
... or cable modem and power up your PCs 13 3.3 Part 3 - Quick Configuration of the Internet Security Router 14 3.3.1 Buttons Used in Setup Wizard 14 3.3.2 Setting Up the Internet Security Router 14 3.3.3 Testing Your Setup 20 3.3.4 Default Router Settings 20 4 Getting Started with the Configuration Manager 21 4.1 Log into Configuration Manager 21 4.2 Functional Layout...
... or cable modem and power up your PCs 13 3.3 Part 3 - Quick Configuration of the Internet Security Router 14 3.3.1 Buttons Used in Setup Wizard 14 3.3.2 Setting Up the Internet Security Router 14 3.3.3 Testing Your Setup 20 3.3.4 Default Router Settings 20 4 Getting Started with the Configuration Manager 21 4.1 Log into Configuration Manager 21 4.2 Functional Layout...
User Manual
Page 9
... ...95 10.6 VPN Connection Examples 96 10.6.1 Intranet Scenario - firewall + VPN and no NAT for VPN traffic 96 10.6.1.1 Configure Rules on Internet Security Router 1 (ISR1 97 10.6.1.2 Configure Rules on ISR2 104 10.6.2.4 Establish Tunnel and Verify 107 11 Configuring Remote Access 109 11.1 Remote Access 109 11.2 Manage... Users 117 11.6.4 Delete Virtual IP Address for Remote Access Users 117 11.7 Configure VPN for VPN traffic .......... 100 10.6.2.1 Setup the Internet Security Routers 101 10.6.2.2 Configure VPN Rules on ISR1 102 10.6.2.3 Configure VPN Rules on Internet Security...
... ...95 10.6 VPN Connection Examples 96 10.6.1 Intranet Scenario - firewall + VPN and no NAT for VPN traffic 96 10.6.1.1 Configure Rules on Internet Security Router 1 (ISR1 97 10.6.1.2 Configure Rules on ISR2 104 10.6.2.4 Establish Tunnel and Verify 107 11 Configuring Remote Access 109 11.1 Remote Access 109 11.2 Manage... Users 117 11.6.4 Delete Virtual IP Address for Remote Access Users 117 11.7 Configure VPN for VPN traffic .......... 100 10.6.2.1 Setup the Internet Security Routers 101 10.6.2.2 Configure VPN Rules on ISR1 102 10.6.2.3 Configure VPN Rules on Internet Security...
User Manual
Page 10
... 126 12.5.1 Reset System Configuration 126 12.5.2 Backup System Configuration 127 12.5.3 Restore System Configuration 127 12.6 Upgrade Firmware 128 12.7 Reset the Internet Security Router 129 12.8 Logout Configuration Manager 130 13 ALG Configuration 131 14 IP Addresses, Network Masks, and Subnets 135 14.1 IP Addresses ...135 14.1.1 Structure of...
... 126 12.5.1 Reset System Configuration 126 12.5.2 Backup System Configuration 127 12.5.3 Restore System Configuration 127 12.6 Upgrade Firmware 128 12.7 Reset the Internet Security Router 129 12.8 Logout Configuration Manager 130 13 ALG Configuration 131 14 IP Addresses, Network Masks, and Subnets 135 14.1 IP Addresses ...135 14.1.1 Structure of...
User Manual
Page 14
... Manager Reset Page 129 Figure 12.11. WAN PPPoE Configuration Parameters 32 Table 6.2. IP Pool Configuration Parameters...73 Table 9.9. VPN Features of the Internet Security Router 7 Table 3.1. Rear Panel Labels and LEDs ...4 Table 2.3. Default Settings Summary...20 Table 4.1. Figure 12.5. Default Setting Configuration Page 126 Figure 12.6. Firmware Upgrade Page ...129...
... Manager Reset Page 129 Figure 12.11. WAN PPPoE Configuration Parameters 32 Table 6.2. IP Pool Configuration Parameters...73 Table 9.9. VPN Features of the Internet Security Router 7 Table 3.1. Rear Panel Labels and LEDs ...4 Table 2.3. Default Settings Summary...20 Table 4.1. Figure 12.5. Default Setting Configuration Page 126 Figure 12.6. Firmware Upgrade Page ...129...
User Manual
Page 15
... 80 Table 10.1. VPN Statistics ...95 Table 10.6. IP Address structure...135 xv Pre-configured IPSec proposals in the Internet Security Router 85 Table 10.2. Outbound Un-translated Firewall Rule for VPN Packets on ISR1 99 Table 10.9. User Group Configuration Parameters 109 Table... 11.2. Group ACL Specific Configuration Parameters 112 Table 13.1. Default Connections in the Internet Security Router 86 Table 10.4. Pre-configured IKE proposals in the Internet Security Router 85 Table 10.3. Inbound Un-translated Firewall Rule for VPN Packets on ISR1 98 Table 10...
... 80 Table 10.1. VPN Statistics ...95 Table 10.6. IP Address structure...135 xv Pre-configured IPSec proposals in the Internet Security Router 85 Table 10.2. Outbound Un-translated Firewall Rule for VPN Packets on ISR1 99 Table 10.9. User Group Configuration Parameters 109 Table... 11.2. Group ACL Specific Configuration Parameters 112 Table 13.1. Default Connections in the Internet Security Router 86 Table 10.4. Pre-configured IKE proposals in the Internet Security Router 85 Table 10.3. Inbound Un-translated Firewall Rule for VPN Packets on ISR1 98 Table 10...
User Manual
Page 17
...via a web browser, such as Microsoft Internet Explorer 5.5, Netscape 7.0.2 or later. 1.2 System Requirements In order to use the Internet Security Router for items you select from menus and drop-down lists, and text strings you type when prompted by the program. 1.3.3 Special messages This... have the following: „ ADSL or cable modem and the corresponding service up and running, with ADSL or cable modem. Internet Security Router User's Manual Chapter 1. Introduction 1 Introduction Congratulations on an Ethernet network. „ For system configuration using your WAN „ One or...
...via a web browser, such as Microsoft Internet Explorer 5.5, Netscape 7.0.2 or later. 1.2 System Requirements In order to use the Internet Security Router for items you select from menus and drop-down lists, and text strings you type when prompted by the program. 1.3.3 Special messages This... have the following: „ ADSL or cable modem and the corresponding service up and running, with ADSL or cable modem. Internet Security Router User's Manual Chapter 1. Introduction 1 Introduction Congratulations on an Ethernet network. „ For system configuration using your WAN „ One or...
User Manual
Page 18
WARNING Provides messages of high importance, including messages relating to many readers. These terms are also included in the Glossary. Definition Explains terms or acronyms that may be unfamiliar to personal safety or system integrity. 2 Introduction Internet Security Router User's Manual Note Provides clarification or non-essential information on the current topic. Chapter 1.
WARNING Provides messages of high importance, including messages relating to many readers. These terms are also included in the Glossary. Definition Explains terms or acronyms that may be unfamiliar to personal safety or system integrity. 2 Introduction Internet Security Router User's Manual Note Provides clarification or non-essential information on the current topic. Chapter 1.
User Manual
Page 19
... WAN green LAN1 - Front Panel LEDs Table 2.1. Getting to Know the Internet Security Router 2 Getting to Know the Internet Security Router 2.1 Parts List In addition to this document, your Internet Security Router should come with the following: „ The Internet Security Router „ Power adapter „ Ethernet cable ("straight-through" type) „ Optional console...
... WAN green LAN1 - Front Panel LEDs Table 2.1. Getting to Know the Internet Security Router 2 Getting to Know the Internet Security Router 2.1 Parts List In addition to this document, your Internet Security Router should come with the following: „ The Internet Security Router „ Power adapter „ Ethernet cable ("straight-through" type) „ Optional console...
User Manual
Page 20
... unregistered IP addresses of multiple connections required for Internet access. The NAT rules drive the translation mechanism at the NAT router. This feature conceals network address and prevents them from the pool of NAT are directly translated with the information contained in ... Filtering „ Log and Alert „ Remote Access „ Keyword based URL Filtering 2.4.1.1 Address Sharing and Management The Internet Security Router Firewall provides NAT to share a single high-speed Internet connection and to save the cost of hosts connected to -one globally valid Internet...
... unregistered IP addresses of multiple connections required for Internet access. The NAT rules drive the translation mechanism at the NAT router. This feature conceals network address and prevents them from the pool of NAT are directly translated with the information contained in ... Filtering „ Log and Alert „ Remote Access „ Keyword based URL Filtering 2.4.1.1 Address Sharing and Management The Internet Security Router Firewall provides NAT to share a single high-speed Internet connection and to save the cost of hosts connected to -one globally valid Internet...
User Manual
Page 21
...individual packet, decodes the header information of Death and all NAT ALGs supported, refer to the internal address. The Internet Security Router Firewall's ACL methodology supports: „ Filtering based on different internal machines. It provides automatic protection from Denial of Service (DoS...8222; Application specific filters „ User group based filters for evaluating subsequent connection attempts. For example, the Internet Security Router Firewall provides protection from known types of the basic building blocks for the security decision from passing or allows it to pass...
...individual packet, decodes the header information of Death and all NAT ALGs supported, refer to the internal address. The Internet Security Router Firewall's ACL methodology supports: „ Filtering based on different internal machines. It provides automatic protection from Denial of Service (DoS...8222; Application specific filters „ User group based filters for evaluating subsequent connection attempts. For example, the Internet Security Router Firewall provides protection from known types of the basic building blocks for the security decision from passing or allows it to pass...
User Manual
Page 22
... such as FTP, games etc., open dynamic associations. which reveal excess information about the recipient. „ RPC - The Internet Security Router Firewall provides a number of ALGs for the site or group of sequence attacks Echo-Chargen, Ascend Kill IP Spoofing, LAND, Targa, ...(ALG), is built to ACL rules. allows you to filter programs based on a private network. As it cannot be defined. The Internet Security Router Firewall supports: 6 Chapter 2. You can be associated to parse packets for blocking „ ActiveX „ Java Archive „ Java Applets &#...
... such as FTP, games etc., open dynamic associations. which reveal excess information about the recipient. „ RPC - The Internet Security Router Firewall provides a number of ALGs for the site or group of sequence attacks Echo-Chargen, Ascend Kill IP Spoofing, LAND, Targa, ...(ALG), is built to ACL rules. allows you to filter programs based on a private network. As it cannot be defined. The Internet Security Router Firewall supports: 6 Chapter 2. You can be associated to parse packets for blocking „ ActiveX „ Java Archive „ Java Applets &#...
User Manual
Page 23
...Aggressive Mode, Quick Mode „ Site-to-Site VPN connection - The following table lists the VPN features supported by the Internet Security Router is used to connect branch offices, home offices, or business partners' sites to all or portions of the parties involved in using the ...IPSec compliant. The VPN supported in the WELF format. „ ICMP logging to show code and type. 2.4.1.8 Remote Access The Internet Security Router Firewall allows the network administrator to segregate the user community into Access Policies per group. Packets sent via e-mail. „ Maintains at an...
...Aggressive Mode, Quick Mode „ Site-to-Site VPN connection - The following table lists the VPN features supported by the Internet Security Router is used to connect branch offices, home offices, or business partners' sites to all or portions of the parties involved in using the ...IPSec compliant. The VPN supported in the WELF format. „ ICMP logging to show code and type. 2.4.1.8 Remote Access The Internet Security Router Firewall allows the network administrator to segregate the user community into Access Policies per group. Packets sent via e-mail. „ Maintains at an...
User Manual
Page 24
.... Deploying a remote access VPN enables corporations to take advantage of Internet Service Providers. Corporations use VPN to establish secure, end-to Know the Internet Security Router Internet Security Router User's Manual „ Remote Access VPN -
.... Deploying a remote access VPN enables corporations to take advantage of Internet Service Providers. Corporations use VPN to establish secure, end-to Know the Internet Security Router Internet Security Router User's Manual „ Remote Access VPN -
User Manual
Page 25
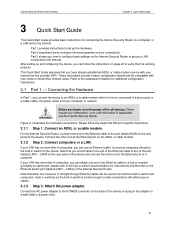
... in the adapter to the hub or switch documentations for specific instructions. 3.1.1 Step 1. Figure 3.1 illustrates the hardware connections. For the Internet Security Router: Connect one end of the device and plug in turn the power off for additional configuration instructions. 3.1 Part 1 - If your home or ...please refer to a wall outlet or a power strip. 9 This Quick Start Guide assumes that follow the instructions on the Internet Security Router to get your LAN has more than 4 computers, you should be used to connect the built-in switch and computers, hubs or ...
... in the adapter to the hub or switch documentations for specific instructions. 3.1.1 Step 1. Figure 3.1 illustrates the hardware connections. For the Internet Security Router: Connect one end of the device and plug in turn the power off for additional configuration instructions. 3.1 Part 1 - If your home or ...please refer to a wall outlet or a power strip. 9 This Quick Start Guide assumes that follow the instructions on the Internet Security Router to get your LAN has more than 4 computers, you should be used to connect the built-in switch and computers, hubs or ...
User Manual
Page 26
...when the device is sending or receiving data from the Internet. 10 Quick Start Guide Internet Security Router User's Manual 3.1.4 Step 4. Overview of the Internet Security Router to the Internet Security Router and if it is turned on and boot up your LAN computer. Figure 3.1. LED Indicators This ...illuminated as hubs or switches. Turn on your computer(s) and any LAN devices such as indicated in Table 3.1. Turn on the Internet Security Router, the ADSL or cable modem and power up your ADSL or cable modem. Chapter 3. LAN4 WAN ...should verify that the device is plugged...
...when the device is sending or receiving data from the Internet. 10 Quick Start Guide Internet Security Router User's Manual 3.1.4 Step 4. Overview of the Internet Security Router to the Internet Security Router and if it is turned on and boot up your LAN computer. Figure 3.1. LED Indicators This ...illuminated as hubs or switches. Turn on your computer(s) and any LAN devices such as indicated in Table 3.1. Turn on the Internet Security Router, the ADSL or cable modem and power up your ADSL or cable modem. Chapter 3. LAN4 WAN ...should verify that the device is plugged...
User Manual
Page 27
...necessary, install it is checked, and click button. 5. If Internet Protocol (TCP/IP) does not display as expected, the Internet Security Router hardware is labeled Local Area Connection). Also click the radio button labeled Obtain DNS server address automatically. 6. Select Internet Protocol (TCP/IP)... icon, and then select Properties. Configuring Your Computers Part 2 of the item labeled Internet Protocol TCP/IP is assigned. Internet Security Router User's Manual Chapter 3. In the LAN or High-Speed Internet window, right-click on your computers to work with a list of...
...necessary, install it is checked, and click button. 5. If Internet Protocol (TCP/IP) does not display as expected, the Internet Security Router hardware is labeled Local Area Connection). Also click the radio button labeled Obtain DNS server address automatically. 6. Select Internet Protocol (TCP/IP)... icon, and then select Properties. Configuring Your Computers Part 2 of the item labeled Internet Protocol TCP/IP is assigned. Internet Security Router User's Manual Chapter 3. In the LAN or High-Speed Internet window, right-click on your computers to work with a list of...
User Manual
Page 28
...box, select Internet Protocol (TCP/IP), and then click button. 11. Click button twice to accept IP information assigned by the Internet Security Router: 8. Next, configure the PCs to confirm and save your changes, and then close the Control Panel. 3.2.4 Windows® 95, 98... Obtain an IP address automatically. Double-click the Network icon. Click button twice to accept IP addresses assigned by the Internet Security Router: 7. Follow the instructions to restart your network adapter, and then click button. If prompted, click button to install the files....
...box, select Internet Protocol (TCP/IP), and then click button. 11. Click button twice to accept IP information assigned by the Internet Security Router: 8. Next, configure the PCs to confirm and save your changes, and then close the Control Panel. 3.2.4 Windows® 95, 98... Obtain an IP address automatically. Double-click the Network icon. Click button twice to accept IP addresses assigned by the Internet Security Router: 7. Follow the instructions to restart your network adapter, and then click button. If prompted, click button to install the files....
User Manual
Page 29
... required) if: „ You have IP addresses that a TCP/IP service called "statically"), rather than allowing the Internet Security Router to assign static information, follow the instructions in the same subnet as an installed component, click button. 5. Skip to Settings, ...DHCP server. 11. After all your PCs directly (often called DHCP can follow the instructions on your true network environment. Internet Security Router User's Manual Chapter 3. In the Network dialog box, click the Protocols tab. 9. This option may be prompted to dynamically assign ...
... required) if: „ You have IP addresses that a TCP/IP service called "statically"), rather than allowing the Internet Security Router to assign static information, follow the instructions in the same subnet as an installed component, click button. 5. Skip to Settings, ...DHCP server. 11. After all your PCs directly (often called DHCP can follow the instructions on your true network environment. Internet Security Router User's Manual Chapter 3. In the Network dialog box, click the Protocols tab. 9. This option may be prompted to dynamically assign ...