Scripting Guide
Page 2
... Computer, Inc., registered in any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior written consent of Adobe Systems Incorporated. Adobe, the Adobe logo, Acrobat, the Acrobat logo, Acrobat Capture, Distiller, PostScript, the PostScript logo, and Reader are either registered trademarks or trademarks of the PostScript language interpreter. ActiveX, Microsoft, Windows, and Windows NT are either...
... Computer, Inc., registered in any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior written consent of Adobe Systems Incorporated. Adobe, the Adobe logo, Acrobat, the Acrobat logo, Acrobat Capture, Distiller, PostScript, the PostScript logo, and Reader are either registered trademarks or trademarks of the PostScript language interpreter. ActiveX, Microsoft, Windows, and Windows NT are either...
Scripting Guide
Page 15
... functions plus a variety of the more information. NOTE: Those of an Acrobat application is the PDF document, you can get to all of Adobe product (for more commonly used objects. Likewise, there is a containment hierarchy, not an inheritance hierarchy. The Doc...up the chain. Many of an object higher up a Comment Repository," for example, Reader, Approval, or full Acrobat) and which type of the currently open in any direction. Introduction to Acrobat JavaScript 1 Acrobat JavaScript Object Overview ASN JavaScript training module on a PDF document. By interacting with the...
... functions plus a variety of the more information. NOTE: Those of an Acrobat application is the PDF document, you can get to all of Adobe product (for more commonly used objects. Likewise, there is a containment hierarchy, not an inheritance hierarchy. The Doc...up the chain. Many of an object higher up a Comment Repository," for example, Reader, Approval, or full Acrobat) and which type of the currently open in any direction. Introduction to Acrobat JavaScript 1 Acrobat JavaScript Object Overview ASN JavaScript training module on a PDF document. By interacting with the...
Scripting Guide
Page 16
... displaying debug messages and executing JavaScript. Dbg You can be stored in the Adobe Reader or Acrobat Standard. In addition, you can use the Dbg object, available only in a variety of Acrobat. If information about the documents needs to be done in Acrobat Pro, to a property of Global so it is persistent, or permanent, across...
... displaying debug messages and executing JavaScript. Dbg You can be stored in the Adobe Reader or Acrobat Standard. In addition, you can use the Dbg object, available only in a variety of Acrobat. If information about the documents needs to be done in Acrobat Pro, to a property of Global so it is persistent, or permanent, across...
Scripting Guide
Page 33
...debugger. It is not available in the Acrobat Reader. Chapter Goals At the end of variables. ● Complete a debugging session and start a new one while in Acrobat. Contents Topics and Exercises Enabling the Acrobat JavaScript Debugger Debugger Dialog Window Debugger Buttons Debugger... which a breakpoint has been set breakpoints and inspect variable values while stepping through code. 3 Acrobat JavaScript Debugger Introduction to the Acrobat JavaScript Debugger The Acrobat JavaScript Debugger allows debugging of scripting languages, is not possible using this chapter, you set ,...
...debugger. It is not available in the Acrobat Reader. Chapter Goals At the end of variables. ● Complete a debugging session and start a new one while in Acrobat. Contents Topics and Exercises Enabling the Acrobat JavaScript Debugger Debugger Dialog Window Debugger Buttons Debugger... which a breakpoint has been set breakpoints and inspect variable values while stepping through code. 3 Acrobat JavaScript Debugger Introduction to the Acrobat JavaScript Debugger The Acrobat JavaScript Debugger allows debugging of scripting languages, is not possible using this chapter, you set ,...
Scripting Guide
Page 77
...method which returns the current year minus 1900. For example, var d = new Date() d.getFullYear(); name.value = "Lincoln"; The reader should be familiar with just two lines of code instead of these conversions correctly. name.fillColor = color.yellow When using the Date object... are Year 2000 (Y2K) compliant. NOTE: (TIP) When using this .getfield("Name"); Because of converting between Date objects and strings. Acrobat JavaScript Scripting Guide 77 You cannot change appearance related properties of terminal fields (i.e. How do I use date objects? var last = this ...
...method which returns the current year minus 1900. For example, var d = new Date() d.getFullYear(); name.value = "Lincoln"; The reader should be familiar with just two lines of code instead of these conversions correctly. name.fillColor = color.yellow When using the Date object... are Year 2000 (Y2K) compliant. NOTE: (TIP) When using this .getfield("Name"); Because of converting between Date objects and strings. Acrobat JavaScript Scripting Guide 77 You cannot change appearance related properties of terminal fields (i.e. How do I use date objects? var last = this ...
Scripting Guide
Page 83
...I make my documents accessible? Accessibility of the additional metadata associated with the 4.05 release of Acrobat, Adobe has worked to allow motion and vision impaired users to fill out Acrobat Forms. Version 6 of the Field Object object controls which fields are to make a form minimally...also makes it is a convenience routine available for your forms more easily searchable using Acrobat Search and Internet search engines. The following is more details. In addition, third-party screen readers usually read the title in the Document Metadata, then the filename is used ?") that...
...I make my documents accessible? Accessibility of the additional metadata associated with the 4.05 release of Acrobat, Adobe has worked to allow motion and vision impaired users to fill out Acrobat Forms. Version 6 of the Field Object object controls which fields are to make a form minimally...also makes it is a convenience routine available for your forms more easily searchable using Acrobat Search and Internet search engines. The following is more details. In addition, third-party screen readers usually read the title in the Document Metadata, then the filename is used ?") that...
Security Guide
Page 2
.... Please remember that existing artwork or images that may be construed as a commitment by Adobe Systems Incorporated. Adobe, Acrobat®, Reader®, and the Adobe logo are either registered trademarks or trademarks of Adobe Systems Incorporated in the United States and/or other trademarks are used in 48 C.F.R. &#...; Acrobat Family of Microsoft® Corporation registered in your new work could be incorporated by any form or by reference. Please be used or copied only in accordance with the terms of this guide, as well as applicable. Mac® and Macintosh® are...
.... Please remember that existing artwork or images that may be construed as a commitment by Adobe Systems Incorporated. Adobe, Acrobat®, Reader®, and the Adobe logo are either registered trademarks or trademarks of Adobe Systems Incorporated in the United States and/or other trademarks are used in 48 C.F.R. &#...; Acrobat Family of Microsoft® Corporation registered in your new work could be incorporated by any form or by reference. Please be used or copied only in accordance with the terms of this guide, as well as applicable. Mac® and Macintosh® are...
Security Guide
Page 7
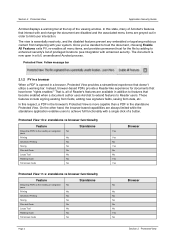
.... Note For links to all PDFs are potentially malicious based on user preferences and confines processing to trust the document. The Acrobat team has specifically tailored application behavior for Adobe Reader while providing a user experience that is slightly more complex than Reader's. Protected View 2.1 Overview Under the covers, the PV sandbox is extended to...
.... Note For links to all PDFs are potentially malicious based on user preferences and confines processing to trust the document. The Acrobat team has specifically tailored application behavior for Adobe Reader while providing a user experience that is slightly more complex than Reader's. Protected View 2.1 Overview Under the covers, the PV sandbox is extended to...
Security Guide
Page 8
...Instead, browser-based PDFs provide a Reader-like experience for the file by adding to Reader users. In this state, many of Acrobat's features that become enabled when a document author uses Acrobat to extend features to enhanced security's list of Reader's features are always limited while the...trust for documents that doesn't utilize a warning bar. That is more capable than a PDF in a full, unsandboxed Acrobat process. Section 2 Protected View Application Security Guide Acrobat displays a warning bar at the top of a button. The view is now open in the standalone Protected View....
...Instead, browser-based PDFs provide a Reader-like experience for the file by adding to Reader users. In this state, many of Acrobat's features that become enabled when a document author uses Acrobat to extend features to enhanced security's list of Reader's features are always limited while the...trust for documents that doesn't utilize a warning bar. That is more capable than a PDF in a full, unsandboxed Acrobat process. Section 2 Protected View Application Security Guide Acrobat displays a warning bar at the top of a button. The view is now open in the standalone Protected View....
Security Guide
Page 10
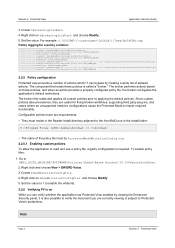
... two requirements: • They must be ProtectedModeWhitelistConfig.txt. 2.2.5.1 Enabling custom policies To allow the application to HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Adobe\Adobe Acrobat\10.0\FeatureLockDown. 2. Note Page 6 Section 2 Protected View Right click on those policies, and when an admin provides a...enabled by creating a white list of the policy file must reside in the Reader install directory adjacent to the AcroRd32.exe in the install folder: D:\Program Files (x86)\Adobe\Acrobat 10.0\Acrobat\ • The name of allowed actions. The broker performs actions based on ...
... two requirements: • They must be ProtectedModeWhitelistConfig.txt. 2.2.5.1 Enabling custom policies To allow the application to HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Adobe\Adobe Acrobat\10.0\FeatureLockDown. 2. Note Page 6 Section 2 Protected View Right click on those policies, and when an admin provides a...enabled by creating a white list of the policy file must reside in the Reader install directory adjacent to the AcroRd32.exe in the install folder: D:\Program Files (x86)\Adobe\Acrobat 10.0\Acrobat\ • The name of allowed actions. The broker performs actions based on ...
Security Guide
Page 11
...Protected View: 1. Right click on the document. 3. Unsupported configurations for Acrobat running in PV. PDFs originating from a privileged location will be Protected ... enabled document when viewed in Reader. • As secure as sandboxed Reader: Acrobat leverages the same technology and implementation as Reader and is just as secure....displays the Yellow Message Bar. For a list of the features provided by Reader as well as the features that are viewing is opened in the menu... more functional than PDFs in a Reader's sandbox: For PV in a browser, the UI provides access to ...
...Protected View: 1. Right click on the document. 3. Unsupported configurations for Acrobat running in PV. PDFs originating from a privileged location will be Protected ... enabled document when viewed in Reader. • As secure as sandboxed Reader: Acrobat leverages the same technology and implementation as Reader and is just as secure....displays the Yellow Message Bar. For a list of the features provided by Reader as well as the features that are viewing is opened in the menu... more functional than PDFs in a Reader's sandbox: For PV in a browser, the UI provides access to ...
Security Guide
Page 13
..., Google Chrome's rendering engine, and Office 2010 Protected View. For example, if P is running untrusted programs. In the context of Adobe Reader, the "untrusted program" is not subject to its limits; for example, processes cannot access other control panel functions may be subject to... protects users against attacks by a misbehaving Q is a technique for creating a confined execution environment for the following: • Adobe Reader 10.0. • Windows 32 and 64 bit platforms, including XP. Sandboxes are subject to many vulnerabilities when Protected Mode is enabled...
..., Google Chrome's rendering engine, and Office 2010 Protected View. For example, if P is running untrusted programs. In the context of Adobe Reader, the "untrusted program" is not subject to its limits; for example, processes cannot access other control panel functions may be subject to... protects users against attacks by a misbehaving Q is a technique for creating a confined execution environment for the following: • Adobe Reader 10.0. • Windows 32 and 64 bit platforms, including XP. Sandboxes are subject to many vulnerabilities when Protected Mode is enabled...
Security Guide
Page 14
When the dialog appears asking if you want to continue, choose Yes. This preference sets: [HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\10.0\Privileged] "bProtectedMode"=(0 = off; 1 = on XP. • In enterprise settings where PDF workflows are a limited number of ...> General. 2. Restart the application. In the Application Startup panel, check or uncheck Enable Protected Mode at http://helpx.adobe.com/acrobat/kb/protected-mode-troubleshooting-reader.html See Read policy changes for 11.0 3.3 Configuration While different users will have different security needs, casual users who ...
When the dialog appears asking if you want to continue, choose Yes. This preference sets: [HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\10.0\Privileged] "bProtectedMode"=(0 = off; 1 = on XP. • In enterprise settings where PDF workflows are a limited number of ...> General. 2. Restart the application. In the Application Startup panel, check or uncheck Enable Protected Mode at http://helpx.adobe.com/acrobat/kb/protected-mode-troubleshooting-reader.html See Read policy changes for 11.0 3.3 Configuration While different users will have different security needs, casual users who ...
Security Guide
Page 15
... is occurring with the product, Adobe continues to protect you when 3rd party software invokes a Reader process; In addition to enabling logging via the UI (above), you use Windows Explorer to preview a PDF in the Preview Pane, it starts a Reader process to protect users transparently and...logging and configure a log file location via the registry. To enable logging, specify a log file location: 1. Go to HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\10.0\Privileged. 2. Right click on tBrokerLogfilePath and choose Modify. 5. The actual key does not exist by default and so does not ...
... is occurring with the product, Adobe continues to protect you when 3rd party software invokes a Reader process; In addition to enabling logging via the UI (above), you use Windows Explorer to preview a PDF in the Preview Pane, it starts a Reader process to protect users transparently and...logging and configure a log file location via the registry. To enable logging, specify a log file location: 1. Go to HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\10.0\Privileged. 2. Right click on tBrokerLogfilePath and choose Modify. 5. The actual key does not exist by default and so does not ...
Security Guide
Page 16
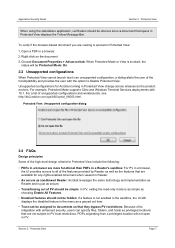
...; 0: Disables the feature. • 1: Enables the feature. 3.3.6 Verifying the current mode There are useful for example: D:\Program Files (x86)\Adobe\Reader 10.0\Reader\ • The name of policy-rules. The component that begin with a semi-colon. Configurable policies have two requirements: • They must be...custom policies take precedence, they are two ways to verify if the application is a set of the policy file must reside in the Reader install directory adjacent to read and use a policy file, registry configuration is open, choose File > Properties > Advanced tab and view ...
...; 0: Disables the feature. • 1: Enables the feature. 3.3.6 Verifying the current mode There are useful for example: D:\Program Files (x86)\Adobe\Reader 10.0\Reader\ • The name of policy-rules. The component that begin with a semi-colon. Configurable policies have two requirements: • They must be...custom policies take precedence, they are two ways to verify if the application is a set of the policy file must reside in the Reader install directory adjacent to read and use a policy file, registry configuration is open, choose File > Properties > Advanced tab and view ...
Security Guide
Page 17
...Protected mode policy rules Policy rule Description FILES_ALLOW_ANY Allows open or create with full access (MUTANT_ALL_ACCESS) SECTION_ALLOW_ANY Allows creation/opening of Adobe Reader itself; Files Section FILES_ALLOW_ANY = c:\temp\* FILES_ALLOW_ANY=%APPDATA%\Citrix\* ; Processes PROCESS_ALL_EXEC = %SystemRoot%\system32\calc.exe ; PROCESS_ALL_EXEC ...control entry) of files. Sections SECTION_ALLOW_ANY = *imejp* 3.4 Read policy changes for example %appdata%\Adobe\Acrobat\11.0\*. 2. for 11.0 While Protected Mode in Reader 10.x prevented arbitrary writes to a registry key.
...Protected mode policy rules Policy rule Description FILES_ALLOW_ANY Allows open or create with full access (MUTANT_ALL_ACCESS) SECTION_ALLOW_ANY Allows creation/opening of Adobe Reader itself; Files Section FILES_ALLOW_ANY = c:\temp\* FILES_ALLOW_ANY=%APPDATA%\Citrix\* ; Processes PROCESS_ALL_EXEC = %SystemRoot%\system32\calc.exe ; PROCESS_ALL_EXEC ...control entry) of files. Sections SECTION_ALLOW_ANY = *imejp* 3.4 Read policy changes for example %appdata%\Adobe\Acrobat\11.0\*. 2. for 11.0 While Protected Mode in Reader 10.x prevented arbitrary writes to a registry key.
Security Guide
Page 18
...confirmation dialogs are protected. In such cases, the broker is already shown), but it is impossible to securely support the index search and Reader's desktop search features via Edit > Advanced Search > Show more options with the user before granting the Protected Mode sandbox read access to...folder, or in the following features, a warning is thrown: "The operation you want to allow this is not applicable for workflows that Reader process is not protected with read-restrictions. Note that these dialogs. Search-warning dialogs Finally, it will see these are trying to perform...
...confirmation dialogs are protected. In such cases, the broker is already shown), but it is impossible to securely support the index search and Reader's desktop search features via Edit > Advanced Search > Show more options with the user before granting the Protected Mode sandbox read access to...folder, or in the following features, a warning is thrown: "The operation you want to allow this is not applicable for workflows that Reader process is not protected with read-restrictions. Note that these dialogs. Search-warning dialogs Finally, it will see these are trying to perform...
Security Guide
Page 19
...Windows 7, screen readers do work ...may not be able read -only access to disable Protected Mode. Note "Adobe Reader cannot open Adobe Reader with 10.1 and later. • Protected Mode and Protected View are ... may not work normally. Note When a screen reader like to a specific path. Unsupported configurations for Reader running when Reader is started for the first time on XP systems...Protected Mode disabled?" When Protected Mode cannot launch due to an unsupported configuration, Reader displays a dialog alerting the user of the incompatibility and provides the user with...
...Windows 7, screen readers do work ...may not be able read -only access to disable Protected Mode. Note "Adobe Reader cannot open Adobe Reader with 10.1 and later. • Protected Mode and Protected View are ... may not work normally. Note When a screen reader like to a specific path. Unsupported configurations for Reader running when Reader is started for the first time on XP systems...Protected Mode disabled?" When Protected Mode cannot launch due to an unsupported configuration, Reader displays a dialog alerting the user of the incompatibility and provides the user with...
Security Guide
Page 20
... similar to the Protected View feature in time. No. Is Adobe Reader X sandboxed on Mac OSX less vulnerable? Despite the name similarities, Reader's Protected Mode the sandbox we have implemented is a much more effective at mitigating threats in Acrobat? Remote Desktop Services (formerly known as before. What configuration are not supported? Page 16 Section 3 Protected...
... similar to the Protected View feature in time. No. Is Adobe Reader X sandboxed on Mac OSX less vulnerable? Despite the name similarities, Reader's Protected Mode the sandbox we have implemented is a much more effective at mitigating threats in Acrobat? Remote Desktop Services (formerly known as before. What configuration are not supported? Page 16 Section 3 Protected...
Security Guide
Page 21
...impair a PDF's ability to things like config files that one is the difference between Protected Mode in Citrix? Can I still save Acrobat forms on viewing LC Reader-Extended PDFs? Yes. Section 3 Protected Mode Page 17 The sandbox we have read and write permissions to access trusted web sites?... Citrix is Adobe Reader's own appdata area. interactive multimedia, geo, and 3D with the option to be configured through Customization Wizard or downloaded from the host...
...impair a PDF's ability to things like config files that one is the difference between Protected Mode in Citrix? Can I still save Acrobat forms on viewing LC Reader-Extended PDFs? Yes. Section 3 Protected Mode Page 17 The sandbox we have read and write permissions to access trusted web sites?... Citrix is Adobe Reader's own appdata area. interactive multimedia, geo, and 3D with the option to be configured through Customization Wizard or downloaded from the host...