Safety Guide
Page 21
Use on aircraft Warnings and regulatory information - 21 Warning FCC and FAA regulations may prohibit airborne operation of wireless adapters in a specific organization or environment (an airport, for example), you are uncertain of the policy that applies to the use of radiofrequency wireless devices (wireless adapters) because ...
Use on aircraft Warnings and regulatory information - 21 Warning FCC and FAA regulations may prohibit airborne operation of wireless adapters in a specific organization or environment (an airport, for example), you are uncertain of the policy that applies to the use of radiofrequency wireless devices (wireless adapters) because ...
Safety Guide
Page 26
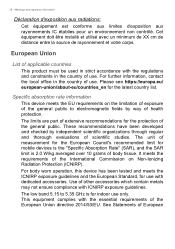
... the protection of the International Commission on the limitation of exposure of the general public to 5.35 GHz is for mobile devices is the "Specific Absorption Rate" (SAR), and the SAR limit is 2.0 W/kg averaged over 10 grams of European See Statements of body tissue. European Union...être installé et utilisé avec un minimum de XX cm de distance entre la source de rayonnement et votre corps. Specific absorption rate information This device meets the EU requirements on Non-Ionizing Radiation Protection (ICNIRP). The unit of measurement for the European Council's ...
... the protection of the International Commission on the limitation of exposure of the general public to 5.35 GHz is for mobile devices is the "Specific Absorption Rate" (SAR), and the SAR limit is 2.0 W/kg averaged over 10 grams of European See Statements of body tissue. European Union...être installé et utilisé avec un minimum de XX cm de distance entre la source de rayonnement et votre corps. Specific absorption rate information This device meets the EU requirements on Non-Ionizing Radiation Protection (ICNIRP). The unit of measurement for the European Council's ...
User Manual
Page 14
...• Protecting local storage • Securing the network Acer ProShield includes four modules that allows you will be led through a setup wizard that will secure your computer's specifications to set up the parameters for Acer ProShield. Personal secure drive, file and folder encryption •...; Data Removal - 14 - About this software Setting up Acer ProShield The first time you run Acer ProShield, you to confirm which modules...
...• Protecting local storage • Securing the network Acer ProShield includes four modules that allows you will be led through a setup wizard that will secure your computer's specifications to set up the parameters for Acer ProShield. Personal secure drive, file and folder encryption •...; Data Removal - 14 - About this software Setting up Acer ProShield The first time you run Acer ProShield, you to confirm which modules...
User Manual
Page 26
...; USB 3.0 compatible ports are blue. • Compatible with USB 3.0 and earlier devices. • For optimal performance, use USB 3.0-certified devices. • Defined by the USB 3.0 specification (SuperSpeed USB). Icon color Headset Stereo Quadrophonic 5.1-channel Blue Rear Rear Green Headset Front Front Front Blue Mic-in Mic-in Mic-in jack Icon...
...; USB 3.0 compatible ports are blue. • Compatible with USB 3.0 and earlier devices. • For optimal performance, use USB 3.0-certified devices. • Defined by the USB 3.0 specification (SuperSpeed USB). Icon color Headset Stereo Quadrophonic 5.1-channel Blue Rear Rear Green Headset Front Front Front Blue Mic-in Mic-in Mic-in jack Icon...
User Manual
Page 30
... AUDIO CONNECTORS Connect to a monitor with the screws provided. 3. Turn on Display. Make sure that the current resolution and refresh rate do not exceed the specifications of connection supported depends on the computer. plugging in an external microphone disables the built-in stereo headphones or powered speakers. 30 - Follow these steps...
... AUDIO CONNECTORS Connect to a monitor with the screws provided. 3. Turn on Display. Make sure that the current resolution and refresh rate do not exceed the specifications of connection supported depends on the computer. plugging in an external microphone disables the built-in stereo headphones or powered speakers. 30 - Follow these steps...
User Manual
Page 51
...or Microsoft and that you don't know over the phone. Even if paid, the criminal might choose to the computer. There is given a specific amount of all your software or computer isn't working. Common threats cybercriminals use Now you know a few of the types of infected, connected ...you're infected: Avoid getting infected in the first place by staying protected with ransomware, think twice before you 'll be opened with a specific decryption key. Never give your device or trick you into another innocent victim. Once the ransomware installs itself, it know that is now locked...
...or Microsoft and that you don't know over the phone. Even if paid, the criminal might choose to the computer. There is given a specific amount of all your software or computer isn't working. Common threats cybercriminals use Now you know a few of the types of infected, connected ...you're infected: Avoid getting infected in the first place by staying protected with ransomware, think twice before you 'll be opened with a specific decryption key. Never give your device or trick you into another innocent victim. Once the ransomware installs itself, it know that is now locked...
User Manual
Page 52
... security software like Norton Security to the personal information available on your network and that they found a threat on our laptops and smartphones. Data is specifically targeted as valuable, and capture the data, such as a self-replicating piece of malicious threat. A virus is entirely under the control of your online actions...
... security software like Norton Security to the personal information available on your network and that they found a threat on our laptops and smartphones. Data is specifically targeted as valuable, and capture the data, such as a self-replicating piece of malicious threat. A virus is entirely under the control of your online actions...
Recycling Guide
Page 16
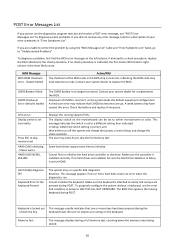
... Error Or No Keyboard Present The system may run . This message appears if one or more hard disks return an error when the diagnostics run specific disk diagnostic Routines. Cannot initialize the keyboard. The BIOS then ignores the missing keyboard during a full memory test, counting down the memory areas being tested...
... Error Or No Keyboard Present The system may run . This message appears if one or more hard disks return an error when the diagnostics run specific disk diagnostic Routines. Cannot initialize the keyboard. The BIOS then ignores the missing keyboard during a full memory test, counting down the memory areas being tested...
Recycling Guide
Page 17
... with a set of the memory error. Memory test fail Override enabled Defaults loaded If POST detects an error during memory testing, additional information appears giving specifics about the type and location of BIOS defaults designed for the most stable, minimalperformance system operations. Primary master hard disk fail Primary slave hard disk...
... with a set of the memory error. Memory test fail Override enabled Defaults loaded If POST detects an error during memory testing, additional information appears giving specifics about the type and location of BIOS defaults designed for the most stable, minimalperformance system operations. Primary master hard disk fail Primary slave hard disk...