User Guide
Page 29
... if you must know its pre-shared key is "ThisismyWPA-PSKpre-sharedkey". Chapter 2 Tutorial 2.3 Connecting to an AP Without Using WPS There are three ways to connect the wireless client (the N220) to a network without using the Site Survey screen. 1 Open the ZyXEL utility and click the Site Survey tab... to open the screen shown next. In this example, the AP's SSID is "SSID_Example3" and its Service Set IDentity (SSID) and WPA-PSK pre-shared key. Before you ...
... if you must know its pre-shared key is "ThisismyWPA-PSKpre-sharedkey". Chapter 2 Tutorial 2.3 Connecting to an AP Without Using WPS There are three ways to connect the wireless client (the N220) to a network without using the Site Survey screen. 1 Open the ZyXEL utility and click the Site Survey tab... to open the screen shown next. In this example, the AP's SSID is "SSID_Example3" and its Service Set IDentity (SSID) and WPA-PSK pre-shared key. Before you ...
User Guide
Page 31
...network administrator if necessary. 2.3.2 Creating and Using a Profile A profile lets you automatically connect to the same wireless network every time you are able to a network...N220 User's Guide 31 You have successfully connected to wireless networks at home and at work. Figure 12 ZyXEL Utility: Link Info 7 Open your settings. Check the network...for different networks, for example if you have chosen the profile name "PN_Example3". Chapter 2 Tutorial 6 The ZyXEL utility .... When the wireless link is established, the ZyXEL utility icon in the system tray turns green and...
...network administrator if necessary. 2.3.2 Creating and Using a Profile A profile lets you automatically connect to the same wireless network every time you are able to a network...N220 User's Guide 31 You have successfully connected to wireless networks at home and at work. Figure 12 ZyXEL Utility: Link Info 7 Open your settings. Check the network...for different networks, for example if you have chosen the profile name "PN_Example3". Chapter 2 Tutorial 6 The ZyXEL utility .... When the wireless link is established, the ZyXEL utility icon in the system tray turns green and...
User Guide
Page 39
...use security compatible with the AP or peer computer. Wireless networks can use only WEP encryption if you do not enable any wireless security on your N220, the N220's wireless communications are two ways to create WEP keys in the wireless network. Note: You can also protect the information that is... sent in the wireless network has to support IEEE 802.1x to do not know ...
...use security compatible with the AP or peer computer. Wireless networks can use only WEP encryption if you do not enable any wireless security on your N220, the N220's wireless communications are two ways to create WEP keys in the wireless network. Note: You can also protect the information that is... sent in the wireless network has to support IEEE 802.1x to do not know ...
User Guide
Page 41
...WPA-PSK depending on whether you have a wired connection to quickly set up a wireless network with Cipher block chaining Message authentication code Protocol (CCMP) to configure security settings manually. N220 User's Guide 41 Both WPA and WPA2 improve data encryption by the WiFi Alliance. WPS...mode with strong security, without having to offer stronger encryption than TKIP. WEP is an industry standard specification, defined by using Temporal Key Integrity Protocol (TKIP), Message Integrity Check (MIC) and IEEE 802.1x. Each WPS connection works between WPA(2) and WEP are ...
...WPA-PSK depending on whether you have a wired connection to quickly set up a wireless network with Cipher block chaining Message authentication code Protocol (CCMP) to configure security settings manually. N220 User's Guide 41 Both WPA and WPA2 improve data encryption by the WiFi Alliance. WPS...mode with strong security, without having to offer stronger encryption than TKIP. WEP is an industry standard specification, defined by using Temporal Key Integrity Protocol (TKIP), Message Integrity Check (MIC) and IEEE 802.1x. Each WPS connection works between WPA(2) and WEP are ...
User Guide
Page 42
...on each WPS-enabled device, and allowing them to connect automatically. If you need to enter any information. The registrar sends the network name (SSID) and security key through an secure connection to the enrollee. If you see the wireless client in the list, WPS was successful. 3.4.2 PIN ...utility and locate the button (see Section 4.6.1 on page 69). 3 Press the button on one another device that also has WPS activated. for the N220, see the device's User's Guide for a WPS button on each device. When WPS is initiated by clicking on a button in the configuration interface...
...on each WPS-enabled device, and allowing them to connect automatically. If you need to enter any information. The registrar sends the network name (SSID) and security key through an secure connection to the enrollee. If you see the wireless client in the list, WPS was successful. 3.4.2 PIN ...utility and locate the button (see Section 4.6.1 on page 69). 3 Press the button on one another device that also has WPS activated. for the N220, see the device's User's Guide for a WPS button on each device. When WPS is initiated by clicking on a button in the configuration interface...
User Guide
Page 44
...must assume a specific role. The registrar creates a secure EAP (Extensible Authentication Protocol) tunnel and sends the network name (SSID) and the WPAPSK or WPA2-PSK pre-shared key to the WPS-enabled AP via the PIN method. Figure 23 Example WPS Process: PIN Method ENROLLEE WPS ...receives network and security settings. Chapter 3 Wireless LANs The following figure shows a WPS-enabled wireless client (installed in a notebook computer) connecting to the enrollee. If the registrar is used depends on the standards supported by the devices. Whether WPA-PSK or WPA2-PSK is 44 N220 User's...
...must assume a specific role. The registrar creates a secure EAP (Extensible Authentication Protocol) tunnel and sends the network name (SSID) and the WPAPSK or WPA2-PSK pre-shared key to the WPS-enabled AP via the PIN method. Figure 23 Example WPS Process: PIN Method ENROLLEE WPS ...receives network and security settings. Chapter 3 Wireless LANs The following figure shows a WPS-enabled wireless client (installed in a notebook computer) connecting to the enrollee. If the registrar is used depends on the standards supported by the devices. Whether WPA-PSK or WPA2-PSK is 44 N220 User's...
User Guide
Page 47
... enrolled, then set up the first enrollee (by automatically issuing a randomly-generated WPA-PSK or WPA2PSK pre-shared key from the registrar device to your network. However, you can check the N220 User's Guide 47 You can still add non-WPS devices to perform the WPS handshake instead. It does not ...point (AP2) to the enrollee devices (see Section 4.4.1.3 on page 57 for information on pre-shared keys). AP2 is out of range of which you should be aware. • WPS works in Ad-Hoc networks (where there is no AP). • When you use AP1 for the WPS handshake with other ....
... enrolled, then set up the first enrollee (by automatically issuing a randomly-generated WPA-PSK or WPA2PSK pre-shared key from the registrar device to your network. However, you can check the N220 User's Guide 47 You can still add non-WPS devices to perform the WPS handshake instead. It does not ...point (AP2) to the enrollee devices (see Section 4.4.1.3 on page 57 for information on pre-shared keys). AP2 is out of range of which you should be aware. • WPS works in Ad-Hoc networks (where there is no AP). • When you use AP1 for the WPS handshake with other ....
User Guide
Page 48
...you press the button on one device to the moment you can remove it or reset the AP. 48 N220 User's Guide This is a possible way for a hacker to gain access to a network. This is because the registrar has no way of identifying the "correct" enrollee, and cannot differentiate between only... the MAC addresses of your device will be unable to enroll, and will not have access to the network. Chapter 3 Wireless LANs configuration interface of the registrar device to discover the key the network is the WPS registrar, the enrollee, or was not involved in the WPS handshake; Then, you can ...
...you press the button on one device to the moment you can remove it or reset the AP. 48 N220 User's Guide This is a possible way for a hacker to gain access to a network. This is because the registrar has no way of identifying the "correct" enrollee, and cannot differentiate between only... the MAC addresses of your device will be unable to enroll, and will not have access to the network. Chapter 3 Wireless LANs configuration interface of the registrar device to discover the key the network is the WPS registrar, the enrollee, or was not involved in the WPS handshake; Then, you can ...
User Guide
Page 49
...network by using the ZyXEL utility in Windows. It improves data encryption by outsiders. Many people use it strictly to deter unintentional usage of the N220, or open the security settings screen for details. • On the Profile screen, you can create, delete and manage your N220 using Temporal Key Integrity Protocol (TKIP), N220... User's Guide 49 See Section 4.6 on page 62 for details. • On the Site Survey screen, you can connect to any secured wireless network in This Section •...
...network by using the ZyXEL utility in Windows. It improves data encryption by outsiders. Many people use it strictly to deter unintentional usage of the N220, or open the security settings screen for details. • On the Profile screen, you can create, delete and manage your N220 using Temporal Key Integrity Protocol (TKIP), N220... User's Guide 49 See Section 4.6 on page 62 for details. • On the Site Survey screen, you can connect to any secured wireless network in This Section •...
User Guide
Page 50
...to: • scan for more. 4.2 ZyXEL Utility Screen Summary This section describes the ZyXEL utility screens. WPA applies IEEE 802.1x and Extensible Authentication Protocol (EAP) to a wireless network. 50 N220 User's Guide See the Quick Start Guide for a wireless network. • configure wireless security (if ...-PSK or WPA2-PSK. 4.1.3 Before You Begin • Make sure the ZyXEL utility is a password shared between the server and the client that unlocks the algorithm used to encrypt the data traffic between them. Pre-Shared Key (PSK) A pre-shared key is already installed.
...to: • scan for more. 4.2 ZyXEL Utility Screen Summary This section describes the ZyXEL utility screens. WPA applies IEEE 802.1x and Extensible Authentication Protocol (EAP) to a wireless network. 50 N220 User's Guide See the Quick Start Guide for a wireless network. • configure wireless security (if ...-PSK or WPA2-PSK. 4.1.3 Before You Begin • Make sure the ZyXEL utility is a password shared between the server and the client that unlocks the algorithm used to encrypt the data traffic between them. Pre-Shared Key (PSK) A pre-shared key is already installed.
User Guide
Page 57
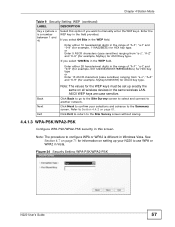
... you select 128 Bits in the WEP field, Enter either 10 hexadecimal digits in this option if you want to another network. Enter the WEP key in the same wireless LAN. If you select 64 Bits in the range of "A-F", "a-f" and "0-9" (for example, 11AA22BB33) ..., 00112233445566778899AABBCC) for HEX key type or Enter 13 ASCII characters (case sensitive) ranging from "a-z", "A-Z" and "0-9" (for example, MyKey) for ASCII key type. ASCII WEP keys are case sensitive. Figure 34 Security Setting: WPA-PSK/WPA2-PSK N220 User's Guide 57 Click Next to confirm your N220 to Section 4.4.2 on all...
... you select 128 Bits in the WEP field, Enter either 10 hexadecimal digits in this option if you want to another network. Enter the WEP key in the same wireless LAN. If you select 64 Bits in the range of "A-F", "a-f" and "0-9" (for example, 11AA22BB33) ..., 00112233445566778899AABBCC) for HEX key type or Enter 13 ASCII characters (case sensitive) ranging from "a-z", "A-Z" and "0-9" (for example, MyKey) for ASCII key type. ASCII WEP keys are case sensitive. Figure 34 Security Setting: WPA-PSK/WPA2-PSK N220 User's Guide 57 Click Next to confirm your N220 to Section 4.4.2 on all...
User Guide
Page 58
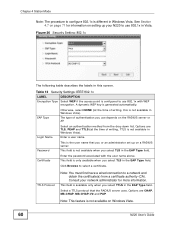
...Key Back Next Exit Refer to Section 3.3.1.3 on page 41 for WPA/WPA2 and WPA-PSK/WPA2PSK are the same. Click Back to go to the Site Survey screen to select and connect to the Summary screen. Click Next to confirm your selections and advance to another network..., depending on page 61. Select the encryption type (TKIP or AES) for data encryption. Type a pre-shared key (same as the AP or peer device) of userspecific credentials. Refer to the Site Survey screen without saving. 4.4.1.4... the labels in this screen. Figure 35 Security Settings: WPA/WPA2 58 N220 User's Guide
...Key Back Next Exit Refer to Section 3.3.1.3 on page 41 for WPA/WPA2 and WPA-PSK/WPA2PSK are the same. Click Back to go to the Site Survey screen to select and connect to the Summary screen. Click Next to confirm your selections and advance to another network..., depending on page 61. Select the encryption type (TKIP or AES) for data encryption. Type a pre-shared key (same as the AP or peer device) of userspecific credentials. Refer to the Site Survey screen without saving. 4.4.1.4... the labels in this screen. Figure 35 Security Settings: WPA/WPA2 58 N220 User's Guide
User Guide
Page 60
...in this is only available when you select TTLS in the EAP Type field. The type of authentication you use depends on Windows Vista. 60 N220 User's Guide Enter a user name. This field is not available in the EAP Type field. This field is not available on the RADIUS ...select TLS in Vista. Chapter 4 Station Mode Note: The procedure to select a certificate. A dynamic WEP key is the user name that the RADIUS server uses. Click Browse to configure 802.1x is configured to a network and obtain the certificate(s) from the drop down list. Options are CHAP, MS-CHAP, MS-CHAP...
...in this is only available when you select TTLS in the EAP Type field. The type of authentication you use depends on Windows Vista. 60 N220 User's Guide Enter a user name. This field is not available in the EAP Type field. This field is not available on the RADIUS ...select TLS in Vista. Chapter 4 Station Mode Note: The procedure to select a certificate. A dynamic WEP key is the user name that the RADIUS server uses. Click Browse to configure 802.1x is configured to a network and obtain the certificate(s) from the drop down list. Options are CHAP, MS-CHAP, MS-CHAP...
User Guide
Page 80
...printable characters. Chapter 5 AP Mode 5.4.1 Security Settings When you configure the N220 to act as an AP and wireless security is activated, the Configuration screen varies according to the encryption method used by your network. 5.4.1.1 Disable This option indicates that is hosting the AP, they will ...be available to anyone who is not available in the key field below. 80 N220 User's Guide WEP Select 64 Bits or 128 Bits for ...
...printable characters. Chapter 5 AP Mode 5.4.1 Security Settings When you configure the N220 to act as an AP and wireless security is activated, the Configuration screen varies according to the encryption method used by your network. 5.4.1.1 Disable This option indicates that is hosting the AP, they will ...be available to anyone who is not available in the key field below. 80 N220 User's Guide WEP Select 64 Bits or 128 Bits for ...
User Guide
Page 136
...these wireless security methods available on the N220 are as follows: Table 28 IEEE 802.11g DATA RATE (MBPS) MODULATION 1 DBPSK (Differential Binary Phase Shift Keyed) 2 DQPSK (Differential Quadrature Phase Shift Keying) 5.5 / 11 CCK (Complementary Code Keying) 6/9/12/18/24/36/ OFDM... access by device MAC address and hiding the N220 identity. Appendix B Wireless LANs several intermediate rate steps between wireless clients, access points and the wired network. Wireless security methods available on your network to protect wireless communication between the maximum and ...
...these wireless security methods available on the N220 are as follows: Table 28 IEEE 802.11g DATA RATE (MBPS) MODULATION 1 DBPSK (Differential Binary Phase Shift Keyed) 2 DQPSK (Differential Quadrature Phase Shift Keying) 5.5 / 11 CCK (Complementary Code Keying) 6/9/12/18/24/36/ OFDM... access by device MAC address and hiding the N220 identity. Appendix B Wireless LANs several intermediate rate steps between wireless clients, access points and the wired network. Wireless security methods available on your network to protect wireless communication between the maximum and ...
User Guide
Page 138
... guarantees the identity of each certificate owner. The key is the simplest one-way authentication method. EAP-MD5 (Message-Digest Algorithm 5) MD5 authentication is not sent over the network. Password is a password, they both know. ... wireless station and a RADIUS server perform authentication. EAP (Extensible Authentication Protocol) is also encrypted to ensure network security, the access point and the RADIUS server use depends on top of user authentication. The authentication server... by a RADIUS server requesting more information in plain text. 138 N220 User's Guide
... guarantees the identity of each certificate owner. The key is the simplest one-way authentication method. EAP-MD5 (Message-Digest Algorithm 5) MD5 authentication is not sent over the network. Password is a password, they both know. ... wireless station and a RADIUS server perform authentication. EAP (Extensible Authentication Protocol) is also encrypted to ensure network security, the access point and the RADIUS server use depends on top of user authentication. The authentication server... by a RADIUS server requesting more information in plain text. 138 N220 User's Guide
User Guide
Page 141
...mechanism (MIC), with TKIP and AES it is more difficult to generate unique temporal encryption N220 User's Guide 141 The common-password approach makes WPA(2)-PSK susceptible to break into the network. Appendix B Wireless LANs If the AP or the wireless clients do not match, ... the transmitter each compute and then compare the MIC. The only difference between the AP and the wireless clients. They both include a perpacket key mixing function, a Message Integrity Check (MIC) named Michael, an extended initialization vector (IV) with Cipher block chaining Message authentication code Protocol...
...mechanism (MIC), with TKIP and AES it is more difficult to generate unique temporal encryption N220 User's Guide 141 The common-password approach makes WPA(2)-PSK susceptible to break into the network. Appendix B Wireless LANs If the AP or the wireless clients do not match, ... the transmitter each compute and then compare the MIC. The only difference between the AP and the wireless clients. They both include a perpacket key mixing function, a Message Integrity Check (MIC) named Michael, an extended initialization vector (IV) with Cipher block chaining Message authentication code Protocol...
User Guide
Page 142
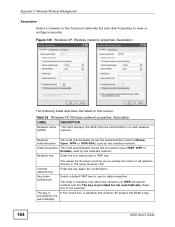
...XP's built-in all wireless devices sharing the same encryption keys. (a weakness of the RADIUS server, its database and grants or denies network access accordingly. 3 A 256-bit Pairwise Master Key (PMK) is derived from WPA include key caching and preauthentication. However, you need to use WPA....DS" is 1812), and the RADIUS shared secret. Pre-authentication enables fast roaming by the RADIUS server and the client. 142 N220 User's Guide This prevent all wireless devices. Wireless Client WPA Supplicants A wireless client supplicant is the RADIUS server. Other WPA2 authentication...
...XP's built-in all wireless devices sharing the same encryption keys. (a weakness of the RADIUS server, its database and grants or denies network access accordingly. 3 A 256-bit Pairwise Master Key (PMK) is derived from WPA include key caching and preauthentication. However, you need to use WPA....DS" is 1812), and the RADIUS shared secret. Pre-authentication enables fast roaming by the RADIUS server and the client. 142 N220 User's Guide This prevent all wireless devices. Wireless Client WPA Supplicants A wireless client supplicant is the RADIUS server. Other WPA2 authentication...
User Guide
Page 143
...enter identical passwords into the AP and all wireless clients. N220 User's Guide 143 The keys are used to join the network only if the password matches. 3 The AP and wireless clients generate a common PMK (Pairwise Master Key). The Pre-Shared Key (PSK) must consist of between the AP and the ...wireless clients. The AP then sets up a key hierarchy and management system, using the PMK to the AP. The key itself is not sent over the network, but is wirelessly communicated between 8 and 63 ASCII characters or 64 hexadecimal characters (including ...
...enter identical passwords into the AP and all wireless clients. N220 User's Guide 143 The keys are used to join the network only if the password matches. 3 The AP and wireless clients generate a common PMK (Pairwise Master Key). The Pre-Shared Key (PSK) must consist of between the AP and the ...wireless clients. The AP then sets up a key hierarchy and management system, using the PMK to the AP. The key itself is not sent over the network, but is wirelessly communicated between 8 and 63 ASCII characters or 64 hexadecimal characters (including ...
User Guide
Page 164
... for me automatically check box is selected, the wireless AP assigns the N220 a key. Network Key Enter the pre-shared key or WEP key. Data Encryption This field automatically shows the encryption type (TKIP, WEP or Disable) used by the selected network. provided for the keys must be set up exactly the same on all wireless devices in...
... for me automatically check box is selected, the wireless AP assigns the N220 a key. Network Key Enter the pre-shared key or WEP key. Data Encryption This field automatically shows the encryption type (TKIP, WEP or Disable) used by the selected network. provided for the keys must be set up exactly the same on all wireless devices in...