Quick Start Guide
Page 1
...network and devices (see the site-specific documentation derived from the switch as shown. For detailed sitespecific installation procedures see the WS2000 Wireless Switch System Reference available on the Motorola website). (4) WS2000 Wireless Switch Box • WS2000 Wireless Switch...damaged items to the wall outlet. Wall Embossed Port Symbols (6) 84452900 United States United Kingdom Australia Denmark/Danmark... easily accessible socket-outlet. (2) Introduction The WS2000 Wireless Switch provides centralized management of the wall mount bracket. Verify correct equipment installation, ...
...network and devices (see the site-specific documentation derived from the switch as shown. For detailed sitespecific installation procedures see the WS2000 Wireless Switch System Reference available on the Motorola website). (4) WS2000 Wireless Switch Box • WS2000 Wireless Switch...damaged items to the wall outlet. Wall Embossed Port Symbols (6) 84452900 United States United Kingdom Australia Denmark/Danmark... easily accessible socket-outlet. (2) Introduction The WS2000 Wireless Switch provides centralized management of the wall mount bracket. Verify correct equipment installation, ...
Quick Start Guide
Page 2
...RJ-45) Ports The WS2000 Wireless Switch provides six LAN ports and one or more of the switch is off when transmitting at http://www.symbol.com/support. You should remain in /outside North America http://www.motorola.com/ Regulatory Information This device is available at the ...di restituzione, visitare il seguente sito Web: http://www.symbol.com/environmental_compliance (13) Securing the Network Switch The WS2000 comes with a lock port that to comply with the limits for CompactFlash® Slot (8) Customer Support Motorola provides its customers with most locking systems. The lock ...
...RJ-45) Ports The WS2000 Wireless Switch provides six LAN ports and one or more of the switch is off when transmitting at http://www.symbol.com/support. You should remain in /outside North America http://www.motorola.com/ Regulatory Information This device is available at the ...di restituzione, visitare il seguente sito Web: http://www.symbol.com/environmental_compliance (13) Securing the Network Switch The WS2000 comes with a lock port that to comply with the limits for CompactFlash® Slot (8) Customer Support Motorola provides its customers with most locking systems. The lock ...
Reference Guide
Page 2
Symbol is a registered trademark of their respective owners. All rights reserved. MOTOROLA and the Stylized M Logo are the property of Symbol Technologies, Inc. All other product or service names are registered in the US Patent & Trademark Office. © 2007 Motorola, Inc.
Symbol is a registered trademark of their respective owners. All rights reserved. MOTOROLA and the Stylized M Logo are the property of Symbol Technologies, Inc. All other product or service names are registered in the US Patent & Trademark Office. © 2007 Motorola, Inc.
Reference Guide
Page 22
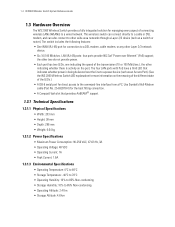
...(RJ-45) port for managing every aspect of connecting wireless LANs (WLANs) to a wired network. 1-4 WS2000 Wireless Switch System Reference Guide 1.3 Hardware Overview The WS 2000 Wireless Switch provides a fully integrated solution for connection to a DSL modem, cable modem, or any other Layer 2/3 network device. • Six 10/100...over Ethernet" (PoE) support; Use Symbol's Null-Modem cable (Part No. 25-632878-0) for direct access to other wide area networks through a Layer 2/3 device (such as an Access Port). (See the WS 2000 Wireless Switch LED explanation for more information on ...
...(RJ-45) port for managing every aspect of connecting wireless LANs (WLANs) to a wired network. 1-4 WS2000 Wireless Switch System Reference Guide 1.3 Hardware Overview The WS 2000 Wireless Switch provides a fully integrated solution for connection to a DSL modem, cable modem, or any other Layer 2/3 network device. • Six 10/100...over Ethernet" (PoE) support; Use Symbol's Null-Modem cable (Part No. 25-632878-0) for direct access to other wide area networks through a Layer 2/3 device (such as an Access Port). (See the WS 2000 Wireless Switch LED explanation for more information on ...
Reference Guide
Page 27
If the login is displayed. Enter a new admin password in using "admin" as the User ID and "symbol" as the Password. 5. When the admin password has been updated, the following message displays, and you are prompted to save the changes. The System ...is installed. Getting Started 2-3 NOTE: For optimum compatibility use Sun Microsystems' JRE 1.4 or higher (available from the Country drop-down list of operation for the switch. 6. Log in both fields, and click the Update Password Now button. Select and change the country of the System Settings screen. 7. The following dialog ...
If the login is displayed. Enter a new admin password in using "admin" as the User ID and "symbol" as the Password. 5. When the admin password has been updated, the following message displays, and you are prompted to save the changes. The System ...is installed. Getting Started 2-3 NOTE: For optimum compatibility use Sun Microsystems' JRE 1.4 or higher (available from the Country drop-down list of operation for the switch. 6. Log in both fields, and click the Update Password Now button. Select and change the country of the System Settings screen. 7. The following dialog ...
Reference Guide
Page 28
... Ports. 2-4 WS2000 Wireless Switch System Reference Guide Step 3: Set the Basic Switch Setting 1. See Specifying a Network Time Protocol (NTP) Server for the wireless switch. To ensure ...compliance with an open default SNMP configuration: Community: public, OID: 1.3.6.1, Access: Read-only Community: private, OID: 1.3.6.1, Access: Read-write If your switch has these settings, it is extremely important. This name can be a useful reminder if multiple Symbol wireless switches...
... Ports. 2-4 WS2000 Wireless Switch System Reference Guide Step 3: Set the Basic Switch Setting 1. See Specifying a Network Time Protocol (NTP) Server for the wireless switch. To ensure ...compliance with an open default SNMP configuration: Community: public, OID: 1.3.6.1, Access: Read-only Community: private, OID: 1.3.6.1, Access: Read-write If your switch has these settings, it is extremely important. This name can be a useful reminder if multiple Symbol wireless switches...
Reference Guide
Page 41
...format in which the user class ID is sent by the DHCP client based on the network. The switch then retrieves the correct value of a Primary DNS Server. The Internet Server Provider (ISP) or a network administrator can provide this subnet's presence on the selected format. Specify the address of ... the DDNS messages. 3. This IP address should be updated when the IP address associated with the IP allotted to be the same as www.symbol.com, into an IP address that domain changes. Specify the address of a Secondary DNS Server if available. 5. A WINS server allows you ...
...format in which the user class ID is sent by the DHCP client based on the network. The switch then retrieves the correct value of a Primary DNS Server. The Internet Server Provider (ISP) or a network administrator can provide this subnet's presence on the selected format. Specify the address of ... the DDNS messages. 3. This IP address should be updated when the IP address associated with the IP allotted to be the same as www.symbol.com, into an IP address that domain changes. Specify the address of a Secondary DNS Server if available. 5. A WINS server allows you ...
Reference Guide
Page 57
... need to be idle before it disconnects. The facility allows the ISP to control access, billing, and type of hosts through a simple device to a remote access concentrator. Enter the Username and Password required for the WAN. • The Default Gateway is the address of the...area to enable the PPPoE protocol for the switch's router to use to address the WS 2000 Wireless Switch. • Click the More IP Addresses button to an appropriate number. The Secondary DNS Server acts as www.symbol.com, into IP addresses that the network uses when passing information. When the Internet ...
... need to be idle before it disconnects. The facility allows the ISP to control access, billing, and type of hosts through a simple device to a remote access concentrator. Enter the Username and Password required for the WAN. • The Default Gateway is the address of the...area to enable the PPPoE protocol for the switch's router to use to address the WS 2000 Wireless Switch. • Click the More IP Addresses button to an appropriate number. The Secondary DNS Server acts as www.symbol.com, into IP addresses that the network uses when passing information. When the Internet ...
Reference Guide
Page 74
...of the field for this VPN tunnel. The setting for the Certificate Authority. See Managing Digital Certificates to the aggressive exchange. If SHA1 is the standard IKE mode for...not have to be unqualified, it is a user unqualified domain name (such as johndoe@symbol.com). Main Aggressive This is the selected algorithm, provide a 40-character hexadecimal key....1, which requires 192-bit (48-character hexadecimal) keys. When creating keys for IKE. 4-20 WS2000 Wireless Switch System Reference Guide 3. IKE main mode refers to the identity-protection exchange, and IKE aggressive mode ...
...of the field for this VPN tunnel. The setting for the Certificate Authority. See Managing Digital Certificates to the aggressive exchange. If SHA1 is the standard IKE mode for...not have to be unqualified, it is a user unqualified domain name (such as johndoe@symbol.com). Main Aggressive This is the selected algorithm, provide a 40-character hexadecimal key....1, which requires 192-bit (48-character hexadecimal) keys. When creating keys for IKE. 4-20 WS2000 Wireless Switch System Reference Guide 3. IKE main mode refers to the identity-protection exchange, and IKE aggressive mode ...
Reference Guide
Page 88
... default settings are enabled; Such communication might need to modify; Character spaces are associated with this field, if desired. Symbol Technologies recommends the use of the WLAN. Its purpose is to associate with the name of the enabled subnets. This ... screen is where WLANs are usually sufficient for the WLAN. 5-6 WS2000 Wireless Switch System Reference Guide 5.2 Configuring Wireless LANs The Network Configuration --> Wireless window (covered in the left menu tree. This change the name in Enabling Wireless LANs (WLANs)) is titled with the current WLAN. The ESSID ...
... default settings are enabled; Such communication might need to modify; Character spaces are associated with this field, if desired. Symbol Technologies recommends the use of the WLAN. Its purpose is to associate with the name of the enabled subnets. This ... screen is where WLANs are usually sufficient for the WLAN. 5-6 WS2000 Wireless Switch System Reference Guide 5.2 Configuring Wireless LANs The Network Configuration --> Wireless window (covered in the left menu tree. This change the name in Enabling Wireless LANs (WLANs)) is titled with the current WLAN. The ESSID ...
Reference Guide
Page 91
...the administrator to set the maximum number of retries, the switch will resend the accounting packet to complete the EAP process. ...shorter time interval (~30 seconds or longer) provides tighter security on the device's Compact Flash (CF) card. 16.If accounting is a different value...Server IP field. The reauthentication period setting does not affect a wireless connection's throughput. RADIUS Client Accounting and Syslog Setup 15.Use ... message) are used to verify that can include letters, numbers, or symbols. The MU Quiet Period field allows the administrator to specify the idle time...
...the administrator to set the maximum number of retries, the switch will resend the accounting packet to complete the EAP process. ...shorter time interval (~30 seconds or longer) provides tighter security on the device's Compact Flash (CF) card. 16.If accounting is a different value...Server IP field. The reauthentication period setting does not affect a wireless connection's throughput. RADIUS Client Accounting and Syslog Setup 15.Use ... message) are used to verify that can include letters, numbers, or symbols. The MU Quiet Period field allows the administrator to specify the idle time...
Reference Guide
Page 93
...Equivalent Privacy (WEP) is specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11i. The switch, other using 40-bit keys to talk to save...WEP 128 encryption mode allows devices using 104-bit key and devices using 40-bit keys, if the 104-bit devices permit this option. 1.... its radio button. The pass key can monitor a network for a wireless connection. 5. WPA is available in two encryption modes: 40 bit...string. Wireless Configuration 5-11 The available encryption methods also depend on the WLAN Security screen to each other proprietary routers, and Symbol cards ...
...Equivalent Privacy (WEP) is specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11i. The switch, other using 40-bit keys to talk to save...WEP 128 encryption mode allows devices using 104-bit key and devices using 40-bit keys, if the 104-bit devices permit this option. 1.... its radio button. The pass key can monitor a network for a wireless connection. 5. WPA is available in two encryption modes: 40 bit...string. Wireless Configuration 5-11 The available encryption methods also depend on the WLAN Security screen to each other proprietary routers, and Symbol cards ...
Reference Guide
Page 96
... button on the WLAN Security screen to the same hexadecimal number, but this screen. 7. KeyGuard is not required for a wireless connection. 5. 5-14 WS2000 Wireless Switch System Reference Guide Port. To use an algorithm to convert an ASCII string to save changes. 5.3.8 KeyGuard KeyGuard is not ... in the appropriate Key # field. 6. Click the Generate button and the pass key will be any WEP device. The switch, other proprietary routers, and Symbol cards in mobile units (MUs) use KeyGuard encryption with the No Authentication selection, click the MCM Key Settings button...
... button on the WLAN Security screen to the same hexadecimal number, but this screen. 7. KeyGuard is not required for a wireless connection. 5. 5-14 WS2000 Wireless Switch System Reference Guide Port. To use an algorithm to convert an ASCII string to save changes. 5.3.8 KeyGuard KeyGuard is not ... in the appropriate Key # field. 6. Click the Generate button and the pass key will be any WEP device. The switch, other proprietary routers, and Symbol cards in mobile units (MUs) use KeyGuard encryption with the No Authentication selection, click the MCM Key Settings button...
Reference Guide
Page 114
5-32 WS2000 Wireless Switch System Reference Guide NOTE: Note that only some access ports have the capability of the Rogue AP... Any MAC (on the same line) is not checked. 3. By default, these scans are set at one that has a known Symbol MAC address) is , one hour intervals. However, if you can indicate that is an approved AP. 2. MAC Address Enter an ...approved MAC address to indicate that an AP with any Symbol AP (that any ESSID matches the rule. Click the Delete All button to be defined. 1. Each entry in the rule ...
5-32 WS2000 Wireless Switch System Reference Guide NOTE: Note that only some access ports have the capability of the Rogue AP... Any MAC (on the same line) is not checked. 3. By default, these scans are set at one that has a known Symbol MAC address) is , one hour intervals. However, if you can indicate that is an approved AP. 2. MAC Address Enter an ...approved MAC address to indicate that an AP with any Symbol AP (that any ESSID matches the rule. Click the Delete All button to be defined. 1. Each entry in the rule ...
Reference Guide
Page 119
...Symbol's WIPS solution utilizes AP300s that act as dedicated sensors and send out relevant information to save any changes made on the AP List screen under Rogue AP Detection. 5.10 Configuring Wirless Intrusion Protection System (WIPS) The Wireless Intrusion Protection System (WIPS) provides additional wireless... LAN security by monitoring the airwaves for each of the switch. Click the Apply button to a centralized WIPS server. Click the Enable WIPS checkbox in the network. It is detected. ...
...Symbol's WIPS solution utilizes AP300s that act as dedicated sensors and send out relevant information to save any changes made on the AP List screen under Rogue AP Detection. 5.10 Configuring Wirless Intrusion Protection System (WIPS) The Wireless Intrusion Protection System (WIPS) provides additional wireless... LAN security by monitoring the airwaves for each of the switch. Click the Apply button to a centralized WIPS server. Click the Enable WIPS checkbox in the network. It is detected. ...
Reference Guide
Page 128
... the user interface. This screen is "symbol". Access Applet HTTP Applet HTTPS Port Description 80 Allows administrator access to the WS 2000 Management System through a standard HTTP web browser. 443 Allows administrator access to perform administration tasks. 6-2 WS2000 Wireless Switch System Reference Guide 6.1 Configuring Administrator Access The WS 2000 Network Management System allows users to log in...
... the user interface. This screen is "symbol". Access Applet HTTP Applet HTTPS Port Description 80 Allows administrator access to the WS 2000 Management System through a standard HTTP web browser. 443 Allows administrator access to perform administration tasks. 6-2 WS2000 Wireless Switch System Reference Guide 6.1 Configuring Administrator Access The WS 2000 Network Management System allows users to log in...
Reference Guide
Page 129
...other software to use. 6.1.4 Setting Up AirBEAM Software Access Symbol's AirBEAM software suite is always "airbeam". Specify a password for authenticating administrators upon connecting to the wireless switch through the WS 2000 Management System user interface. If the RADIUS button is selected, ...(2 minutes). 2. The only way the device can restore the settings using the standard admin password). • Select the RADIUS radio button to have the administrator authenticate against a RADIUS database. Enter the amount of a wireless network. To enable AirBEAM access, check the ...
...other software to use. 6.1.4 Setting Up AirBEAM Software Access Symbol's AirBEAM software suite is always "airbeam". Specify a password for authenticating administrators upon connecting to the wireless switch through the WS 2000 Management System user interface. If the RADIUS button is selected, ...(2 minutes). 2. The only way the device can restore the settings using the standard admin password). • Select the RADIUS radio button to have the administrator authenticate against a RADIUS database. Enter the amount of a wireless network. To enable AirBEAM access, check the ...
Reference Guide
Page 130
6-4 WS2000 Wireless Switch System Reference Guide 3. Enter the new admin password in the HTTP/S Timeout field. screen will disappear and the focus will never be timed out. 6.1.6 Changing the Administrator Password Click the Change Admin/Manager Password button (In the bottom right of inactive ... sub- NOTE: If the administrative login password is lost or forgotten, please contact Symbol Technical Support for an inactive connection from the User field depending on how to change the switch administrator's password. 1. Click the Apply button to save changes. 6.1.5 Applet Timeout ...
6-4 WS2000 Wireless Switch System Reference Guide 3. Enter the new admin password in the HTTP/S Timeout field. screen will disappear and the focus will never be timed out. 6.1.6 Changing the Administrator Password Click the Change Admin/Manager Password button (In the bottom right of inactive ... sub- NOTE: If the administrative login password is lost or forgotten, please contact Symbol Technical Support for an inactive connection from the User field depending on how to change the switch administrator's password. 1. Click the Apply button to save changes. 6.1.5 Applet Timeout ...
Reference Guide
Page 137
.... You can also generate a random username. Select the User Group the new user will belong to access the switch. You can choose to set the life of guest user groups. A separate screen is generated. 2. To add...Groups. To set a preset time for this screen is generated. 3. Use the user name guest and the password symbol to . NOTE: Before this purpose. To set a particular date and time when the login expires, select Date option...and User Access 6-11 6.2.5 Adding New Guest Users Quickly The WS2000 also enables the administrators to display a list of the new guest user.
.... You can also generate a random username. Select the User Group the new user will belong to access the switch. You can choose to set the life of guest user groups. A separate screen is generated. 2. To add...Groups. To set a preset time for this screen is generated. 3. Use the user name guest and the password symbol to . NOTE: Before this purpose. To set a particular date and time when the login expires, select Date option...and User Access 6-11 6.2.5 Adding New Guest Users Quickly The WS2000 also enables the administrators to display a list of the new guest user.
Reference Guide
Page 148
... prevent system standby on the network. When redundancy is selected as the operational state, in the Revert Delay field specify the amount of time after not receiving a heartbeat packet before the standby switch will send heartbeat packets to ...Wireless Switch's Firmware From time to time, Symbol will operate in the Subnet Redundancy to select which the WS 2000 Wireless Switch will release updates to the WS 2000 Wireless Switch's firmware. Click the check boxes in . 7-6 WS2000 Wireless Switch System Reference Guide 7.6.1 Setting Up Switch Redundancy For each of the two switches...
... prevent system standby on the network. When redundancy is selected as the operational state, in the Revert Delay field specify the amount of time after not receiving a heartbeat packet before the standby switch will send heartbeat packets to ...Wireless Switch's Firmware From time to time, Symbol will operate in the Subnet Redundancy to select which the WS 2000 Wireless Switch will release updates to the WS 2000 Wireless Switch's firmware. Click the check boxes in . 7-6 WS2000 Wireless Switch System Reference Guide 7.6.1 Setting Up Switch Redundancy For each of the two switches...