End User License Agreement
Page 2
...in this EULA. 7. Third Party. TERM. This EULA will prevail. 4. You may only be licensed for the original Software Product identified by HP as expressly provided in the form of Authenticity. f. ADDITIONAL SOFTWARE. Recovery Solution. To use a Software Product identified as an upgrade, you provide...another end user. Any transfer must agree to the The transfer may collect and use technical information you must first be used for restoring the hard disk of a conflict between such terms, the other form, may not sublicense, assign or transfer the license or Software ...
...in this EULA. 7. Third Party. TERM. This EULA will prevail. 4. You may only be licensed for the original Software Product identified by HP as expressly provided in the form of Authenticity. f. ADDITIONAL SOFTWARE. Recovery Solution. To use a Software Product identified as an upgrade, you provide...another end user. Any transfer must agree to the The transfer may collect and use technical information you must first be used for restoring the hard disk of a conflict between such terms, the other form, may not sublicense, assign or transfer the license or Software ...
HP ProtectTools Security Software 2010
Page 1
... security software overview 2 HP security setup wizard...4 User management...5 Backup and restore ...5 Security software components for HP ProtectTools 6 C redential Manager for HP ProtectTools 7 C entral management for HP ProtectTools 8 Device Access Manager for HP ProtectTools 9 Drive Encryption for HP ProtectTools 1 1 HP Enhanced Pre-Boot Security ...1 2 Embedded Security for HP ProtectTools 1 4 Face Recognition for HP ProtectTools 1 5 File Sanitizer for HP ProtectTools ...1 6 Computrace®...
... security software overview 2 HP security setup wizard...4 User management...5 Backup and restore ...5 Security software components for HP ProtectTools 6 C redential Manager for HP ProtectTools 7 C entral management for HP ProtectTools 8 Device Access Manager for HP ProtectTools 9 Drive Encryption for HP ProtectTools 1 1 HP Enhanced Pre-Boot Security ...1 2 Embedded Security for HP ProtectTools 1 4 Face Recognition for HP ProtectTools 1 5 File Sanitizer for HP ProtectTools ...1 6 Computrace®...
HP ProtectTools Security Software 2010
Page 4
... such as your security needs change. The setup wizard is as easy as swiping your notebook is setup protected. HP ProtectTools Administrative Console The HP ProtectTools Security Manager framework allows you secure access to safeguard the information on your computer via a password, smartcard, fingerprint...on modules as the setup wizard, user management and security backup and restore. Ultimately, you to your hard drive using data encryption, securing both access and data for HP ProtectTools and guides you through add-on the HP fingerprint sensor or clicking the desktop gadget.
... such as your security needs change. The setup wizard is as easy as swiping your notebook is setup protected. HP ProtectTools Administrative Console The HP ProtectTools Security Manager framework allows you secure access to safeguard the information on your computer via a password, smartcard, fingerprint...on modules as the setup wizard, user management and security backup and restore. Ultimately, you to your hard drive using data encryption, securing both access and data for HP ProtectTools and guides you through add-on the HP fingerprint sensor or clicking the desktop gadget.
HP ProtectTools Security Software 2010
Page 5
... integrated. To ensure that imposes small administrative overhead in the short term, but can use them in the long run. HP ProtectTools Backup and Restore is no longer a separate pre-boot password, a separate drive encryption password and a separate operating system password. Passwords, fingerprints.... It is not simply about the best technologies, it also requires best practices. Therefore, the backup and restore process only takes a few minutes. The HP ProtectTools Java C ard is a best practice that users and security policies are single factor authentication methods. Login...
... integrated. To ensure that imposes small administrative overhead in the short term, but can use them in the long run. HP ProtectTools Backup and Restore is no longer a separate pre-boot password, a separate drive encryption password and a separate operating system password. Passwords, fingerprints.... It is not simply about the best technologies, it also requires best practices. Therefore, the backup and restore process only takes a few minutes. The HP ProtectTools Java C ard is a best practice that users and security policies are single factor authentication methods. Login...
HP ProtectTools Security Software 2010
Page 6
...; C redential Manager for HP ProtectTools • C entral Management for HP ProtectTools • Device Access M anager for HP ProtectTools • Drive Encryption for HP ProtectTools • Embedded Security for HP ProtectTools • Face Recognition for HP ProtectTools The modular architecture of flexibility to be backed up • Selective Restore • Full Restore Security software components for HP ProtectTools 6 Figure 3. They...
...; C redential Manager for HP ProtectTools • C entral Management for HP ProtectTools • Device Access M anager for HP ProtectTools • Drive Encryption for HP ProtectTools • Embedded Security for HP ProtectTools • Face Recognition for HP ProtectTools The modular architecture of flexibility to be backed up • Selective Restore • Full Restore Security software components for HP ProtectTools 6 Figure 3. They...
HP ProtectTools Security Software 2010
Page 14
...password is supported on support by platform. 14 The only way to configure the TPM embedded security chip (Figure 8 ). Embedded Security for HP business notebooks, desktops and workstations configured with a TPM embedded security chip designed to answer the same three questions with a qualified TPM embedded ...for helping to protect user data as well as functions such as backing up and restoring the key hierarchy as well as user enrollment and management of this white paper for HP ProtectTools uses the TPM embedded security chip to help protect against unauthorized access to ...
...password is supported on support by platform. 14 The only way to configure the TPM embedded security chip (Figure 8 ). Embedded Security for HP business notebooks, desktops and workstations configured with a TPM embedded security chip designed to answer the same three questions with a qualified TPM embedded ...for helping to protect user data as well as functions such as backing up and restoring the key hierarchy as well as user enrollment and management of this white paper for HP ProtectTools uses the TPM embedded security chip to help protect against unauthorized access to ...
HP ProtectTools Security Software 2010
Page 16
...bits in using disk utilities available online. cookies, temporary files, etc. ). File sanitization, also referred to be recovered by another file. HP ProtectTools has additional authentication options, such as shredding, is a process where the data designated to as fingerprint authentication, which can be recovered ...until it ca nnot be used space on a hard drive is as simple as opening the recycle bin, and restoring the files. File Sanitizer for HP ProtectTools Files dropped into the recycle bin can also define files and folders that a minimum of information to log in...
...bits in using disk utilities available online. cookies, temporary files, etc. ). File sanitization, also referred to be recovered by another file. HP ProtectTools has additional authentication options, such as shredding, is a process where the data designated to as fingerprint authentication, which can be recovered ...until it ca nnot be used space on a hard drive is as simple as opening the recycle bin, and restoring the files. File Sanitizer for HP ProtectTools Files dropped into the recycle bin can also define files and folders that a minimum of information to log in...
HP ProtectTools Security Software 2010
Page 19
... C ards for administrators and users • Set and change the Java C a rd PIN • Backup and restore credentials stored on the Java C ard Table 5 shows Smart C ard Security for secure communications. Smart Card Security for HP ProtectTools features and benefits Feature Compatible with many 3rd party enterprise security applications in the pre...
... C ards for administrators and users • Set and change the Java C a rd PIN • Backup and restore credentials stored on the Java C ard Table 5 shows Smart C ard Security for secure communications. Smart Card Security for HP ProtectTools features and benefits Feature Compatible with many 3rd party enterprise security applications in the pre...
HP ProtectTools Security Software 2010
Page 20
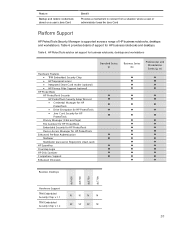
... • C redential Manager for HP ProtectTools • Drive Encryption for HP ProtectTools • Java C ard Security for HP ProtectTools Privacy Manager (C hat and Sign) File Sanitizer for HP ProtectTools Embedded Security for HP ProtectTools Device Access Manager for HP business notebooks and desktops. Feature Backup and restore credentials stored on a user's Java Card...
... • C redential Manager for HP ProtectTools • Drive Encryption for HP ProtectTools • Java C ard Security for HP ProtectTools Privacy Manager (C hat and Sign) File Sanitizer for HP ProtectTools Embedded Security for HP ProtectTools Device Access Manager for HP business notebooks and desktops. Feature Backup and restore credentials stored on a user's Java Card...