User Manual
Page 5
Administration & Management 103 9.1 Configuration Access Control 103 9.1.1 Remote Management 103 9.1.2 CLI Access...104 9.2 SNMP Configuration 104 9.3 Configuring Time Zone and NTP 106 9.4 Log Configuration 107 9.4.1 Defining What to Log 107 3 Advanced Configuration Tools ...
Administration & Management 103 9.1 Configuration Access Control 103 9.1.1 Remote Management 103 9.1.2 CLI Access...104 9.2 SNMP Configuration 104 9.3 Configuring Time Zone and NTP 106 9.4 Log Configuration 107 9.4.1 Defining What to Log 107 3 Advanced Configuration Tools ...
User Manual
Page 6
... Using Diagnostic Tools 117 Ping ...118 Trace Route ...118 DNS Lookup ...119 Router Options ...119 Chapter 10. Unified Services Router User Manual 9.4.2 9.4.3 9.5 9.6 9.7 9.8 9.8.1 9.8.2 9.8.3 9.8.4 Sending Logs to a remote device 136 11.4 Restoring factory-default configuration settings 137 Chapter 12. Glossary ...140 Appendix B.
... Using Diagnostic Tools 117 Ping ...118 Trace Route ...118 DNS Lookup ...119 Router Options ...119 Chapter 10. Unified Services Router User Manual 9.4.2 9.4.3 9.5 9.6 9.7 9.8 9.8.1 9.8.2 9.8.3 9.8.4 Sending Logs to a remote device 136 11.4 Restoring factory-default configuration settings 137 Chapter 12. Glossary ...140 Appendix B.
User Manual
Page 9
... configuration ...101 Figure 66: Certificate summary for IPSec and HTTPS management 102 Figure 67: User Login policy configuration 103 Figure 68: Remote Management from the WAN 104 Figure 69: SNMP Users, Traps, and Access Control 105 Figure 70: SNMP system information for this ...Logging 109 Figure 73: Log configuration options for traffic through router 111 Figure 74: E-mail configuration as a Remote Logging option 112 Figure 75: Syslog server configuration for Remote Logging (continued 113 Figure 76: VPN logs displayed in GUI event viewer 114 Figure 77: Restoring configuration from...
... configuration ...101 Figure 66: Certificate summary for IPSec and HTTPS management 102 Figure 67: User Login policy configuration 103 Figure 68: Remote Management from the WAN 104 Figure 69: SNMP Users, Traps, and Access Control 105 Figure 70: SNMP system information for this ...Logging 109 Figure 73: Log configuration options for traffic through router 111 Figure 74: E-mail configuration as a Remote Logging option 112 Figure 75: Syslog server configuration for Remote Logging (continued 113 Figure 76: VPN logs displayed in GUI event viewer 114 Figure 77: Restoring configuration from...
User Manual
Page 68
... that affects traffic on the weekends if the request originates from a specific group of machines in the LAN having a known range of day, select "all remote users). Select "Saturday" and "Sunday" • In the scheduled time of IP addresses, and anyone coming in through NAT. this procedure: Router • WAN IP...
... that affects traffic on the weekends if the request originates from a specific group of machines in the LAN having a known range of day, select "all remote users). Select "Saturday" and "Sunday" • In the scheduled time of IP addresses, and anyone coming in through NAT. this procedure: Router • WAN IP...
User Manual
Page 81
... > Wizard > VPN Wizard You can use the VPN wizard to secure traffic between two gateway routers or a remote PC client. The following types of tunnels can modify it as the IP address of the remote PC client is not known in advance. Once the IKE or VPN policy is behind a NAT Router... client at the NAT router initiates a VPN tunnel as required. 79 The gateway WAN port acts as a responder. • Remote client behind a NAT router: The client has a dynamic IP address and is created, you can be created: • Gateway-to-gateway VPN: to connect two ...
... > Wizard > VPN Wizard You can use the VPN wizard to secure traffic between two gateway routers or a remote PC client. The following types of tunnels can modify it as the IP address of the remote PC client is not known in advance. Once the IKE or VPN policy is behind a NAT Router... client at the NAT router initiates a VPN tunnel as required. 79 The gateway WAN port acts as a responder. • Remote client behind a NAT router: The client has a dynamic IP address and is created, you can be created: • Gateway-to-gateway VPN: to connect two ...
User Manual
Page 82
...is used for management, and the pre-shared key will be configured for the tunnel endpoints • Remote Gateway Type: identify the remote endpoint of the tunnel by FQDN or static IP address 80 Step 2: Configure Remote and Local WAN address for either be a gateway to gateway connection (site-to-site) or a tunnel... follow the steps below: 1. if there is more than 1 WAN configured the tunnel can either of the tunnel by FQDN or static IP address • Remote WAN IP address / FQDN: This field is enabled only if the peer you are trying to connect to a host on the VPN client or gateway...
...is used for management, and the pre-shared key will be configured for the tunnel endpoints • Remote Gateway Type: identify the remote endpoint of the tunnel by FQDN or static IP address 80 Step 2: Configure Remote and Local WAN address for either be a gateway to gateway connection (site-to-site) or a tunnel... follow the steps below: 1. if there is more than 1 WAN configured the tunnel can either of the tunnel by FQDN or static IP address • Remote WAN IP address / FQDN: This field is enabled only if the peer you are trying to connect to a host on the VPN client or gateway...
User Manual
Page 83
...: review the settings and click Connect to the online help for a VPN Client or Gateway policy (these can modify the required fields through the edit link. Once the Wizard creates the matching IKE and VPN policies required by the Auto policy, one specified in the WAN port's configuration. 3. Step 3:... blank if you are not using a different FQDN or IP address than the one can be different from the IP address range used on the remote LAN must be accessed from Wizard Aggressive (Client policy ) or Main (Gateway policy) FQDN wan_local.com (only applies to Client policies) wan_remote.com ...
...: review the settings and click Connect to the online help for a VPN Client or Gateway policy (these can modify the required fields through the edit link. Once the Wizard creates the matching IKE and VPN policies required by the Auto policy, one specified in the WAN port's configuration. 3. Step 3:... blank if you are not using a different FQDN or IP address than the one can be different from the IP address range used on the remote LAN must be accessed from Wizard Aggressive (Client policy ) or Main (Gateway policy) FQDN wan_local.com (only applies to Client policies) wan_remote.com ...
User Manual
Page 84
... > VPN Settings > IPSec > IPSec Policies A IPSec policy is between the two policy endpoints. • Transport: This is used for end-to hosts on the remote LAN. The IPSec mode can enable NetBIOS and DHCP over the tunnel. 82 Only the data payload is encrypted and the IP header is not... header is encrypted and/or authenticated. When tunnel mode is one endpoint of IPs, or subnet on a remote host. As well in this router and a IPSec client on both the local and remote private networks that can define the single IP address, range of the tunnel. In this gateway is selected...
... > VPN Settings > IPSec > IPSec Policies A IPSec policy is between the two policy endpoints. • Transport: This is used for end-to hosts on the remote LAN. The IPSec mode can enable NetBIOS and DHCP over the tunnel. 82 Only the data payload is encrypted and the IP header is not... header is encrypted and/or authenticated. When tunnel mode is one endpoint of IPs, or subnet on a remote host. As well in this router and a IPSec client on both the local and remote private networks that can define the single IP address, range of the tunnel. In this gateway is selected...
User Manual
Page 86
...IKE and instead relies on manual keying to establish successfully. The incoming and outgoing security parameter index (SPI) values must match on the remote tunnel endpoint. Note that using Auto policies with IKE are preferred as in order for the tunnel to exchange authentication parameters between the two... IPSec hosts. As well the encryption and integrity algorithms and keys must be mirrored on the remote IPSec host exactly in some IPSec implementations the SPI (security parameter index) values require conversion at each endpoint. 84
...IKE and instead relies on manual keying to establish successfully. The incoming and outgoing security parameter index (SPI) values must match on the remote tunnel endpoint. Note that using Auto policies with IKE are preferred as in order for the tunnel to exchange authentication parameters between the two... IPSec hosts. As well the encryption and integrity algorithms and keys must be mirrored on the remote IPSec host exactly in some IPSec implementations the SPI (security parameter index) values require conversion at each endpoint. 84
User Manual
Page 87
... server with the same VPN policy parameters used to authenticate users. if they are not, the router connects to the RADIUS server. 6.3 Configuring VPN clients Remote VPN clients must also be configured with the authentication protocol supported by the server (PAP or CHAP). Upon establishing these authentication parameters, the VPN Client...
... server with the same VPN policy parameters used to authenticate users. if they are not, the router connects to the RADIUS server. 6.3 Configuring VPN clients Remote VPN clients must also be configured with the authentication protocol supported by the server (PAP or CHAP). Upon establishing these authentication parameters, the VPN Client...
User Manual
Page 88
... through this router. Once authenticated by the PPTP server (the tunnel endpoint), PPTP clients have access to create a TCP control connection between the router and remote endpoint. Refer to establish a VPN tunnel between the LAN VPN client and the VPN server. 6.4.1 PPTP Tunnel Support Setup > VPN Settings > PPTP > PPTP Server A PPTP...
... through this router. Once authenticated by the PPTP server (the tunnel endpoint), PPTP clients have access to create a TCP control connection between the router and remote endpoint. Refer to establish a VPN tunnel between the LAN VPN client and the VPN server. 6.4.1 PPTP Tunnel Support Setup > VPN Settings > PPTP > PPTP Server A PPTP...
User Manual
Page 91
... of the users (IPSec, SSL VPN, or GUI) is installed in the remote host to allow remote users to access the LAN over an encrypted link through the SSL User Portal using the Internet Explorer browser. The remote user must specify the user, group and domain when logging in place of a... preinstalled VPN client on the remote host to remote port forwarding users instead of a Group. Instead, users...
... of the users (IPSec, SSL VPN, or GUI) is installed in the remote host to allow remote users to access the LAN over an encrypted link through the SSL User Portal using the Internet Explorer browser. The remote user must specify the user, group and domain when logging in place of a... preinstalled VPN client on the remote host to remote port forwarding users instead of a Group. Instead, users...
User Manual
Page 92
... access policies to a select few. The 90 Advanced > Users > Groups Groups are domain subsets that can be created and assigned to the remote SSL user. Unified Services Router Figure 55: Available Users with minimal number of SSL users; As well the Domain determines the portal layout presented ...(local user database, external server) to be seen as types of policies to configure. With groups, a very secure hierarchy of SSL VPN remote access can be created for all available network resources and some can be specified by browser, IP address of the host, and whether the user...
... access policies to a select few. The 90 Advanced > Users > Groups Groups are domain subsets that can be created and assigned to the remote SSL user. Unified Services Router Figure 55: Available Users with minimal number of SSL users; As well the Domain determines the portal layout presented ...(local user database, external server) to be seen as types of policies to configure. With groups, a very secure hierarchy of SSL VPN remote access can be created for all available network resources and some can be specified by browser, IP address of the host, and whether the user...
User Manual
Page 96
Once this resource as required. 94 The Network Address, Mask Length, and Port Range/Port Number can all be defined for multiple remote SSL VPN users. Unified Services Router Figure 58: SSL VPN policy configuration User Manual 7.2.1 Using Network Resources Setup > VPN Settings > SSL VPN Server > Resources Network ...
Once this resource as required. 94 The Network Address, Mask Length, and Port Range/Port Number can all be defined for multiple remote SSL VPN users. Unified Services Router Figure 58: SSL VPN policy configuration User Manual 7.2.1 Using Network Resources Setup > VPN Settings > SSL VPN Server > Resources Network ...
User Manual
Page 97
...available to assign to SSL VPN policies 7.3 Application Port Forwarding Setup > VPN Settings > SSL VPN Server > Port Forwarding Port forwarding allows remote SSL users to access specified network applications or services after they login to the User Portal and launch the Port Forwarding service. This host ...name resolution provides 95 Traffic from the remote user to allow for IP address resolution. Unified Services Router User Manual Figure 59: List of the application to be tunneled. The...
...available to assign to SSL VPN policies 7.3 Application Port Forwarding Setup > VPN Settings > SSL VPN Server > Port Forwarding Port forwarding allows remote SSL users to access specified network applications or services after they login to the User Portal and launch the Port Forwarding service. This host ...name resolution provides 95 Traffic from the remote user to allow for IP address resolution. Unified Services Router User Manual Figure 59: List of the application to be tunneled. The...
User Manual
Page 98
... IP address of the VPN tunnel client does not conflict with an IP address from the user portal, a "network adapter" with physical devices on the remote SSL VPN client machine. Unified Services Router User Manual users with easy-to-remember FQDN's to -point connection between the browserside machine and this router...
... IP address of the VPN tunnel client does not conflict with an IP address from the user portal, a "network adapter" with physical devices on the remote SSL VPN client machine. Unified Services Router User Manual users with easy-to-remember FQDN's to -point connection between the browserside machine and this router...
User Manual
Page 99
... identical to the router's IP address or a server on the corporate LAN that is needed to forward private traffic through the VPN Firewall to the remote SSL VPN client. 97 Split tunnel mode only sends traffic to the private LAN based on the private LAN's firewall (typically this router) is being...
... identical to the router's IP address or a server on the corporate LAN that is needed to forward private traffic through the VPN Firewall to the remote SSL VPN client. 97 Split tunnel mode only sends traffic to the private LAN based on the private LAN's firewall (typically this router) is being...
User Manual
Page 100
... presented to provide the appropriate access levels and privileges as determined by the router administrator. This portal provides the authentication fields to the remote user. 98 Unified Services Router User Manual Figure 62: Configured client routes only apply in split tunnel mode 7.5 User Portal Setup >... VPN Settings > SSL VPN Client > SSL VPN Client Portal When remote users want to access the private network through an SSL tunnel (either using the Port Forwarding or VPN tunnel service), they login through a ...
... presented to provide the appropriate access levels and privileges as determined by the router administrator. This portal provides the authentication fields to the remote user. 98 Unified Services Router User Manual Figure 62: Configured client routes only apply in split tunnel mode 7.5 User Portal Setup >... VPN Settings > SSL VPN Client > SSL VPN Client Portal When remote users want to access the private network through an SSL tunnel (either using the Port Forwarding or VPN tunnel service), they login through a ...
User Manual
Page 101
...The portal name is https://192.168.10.1/scgibin/userPortal/portal. The portal name, title, banner name, and banner contents are available to remote users. The router administrator creates and edits portal layouts from the configuration pages in the portal visible to select for all customizable to this portal... and other usage details in the SSL VPN menu. As well, the users assigned to the intended users for remote SSL VPN users that opens when the "User Portal" link is presented upon authentication. This is the same page that is clicked on the SSL VPN menu of configured SSL...
...The portal name is https://192.168.10.1/scgibin/userPortal/portal. The portal name, title, banner name, and banner contents are available to remote users. The router administrator creates and edits portal layouts from the configuration pages in the portal visible to select for all customizable to this portal... and other usage details in the SSL VPN menu. As well, the users assigned to the intended users for remote SSL VPN users that opens when the "User Portal" link is presented upon authentication. This is the same page that is clicked on the SSL VPN menu of configured SSL...
User Manual
Page 105
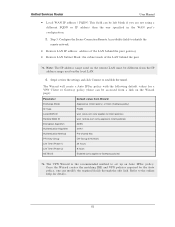
... opened port for SSL traffic can define a known PC, single IP address or range of 443 at the same time as defining the allowed remote management IP address range. 103 The router administrator can be configured to the router's management interface. The GUI can be accessed from LAN node ...the LAN or the Internet (WAN) by using the gateway's WAN IP address and HTTPS (HTTP over SSL). Figure 67: User Login policy configuration 9.1.1 Remote Management Both HTTPS and telnet access can be restricted to configure this gateway via the browser-independent GUI. The user type is set in the...
... opened port for SSL traffic can define a known PC, single IP address or range of 443 at the same time as defining the allowed remote management IP address range. 103 The router administrator can be configured to the router's management interface. The GUI can be accessed from LAN node ...the LAN or the Internet (WAN) by using the gateway's WAN IP address and HTTPS (HTTP over SSL). Figure 67: User Login policy configuration 9.1.1 Remote Management Both HTTPS and telnet access can be restricted to configure this gateway via the browser-independent GUI. The user type is set in the...