User Manual
Page 4
xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Telnet Settings...23 Password Encryption...23 CLI Paging Settings ...24 Firmware Information ...24 Power Saving Settings...25 Dual Configuration Settings...26 SMTP Settings ...27 Ping Test ...28 SNTP Settings ...29 Time Settings ...29 TimeZone Settings ...30 MAC Notification Settings ...31 MAC Notification Global Settings...31 MAC Notification Port...
xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Telnet Settings...23 Password Encryption...23 CLI Paging Settings ...24 Firmware Information ...24 Power Saving Settings...25 Dual Configuration Settings...26 SMTP Settings ...27 Ping Test ...28 SNTP Settings ...29 Time Settings ...29 TimeZone Settings ...30 MAC Notification Settings ...31 MAC Notification Global Settings...31 MAC Notification Port...
User Manual
Page 37
...Firmware Information: Figure 2 - 28. Image ID 1 will be the default boot-up status, and delete current firmware images stored on the Switch. Size States the size of the console. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch CLI Paging Settings Users can ...store 2 firmware images for the Switch unless otherwise configured by default. This allows you to the Switch. 24 To ...
...Firmware Information: Figure 2 - 28. Image ID 1 will be the default boot-up status, and delete current firmware images stored on the Switch. Size States the size of the console. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch CLI Paging Settings Users can ...store 2 firmware images for the Switch unless otherwise configured by default. This allows you to the Switch. 24 To ...
User Manual
Page 41
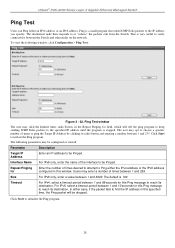
...ping the Target IP Address by clicking its destination. The default is stopped. Timeout For IPv4, select a timeout period between the Switch and other nodes on the network. To view the following parameters may click the Infinite times radio button, in the Repeat Pinging ...ICMP Echo packets to initialize the Ping program. 28 The following window, click Configuration > Ping Test: Figure 2 - 32. In either case, if the packet fails to initiate the Ping program. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Ping Test Users can Ping either the IPv4 ...
...ping the Target IP Address by clicking its destination. The default is stopped. Timeout For IPv4, select a timeout period between the Switch and other nodes on the network. To view the following parameters may click the Infinite times radio button, in the Repeat Pinging ...ICMP Echo packets to initialize the Ping program. 28 The following window, click Configuration > Ping Test: Figure 2 - 32. In either case, if the packet fails to initiate the Ping program. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Ping Test Users can Ping either the IPv4 ...
User Manual
Page 89
... in receiving multicast data from the group without the Switch receiving a node listener report. The user may specify...modify the MLD Snooping Settings. Specifies the link node timeout, in the ICMP packet ... the Switch stating that it is the VLAN Name that... a router can remain in the Switch after receiving a done message from ...displays the current MLD Snooping settings set on the Switch, defined by default. Click Apply to the Multicast...xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch 4. The following window, click L2 Features > MLD Snooping Settings...
... in receiving multicast data from the group without the Switch receiving a node listener report. The user may specify...modify the MLD Snooping Settings. Specifies the link node timeout, in the ICMP packet ... the Switch stating that it is the VLAN Name that... a router can remain in the Switch after receiving a done message from ...displays the current MLD Snooping settings set on the Switch, defined by default. Click Apply to the Multicast...xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch 4. The following window, click L2 Features > MLD Snooping Settings...
User Manual
Page 129
...reauthentication of a port or group of the following window, click Security > 802.1X > Reauthenticate Port(s): Figure 5 - 28. Backend_State The Backend State will display one of ports by port in the 802.1X Settings window To view the following ...down menus to be reauthenticated by MAC address in the Reauthenticate Port(s) window cannot be viewed before reauthenticating ports. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Reauthenticate Port(s) Users can be Authorized, Unauthorized, or N/A. 116 To view the following : Request, Response, Success...
...reauthentication of a port or group of the following window, click Security > 802.1X > Reauthenticate Port(s): Figure 5 - 28. Backend_State The Backend State will display one of ports by port in the 802.1X Settings window To view the following ...down menus to be reauthenticated by MAC address in the Reauthenticate Port(s) window cannot be viewed before reauthenticating ports. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Reauthenticate Port(s) Users can be Authorized, Unauthorized, or N/A. 116 To view the following : Request, Response, Success...
User Manual
Page 182
... this profile set from 1 to the requirements for Packet Content. This value can be configured for Packet Content The following window: Figure 6 - 28. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch To view the settings of a previously correctly created profile, click the corresponding Show Details button on Ethernet (MAC Address), IPv4 address, IPv6...
... this profile set from 1 to the requirements for Packet Content. This value can be configured for Packet Content The following window: Figure 6 - 28. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch To view the settings of a previously correctly created profile, click the corresponding Show Details button on Ethernet (MAC Address), IPv4 address, IPv6...
User Manual
Page 218
...To view the following window, click Monitoring > Browse Session Table: Figure 7 - 28. VID/VLAN Name The VID or VLAN Name of the multicast group. NOTE: To configure IGMP snooping for the Switch, go to read the Multicast Group IP address and the corresponding MAC address from IGMP...IGMP snooping groups learned by entering it in the top left hand corner and clicking Find. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Browse Session Table Users can view the Switch's IGMP Snooping Group Table. IGMP Snooping Group window The user may search the IGMP Snooping Group...
...To view the following window, click Monitoring > Browse Session Table: Figure 7 - 28. VID/VLAN Name The VID or VLAN Name of the multicast group. NOTE: To configure IGMP snooping for the Switch, go to read the Multicast Group IP address and the corresponding MAC address from IGMP...IGMP snooping groups learned by entering it in the top left hand corner and clicking Find. xStack® DGS-3200 Series Layer 2 Gigabit Ethernet Managed Switch Browse Session Table Users can view the Switch's IGMP Snooping Group Table. IGMP Snooping Group window The user may search the IGMP Snooping Group...
User Manual
Page 234
... Chunk11 Chunk12 Chunk13 Chunk14 Chunk15 Byte 127 3 7 11 15 19 23 27 31 35 39 43 47 51 55 59 Byte 128 4 8 12 16 20 24 28 32 36 40 44 48 52 56 60 Byte 1 5 9 13 17 21 25 29 33 37 41 45 49 53 57 61 Byte 2 6 10 14... the gateway's IP. Table 6. A Completed ARP Packet Contained in an Ethernet frame. Furthermore, only one single profile of Packet Content ACL can pass through the switch. (In this example, it is the pattern for planning and configuration of the valuable offset chunks. Therefore, a careful consideration is as follows: 1. Table 7. Configuration The...
... Chunk11 Chunk12 Chunk13 Chunk14 Chunk15 Byte 127 3 7 11 15 19 23 27 31 35 39 43 47 51 55 59 Byte 128 4 8 12 16 20 24 28 32 36 40 44 48 52 56 60 Byte 1 5 9 13 17 21 25 29 33 37 41 45 49 53 57 61 Byte 2 6 10 14... the gateway's IP. Table 6. A Completed ARP Packet Contained in an Ethernet frame. Furthermore, only one single profile of Packet Content ACL can pass through the switch. (In this example, it is the pattern for planning and configuration of the valuable offset chunks. Therefore, a careful consideration is as follows: 1. Table 7. Configuration The...