Product Manual
Page 19
...totally for use by the rule sets. The notion of rules (or rule sets). Another example of logical objects are forwarded without any possibility to perform in documentation as predefined building blocks for the administrator to define additional parameters on information found in... apply bandwidth management and a variety of the network traffic which represent specific protocol and port combinations. Traditional IP routers or switches commonly inspect all packets and then perform forwarding decisions based on specific protocols such as being established, and keeps a small piece of...
...totally for use by the rule sets. The notion of rules (or rule sets). Another example of logical objects are forwarded without any possibility to perform in documentation as predefined building blocks for the administrator to define additional parameters on information found in... apply bandwidth management and a variety of the network traffic which represent specific protocol and port combinations. Traditional IP routers or switches commonly inspect all packets and then perform forwarding decisions based on specific protocols such as being established, and keeps a small piece of...
Product Manual
Page 21
... being the matched tunnel interface. If the action is Drop, the packet is dropped and the event is present, the packet might have to be forwarded out on , to further analyze or transform the traffic. • If the contents of the packet is sent into NetDefendOS again, now with IPsec...continues at step 3 above. • If traffic management information is logged according to the log settings for example TCP, UDP, ICMP) • TCP/UDP ports • ICMP types • Point in time in the state, NetDefendOS now knows what NetDefendOS should do with the incoming packet: • If ALG ...
... being the matched tunnel interface. If the action is Drop, the packet is dropped and the event is present, the packet might have to be forwarded out on , to further analyze or transform the traffic. • If the contents of the packet is sent into NetDefendOS again, now with IPsec...continues at step 3 above. • If traffic management information is logged according to the log settings for example TCP, UDP, ICMP) • TCP/UDP ports • ICMP types • Point in time in the state, NetDefendOS now knows what NetDefendOS should do with the incoming packet: • If ALG ...
Product Manual
Page 99
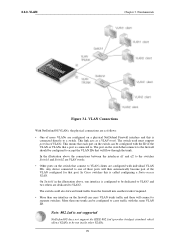
Fundamentals Figure 3.1. Any device connected to one trunk can be dedicated to VLAN2. The switch could also forward trunk traffic from the firewall into another trunk if required. • More than one of these will flow through the trunk. Note: 802.1ad is... connect to VLAN clients are dedicated to VLAN1 and two others are configured with individual VLAN IDs. This link acts as follows: • One of more VLANs are configured on the switch that a port is called configuring a Static-access VLAN. On Switch1 in the illustration above the connections between the interfaces ...
Fundamentals Figure 3.1. Any device connected to one trunk can be dedicated to VLAN2. The switch could also forward trunk traffic from the firewall into another trunk if required. • More than one of these will flow through the trunk. Note: 802.1ad is... connect to VLAN clients are dedicated to VLAN1 and two others are configured with individual VLAN IDs. This link acts as follows: • One of more VLANs are configured on the switch that a port is called configuring a Static-access VLAN. On Switch1 in the illustration above the connections between the interfaces ...
Product Manual
Page 250
The FTP ALG Chapter 6. Now enter: • Name: SAT-ftp-inbound • Action: SAT • Service: ftp-inbound-service 3. New Port: 21 7. Now enter: • Name: NAT-ftp • Action: NAT • Service: ftp-inbound-service 3. For NAT check Use Interface Address 5....Rules > Add > IPRule 2. For SAT check Translate the Destination IP Address 5. Click OK E. Define a rule to allow connections to the public IP on port 21 and forward that to the internal FTP server: 1. For Address Filter enter: • Source Interface: dmz • Destination Interface: core • Source Network: dmznet ...
The FTP ALG Chapter 6. Now enter: • Name: SAT-ftp-inbound • Action: SAT • Service: ftp-inbound-service 3. New Port: 21 7. Now enter: • Name: NAT-ftp • Action: NAT • Service: ftp-inbound-service 3. For NAT check Use Interface Address 5....Rules > Add > IPRule 2. For SAT check Translate the Destination IP Address 5. Click OK E. Define a rule to allow connections to the public IP on port 21 and forward that to the internal FTP server: 1. For Address Filter enter: • Source Interface: dmz • Destination Interface: core • Source Network: dmznet ...
Product Manual
Page 269
...user. Security Mechanisms The SIP proxy in any setup. The NetDefendOS SIP ALG will automatically locate the local receiver, perform address translation and forward SIP messages to the IP of all NAT traversal issues in two ways: • Using NAT to the NAT rule above. Define a.... When a SIP client behind a NATing NetDefend Firewall registers with the SIP ALG object. The proxy should have: • Destination Port set to 5060 (the default SIP signalling port). • Type set : • A NAT rule for this scenario are being NATed. • An Allow rule for translating...
...user. Security Mechanisms The SIP proxy in any setup. The NetDefendOS SIP ALG will automatically locate the local receiver, perform address translation and forward SIP messages to the IP of all NAT traversal issues in two ways: • Using NAT to the NAT rule above. Define a.... When a SIP client behind a NATing NetDefend Firewall registers with the SIP ALG object. The proxy should have: • Destination Port set to 5060 (the default SIP signalling port). • Type set : • A NAT rule for this scenario are being NATed. • An Allow rule for translating...
Product Manual
Page 273
... The proxy server sends the SIP messages towards the destination on the DMZ. • The IP address of the 273 The local proxy forwards the reply to the outbound local proxy server on the DMZ interface. Using NAT The following should have the IP address of the DMZ interface... rule. Solution A - Define four rules in a topology hiding setup with the proxy on the DMZ will have : • Destination Port set to 5060 (the default SIP signalling port) • Type set : • A NAT rule for outbound traffic from the clients on the external interface. This address can be...
... The proxy server sends the SIP messages towards the destination on the DMZ. • The IP address of the 273 The local proxy forwards the reply to the outbound local proxy server on the DMZ interface. Using NAT The following should have the IP address of the DMZ interface... rule. Solution A - Define four rules in a topology hiding setup with the proxy on the DMZ will have : • Destination Port set to 5060 (the default SIP signalling port) • Type set : • A NAT rule for outbound traffic from the clients on the external interface. This address can be...
Product Manual
Page 276
...between endpoints, or it may allow calls to establish a connection between H.323 networks and non-H.323 networks such as follow-me/find-me, forward on the type of H.323 product, T.120 protocol can also take care of logical channels. The H.323 specification was not designed to ...make sure that allows H.323 devices such as H.323 phones and applications to handle NAT, as IP addresses and ports are used for application sharing, file transfer as well as whiteboards. 6.2.9. H.245 Media Control and Transport Provides control of communication and application ...
...between endpoints, or it may allow calls to establish a connection between H.323 networks and non-H.323 networks such as follow-me/find-me, forward on the type of H.323 product, T.120 protocol can also take care of logical channels. The H.323 specification was not designed to ...make sure that allows H.323 devices such as H.323 phones and applications to handle NAT, as IP addresses and ports are used for application sharing, file transfer as well as whiteboards. 6.2.9. H.245 Media Control and Transport Provides control of communication and application ...
Product Manual
Page 343
... the administrator can translate entire ranges of the network known as an Allow rule, must first be defined. Note: Port forwarding Some network equipment vendors use the term "port forwarding" when referring to the destination 1.1.1.1 and not 2.2.2.2. This scenario is known as a Virtual IP or Virtual Server ...rule only defines the translation that has a private address. A common mistake is to have the maximum exposure to the same address or port. The Role of the DMZ At this access takes place across the public Internet. 7.4. SAT Requires Multiple IP Rules Unlike NAT, ...
... the administrator can translate entire ranges of the network known as an Allow rule, must first be defined. Note: Port forwarding Some network equipment vendors use the term "port forwarding" when referring to the destination 1.1.1.1 and not 2.2.2.2. This scenario is known as a Virtual IP or Virtual Server ...rule only defines the translation that has a private address. A common mistake is to have the maximum exposure to the same address or port. The Role of the DMZ At this access takes place across the public Internet. 7.4. SAT Requires Multiple IP Rules Unlike NAT, ...
Product Manual
Page 426
VPN TCP port 1723 and/or IP protocol 47 before the PPTP connection can indicate if this example. 9.5.2. Enter a name for the PPTP Server, for example MyPPTPServer 3. To ... with a large number of clients and arguably offers better security than PPTP. In most cases the client will use of the best features of Layer 2 Forwarding (L2F) protocol and PPTP, making use to give out IP addresses to the NetDefend Firewall. Because it is IPsec based, L2TP requires NAT traversal (NAT...
VPN TCP port 1723 and/or IP protocol 47 before the PPTP connection can indicate if this example. 9.5.2. Enter a name for the PPTP Server, for example MyPPTPServer 3. To ... with a large number of clients and arguably offers better security than PPTP. In most cases the client will use of the best features of Layer 2 Forwarding (L2F) protocol and PPTP, making use to give out IP addresses to the NetDefend Firewall. Because it is IPsec based, L2TP requires NAT traversal (NAT...
Product Manual
Page 454
... be ignored by NetDefendOS. Precedences Chapter 10. Traffic flowing through 23 into two rules, covering 22 and 23, respectively: Keep the forward chain of traffic with lower precedences. Differentiated Guarantees A problem arises if the aim is limited to SSH traffic. The solution is to... of a problem here, but it has, at the best effort precedence is then forwarded on inbound traffic, which is the direction that specific precedence. Then, split the previously defined rule covering ports 22 through a pipe will get the guarantee specified for the lowest (best effort) ...
... be ignored by NetDefendOS. Precedences Chapter 10. Traffic flowing through 23 into two rules, covering 22 and 23, respectively: Keep the forward chain of traffic with lower precedences. Differentiated Guarantees A problem arises if the aim is limited to SSH traffic. The solution is to... of a problem here, but it has, at the best effort precedence is then forwarded on inbound traffic, which is the direction that specific precedence. Then, split the previously defined rule covering ports 22 through a pipe will get the guarantee specified for the lowest (best effort) ...
Product Manual
Page 511
... in the wrong way and can, in the TCP header, which should be 0. This field is forwarded. 511 Default: DropLog TCP URG Specifies how NetDefendOS will deal with TCP packets with both OS Fingerprinting and stealth port scanners, as FTP and MS SQL Server, nearly always use of the SYN, ACK, FIN...
... in the wrong way and can, in the TCP header, which should be 0. This field is forwarded. 511 Default: DropLog TCP URG Specifies how NetDefendOS will deal with TCP packets with both OS Fingerprinting and stealth port scanners, as FTP and MS SQL Server, nearly always use of the SYN, ACK, FIN...
Product Manual
Page 542
..., 190 command, 190 concepts, 174 dynamic routing rules, 185 interface, 182 neighbors, 184 router process, 179 setting up, 188 virtual links, 176, 184 Other Idle Lifetimes setting, 516 overriding content filtering, 299 P packet flow full description, 23 simplified, 118 password length,...rules, 445 pipes, 445 policies, 116 policy based routing, 160 Poll Interval setting, 65 POP3 ALG, 263 Port 0 setting, 525 port address translation, 350 port forwarding (see SAT) port mirroring (see pcapdump) PPP authentication with LDAP, 364 PPPoE, 101 client configuration, 101 unnumbered support, 102 with ...
..., 190 command, 190 concepts, 174 dynamic routing rules, 185 interface, 182 neighbors, 184 router process, 179 setting up, 188 virtual links, 176, 184 Other Idle Lifetimes setting, 516 overriding content filtering, 299 P packet flow full description, 23 simplified, 118 password length,...rules, 445 pipes, 445 policies, 116 policy based routing, 160 Poll Interval setting, 65 POP3 ALG, 263 Port 0 setting, 525 port address translation, 350 port forwarding (see SAT) port mirroring (see pcapdump) PPP authentication with LDAP, 364 PPPoE, 101 client configuration, 101 unnumbered support, 102 with ...
Product Manual
Page 543
...Relay MPLS setting, 221 Relay Spanning-tree BPDUs setting, 218, 220 restore to factory defaults, 74 restoring configuration backups, 73 reverse path forwarding (see multicast) reverse route lookup, 118, 147, 237 roaming clients, 408 roundrobin RLB algorithm, 165 route failover, 151 host monitoring... association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address translation, 348 multiplex rule, 195 port forwarding, 343 second rule destination, 343 schedules, 126 SCP, 45 scripting (see CLI scripts) Secondary Time Server setting, 137 secure copy (see ...
...Relay MPLS setting, 221 Relay Spanning-tree BPDUs setting, 218, 220 restore to factory defaults, 74 restoring configuration backups, 73 reverse path forwarding (see multicast) reverse route lookup, 118, 147, 237 roaming clients, 408 roundrobin RLB algorithm, 165 route failover, 151 host monitoring... association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address translation, 348 multiplex rule, 195 port forwarding, 343 second rule destination, 343 schedules, 126 SCP, 45 scripting (see CLI scripts) Secondary Time Server setting, 137 secure copy (see ...