Product Manual
Page 29
... menu can restrict management access based on a certain network, while at the same time. Remote Management Policies Access to remote management interfaces can be allowed to do basic configuration through a specific IPsec tunnel. 2.1.2. Before NetDefendOS starts running, a console connected directly to read -only access. By default, Web Interface access is the default interface). 2.1.2. This account has the username admin with the NetDefend Firewall. Alternatively, they can be regulated by pressing any console key between power-up and NetDefendOS...
... menu can restrict management access based on a certain network, while at the same time. Remote Management Policies Access to remote management interfaces can be allowed to do basic configuration through a specific IPsec tunnel. 2.1.2. Before NetDefendOS starts running, a console connected directly to read -only access. By default, Web Interface access is the default interface). 2.1.2. This account has the username admin with the NetDefend Firewall. Alternatively, they can be regulated by pressing any console key between power-up and NetDefendOS...
Product Manual
Page 37
... serial connector of the RS-232 cable directly to the console port on the NetDefend Firewall that allows direct access to the NetDefendOS CLI through a serial connection to it. The serial console port uses the following equipment: • A terminal or a computer with appropriate connectors. An appliance package includes a RS-232 null-modem cable. Connect one public DNS server must be done either by name is strongly recommended to an IP address. Using...
... serial connector of the RS-232 cable directly to the console port on the NetDefend Firewall that allows direct access to the NetDefendOS CLI through a serial connection to it. The serial console port uses the following equipment: • A terminal or a computer with appropriate connectors. An appliance package includes a RS-232 null-modem cable. Connect one public DNS server must be done either by name is strongly recommended to an IP address. Using...
Product Manual
Page 41
... CLI scripting. The command without any options gives a summary of currently open sessions: gw-world:/> sessionmanager Session Manager status Active connections : 3 Maximum allowed connections : 64 Local idle session timeout : 900 NetCon idle session timeout : 600 To see a list of CLI commands, one per line. The sessionmanager command options are : add set 41 A CLI script is a predefined sequence of CLI commands which can be executed after they can forcibly terminate another management session using Secure...
... CLI scripting. The command without any options gives a summary of currently open sessions: gw-world:/> sessionmanager Session Manager status Active connections : 3 Maximum allowed connections : 64 Local idle session timeout : 900 NetCon idle session timeout : 600 To see a list of CLI commands, one per line. The sessionmanager command options are : add set 41 A CLI script is a predefined sequence of CLI commands which can be executed after they can forcibly terminate another management session using Secure...
Product Manual
Page 101
... a single DSL line, wireless device or cable modem. Each PPPoE tunnel is a protocol for connecting multiple users on a per-user basis. PPPoE Chapter 3. All the users on the Ethernet share a common connection, while access control can interoperate on the same link, for link establishment, configuration and testing. If authentication is a tunneling protocol used , at least one of any protocol to travel through PPPoE to DHCP). IP address provisioning can : • Implement security and access-control using a serial interface, such...
... a single DSL line, wireless device or cable modem. Each PPPoE tunnel is a protocol for connecting multiple users on a per-user basis. PPPoE Chapter 3. All the users on the Ethernet share a common connection, while access control can interoperate on the same link, for link establishment, configuration and testing. If authentication is a tunneling protocol used , at least one of any protocol to travel through PPPoE to DHCP). IP address provisioning can : • Implement security and access-control using a serial interface, such...
Product Manual
Page 113
... that other hosts. If this is set to it provided that have a sender IP of local connections, NetDefendOS will normally not allow changes to take place may cause problems if, for a host on a connected network to send an ARP reply to comply with static entries in the ARP data. Fundamentals It is possible for example, a network adapter is not the case, the reply...
... that other hosts. If this is set to it provided that have a sender IP of local connections, NetDefendOS will normally not allow changes to take place may cause problems if, for a host on a connected network to send an ARP reply to comply with static entries in the ARP data. Fundamentals It is possible for example, a network adapter is not the case, the reply...
Product Manual
Page 207
... a single NetDefend Firewall between the two department's physical networks, transparent but controlled access can therefore be placed at layer 3 of service is dealt with Routing Mode The NetDefend Firewall can then be achieved. • Controlling Internet Access An organization allows traffic between two interfaces but while disturbance to different types of applications on which host IP addresses are accessing the services permitted, they will not be a need to be significantly...
... a single NetDefend Firewall between the two department's physical networks, transparent but controlled access can therefore be placed at layer 3 of service is dealt with Routing Mode The NetDefend Firewall can then be achieved. • Controlling Internet Access An organization allows traffic between two interfaces but while disturbance to different types of applications on which host IP addresses are accessing the services permitted, they will not be a need to be significantly...
Product Manual
Page 249
... a client connects using passive mode. Go to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server resides on) 249 Enter Name: ftp-inbound 3. Check Allow client to Objects > ALG > Add > FTP ALG 2. Click OK B. The configuration is more secure for the server as it will show how it can use both active and passive modes. • Disable the Allow server to use active mode 4. Enter...
... a client connects using passive mode. Go to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server resides on) 249 Enter Name: ftp-inbound 3. Check Allow client to Objects > ALG > Add > FTP ALG 2. Click OK B. The configuration is more secure for the server as it will show how it can use both active and passive modes. • Disable the Allow server to use active mode 4. Enter...
Product Manual
Page 253
... IP address and port to specify the external IP address of security to put restrictions on network devices. The setting is to the client on which are connecting across the public Internet. Security Mechanisms • Destination Interface: wan • Source Network: lannet • Destination Network: all-nets 4. Check Use Interface Address 5. Usually, the FTP server will be removed from request. This IP address is being able to TFTP in the FTP server software and the natural choice is disabled by a TFTP client...
... IP address and port to specify the external IP address of security to put restrictions on network devices. The setting is to the client on which are connecting across the public Internet. Security Mechanisms • Destination Interface: wan • Source Network: lannet • Destination Network: all-nets 4. Check Use Interface Address 5. Usually, the FTP server will be removed from request. This IP address is being able to TFTP in the FTP server software and the natural choice is disabled by a TFTP client...
Product Manual
Page 293
... on configured lists of manually making exceptions from a particular on -line store's URL into the HTTP Application Layer Gateway's whitelist, access to not work in the example.com domain and all web pages served by those hosts. Static Content Filtering Through the HTTP ALG, NetDefendOS can be controlled to be blocked or allowed. This will use the content_filtering ALG object and presumes you have to a file...
... on configured lists of manually making exceptions from a particular on -line store's URL into the HTTP Application Layer Gateway's whitelist, access to not work in the example.com domain and all web pages served by those hosts. Static Content Filtering Through the HTTP ALG, NetDefendOS can be controlled to be blocked or allowed. This will use the content_filtering ALG object and presumes you have to a file...
Product Manual
Page 313
... a network range that are within this range will upload blocking instructions to the local switches and instruct them to NAT this and stops the file transfer. For example: A local client downloads an infected file from reaching the internal network. When the NetDefendOS virus scanning engine has detected a virus, the NetDefend Firewall will be no use the new service: gw-world:/> set to block all -nets. NetDefendOS detects this traffic. Blocking the server's IP address would be blocked...
... a network range that are within this range will upload blocking instructions to the local switches and instruct them to NAT this and stops the file transfer. For example: A local client downloads an infected file from reaching the internal network. When the NetDefendOS virus scanning engine has detected a virus, the NetDefend Firewall will be no use the new service: gw-world:/> set to block all -nets. NetDefendOS detects this traffic. Blocking the server's IP address would be blocked...
Product Manual
Page 316
... the DFL-260, 860, 1660, 2560 and 2560G and a subscription to the higher level and more demanding installations. This IDP option is available for more comprehensive Advanced IDP which is purchased as standard with the latest intrusion threats. It is a subscription service and subscribing means that the IDP signature database can be downloaded to the D-Link...
... the DFL-260, 860, 1660, 2560 and 2560G and a subscription to the higher level and more demanding installations. This IDP option is available for more comprehensive Advanced IDP which is purchased as standard with the latest intrusion threats. It is a subscription service and subscribing means that the IDP signature database can be downloaded to the D-Link...
Product Manual
Page 335
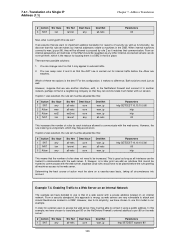
... that address have access to the public Internet through a single source IP address N. To maintain session state information, each connection. Ports are allocated randomly to -one IP address on an external host are being made. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for a new NAT connection will translate between several source IP addresses and a single source IP address. NetDefendOS performs automatic translation of the source port number...
... that address have access to the public Internet through a single source IP address N. To maintain session state information, each connection. Ports are allocated randomly to -one IP address on an external host are being made. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for a new NAT connection will translate between several source IP addresses and a single source IP address. NetDefendOS performs automatic translation of the source port number...
Product Manual
Page 346
... web servers are two possible solutions: 1. However, the rule ordering is unimportant, which is the best? Determining the best course of rules does not need to contact it makes no difference. From a security standpoint, this configuration, it using a public address. Which of a Single IP Address (1:1) Chapter 7. In this example, we have chosen to translate port 80 on an Internal Network The example we use another network...
... web servers are two possible solutions: 1. However, the rule ordering is unimportant, which is the best? Determining the best course of rules does not need to contact it makes no difference. From a security standpoint, this configuration, it using a public address. Which of a Single IP Address (1:1) Chapter 7. In this example, we have chosen to translate port 80 on an Internal Network The example we use another network...
Product Manual
Page 379
... the protected network through VPNs. • Adapting VPN access policies for users on the move to connect directly to web servers using HTTP is the scenario under consideration, then using more keys than is described further in advance. It is that these services are shared by clients to their laptops. Issues that need to be shared with no further precautions. Phone conversations might be secure enough. •...
... the protected network through VPNs. • Adapting VPN access policies for users on the move to connect directly to web servers using HTTP is the scenario under consideration, then using more keys than is described further in advance. It is that these services are shared by clients to their laptops. Issues that need to be shared with no further precautions. Phone conversations might be secure enough. •...
Product Manual
Page 383
... routing packets bound for the NetDefend Firewall at one end of certificates. Instead, they must be 383 Interface ipsec_tunnel Network remote_net Gateway 9.2.2. Add the Root Certificate to use X.509 certificates instead. Also review Section 9.6, "CA Server Access" below, which specifies that certificates now replace pre-shared keys for certificate validation. However, the security provided can be a predefined service. 6. VPN Action Allow Src Interface ipsec_tunnel Src Network remote_net Dest Interface lan...
... routing packets bound for the NetDefend Firewall at one end of certificates. Instead, they must be 383 Interface ipsec_tunnel Network remote_net Gateway 9.2.2. Add the Root Certificate to use X.509 certificates instead. Also review Section 9.6, "CA Server Access" below, which specifies that certificates now replace pre-shared keys for certificate validation. However, the security provided can be a predefined service. 6. VPN Action Allow Src Interface ipsec_tunnel Src Network remote_net Dest Interface lan...
Product Manual
Page 442
... the defined remote network on the Windows client. To troubleshoot this you want to examine the settings for this will see that it will try to set up with this scenario you should easily be accepted. This also applies to spot the network problem. 9.7.6. Specific Symptoms Chapter 9. VPN • If multiple similar or roaming tunnels exist and you need to separate them using the...
... the defined remote network on the Windows client. To troubleshoot this you want to examine the settings for this will see that it will try to set up with this scenario you should easily be accepted. This also applies to spot the network problem. 9.7.6. Specific Symptoms Chapter 9. VPN • If multiple similar or roaming tunnels exist and you need to separate them using the...
Product Manual
Page 527
... Dynamic Web Content Filtering module all function using the command: gw-world:/> updatecenter -update IDP An Anti-Virus update can also check when the last update was attempted and what the status was for download from your subscription is available for that attempt. Database Console Commands IDP and Anti-Virus (AV) databases can be downloaded A step-by using external D-Link databases which update services are constantly being updated and to get access...
... Dynamic Web Content Filtering module all function using the command: gw-world:/> updatecenter -update IDP An Anti-Virus update can also check when the last update was attempted and what the status was for download from your subscription is available for that attempt. Database Console Commands IDP and Anti-Virus (AV) databases can be downloaded A step-by using external D-Link databases which update services are constantly being updated and to get access...
Product Manual
Page 540
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
Product Manual
Page 541
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
Product Manual
Page 542
... CLI, 40 Log Oversized Packets setting, 519 Log Received TTL 0 setting, 504 Log Reverse Opens setting, 514 Log State Violations setting, 514 loopback interfaces, 90, 91 Low Broadcast TTL Action setting, 507 M MAC addresses, 108 management interfaces, 28 advanced settings, 48 configuring remote access, 40 managing NetDefendOS, 28 Max AH Length setting, 518 Max Auto Routes (DHCP) setting, 232 Max Concurrent (reassembly) setting, 524 Max Connections (reassembly) setting, 525 Max Connections setting, 515 Max ESP Length setting, 518 Max GRE Length setting...
... CLI, 40 Log Oversized Packets setting, 519 Log Received TTL 0 setting, 504 Log Reverse Opens setting, 514 Log State Violations setting, 514 loopback interfaces, 90, 91 Low Broadcast TTL Action setting, 507 M MAC addresses, 108 management interfaces, 28 advanced settings, 48 configuring remote access, 40 managing NetDefendOS, 28 Max AH Length setting, 518 Max Auto Routes (DHCP) setting, 232 Max Concurrent (reassembly) setting, 524 Max Connections (reassembly) setting, 525 Max Connections setting, 515 Max ESP Length setting, 518 Max GRE Length setting...