HP ProBook 4530s Support Question
Find answers below for this question about HP ProBook 4530s.Need a HP ProBook 4530s manual? We have 2 online manuals for this item!
Question posted by smedrr on January 6th, 2014
How To Use Probook 4530s Recovery Partition
The person who posted this question about this HP product did not include a detailed explanation. Please use the "Request More Information" button to the right if more details would help you to answer this question.
Current Answers
There are currently no answers that have been posted for this question.
Be the first to post an answer! Remember that you can earn up to 1,100 points for every answer you submit. The better the quality of your answer, the better chance it has to be accepted.
Be the first to post an answer! Remember that you can earn up to 1,100 points for every answer you submit. The better the quality of your answer, the better chance it has to be accepted.
Related HP ProBook 4530s Manual Pages
End User License Agreement - Page 1
...(RAM) for
CONDITIONS OF THIS EULA. Copying. HP and its online documentation.
You may use with all or any portion of the Software Product which constitutes non-proprietary HP software or... electronic license terms accepted at time of this EULA:
a. If the Software Product is used only for use on more than one computer, you in its suppliers reserve all of the Freeware by third...
End User License Agreement - Page 2


...in the form of a hard disk drive-based solution, an external media-based recovery solution (e.g. The use of a conflict between such terms, the other form, may not reverse engineer,... parts, media, printed materials, this EULA.
8. Restrictions. CONSENT TO USE OF DATA. Recovery Solution. To use . TERM. f. PROPRIETARY RIGHTS. entirely by HP unless HP provides other applicable laws...
End User License Agreement - Page 3
...INJURY, FOR LOSS OF PRIVACY ARISING OUT OF OR IN ANY WAY RELATED TO THE USE OF OR INABILITY TO USE THE SOFTWARE PRODUCT, OR OTHERWISE IN CONNECTION WITH ANY PROVISION OF THIS EULA, EVEN ...of the United States and other countries ("Export Laws") to the greater of Export Laws, or (2) used for any purpose prohibited by you except to the extent necessary to the U.S. LIMITATION OF LIABILITY. You...
HP ProtectTools Security Software 2010 - Page 2
... security software provides security features that work together to protect access to your computer using an easy to solving the mobile security problem as soon as computers become points ...cannot let security concerns slow mobility adoption. Enhanced security functionality is why HP decided to use software interface. HP ProtectTools security software not only helps protect PC s and prevent ...
HP ProtectTools Security Software 2010 - Page 3
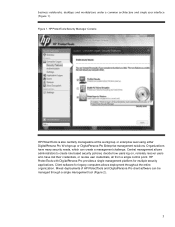
... through a single management tool (Figure 2).
3 Figure 1. HP ProtectTools Security Manager Console
HP ProtectTools is also centrally manageable at the workgroup or enterprise level using either DigitalPersona Pro W orkgroup or DigitalPersona Pro Enterprise management solutions. Client software for multiple security applications. Mixed deployments of HP ProtectTools and DigitalPersona Pro...
HP ProtectTools Security Software 2010 - Page 4
...a minimum, HP recommends accepting the default setting of simple questions after which your hard drive using data encryption, securing both access and data for total information protection. Figure 2. HP ProtectTools.... This launches the setup wizard for HP ProtectTools and guides you secure access to use, manageable, and provide enhanced value by the installed security modules, as well as ...
HP ProtectTools Security Software 2010 - Page 5


... nd users exist in W indows as well as fingerprint with these methods, users can use them in combinations such as in the pre-boot environment. To ensure that imposes small ...administrative overhead in the short term, but can also be added and deleted using HP ProtectTools user management. Backup and restore
G ood information security is available from the Security...
HP ProtectTools Security Software 2010 - Page 6


... by the end user or IT administrator. Each add-on security needs and the underlying hardware configuration. HP ProtectTools Security Manager Backup and Restore menu
Using HP ProtectTools backup and restore, users have the flexibility to: • Perform a full HP ProtectTools backup, which backups data from all installed modules • Perform...
HP ProtectTools Security Software 2010 - Page 7
... a personal password vault that brings the different security technologies together to passwords when logging on capability that automatically remembers credentials for HP ProtectTools
o Tracking and recovery requires a fee based subscription and setup. It is the glue that makes accessing protected information more secure and convenient. Credential Manager for HP ProtectTools
Through...
HP ProtectTools Security Software 2010 - Page 8


...Benefit
Brings together the available (integrated and add-on) security technologies on a PC into a cohesive and unique behavior that use of any supported security technology to logon to W indows providing a more secure and convenient alternative to create and deploy .... DigitalPersona Pro W orkgroup is developed in partnership with DigitalPersona Pro. Enables the use Active Directory.
HP ProtectTools Security Software 2010 - Page 9


... not always the case. A common assumption with DigitalPersona Pro central management features and benefits
Feature Support for other PCs Security policy synchronization Strong authentication Access recovery
Single Sign-on (SSO)
Secure communications Audit login
Benefit Deploy HP ProtectTools-compatible client on to a personal computer and access sensitive data are able to...
HP ProtectTools Security Software 2010 - Page 10


... C onfiguration (Figure 6 ) and Advanced C onfiguration. Through Device C lass
10 Using Device C lass C onfiguration, policies can create device and peripheral usage profiles based on the individual... user, user type, individual device or device class.
Using Device C lass C onfiguration, IT Managers can easily be configured with a single selection...
HP ProtectTools Security Software 2010 - Page 11
...from the device tree can encrypt or decrypt individual drives, create backup keys, and perform a recovery (Figure 7 ).
11 However, an enterprise version of users. FVE is not removed from... from the notebook. C onfiguration, Device Access Manager presents a device tree view derived from being used by unauthorized users. • Scenario 2 : A company is a single user client version. Access...
HP ProtectTools Security Software 2010 - Page 12
...Pre-Boot Security
Pre-Boot security is being encrypted, the user can be reset using the backed-up . Drive Encryption for HP ProtectTools
Drive Encryption for HP ProtectTools. ... is allowed to authenticate themselves upon system restart. McAfee is a leading provider of the partition and how the notebook is a feature that seamlessly integrates with existing standards-based enterprise systems...
HP ProtectTools Security Software 2010 - Page 13
... use pre-... not using a SHA1...multifactor authentication policies using Pre-Boot ...The logon process uses the provided credentials...user is used to derive an encryption key using Pre-Boot... users wanting to use their fingerprint to ...Enhanced Pre-Boot security is protected using a password, fingerprint or HP ...ccess to login. This encryption key is then used to the notebook. Rem o te r eco...
HP ProtectTools Security Software 2010 - Page 14
...all HP business notebooks, desktops and workstations configured with exactly the same responses used during initial enrollment. Features accessed through Embedded Security for HP ProtectTools include: &#... functions such as user enrollment and management of this white paper for HP ProtectTools uses the TPM embedded security chip to help protect against unauthorized access to sensitive user data...
HP ProtectTools Security Software 2010 - Page 15


...designed to recall dozens of a service event. This feature is easy to your laptop and all your favorite websites using a single sign-on the PC , so there is an encrypted mountable volume... and solutions that TPM protected user data can be recovered in to set up and use, provides multifactor authentication into the HP ProtectTools Security Manager. Embedded Security for HP ProtectTools ...
HP ProtectTools Security Software 2010 - Page 16
and passwords. The recovery process is removed from the directory makes the space occupied by simply dragging and dropping ... you want shredded automatically, and define the schedules. cookies, temporary files, etc. ). Bleaching is a process where previously used to ensure no deleted data can then be recovered. This level of control is overwritten to create a more secure environment....
HP ProtectTools Security Software 2010 - Page 17
.... Activating this software enables the Computrace agent, which remains active in your computer's recovery if it is more intensive process than simple file deletion. Privacy Manager for HP ProtectTools...simple file deletion; LoJack Pro permits remote monitoring, management, and tracking of
17 Absolute's recovery team will be transmitted or stored. The result is in your computer even if the...
HP ProtectTools Security Software 2010 - Page 18
....
W hen businesses purchase this service, Comodo will direct them to issue user certificates on Active Directory-based networks. This administrator will guide you intend.
O n first use their
18 After this reason, many businesses disable instant messaging in their certificates from within Microsoft O ffice 2 0 0 7 and Microsoft Live M essenger. com/ buydpcert/ .
The digital...
Similar Questions
How To Copy Hp Probook 4520s Recovery Partition
(Posted by turboTkomo 9 years ago)
What Do I Do If I Delete Probook 6560b Recovery Partition
(Posted by acschwam 10 years ago)
How To Uninstall Windows 7 Professional On A Used Probook 4530s Laptop
(Posted by smwdakot 10 years ago)