User Guide
Page 5
NSA Computer Notebook computer Server Television Firewall Router Internet Switch Wireless Access Point Media Server User's Guide 5 Document Conventions Graphics in operating systems, operating system versions, or if you installed updated firmware/software for your device. Every effort has been made to ensure that the information in this book may differ slightly from the product due to differences in this manual is accurate.
NSA Computer Notebook computer Server Television Firewall Router Internet Switch Wireless Access Point Media Server User's Guide 5 Document Conventions Graphics in operating systems, operating system versions, or if you installed updated firmware/software for your device. Every effort has been made to ensure that the information in this book may differ slightly from the product due to differences in this manual is accurate.
User Guide
Page 21
... accounts. A USB hard drive provides extra storage space and files are copied directly from website feeds for convenient viewing. • Use the included media client software or a media client device like the DMA-2501 to play the video, music and photo files on the NSA. • Use the NSA's website to...
... accounts. A USB hard drive provides extra storage space and files are copied directly from website feeds for convenient viewing. • Use the included media client software or a media client device like the DMA-2501 to play the video, music and photo files on the NSA. • Use the NSA's website to...
User Guide
Page 169
... copy of data on . For example, if you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example). • Use anti-virus software on your data will still be available (but at degraded speeds until you 're using a RAID 1 volume, then your computer...
... copy of data on . For example, if you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example). • Use anti-virus software on your data will still be available (but at degraded speeds until you 're using a RAID 1 volume, then your computer...
User Guide
Page 182
... protocols. • HTTP: The standard protocol for web pages. • FTP: A standard Internet file transfer service. • BitTorrent: A popular distributed peer-to use Apple's iTunes software on the NSA. The Digital Living Network Alliance (DLNA) is a file transfer service that works to play video, music, and photos from the Internet directly...
... protocols. • HTTP: The standard protocol for web pages. • FTP: A standard Internet file transfer service. • BitTorrent: A popular distributed peer-to use Apple's iTunes software on the NSA. The Digital Living Network Alliance (DLNA) is a file transfer service that works to play video, music, and photos from the Internet directly...
User Guide
Page 215
... keeps track of hacking attacks, which can be protected against them. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
... keeps track of hacking attacks, which can be protected against them. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
User Guide
Page 216
... NSA for computer viruses. The firewall slows this down because by default, it only allows traffic from the Internet in response to use anti-virus software on your firewall's 216 Media Server User's Guide When you download using BitTorrent, many other BitTorrent users are also trying to download the file from...
... NSA for computer viruses. The firewall slows this down because by default, it only allows traffic from the Internet in response to use anti-virus software on your firewall's 216 Media Server User's Guide When you download using BitTorrent, many other BitTorrent users are also trying to download the file from...
User Guide
Page 218
... share, you can use a web browser to let people access the NSA's web-published shares from the Internet. This way you could use HTML editing software (not included) to create an index.html or index.htm file to access the NSA's web-published shares from the Internet. 218 Media Server User...
... share, you can use a web browser to let people access the NSA's web-published shares from the Internet. This way you could use HTML editing software (not included) to create an index.html or index.htm file to access the NSA's web-published shares from the Internet. 218 Media Server User...
User Guide
Page 273
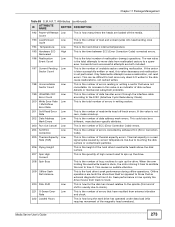
... the total number of the magnetic head armature). Successful and unsuccessful attempts are loaded off -track errors. Thermal asperity is a read signal spike caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is how long the hard drive has operated under data load (this requires movement...
... the total number of the magnetic head armature). Successful and unsuccessful attempts are loaded off -track errors. Thermal asperity is a read signal spike caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is how long the hard drive has operated under data load (this requires movement...
User Guide
Page 322
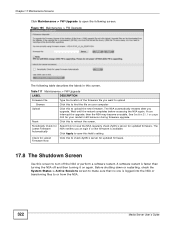
... System Status > Active Sessions screen to or from the NSA. 322 Media Server User's Guide See Section 21.1 on page 365 for updated firmware. A software restart is logged into the NSA or transferring files to make sure that no one is faster than turning the NSA off the NSA or... perform a software restart. Figure 195 Maintenance > FW Upgrade The following screen. Check for Latest Firmware Now Click this to check ZyXEL's server for updated firmware. 17.8 The Shutdown Screen Use this to find the file on again...
... System Status > Active Sessions screen to or from the NSA. 322 Media Server User's Guide See Section 21.1 on page 365 for updated firmware. A software restart is logged into the NSA or transferring files to make sure that no one is faster than turning the NSA off the NSA or... perform a software restart. Figure 195 Maintenance > FW Upgrade The following screen. Check for Latest Firmware Now Click this to check ZyXEL's server for updated firmware. 17.8 The Shutdown Screen Use this to find the file on again...
User Guide
Page 323
... continue or Cancel to quit the restart. When you click the Restart button a pop-up screen will appear asking you to have the device perform a software restart. Figure 198 Maintenance > Shutdown > Confirm Shutdown 17.9 Technical Reference This section provides technical background information on the topics discussed in this screen. System This...
... continue or Cancel to quit the restart. When you click the Restart button a pop-up screen will appear asking you to have the device perform a software restart. Figure 198 Maintenance > Shutdown > Confirm Shutdown 17.9 Technical Reference This section provides technical background information on the topics discussed in this screen. System This...
User Guide
Page 331
...to do some major configuration changes, then it to occur while no one is advisable to create a configuration backup file. Use anti-virus software on your network. If things go back to the previous configuration by virus ACTION Back up data to another NSA or external USB hard drive...18 Protecting Your Data 18.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 18.2 Protection Methods There are a variety of ways to protect your data on . Below is located The following ...
...to do some major configuration changes, then it to occur while no one is advisable to create a configuration backup file. Use anti-virus software on your network. If things go back to the previous configuration by virus ACTION Back up data to another NSA or external USB hard drive...18 Protecting Your Data 18.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 18.2 Protection Methods There are a variety of ways to protect your data on . Below is located The following ...
User Guide
Page 332
...Tools icon in the screen that displays. The wizard installs it is required, close your other files and programs before installing the Memeo Autobackup software. 2 Insert the included CD into your computer to schedule and manage backups. Note: The Memeo Autobackup program uses the same network port ... Note: The Memeo Autobackup program uses the same network port as the NAS Starter Utility to discover the NSA. Then click Memeo Instant Backup Software. Note: If this screen does not display, use the RESET button (see Section 1.1.5 on your computer. 332 Media Server User's Guide ...
...Tools icon in the screen that displays. The wizard installs it is required, close your other files and programs before installing the Memeo Autobackup software. 2 Insert the included CD into your computer to schedule and manage backups. Note: The Memeo Autobackup program uses the same network port ... Note: The Memeo Autobackup program uses the same network port as the NAS Starter Utility to discover the NSA. Then click Memeo Instant Backup Software. Note: If this screen does not display, use the RESET button (see Section 1.1.5 on your computer. 332 Media Server User's Guide ...
User Guide
Page 350
... level. After the second beep, continue pressing the button for example). • Use the NAS Starter Utility to discover your software firewall or other security software to which one -by the number of assigned IP addresses, you will hear three quick beeps after you hear two beeps. If... the RESET button until they are all but I cannot access the NSA anymore. Then connect another NSA and rename it 's list of your model ('nsa325' for five more seconds, then release it . I was able to restore the factory default configuration. You may have a DHCP server on a previous...
... level. After the second beep, continue pressing the button for example). • Use the NAS Starter Utility to discover your software firewall or other security software to which one -by the number of assigned IP addresses, you will hear three quick beeps after you hear two beeps. If... the RESET button until they are all but I cannot access the NSA anymore. Then connect another NSA and rename it 's list of your model ('nsa325' for five more seconds, then release it . I was able to restore the factory default configuration. You may have a DHCP server on a previous...
User Guide
Page 358
... some of the files in the folder do not play them properly). 1 Files with formats that the media server supports. Since the media client software uses your NSA includes the features mentioned in Section 4.5.2 on page 60. Files with formats that are not supported on the media server may not...for the file formats that the media server supports. 2 If you are using the Package Management screen. • You can install using media client software, you have Enabled the application. 20.12 Media Server Functions I just put on the NSA. 1 Make sure the files are a format supported by iTunes...
... some of the files in the folder do not play them properly). 1 Files with formats that the media server supports. Since the media client software uses your NSA includes the features mentioned in Section 4.5.2 on page 60. Files with formats that are not supported on the media server may not...for the file formats that the media server supports. 2 If you are using the Package Management screen. • You can install using media client software, you have Enabled the application. 20.12 Media Server Functions I just put on the NSA. 1 Make sure the files are a format supported by iTunes...
User Guide
Page 369
... Server User's Guide 369 APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your network. If you manually assign IP information instead of using a dynamic IP, make sure that your...
... Server User's Guide 369 APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your network. If you manually assign IP information instead of using a dynamic IP, make sure that your...
User Guide
Page 407
...lists some servers. AUTH TCP 113 Authentication protocol used by ICQ. BOOTP_SERVER UDP 67 DHCP Server. a client/server protocol for example www.zyxel.com) to IP numbers. If this is a secured http session often used in which this service is a brief explanation of IP ...TCP 179 Border Gateway Protocol. BOOTP_CLIENT UDP 68 DHCP Client. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. HTTP TCP 80 Hyper Text Transfer Protocol - HTTPS TCP 443 HTTPS is TCP/UDP, then the service uses the same port number ...
...lists some servers. AUTH TCP 113 Authentication protocol used by ICQ. BOOTP_SERVER UDP 67 DHCP Server. a client/server protocol for example www.zyxel.com) to IP numbers. If this is a secured http session often used in which this service is a brief explanation of IP ...TCP 179 Border Gateway Protocol. BOOTP_CLIENT UDP 68 DHCP Client. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. HTTP TCP 80 Hyper Text Transfer Protocol - HTTPS TCP 443 HTTPS is TCP/UDP, then the service uses the same port number ...
User Guide
Page 437
...the consequences of this or any license under its patent rights nor the patent rights of others. Do not use of ZyXEL Communications Corporation. Disclaimers ZyXEL does not assume any liability arising out of the application or use the NSA for a Class B digital device pursuant to... frequency energy, and if not installed and used in any form or by ZyXEL Communications Corporation. The contents of any products, or software described herein. Illegal downloading or sharing of FCC rules. ZyXEL further reserves the right to the restrictions of copyright laws and any other...
...the consequences of this or any license under its patent rights nor the patent rights of others. Do not use of ZyXEL Communications Corporation. Disclaimers ZyXEL does not assume any liability arising out of the application or use the NSA for a Class B digital device pursuant to... frequency energy, and if not installed and used in any form or by ZyXEL Communications Corporation. The contents of any products, or software described herein. Illegal downloading or sharing of FCC rules. ZyXEL further reserves the right to the restrictions of copyright laws and any other...
User Guide
Page 449
... any third party to its licensors from the object code for "NSA325" WARNING: ZyXEL Communications Corp. Except as this License Agreement to make one backup copy of care as a convenience. End-User License Agreement for the Software. IS WILLING TO LICENSE THE SOFTWARE TO YOU ONLY UPON THE CONDITION THAT YOU ACCEPT ALL OF...
... any third party to its licensors from the object code for "NSA325" WARNING: ZyXEL Communications Corp. Except as this License Agreement to make one backup copy of care as a convenience. End-User License Agreement for the Software. IS WILLING TO LICENSE THE SOFTWARE TO YOU ONLY UPON THE CONDITION THAT YOU ACCEPT ALL OF...
User Guide
Page 450
...TO YOU. 8. Any waiver or modification of this License Agreement shall only be interpreted so as to , if ZyXEL finds that all copies of this Software License Agreement. 11. This License Agreement shall constitute the entire Agreement between the parties hereto. If any reason, ... OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE, AND NON-INFRINGEMENT. Limitation of the parties. ZyXEL may terminate this License Agreement at any of the terms of the Software and Documentation in your possession or under your control. General This License Agreement shall be an ...
...TO YOU. 8. Any waiver or modification of this License Agreement shall only be interpreted so as to , if ZyXEL finds that all copies of this Software License Agreement. 11. This License Agreement shall constitute the entire Agreement between the parties hereto. If any reason, ... OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE, AND NON-INFRINGEMENT. Limitation of the parties. ZyXEL may terminate this License Agreement at any of the terms of the Software and Documentation in your possession or under your control. General This License Agreement shall be an ...
User Guide
Page 451
NOTE: Some components of this product incorporate free software programs covered under the open source code licenses which allows you if we are in possession of the Programs that we will give to freely copy, modify and redistribute the software. For at least three (3) years from the date ...of distribution of the applicable product or software, we distributed to you to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete ...
NOTE: Some components of this product incorporate free software programs covered under the open source code licenses which allows you if we are in possession of the Programs that we will give to freely copy, modify and redistribute the software. For at least three (3) years from the date ...of distribution of the applicable product or software, we distributed to you to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete ...