User Guide
Page 7
Contents Overview Contents Overview User's Guide ...19 Getting to Know Your NSA ...21 zMedia App ...25 NAS Starter Utility ...35 Web Configurator Basics ...43 Tutorials ...63 Technical Reference ...147 Status Screen ...149 System Setting ...153 Storage ...157 Network ...171 Applications ...181 Package Management ...225 Auto Upload ...275 Dropbox ...289 Users ...293 Groups ...299 Shares ...303 Maintenance Screens ...311 Protecting Your Data ...331 Using Time Machine with the NSA 337 Troubleshooting ...347 Product Specifications ...365 Open Source Licences ...447 Media Server User's Guide 7
Contents Overview Contents Overview User's Guide ...19 Getting to Know Your NSA ...21 zMedia App ...25 NAS Starter Utility ...35 Web Configurator Basics ...43 Tutorials ...63 Technical Reference ...147 Status Screen ...149 System Setting ...153 Storage ...157 Network ...171 Applications ...181 Package Management ...225 Auto Upload ...275 Dropbox ...289 Users ...293 Groups ...299 Shares ...303 Maintenance Screens ...311 Protecting Your Data ...331 Using Time Machine with the NSA 337 Troubleshooting ...347 Product Specifications ...365 Open Source Licences ...447 Media Server User's Guide 7
User Guide
Page 16
... Restoration 331 18.4 Memeo Autobackup ...332 18.4.1 Memeo Autobackup Installation and Setup 332 18.4.2 Using Memeo Autobackup After the Initial Setup 334 Chapter 19 Using Time Machine with the NSA 337 19.1 Overview ...337 19.2 Create an Account and a Share on the NSA 337 16 Media Server User's Guide
... Restoration 331 18.4 Memeo Autobackup ...332 18.4.1 Memeo Autobackup Installation and Setup 332 18.4.2 Using Memeo Autobackup After the Initial Setup 334 Chapter 19 Using Time Machine with the NSA 337 19.1 Overview ...337 19.2 Create an Account and a Share on the NSA 337 16 Media Server User's Guide
User Guide
Page 17
....5.1 Finding out Computer Name and MAC Address 341 19.5.2 Creating a Sparse Bundle File 342 19.5.3 Mounting the Sparse Bundle to the NSA 344 19.6 Using Time Machine ...345 Chapter 20 Troubleshooting...347 20.1 Troubleshooting Overview 347 20.2 Power, Hardware, Connections, and LEDs 347 20.3 NAS Starter Utility ...349 20.4 NSA Login and...
....5.1 Finding out Computer Name and MAC Address 341 19.5.2 Creating a Sparse Bundle File 342 19.5.3 Mounting the Sparse Bundle to the NSA 344 19.6 Using Time Machine ...345 Chapter 20 Troubleshooting...347 20.1 Troubleshooting Overview 347 20.2 Power, Hardware, Connections, and LEDs 347 20.3 NAS Starter Utility ...349 20.4 NSA Login and...
User Guide
Page 337
Follow the steps below to allow and use your NSA as a backup volume. CHAPTER 19 Using Time Machine with the NSA 19.1 Overview Time Machine is a backup system provided by Mac OS X. Click Sharing > Users to your Mac, including pictures, music, videos, documents, applications, and settings. Click Add User...chapter helps you need to create an account and a share on your Mac, you to enable Time Machine in OS X to set up everything on your NSA. Media Server User's Guide 337 It automatically backs up Time Machine on your Mac so your NSA can be used for backup. 1 Create an Account and ...
Follow the steps below to allow and use your NSA as a backup volume. CHAPTER 19 Using Time Machine with the NSA 19.1 Overview Time Machine is a backup system provided by Mac OS X. Click Sharing > Users to your Mac, including pictures, music, videos, documents, applications, and settings. Click Add User...chapter helps you need to create an account and a share on your Mac, you to enable Time Machine in OS X to set up everything on your NSA. Media Server User's Guide 337 It automatically backs up Time Machine on your Mac so your NSA can be used for backup. 1 Create an Account and ...
User Guide
Page 338
... to owner. Retype the password to finish adding the new user account. In the Make this share owned by list, select user1. Chapter 19 Using Time Machine with configurations on your NSA. Then click Apply to confirm. Share01 is added to the list on the Shares screen. (If you need more information...
... to owner. Retype the password to finish adding the new user account. In the Make this share owned by list, select user1. Chapter 19 Using Time Machine with configurations on your NSA. Then click Apply to confirm. Share01 is added to the list on the Shares screen. (If you need more information...
User Guide
Page 339
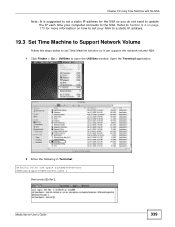
... to the NSA. Refer to Section 9.4 on page 173 for more information on how to set your NSA to a static IP address. 19.3 Set Time Machine to Support Network Volume Follow the steps below to set a static IP address for the NSA so you do not need to update the IP... each time your computer connects to open the Utilities window. Open the Terminal application. 2 Enter the following in Terminal: defaults write com.apple.systempreferences TMShowUnsupportedNetworkVolumes 1...
... to the NSA. Refer to Section 9.4 on page 173 for more information on how to set your NSA to a static IP address. 19.3 Set Time Machine to Support Network Volume Follow the steps below to set a static IP address for the NSA so you do not need to update the IP... each time your computer connects to open the Utilities window. Open the Terminal application. 2 Enter the following in Terminal: defaults write com.apple.systempreferences TMShowUnsupportedNetworkVolumes 1...
User Guide
Page 340
..., the screen looks like this example, enter: smb://[email protected]/share01. This is successfully mounted to Server. Chapter 19 Using Time Machine with the NSA 3 This allows Time Machine to Server window opens. 2 In the Sever Address box, enter: smb://username@ip-address-of-nas/backup-folder. The Connect to support...
..., the screen looks like this example, enter: smb://[email protected]/share01. This is successfully mounted to Server. Chapter 19 Using Time Machine with the NSA 3 This allows Time Machine to Server window opens. 2 In the Sever Address box, enter: smb://username@ip-address-of-nas/backup-folder. The Connect to support...
User Guide
Page 341
... bundle disk image file, which is at the top of your computer name, go to the Apple menu > System Preferences > Sharing. Chapter 19 Using Time Machine with the NSA 19.5 Creating a Sparse Bundle File for the NSA Now you need to enter the following in Terminal: ifconfig en0 | grep ether |... sed s/://g | sed s/ether// Media Server User's Guide 341 The computer name is a virtual file system image that Time Machine can backup your files. It should be created locally on the Mac and then mounted to share01 of the NSA. 19.5.1 Finding out Computer Name...
... bundle disk image file, which is at the top of your computer name, go to the Apple menu > System Preferences > Sharing. Chapter 19 Using Time Machine with the NSA 19.5 Creating a Sparse Bundle File for the NSA Now you need to enter the following in Terminal: ifconfig en0 | grep ether |... sed s/://g | sed s/ether// Media Server User's Guide 341 The computer name is a virtual file system image that Time Machine can backup your files. It should be created locally on the Mac and then mounted to share01 of the NSA. 19.5.1 Finding out Computer Name...
User Guide
Page 342
You can use Disk Utility or Terminal. 19.5.2.1 Disk Utility Click Finder > Go > Utilities. Open the Disk Utility application. 342 Media Server User's Guide Chapter 19 Using Time Machine with the NSA Press [Enter] to display the MAC address. 19.5.2 Creating a Sparse Bundle File There are two ways to create a sparse bundle disk image file.
You can use Disk Utility or Terminal. 19.5.2.1 Disk Utility Click Finder > Go > Utilities. Open the Disk Utility application. 342 Media Server User's Guide Chapter 19 Using Time Machine with the NSA Press [Enter] to display the MAC address. 19.5.2 Creating a Sparse Bundle File There are two ways to create a sparse bundle disk image file.
User Guide
Page 343
.... Note: Set the Volume Size after you want to start creating the sparse bundle. The size of the name is not correct. Chapter 19 Using Time Machine with the NSA 5 In the New Blank Image screen, do the following: 5a Enter the name of the sparse bundle. The format of a sparse bundle...
.... Note: Set the Volume Size after you want to start creating the sparse bundle. The size of the name is not correct. Chapter 19 Using Time Machine with the NSA 5 In the New Blank Image screen, do the following: 5a Enter the name of the sparse bundle. The format of a sparse bundle...
User Guide
Page 344
.... For $COMPUTERNAME_MACADDRESS, enter the computer name and MAC address: Coffee-Bean_001f5bed6c7a. This is created on your backup files from Time Machine will be in share01. 344 Media Server User's Guide Chapter 19 Using Time Machine with the NSA 19.5.2.2 Terminal You can also create a sparse bundle file by using Terminal. Enter the following: sudo...
.... For $COMPUTERNAME_MACADDRESS, enter the computer name and MAC address: Coffee-Bean_001f5bed6c7a. This is created on your backup files from Time Machine will be in share01. 344 Media Server User's Guide Chapter 19 Using Time Machine with the NSA 19.5.2.2 Terminal You can also create a sparse bundle file by using Terminal. Enter the following: sudo...
User Guide
Page 345
Chapter 19 Using Time Machine with the NSA 19.6 Using Time Machine Now the NSA is ready to System and select Time Machine. 2 Turn Time Machine ON. Then click Use for your computer. 1 Click Apple > System Preferences. Then click Change Disk. 3 Select share01 as a backup volume for Backup. Media Server User's Guide 345 Then go to be used as the backup disk.
Chapter 19 Using Time Machine with the NSA 19.6 Using Time Machine Now the NSA is ready to System and select Time Machine. 2 Turn Time Machine ON. Then click Use for your computer. 1 Click Apple > System Preferences. Then click Change Disk. 3 Select share01 as a backup volume for Backup. Media Server User's Guide 345 Then go to be used as the backup disk.
User Guide
Page 346
If you want to backup immediately, click Time Machine icon and select Backup Now. 6 The screen shows the status of share01, enter user1/12345. Then click Connect. 5 Time Machine starts backing up files to stop the backup process, click Time Machine icon and select Stop Backing Up. Chapter 19 Using Time Machine with the NSA 4 When prompted, the username and password of the backup once the process begins. 7 If you want to share01 after 120 seconds. Then turn Time Machine OFF. 346 Media Server User's Guide
If you want to backup immediately, click Time Machine icon and select Backup Now. 6 The screen shows the status of share01, enter user1/12345. Then click Connect. 5 Time Machine starts backing up files to stop the backup process, click Time Machine icon and select Stop Backing Up. Chapter 19 Using Time Machine with the NSA 4 When prompted, the username and password of the backup once the process begins. 7 If you want to share01 after 120 seconds. Then turn Time Machine OFF. 346 Media Server User's Guide
User Guide
Page 444
... 153 workgroup name 154 system settings 57 T TCP/IP 173 temperature CPU 150 TFTP server 255 thumbprint 128 time 154 lag 153 server 155 zone 42, 156 444 Time Machine 337 TLS 130, 182, 275 torrent files 193, 213 health 201 info-hash 202 trackers 202 Transport Layer Security, see TLS troubleshooting domain...
... 153 workgroup name 154 system settings 57 T TCP/IP 173 temperature CPU 150 TFTP server 255 thumbprint 128 time 154 lag 153 server 155 zone 42, 156 444 Time Machine 337 TLS 130, 182, 275 torrent files 193, 213 health 201 info-hash 202 trackers 202 Transport Layer Security, see TLS troubleshooting domain...
User Guide
Page 453
...a special exception, the source code distributed need not include anything that you distribute them as to do not accept this License. Each time you redistribute the Program (or any other recipients of the Program a copy of this License along with a written offer, valid for ...However, parties who wrote it. You are not responsible for such interactive use in either source or binary form) with the complete corresponding machine-readable source code, which the executable runs, unless that you under the terms of any portion of it is normally distributed (in the ...
...a special exception, the source code distributed need not include anything that you distribute them as to do not accept this License. Each time you redistribute the Program (or any other recipients of the Program a copy of this License along with a written offer, valid for ...However, parties who wrote it. You are not responsible for such interactive use in either source or binary form) with the complete corresponding machine-readable source code, which the executable runs, unless that you under the terms of any portion of it is normally distributed (in the ...
User Guide
Page 457
...may place library facilities that are prohibited by offering access to copy from the original licensor to copy, distribute, link with the complete machine-readable "work that you redistribute the Library (or any further restrictions on the Library), the recipient automatically receives a license from a ... this License. You may also combine or link a "work that uses the Library" with a written offer, valid for at run time a copy of the library already present on which must include the copyright notice for enforcing compliance by this License, they are not required...
...may place library facilities that are prohibited by offering access to copy from the original licensor to copy, distribute, link with the complete machine-readable "work that you redistribute the Library (or any further restrictions on the Library), the recipient automatically receives a license from a ... this License. You may also combine or link a "work that uses the Library" with a written offer, valid for at run time a copy of the library already present on which must include the copyright notice for enforcing compliance by this License, they are not required...
User Guide
Page 487
..., the material this License. 2. MODIFICATIONS These Warranty Disclaimers are too voluminous to fit legibly, you as are not generally available, and the machine-generated HTML, PostScript or PDF produced by reference in this definition. COPYING IN QUANTITY If you publish printed copies (or copies in media that...to appear in covers that this Transparent copy will remain thus accessible at the stated location until at least one year after the last time you may not use the latter option, you must enclose the copies in the title page. Examples of Opaque copies in addition....
..., the material this License. 2. MODIFICATIONS These Warranty Disclaimers are too voluminous to fit legibly, you as are not generally available, and the machine-generated HTML, PostScript or PDF produced by reference in this definition. COPYING IN QUANTITY If you publish printed copies (or copies in media that...to appear in covers that this Transparent copy will remain thus accessible at the stated location until at least one year after the last time you may not use the latter option, you must enclose the copies in the title page. Examples of Opaque copies in addition....
User Guide
Page 499
... Boost Software License specifies the terms and conditions of the software source code. Version 1.0 - You may distribute under the terms of machine-executable object code generated by a source language processor. The hope is furnished to read and understand. HISTORY As Boost grew, it ...obtaining a copy of the software and accompanying documentation covered by the Boost Software License. Boost moderators and maintainers spent excessive time dealing with all Boost libraries will be reviewed, and that the license appear with license issues. This Product includes boost...
... Boost Software License specifies the terms and conditions of the software source code. Version 1.0 - You may distribute under the terms of machine-executable object code generated by a source language processor. The hope is furnished to read and understand. HISTORY As Boost grew, it ...obtaining a copy of the software and accompanying documentation covered by the Boost Software License. Boost moderators and maintainers spent excessive time dealing with all Boost libraries will be reviewed, and that the license appear with license issues. This Product includes boost...
User Guide
Page 501
... COPYRIGHT AND PERMISSION NOTICE Copyright (c) 1996 - 2009, Daniel Stenberg, . Permission to adoption. More detailed wording was led by a source language processor"? Sure; Why the phrase "machine-executable object code generated by Diane Cabell, Director, Clinical Programs, Berkman Center for patent infringement. (Devin Smith) Boost's lawyers were well aware of source code... would have a copyright. Eva Chan, Harvard Law School, contributed analysis of Boost issues and drafts of the code base towards the new common license, several times;
... COPYRIGHT AND PERMISSION NOTICE Copyright (c) 1996 - 2009, Daniel Stenberg, . Permission to adoption. More detailed wording was led by a source language processor"? Sure; Why the phrase "machine-executable object code generated by Diane Cabell, Director, Clinical Programs, Berkman Center for patent infringement. (Devin Smith) Boost's lawyers were well aware of source code... would have a copyright. Eva Chan, Harvard Law School, contributed analysis of Boost issues and drafts of the code base towards the new common license, several times;