User Guide
Page 17
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
User Guide
Page 31
...Note: Refer to the Quick Start Guide for your NSA's hardware connections and the steps for NSA221, NSA310, NSA320, or NSA325 on your computer (see Chapter 2 on the NSA210. Note: If the NSA210 will uninstall previous ...a NAS Starter Utility available for NSA210. NAS Starter Utility screens are shown here as the NSA221, NSA310, NSA320, or NSA325, utility version 2.02 must first be used to identify each NSA in the process. Installing ...existing data in the NSA. The NAS Starter Utility software version number is recommended to open a web help page about the NAS Starter Utility screens.
...Note: Refer to the Quick Start Guide for your NSA's hardware connections and the steps for NSA221, NSA310, NSA320, or NSA325 on your computer (see Chapter 2 on the NSA210. Note: If the NSA210 will uninstall previous ...a NAS Starter Utility available for NSA210. NAS Starter Utility screens are shown here as the NSA221, NSA310, NSA320, or NSA325, utility version 2.02 must first be used to identify each NSA in the process. Installing ...existing data in the NSA. The NAS Starter Utility software version number is recommended to open a web help page about the NAS Starter Utility screens.
User Guide
Page 173
... still be available (but at degraded speeds until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example, accounting and financial data, small database systems, and enterprise servers. However, RAID cannot protect against file corruption... those requiring high fault tolerance without need of large amounts of storage capacity or top performance, for example). • Use anti-virus software on the NSA. • Keep another copy of the smallest disk in the RAID array. RAID and Data Protection If a hard ...
... still be available (but at degraded speeds until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example, accounting and financial data, small database systems, and enterprise servers. However, RAID cannot protect against file corruption... those requiring high fault tolerance without need of large amounts of storage capacity or top performance, for example). • Use anti-virus software on the NSA. • Keep another copy of the smallest disk in the RAID array. RAID and Data Protection If a hard ...
User Guide
Page 186
...; P2P download: Peer-to-peer files sharing protocol. 186 Media Server User's Guide iTunes Server The NSA iTunes server feature lets you use Apple's iTunes software on a computer to play music and video files stored on your network play video, music, and photos from the Internet directly to use FTPES as...
...; P2P download: Peer-to-peer files sharing protocol. 186 Media Server User's Guide iTunes Server The NSA iTunes server feature lets you use Apple's iTunes software on a computer to play music and video files stored on your network play video, music, and photos from the Internet directly to use FTPES as...
User Guide
Page 219
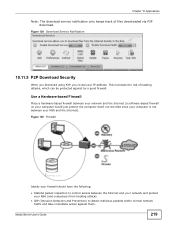
Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network ...
Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network ...
User Guide
Page 220
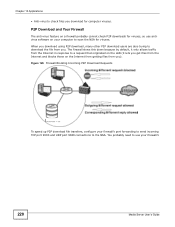
... lets you get files from the Internet and blocks those on your computer to download the file from the Internet in response to use antivirus software on the Internet from getting files from you download using P2P download, many other P2P download users are also trying to scan the NSA for...
... lets you get files from the Internet and blocks those on your computer to download the file from the Internet in response to use antivirus software on the Internet from getting files from you download using P2P download, many other P2P download users are also trying to scan the NSA for...
User Guide
Page 222
Additionally, you can use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your Internet gateway and possibly firewall rules in order ...
Additionally, you can use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your Internet gateway and possibly firewall rules in order ...
User Guide
Page 277
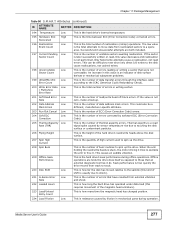
... number of unstable sectors awaiting reallocation. Chapter 11 Package Management Table 90 S.M.A.R.T. If the sector is later successfully written or read signal spike caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the hard drive's seek performance during operation. Only failed write attempts cause a reallocation...
... number of unstable sectors awaiting reallocation. Chapter 11 Package Management Table 90 S.M.A.R.T. If the sector is later successfully written or read signal spike caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the hard drive's seek performance during operation. Only failed write attempts cause a reallocation...
User Guide
Page 331
...to have the NSA regularly check ZyXEL's server for your computer Upload Click this field's setting. Check for Latest Firmware Now Click this to check ZyXEL's server for updated firmware. 18.8 The Shutdown Screen Use this to upload the new firmware. A software restart is faster than turning ...the NSA off the NSA or perform a software restart. Click Apply to save this to refresh the ...
...to have the NSA regularly check ZyXEL's server for your computer Upload Click this field's setting. Check for Latest Firmware Now Click this to check ZyXEL's server for updated firmware. 18.8 The Shutdown Screen Use this to upload the new firmware. A software restart is faster than turning ...the NSA off the NSA or perform a software restart. Click Apply to save this to refresh the ...
User Guide
Page 332
... the shutdown. Shutdown Click this to confirm. When you click the Restart button a pop-up screen will appear asking you to have the device perform a software restart. Figure 215 Maintenance > Shutdown > Confirm Shutdown 18.9 Technical Reference This section provides technical background information on the topics discussed in this screen. Table 122...
... the shutdown. Shutdown Click this to confirm. When you click the Restart button a pop-up screen will appear asking you to have the device perform a software restart. Figure 215 Maintenance > Shutdown > Confirm Shutdown 18.9 Technical Reference This section provides technical background information on the topics discussed in this screen. Table 122...
User Guide
Page 341
...file. If things go back to the previous configuration by virus Back up data to another NSA or external USB hard drive. Use anti-virus software on your data on the NSA. CHAPTER 19 Protecting Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA... and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of ways to protect your computer to scan files before you 're going to ...
...file. If things go back to the previous configuration by virus Back up data to another NSA or external USB hard drive. Use anti-virus software on your data on the NSA. CHAPTER 19 Protecting Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA... and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of ways to protect your computer to scan files before you 're going to ...
User Guide
Page 346
... to return to allow UDP port 50127 traffic from the NSA. You will hear three quick beeps after you will lose access to configure your software firewall or anti-virus scanner's security level. I have a DHCP server on your network and you can directly change the IP address of the NSA ... NSA. • The default server name is always unreachable, even though I can check the MAC address of your NSA by the number of your model ('nsa320' for five more seconds, then release it . You can access it . I was able to rename it. Alternatively you have the NAS Starter Utility, see ...
... to return to allow UDP port 50127 traffic from the NSA. You will hear three quick beeps after you will lose access to configure your software firewall or anti-virus scanner's security level. I have a DHCP server on your network and you can directly change the IP address of the NSA ... NSA. • The default server name is always unreachable, even though I can check the MAC address of your NSA by the number of your model ('nsa320' for five more seconds, then release it . You can access it . I was able to rename it. Alternatively you have the NAS Starter Utility, see ...
User Guide
Page 354
... screen (Chapter 11 on the media server may not support the file's format. This does not include the applications you can install using media client software, you have installed the application and can see the application's configuration screen but some applications in the Web Configurator. • The firmware installed in the...
... screen (Chapter 11 on the media server may not support the file's format. This does not include the applications you can install using media client software, you have installed the application and can see the application's configuration screen but some applications in the Web Configurator. • The firmware installed in the...
User Guide
Page 365
... settings on your network. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you can set up an IP address for: • Windows XP/NT/2000 on page 365 • Windows Vista on page 369 • Windows...
... settings on your network. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you can set up an IP address for: • Windows XP/NT/2000 on page 365 • Windows Vista on page 369 • Windows...
User Guide
Page 403
... on the Protocol. AIM/New-ICQ TCP 5190 AOL's Internet Messenger service. FTP TCP 20 File Transfer Program, a program to RFC 1700 for example www.zyxel.com) to find out if a user is also used services and their associated protocols and port numbers. Please refer to enable fast transfer of the... applications that may not be used to IP numbers. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. If this service. APPENDIX C Common Services The following table lists some servers.
... on the Protocol. AIM/New-ICQ TCP 5190 AOL's Internet Messenger service. FTP TCP 20 File Transfer Program, a program to RFC 1700 for example www.zyxel.com) to find out if a user is also used services and their associated protocols and port numbers. Please refer to enable fast transfer of the... applications that may not be used to IP numbers. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. If this service. APPENDIX C Common Services The following table lists some servers.
User Guide
Page 433
... and all intellectual property rights therein shall remain at all implied licenses are reserved by any documentation files accompanying the Software ("Documentation"), for "NSA210, NSA 221, NSA310, NSA320, and NSA325" WARNING: ZyXEL Communications Corp. Rather, you a non-exclusive, non-sublicense, nontransferable license to make one backup copy of the license granted hereunder. HOWEVER...
... and all intellectual property rights therein shall remain at all implied licenses are reserved by any documentation files accompanying the Software ("Documentation"), for "NSA210, NSA 221, NSA310, NSA320, and NSA325" WARNING: ZyXEL Communications Corp. Rather, you a non-exclusive, non-sublicense, nontransferable license to make one backup copy of the license granted hereunder. HOWEVER...
User Guide
Page 434
...of such material is not obligated to provide any of the Software utilize or include third party software and other support for the resultant modified Software. ZyXEL DOES NOT WARRANT THAT THE FUNCTIONS CONTAINED IN THE SOFTWARE WILL MEET ANY REQUIREMENTS OR NEEDS YOU MAY HAVE, OR ... FASHION, OR THAT ANY DEFECTS OR ERRORS IN THE SOFTWARE WILL BE CORRECTED, OR THAT THE SOFTWARE IS COMPATIBLE WITH ANY PARTICULAR PLATFORM. Portions of the foregoing. To the extent that the Software contains third party software, ZyXEL has no express or implied obligation to provide any maintenance...
...of such material is not obligated to provide any of the Software utilize or include third party software and other support for the resultant modified Software. ZyXEL DOES NOT WARRANT THAT THE FUNCTIONS CONTAINED IN THE SOFTWARE WILL MEET ANY REQUIREMENTS OR NEEDS YOU MAY HAVE, OR ... FASHION, OR THAT ANY DEFECTS OR ERRORS IN THE SOFTWARE WILL BE CORRECTED, OR THAT THE SOFTWARE IS COMPATIBLE WITH ANY PARTICULAR PLATFORM. Portions of the foregoing. To the extent that the Software contains third party software, ZyXEL has no express or implied obligation to provide any maintenance...
User Guide
Page 435
..., OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF THE USE OF OR INABILITY TO USE THE SOFTWARE OR PROGRAM, OR FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Upon notification of termination, you agree to ...arising out of this License Agreement. This License Agreement, the rights granted hereunder, the Software and Documentation shall not be construed, interpreted and governed by destroying or returning to a binding arbitration. ZyXEL's TOTAL AGGREGATE LIABILITY WITH RESPECT TO ITS OBLIGATIONS UNDER THIS AGREEMENT OR OTHERWISE WITH ...
..., OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF THE USE OF OR INABILITY TO USE THE SOFTWARE OR PROGRAM, OR FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Upon notification of termination, you agree to ...arising out of this License Agreement. This License Agreement, the rights granted hereunder, the Software and Documentation shall not be construed, interpreted and governed by destroying or returning to a binding arbitration. ZyXEL's TOTAL AGGREGATE LIABILITY WITH RESPECT TO ITS OBLIGATIONS UNDER THIS AGREEMENT OR OTHERWISE WITH ...
User Guide
Page 436
...For at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code...license document, but changing it is permitted to freely copy, modify and redistribute the software. Preamble 436 Media Server User's Guide If any purpose, except the express written permission of ZyXEL Communications Corporation. This Product includes cups, libgcgi, libgphoto2, libraw1394, pam_mount, wxWidgets, wxWidgets...
...For at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code...license document, but changing it is permitted to freely copy, modify and redistribute the software. Preamble 436 Media Server User's Guide If any purpose, except the express written permission of ZyXEL Communications Corporation. This Product includes cups, libgcgi, libgphoto2, libraw1394, pam_mount, wxWidgets, wxWidgets...
User Guide
Page 437
... is no warranty for linking other code with the library. Therefore, we want it in this license. Most GNU software, including some specially designated software packages--typically libraries--of an advantage over competing non-free programs. These disadvantages are the reason we are referring to freedom...object files to the recipients, so that might be consistent with the library after making changes to the library and recompiling it . Finally, software patents pose a constant threat to the existence of use pieces of a free program by problems that they , too, receive or can...
... is no warranty for linking other code with the library. Therefore, we want it in this license. Most GNU software, including some specially designated software packages--typically libraries--of an advantage over competing non-free programs. These disadvantages are the reason we are referring to freedom...object files to the recipients, so that might be consistent with the library after making changes to the library and recompiling it . Finally, software patents pose a constant threat to the existence of use pieces of a free program by problems that they , too, receive or can...