User Guide
Page 220
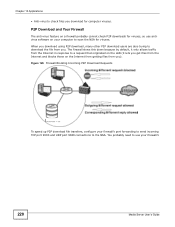
The firewall slows this down because by default, it only allows traffic from the Internet in response to a request that originated on the LAN (it lets you get ... anti-virus feature on your firewall's 220 Media Server User's Guide Figure 126 Firewall Blocking Incoming P2P Download Requests To speed up P2P download file transfers, configure your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089 connections to download the file from you download for viruses...
The firewall slows this down because by default, it only allows traffic from the Internet in response to a request that originated on the LAN (it lets you get ... anti-virus feature on your firewall's 220 Media Server User's Guide Figure 126 Firewall Blocking Incoming P2P Download Requests To speed up P2P download file transfers, configure your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089 connections to download the file from you download for viruses...
User Guide
Page 260
...an Archive backup, this means using all of your backup. Figure 161 Protect > Backup: Step 3 The following table describes the labels in slow networks only. Encryption For a Synchronization backup (to a remote target), the source data will be compressed before enabling it. Bandwidth For a ..., compression is only available if you really need this feature before the transmission to a remote target), this means securing the file transfer session. This step is a method of synchronization backups to help stop them from using a password to secure files. Chapter 11 Package...
...an Archive backup, this means using all of your backup. Figure 161 Protect > Backup: Step 3 The following table describes the labels in slow networks only. Encryption For a Synchronization backup (to a remote target), the source data will be compressed before enabling it. Bandwidth For a ..., compression is only available if you really need this feature before the transmission to a remote target), this means securing the file transfer session. This step is a method of synchronization backups to help stop them from using a password to secure files. Chapter 11 Package...
User Guide
Page 341
... more information on RAID. 19.3 Configuration File Backup and Restoration Use the Maintenance > Configuration menus to the NSA after configuration changes Need to transfer data from your computer to create a file of your NSA configurations such as a fire or earthquake occurs where your data to scan files ...NSA or external USB hard drive. Backup your NSA is located The following sections describe these methods in each situation. If you can be slow so you make the configuration changes, you 're going to do some major configuration changes, then it to protect your data on the...
... more information on RAID. 19.3 Configuration File Backup and Restoration Use the Maintenance > Configuration menus to the NSA after configuration changes Need to transfer data from your computer to create a file of your NSA configurations such as a fire or earthquake occurs where your data to scan files ...NSA or external USB hard drive. Backup your NSA is located The following sections describe these methods in each situation. If you can be slow so you make the configuration changes, you 're going to do some major configuration changes, then it to protect your data on the...